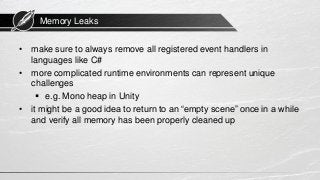
The document discusses techniques for debugging and performance optimization in game programming, emphasizing the need to start debugging immediately and avoid premature optimization. It covers various tools and strategies for tracking down and fixing bugs, as well as identifying performance bottlenecks related to GPU, CPU, and memory. Additionally, it highlights the importance of profiling before optimization and offers advice on managing memory leaks.
![Stack Traces
Object reference not set to an instance of an object
at LifeApplication.Initializer.CreateManagers () [0x00488] in
Initializer.cs:481
at LifeApplication.Initializer.OnLoad () [0x00016] in
Initializer.cs:235
8 / 55](https://image.slidesharecdn.com/gameprogramming-debuggingperformanceoptimization-160627195313/85/Game-Programming-13-Debugging-Performance-Optimization-8-320.jpg)