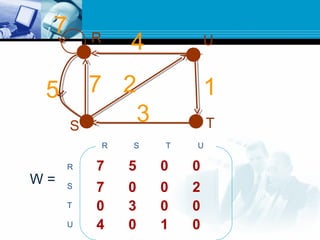
A graph is a data structure consisting of nodes connected by edges. There are different types of graphs such as undirected graphs, directed graphs, connected graphs, and strongly connected graphs. Algorithms like depth-first search, Kosaraju's algorithm, and Warshall's algorithm can be used to find strongly connected components, biconnected components, and shortest paths in graphs.
![A graph G consists of two things:
1.A set V of elements called nodes(or points or vertices)
2.A set E of edges such that each edge e in E is identified with a unique pair
[u,v] of nodes in V, denoted by e=[u,v]
Suppose e=[u,v]. Then the nodes u and v are called endpoints of e and u and v
are said to be adjacent nodes or neighbors.](https://image.slidesharecdn.com/graph-150531095324-lva1-app6892/85/Graph-3-320.jpg)
![Node or
Point or
vertex
Edge
u
v
e=[u,v]
Adjacentnodesorneighbors](https://image.slidesharecdn.com/graph-150531095324-lva1-app6892/85/Graph-4-320.jpg)
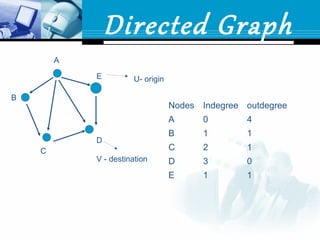
![Directed Graph
Each edge is assigned a direction or each edge E is
identified with ordered pair (u,v)
(u,v) directed graph
[u,v] undirected graph
U=origin
v=destination](https://image.slidesharecdn.com/graph-150531095324-lva1-app6892/85/Graph-6-320.jpg)



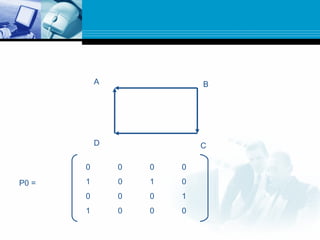
![ This algorithm is used to find the shortest
paths in G when G is weighted.
First we define m-square boolean matrices
P0,P1…….,Pm as follows:
Let Pk[i,j] denote the i, j entry of the
matrix Pk.](https://image.slidesharecdn.com/graph-150531095324-lva1-app6892/85/Graph-35-320.jpg)
![ Then we define
Pk[i,j]=
1 ,if there is a simple path from vi to vj which does
not use any other node except possibly v1,v2,
…..,vk
0 ,otherwise
In other words,
P0[i,j]=1, if there is an edge from vi to vj
P1[i,j]=1, if there is a simple path from vi to vj which does not use any other node
except possibly v1.
P2[i,j]=1, if there is a simple path from vi to vj which does not use any other node
except possibly v1 and v2.](https://image.slidesharecdn.com/graph-150531095324-lva1-app6892/85/Graph-36-320.jpg)
![ Observe that P0=A, the adjacency matrix of G.
Since G has only m nodes, the last matrix
Pm=P, the path matrix of G.
