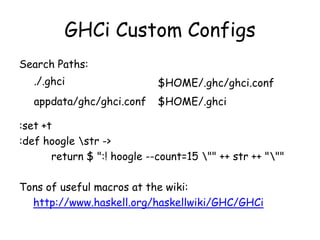
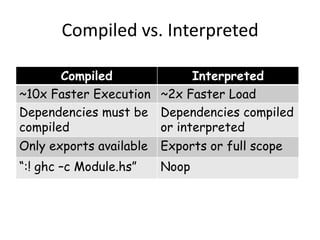
This document discusses using GHCi, Haskell's interactive environment, more effectively. It provides tips on allowing multi-line definitions, showing types, executing Haskell code, and setting up GHCi. It also covers loading and reloading modules, compiled vs interpreted code, controlling GHCi scope, debugging basics like breakpoints, and advanced techniques like time travel debugging.











![Review: Debugging Basics
:set stop :list
:break [<id>] or [<module?> <line?> <col?>]
:show breaks
:delete <breakpoint_id|*>
:step <expr?> / :steplocal / :stepmodule
:abandon / :continue
:print <id> / :force <id>](https://image.slidesharecdn.com/gchi-130619115108-phpapp02/85/GHCi-More-Awesome-Than-You-Thought-14-320.jpg)


