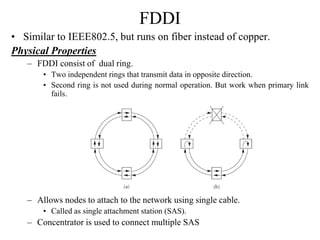
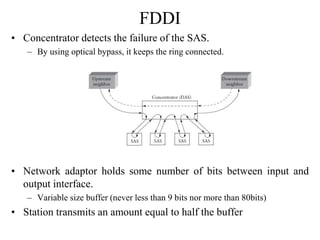
FDDI is a fiber optic network similar to IEEE 802.5 but uses fiber cables instead of copper. It uses a dual ring topology with two independent rings transmitting in opposite directions to provide redundancy in case the primary link fails. Nodes can attach to the network via a single cable using a single attachment station concentrator. The timed token protocol is used to ensure fair access to the network and maintains a target token rotation time to prevent latency.