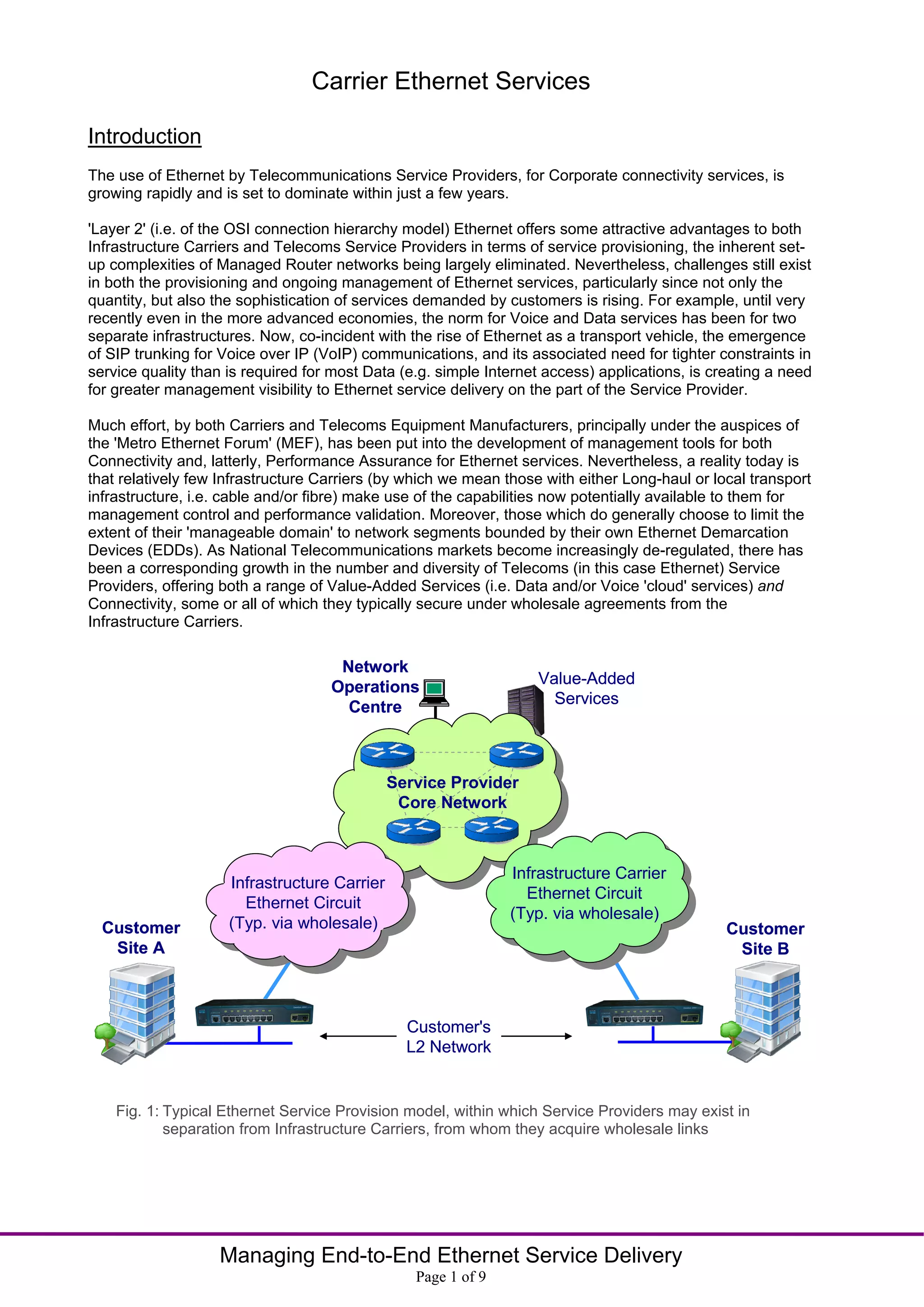
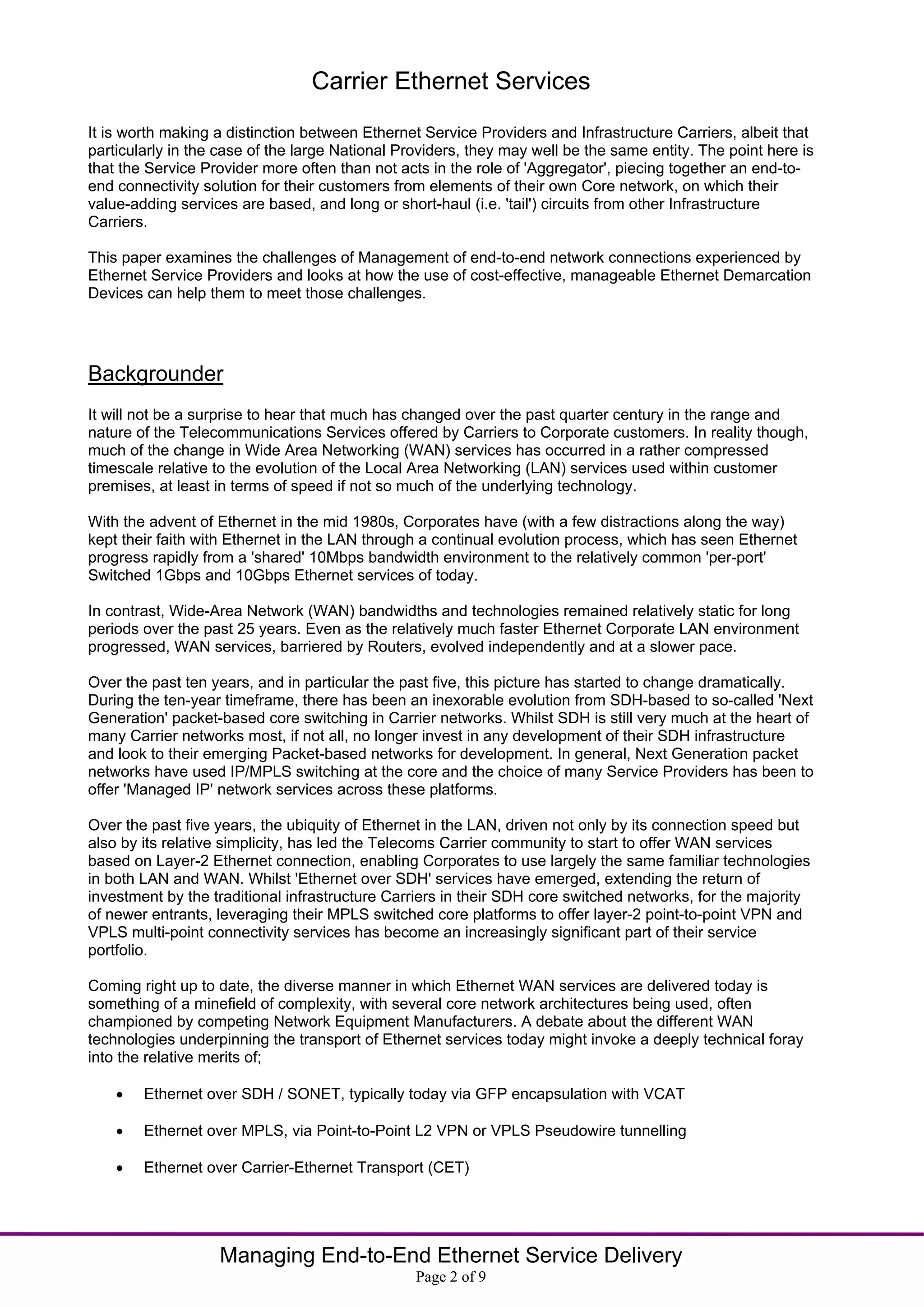
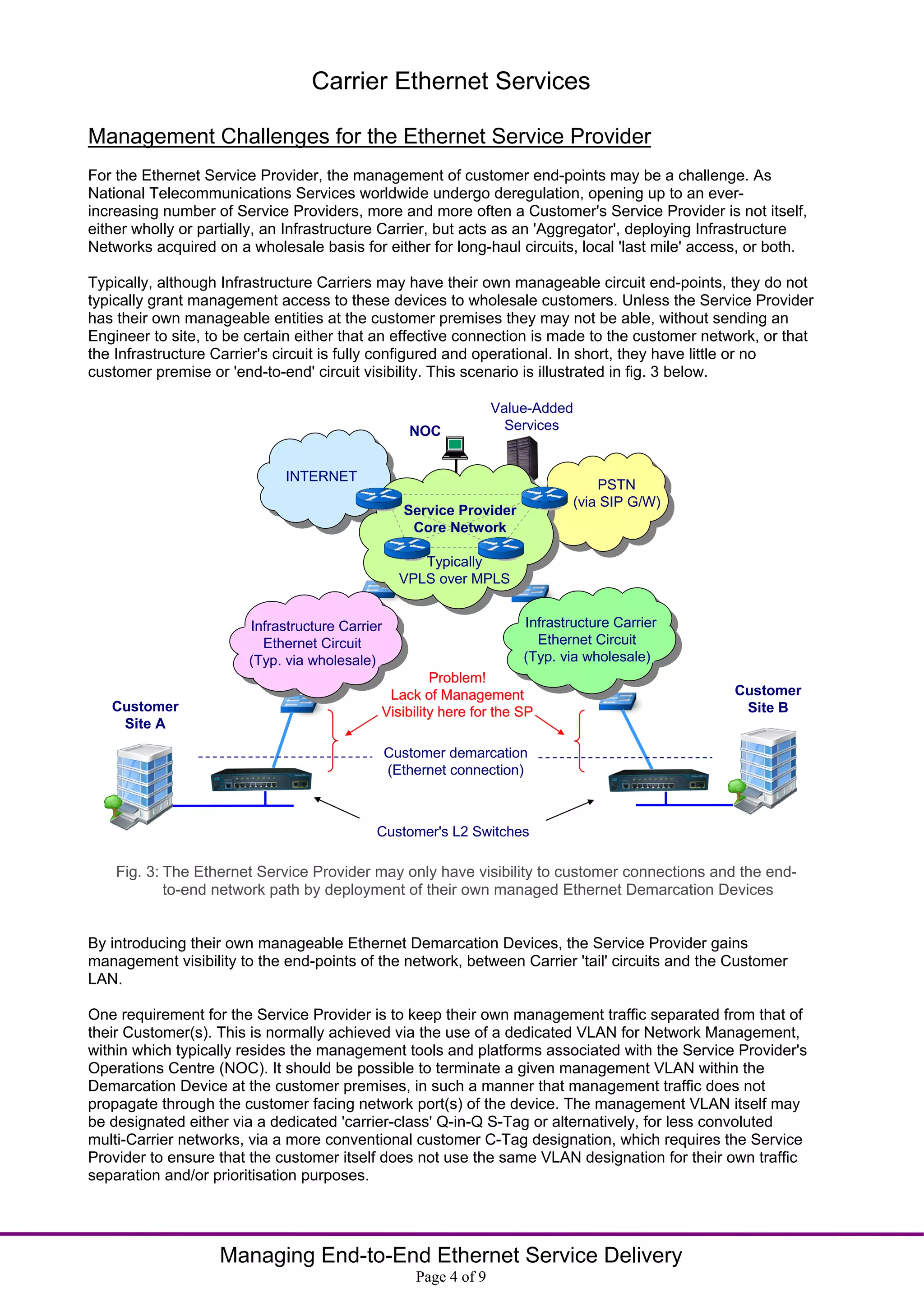
