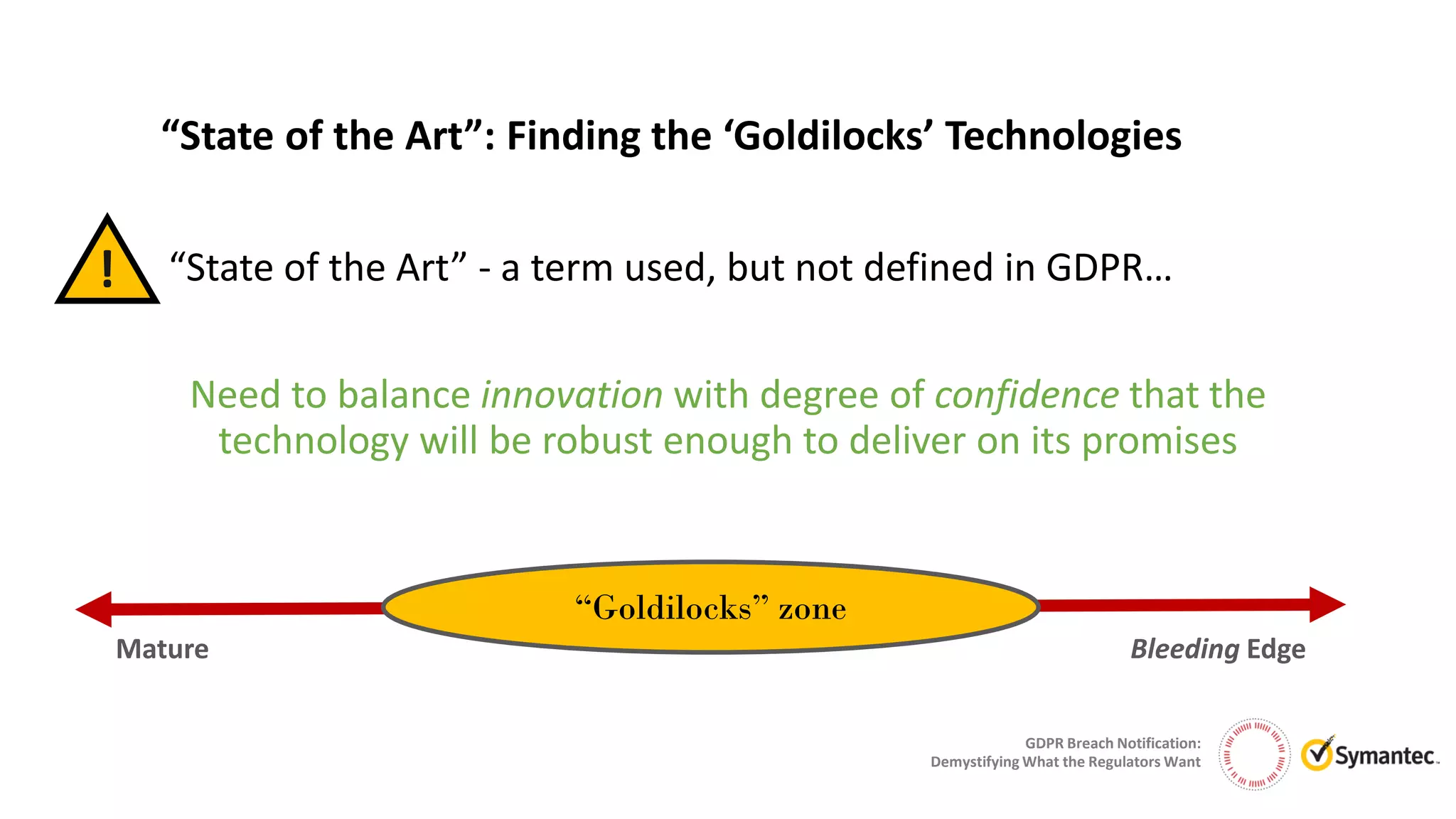
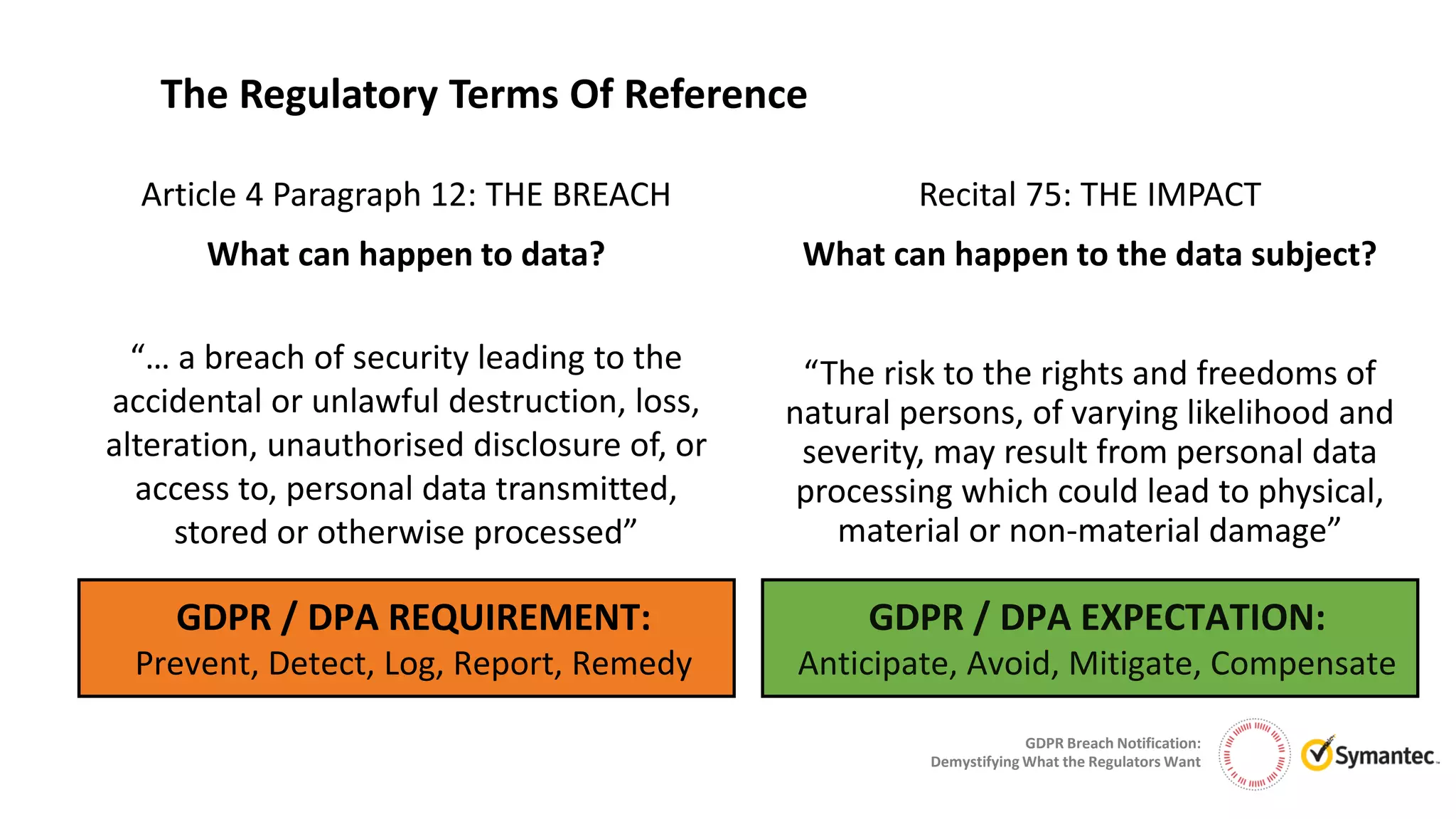
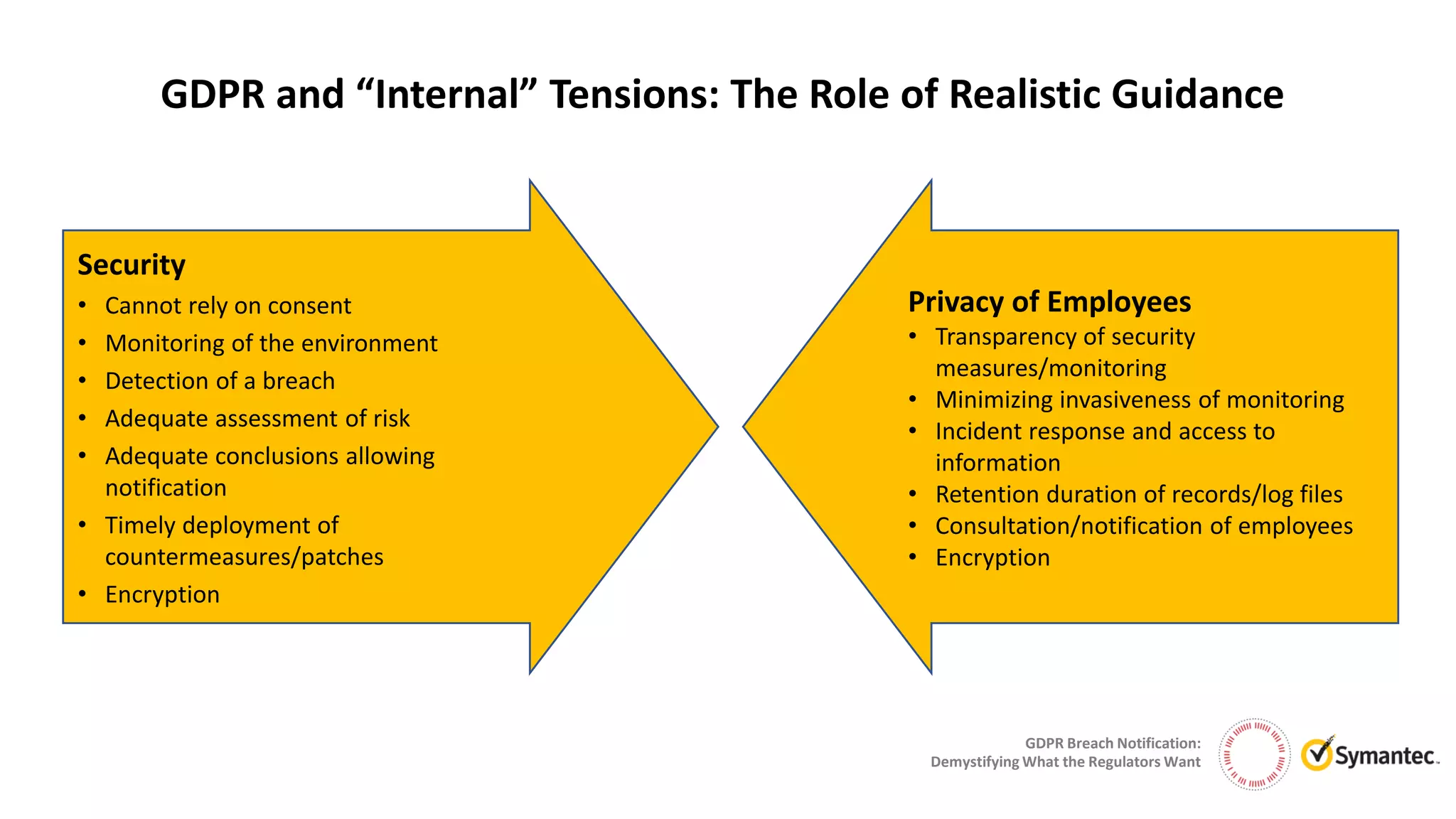