Warshall observed that Pk[i,j]=1 can occur only
if one of the following two cases occur:
1. There is a simple path from vi to vj which does
not use any other node except possibly v1,v2,
….,vk-1, hence
Pk-1[i,j]=1
vi ……….. vj](https://image.slidesharecdn.com/graph-150531095324-lva1-app6892/85/Graph-37-320.jpg)
![2. There is a simple path from vi to vk and
a simple path from vk to vj where each
path does not use any other nodes
except possibly v1,v2,……,vk-1; hence
Pk-1[i,k]=1 and Pk-1[k,j]=1
vi ……….. ………..vk vj](https://image.slidesharecdn.com/graph-150531095324-lva1-app6892/85/Graph-38-320.jpg)
![ Accordingly, the elements of matrix Pk can
be obtained by:
Pk[i,j]=Pk-1[i,j] v (Pk-1[i,k] Pk-1[k,j])
Where V and denote the logical OR and AND operator
^ 0 1
0 0 0
1 0 1
v 0 1
0 0 1
1 1 1](https://image.slidesharecdn.com/graph-150531095324-lva1-app6892/85/Graph-39-320.jpg)
![ P1[1,1]=P0[1,1]v(P0[1,1]^P0[1,1])
=0v(0^0)
=0v0=0
P1[1,2]=P0[1,2]v(P0[1,1]^P0[1,2])
=0v(0^0)
=0v0=0
P1[1,3]=P0[1,3]v(P0[1,1]^P0[1,3])
=0v(0^0)
=0v0=0
P1[1,4]=P0[1,4]v(P0[1,1]^P0[1,4])
=0v(0^0)
=0v0=0
P1[2,1]=P0[2,1]v(P0[2,1]^P0[1,1])
=1v(1^0)
=1v0=1
P1[2,2]=P0[2,2]v(P0[2,1]^P0[1,2])
=0v(1^0)
=0v0=0
