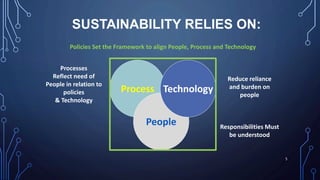
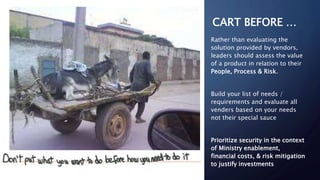
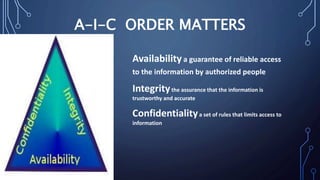
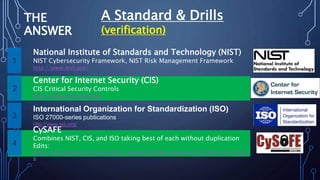
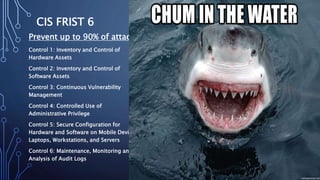
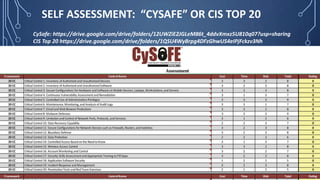
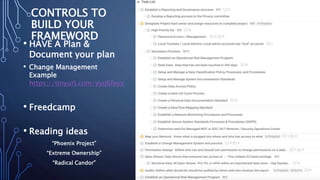
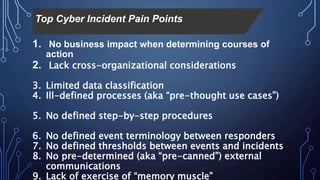
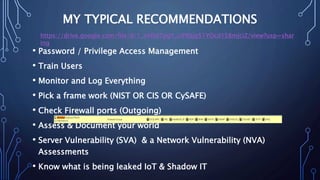
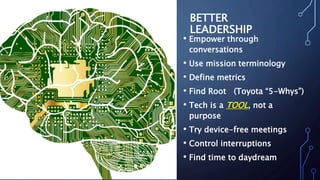
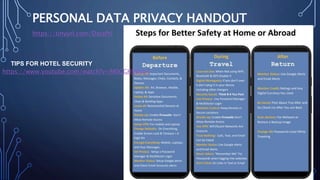
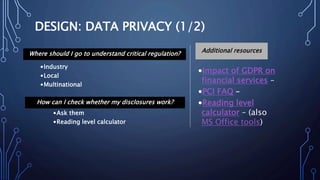
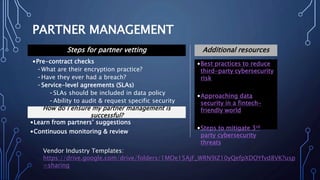
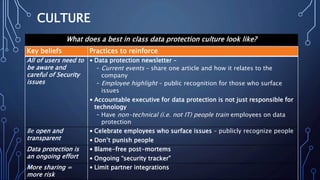
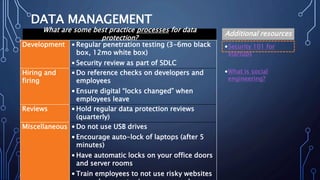
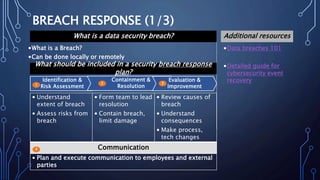
The document provides legal disclaimers and information about sustainable cybersecurity practices. It discusses starting cybersecurity at the administration level by making it cultural rather than technical, based on needs rather than vendor features, iterative and continuous. It also discusses establishing a data protection steering committee and reducing reliance on people by ensuring responsibilities are understood and policies and processes are documented. The document provides recommendations on cybersecurity frameworks, controls, and best practices.