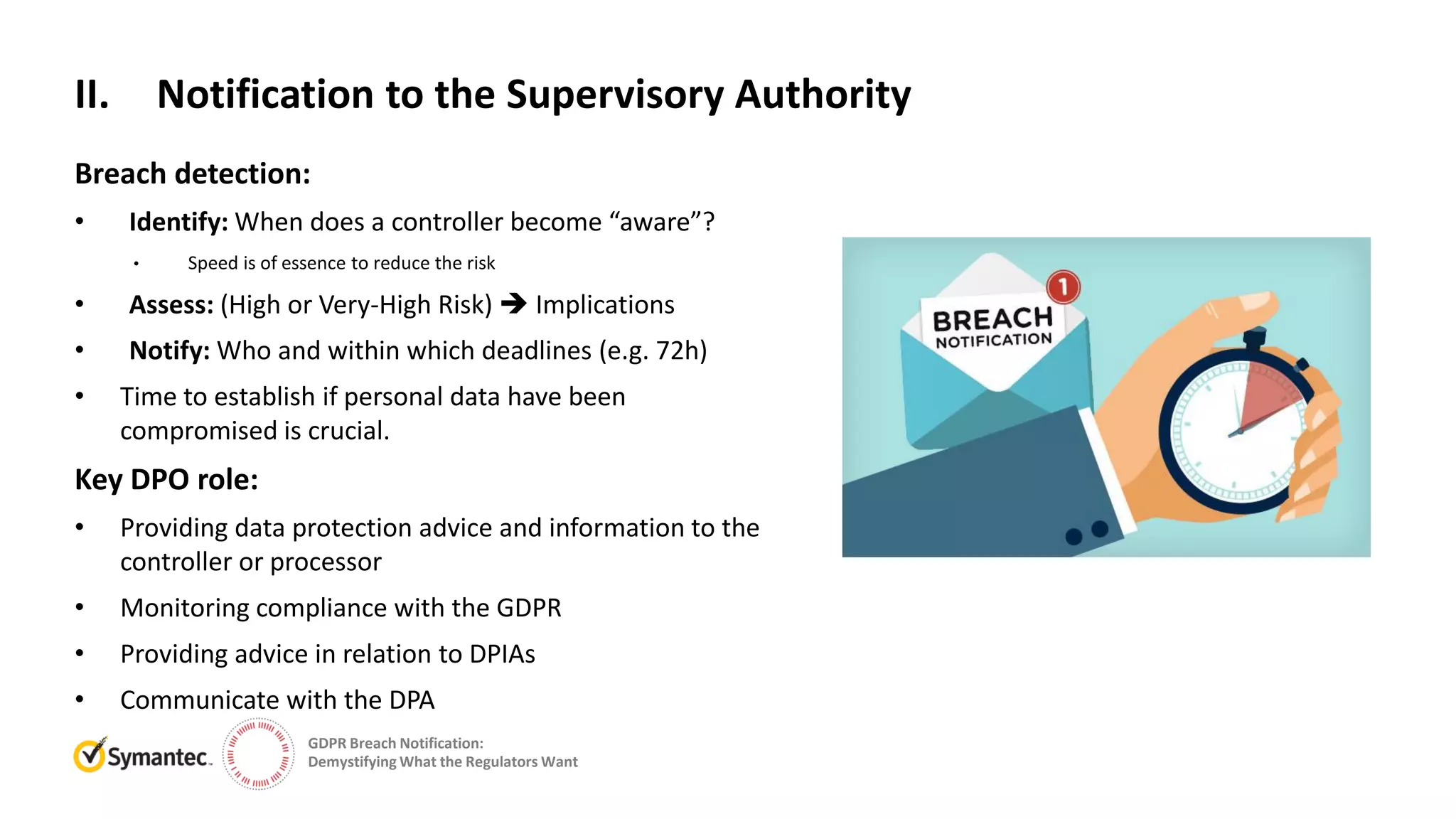
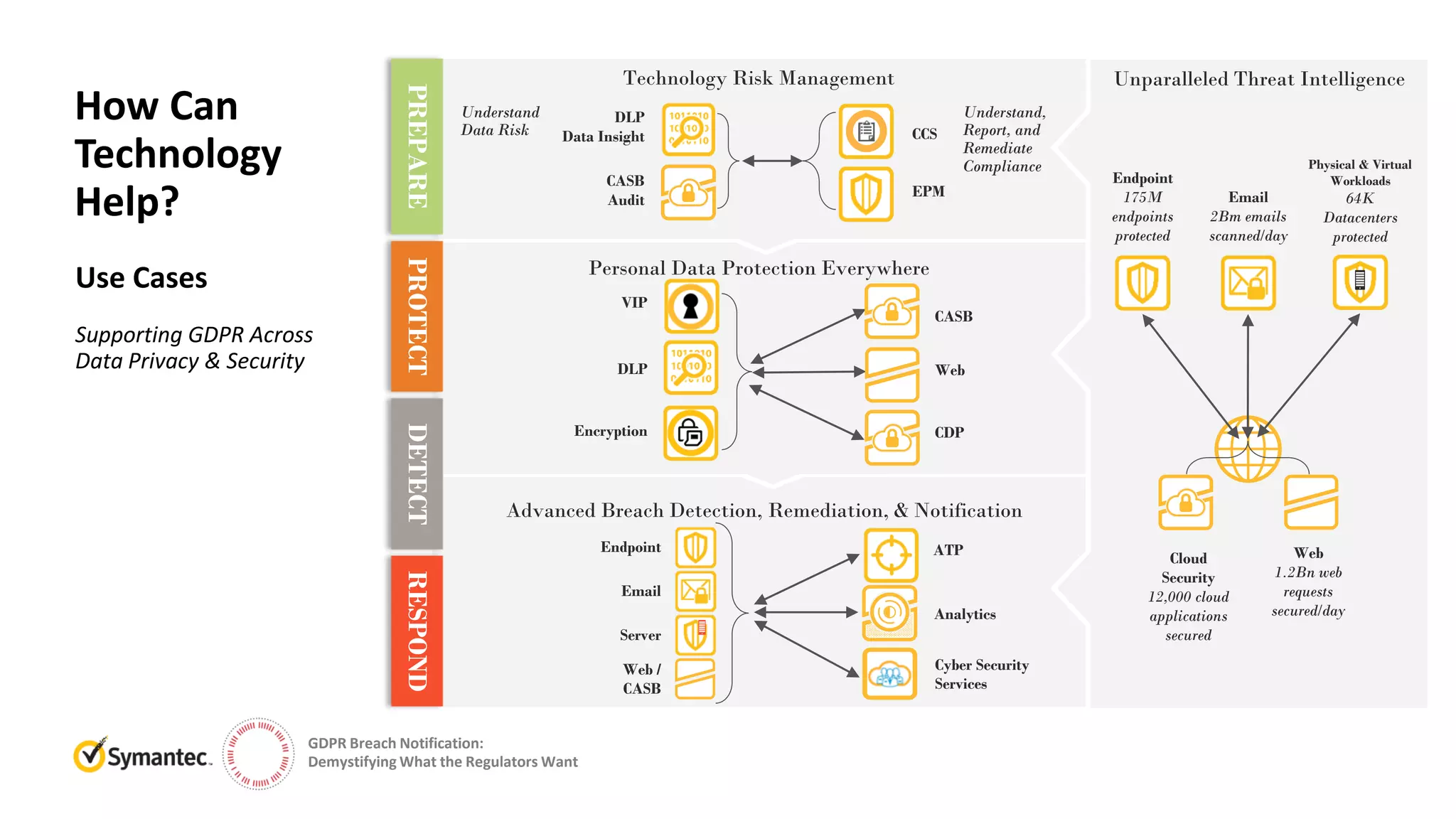
