Carmen Alcivar completed a lab assignment for her Foundations of Information Assurance course at Northeastern University. The assignment involved attacking a vulnerable web application and database. She performed tests like SQL injection and cross-site scripting attacks. Carmen provided screenshots and explanations of her results. She demonstrated techniques for discovering database structure and vulnerabilities. Overall, the assignment aimed to help Carmen learn how to identify security issues through penetration testing before software is deployed.


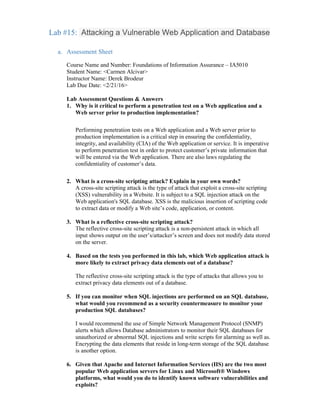
![I could search the CVE listing using the keyword Apache to find all known
Apache vulnerabilities and exploits. This allows to include all software patches
and security patches on the production Web servers to remediate critical and
major software vulnerabilities before the application is released.
7. What can you do to ensure that your organization incorporates penetration
testing and Web application testing as part of its implementation
procedures?
Penetration testing should be part of the policy. The organization's security policy
should dictate that no production Web application can be implemented without
proper penetration testing and security hardening.
8. What is the purpose of setting the DVWA security level to “low” before
beginning the remaining lab steps
The low setting mimics a vulnerable Web application. Only a vulnerable system
can be attacked.
9. As an ethical hacker, once you’ve determined that a database is injectable,
what should you do with that information?
As an ethical hacker, I should recommend specific countermeasures for
remediating the vulnerabilities and eliminating the exploits. Once I have
determined that a database is injectable
b. Challenge Question
c. Screenshots:
Part 2:
[Deliverable Lab Step 5] screen shot showing the exposed vulnerability](https://image.slidesharecdn.com/b53f162b-1944-4810-8640-95fe7ee5d75e-160413172314/85/example-of-sql-injection-4-320.jpg)
![1. [Deliverable Lab Step 8] screen shot showing cross-site scripting attacks in the High
setting. It does not go through.](https://image.slidesharecdn.com/b53f162b-1944-4810-8640-95fe7ee5d75e-160413172314/85/example-of-sql-injection-5-320.jpg)


![[Deliverable Lab Step 18]: a screen capture showing the user information for the user
name that is currently being used to make queries on the server.
[Deliverable Lab Step 20 ] a screen capture showing hash for the user to the backend
database. Hashing in a database allows the creation of an index number. This facilitates the
search of a record later on. http://www.webopedia.com/TERM/H/hashing.html](https://image.slidesharecdn.com/b53f162b-1944-4810-8640-95fe7ee5d75e-160413172314/85/example-of-sql-injection-8-320.jpg)
![Part 4:
[Deliverable Lab Step 8] screen capture showing the contents of the testing1.txt file](https://image.slidesharecdn.com/b53f162b-1944-4810-8640-95fe7ee5d75e-160413172314/85/example-of-sql-injection-9-320.jpg)