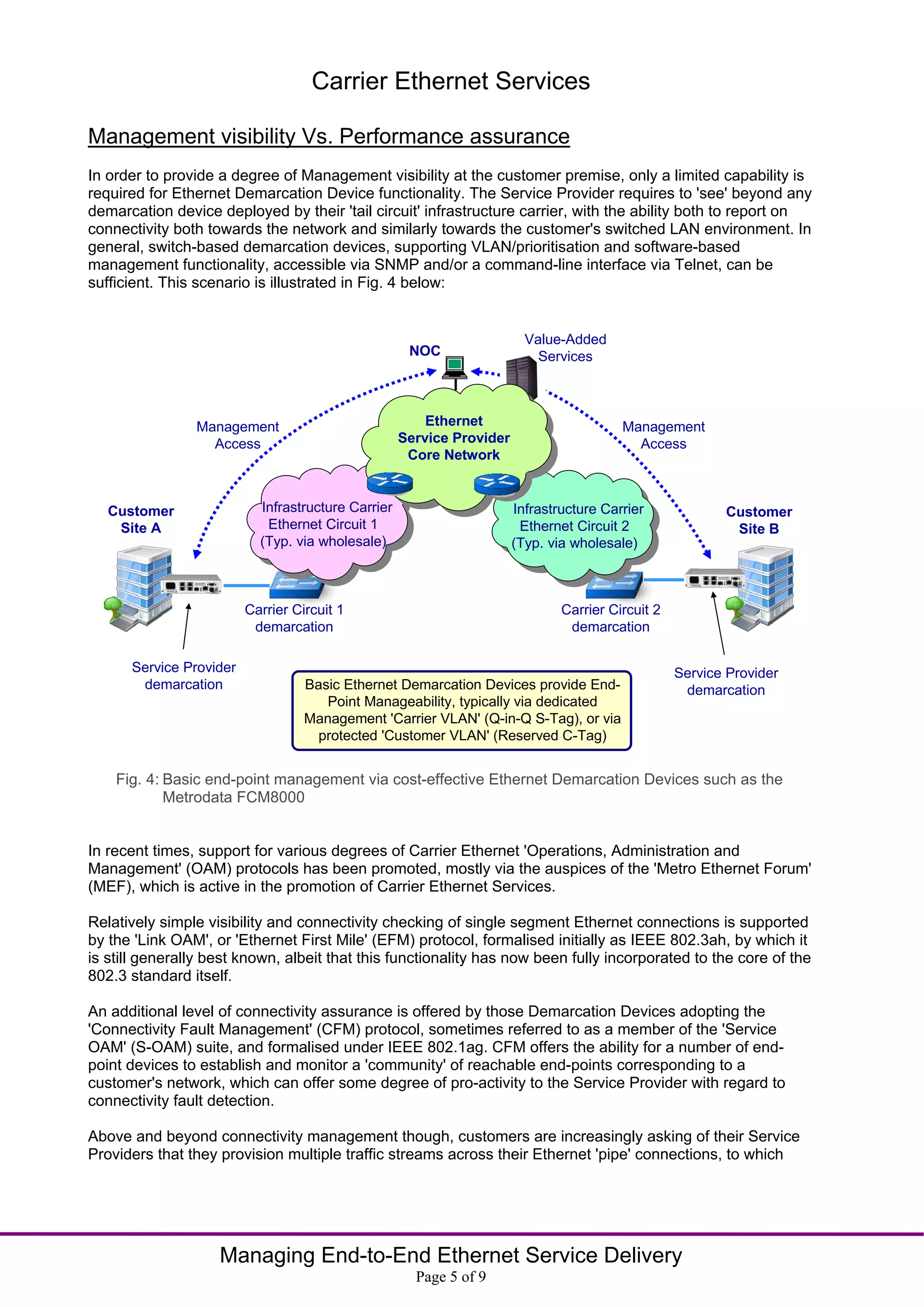
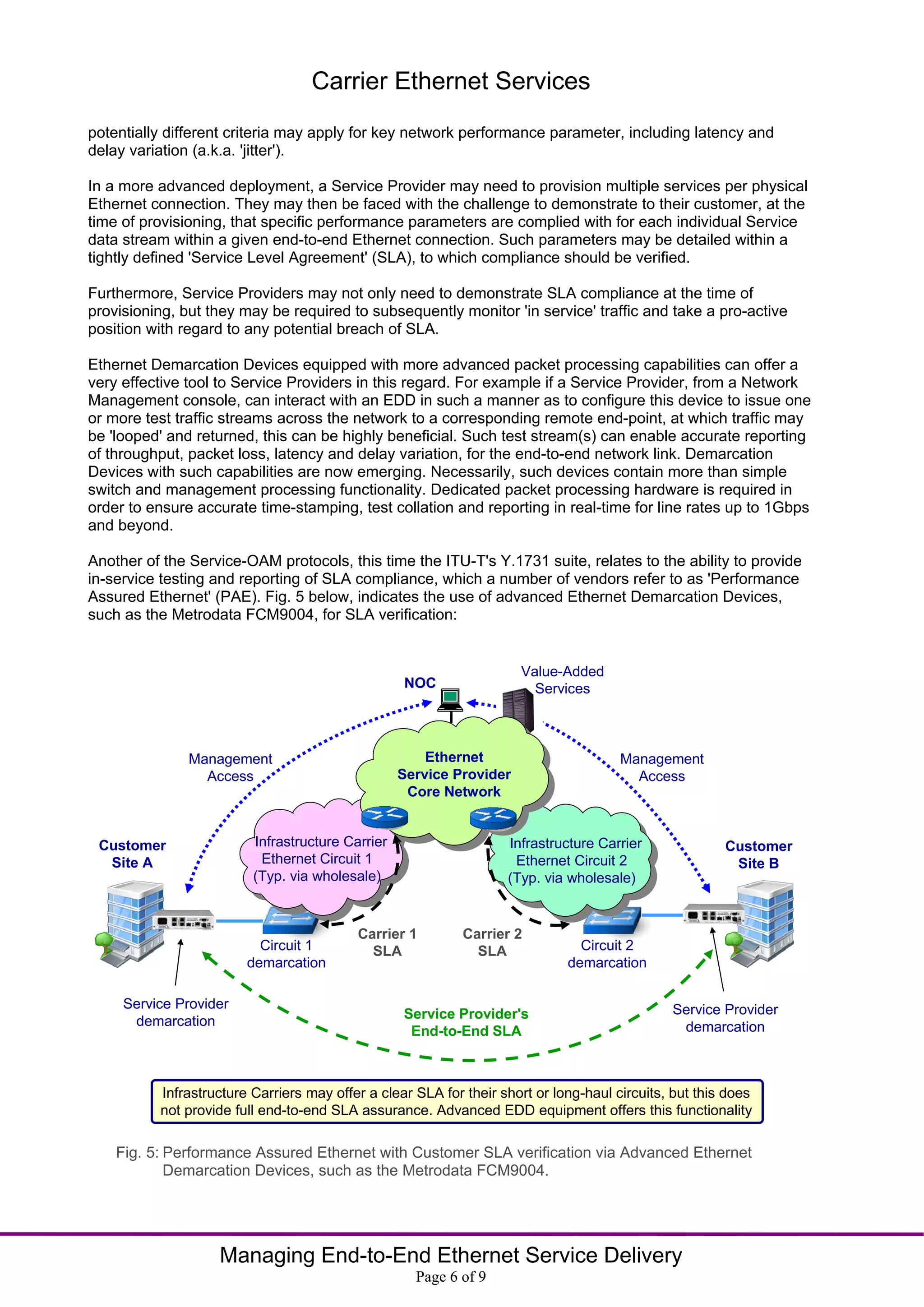
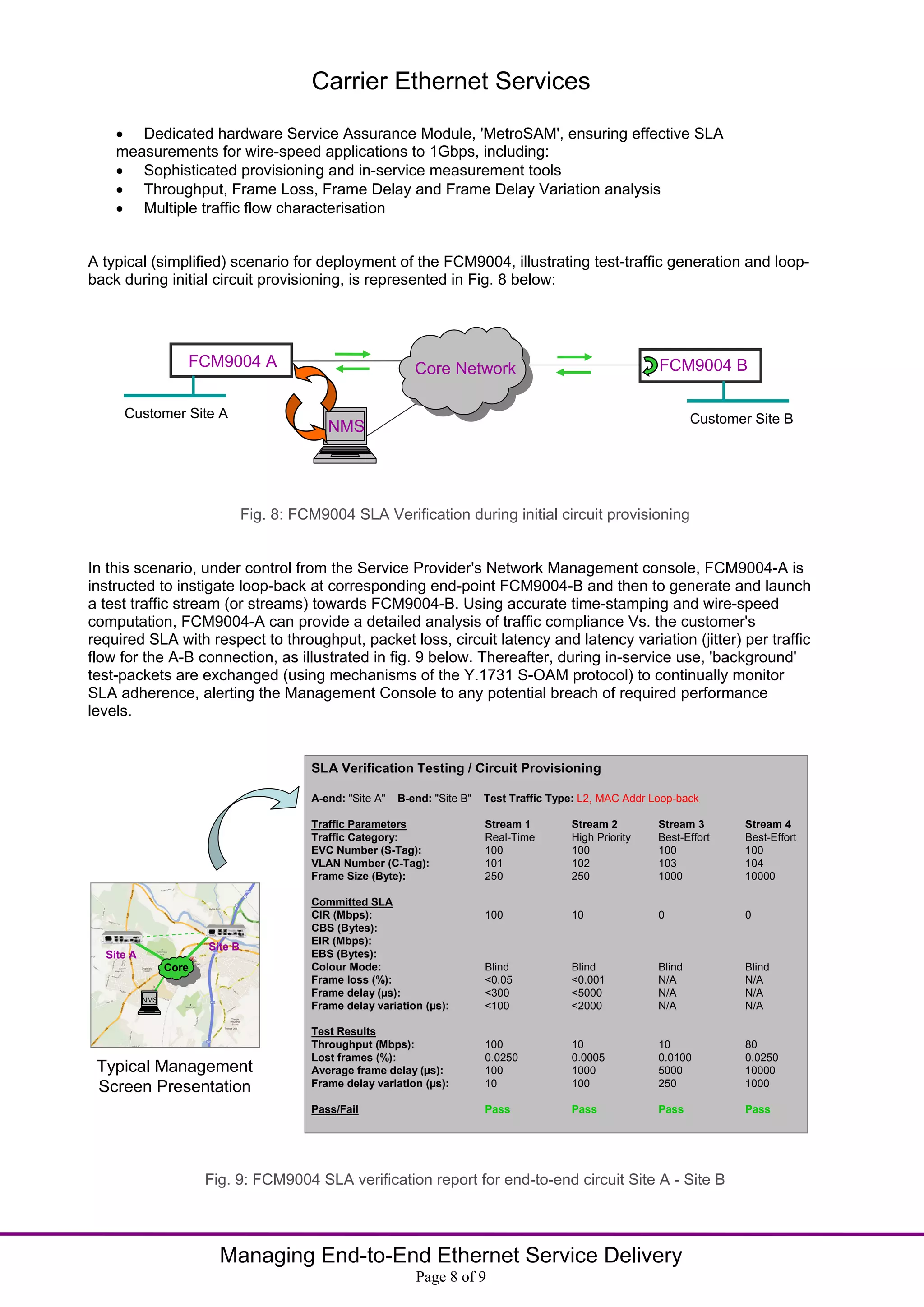