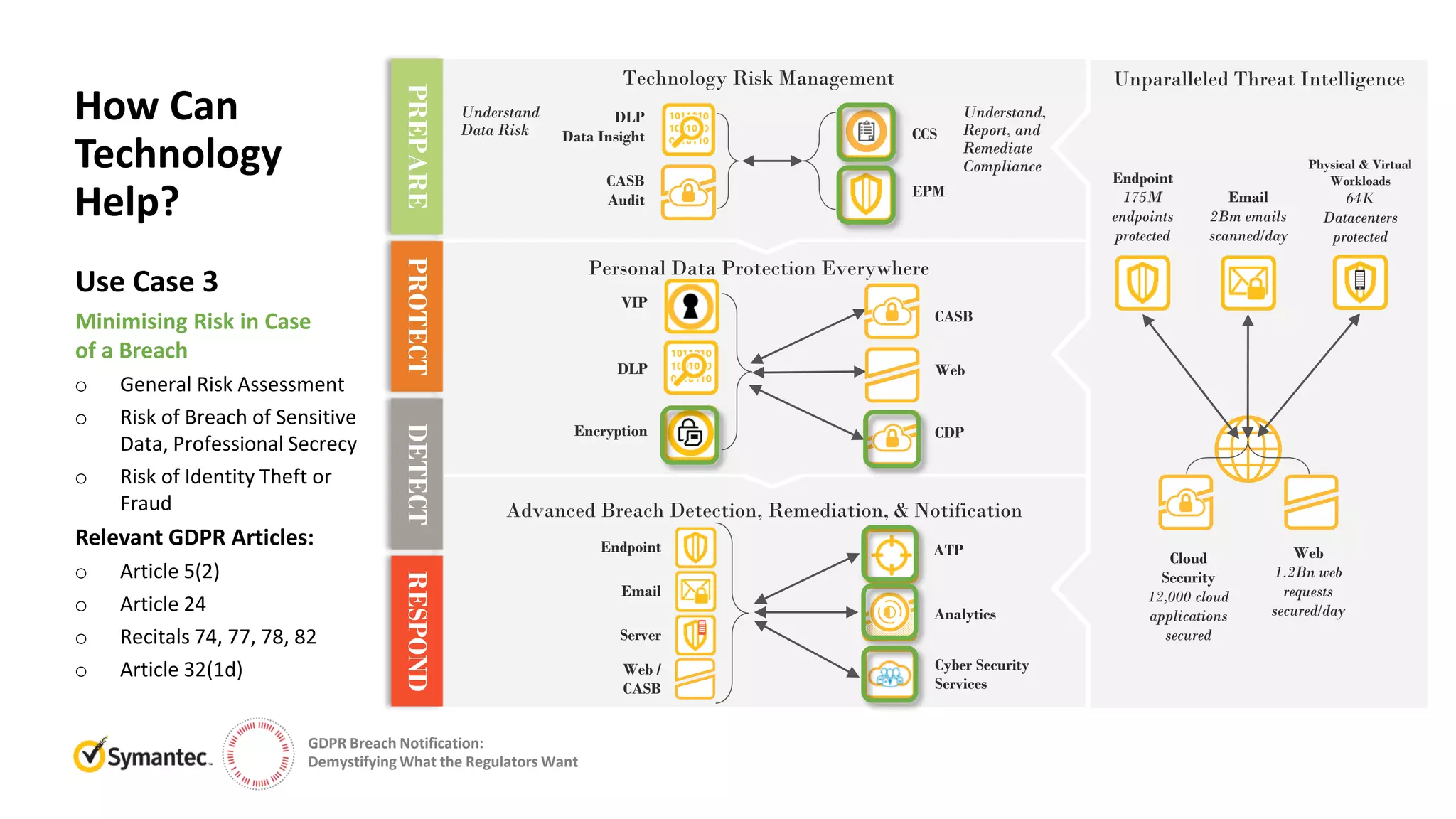
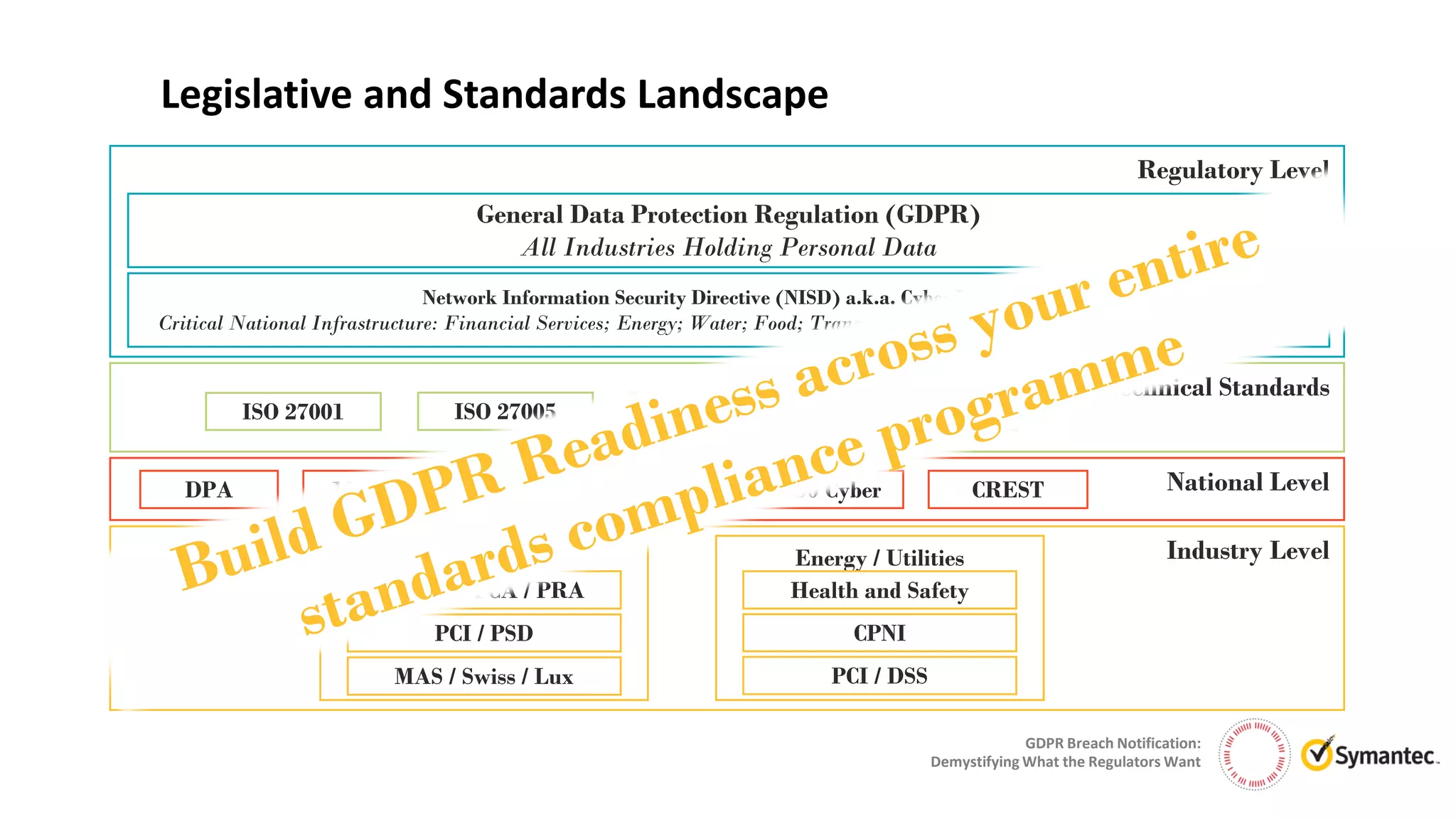
The document discusses the intricacies of GDPR breach notification, emphasizing that it's an ongoing process rather than a one-time event. It outlines the requirements for breach detection, assessment, and notification, highlighting the importance of cybersecurity and appropriate measures to mitigate risks. It also addresses the role of technology, organizational protocols, and the responsibilities of data controllers in ensuring compliance with GDPR regulations.