P1[2,3]=P0[2,3]v(P0[2,1]^P0[1,3])
=1v(1^0)
=1v0=1
P1[2,4]=P0[2,4]v(P0[2,1]^P0[1,4])
=0v(1^0)
=0v0=0
P1 =
0 0 0 0
1 0 1 0
- - - -
- - - -](https://image.slidesharecdn.com/graph-150531095324-lva1-app6892/85/Graph-41-320.jpg)
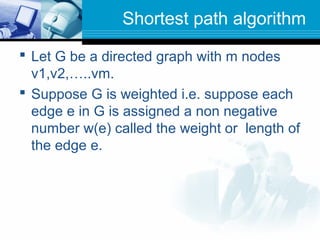
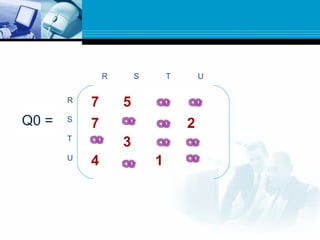
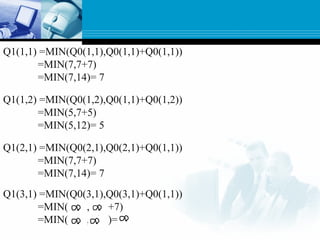
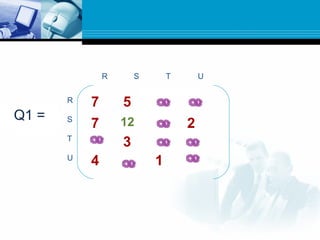
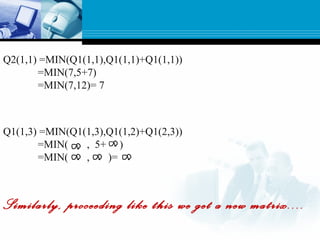
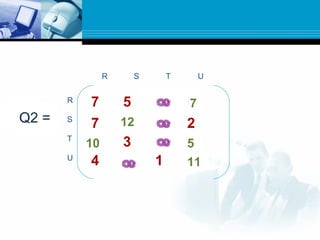
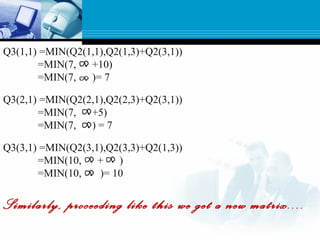
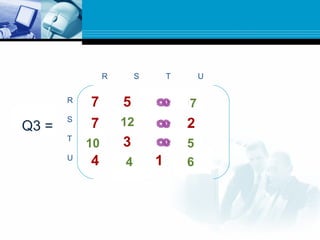
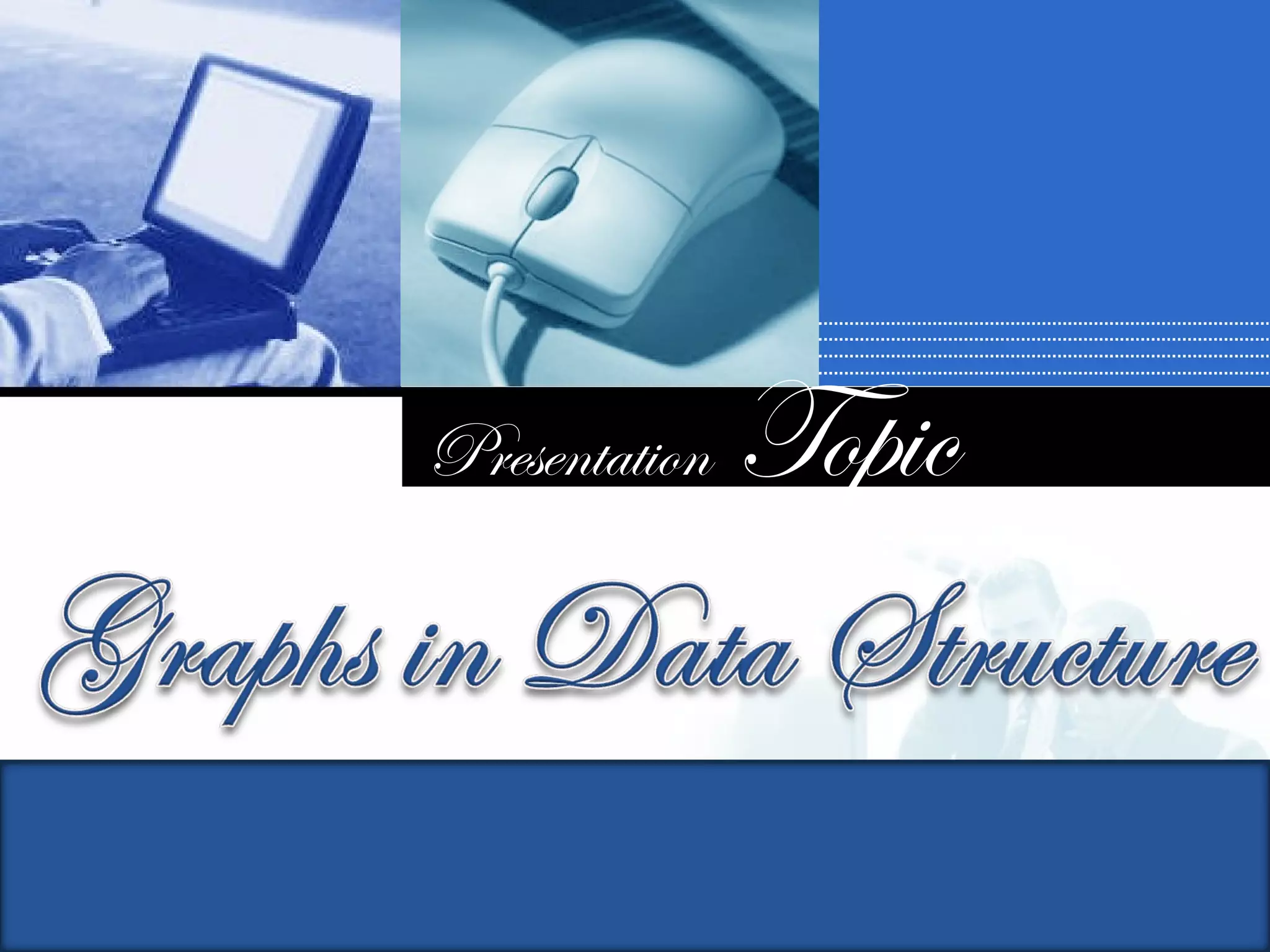
![ Path matrix P tells us whether or not there are paths
between the nodes.
Now we want to find a matrix Q which tell us the lengths of
the shortest paths between the nodes or a matrix Q=(qij)
where
qij= length of shortest path from vi to vj.
Here we define a sequence of matrices Q1,Q2,…..Qm
defined as
Qk[i,j]= the smaller of the length of the preceding paths from
vi to vj or the sum of the lengths of preceeding paths from vi
to vk and from vk to vj.
Qk[i,j]=min(Qk-1[i,j],Qk-1[i,k]+Qk-1[k,j])](https://image.slidesharecdn.com/graph-150531095324-lva1-app6892/85/Graph-44-320.jpg)