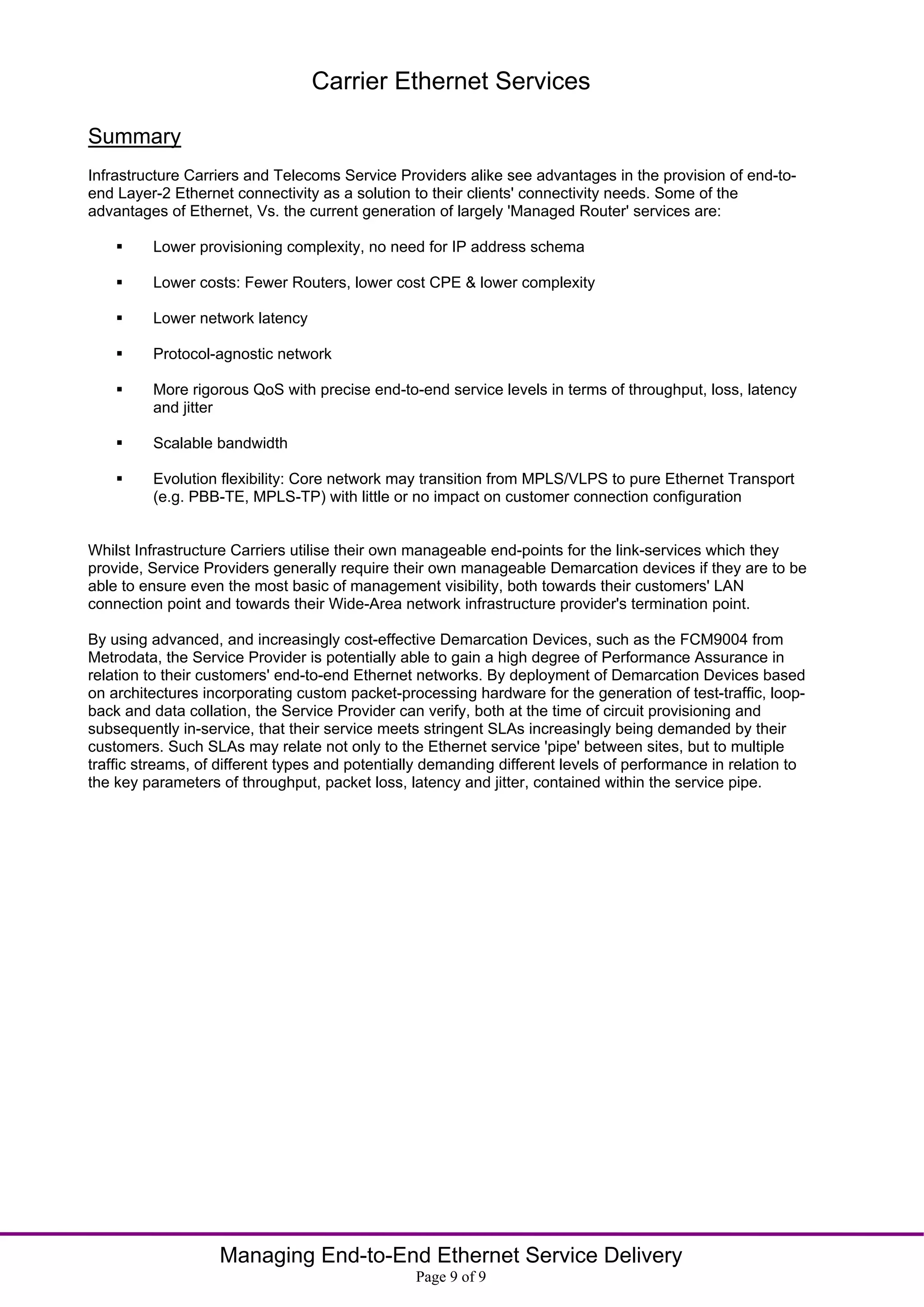
The document discusses the rising demand for carrier Ethernet services among telecommunications providers, highlighting the transition to Layer 2 Ethernet for corporate connectivity. It emphasizes the need for effective management tools, particularly Ethernet demarcation devices (EDDs), to ensure service level agreement (SLA) compliance and improve visibility across end-to-end connections. Additionally, it addresses the complexities of managing multiple service flows and the technological evolution of WAN services over the past decades.