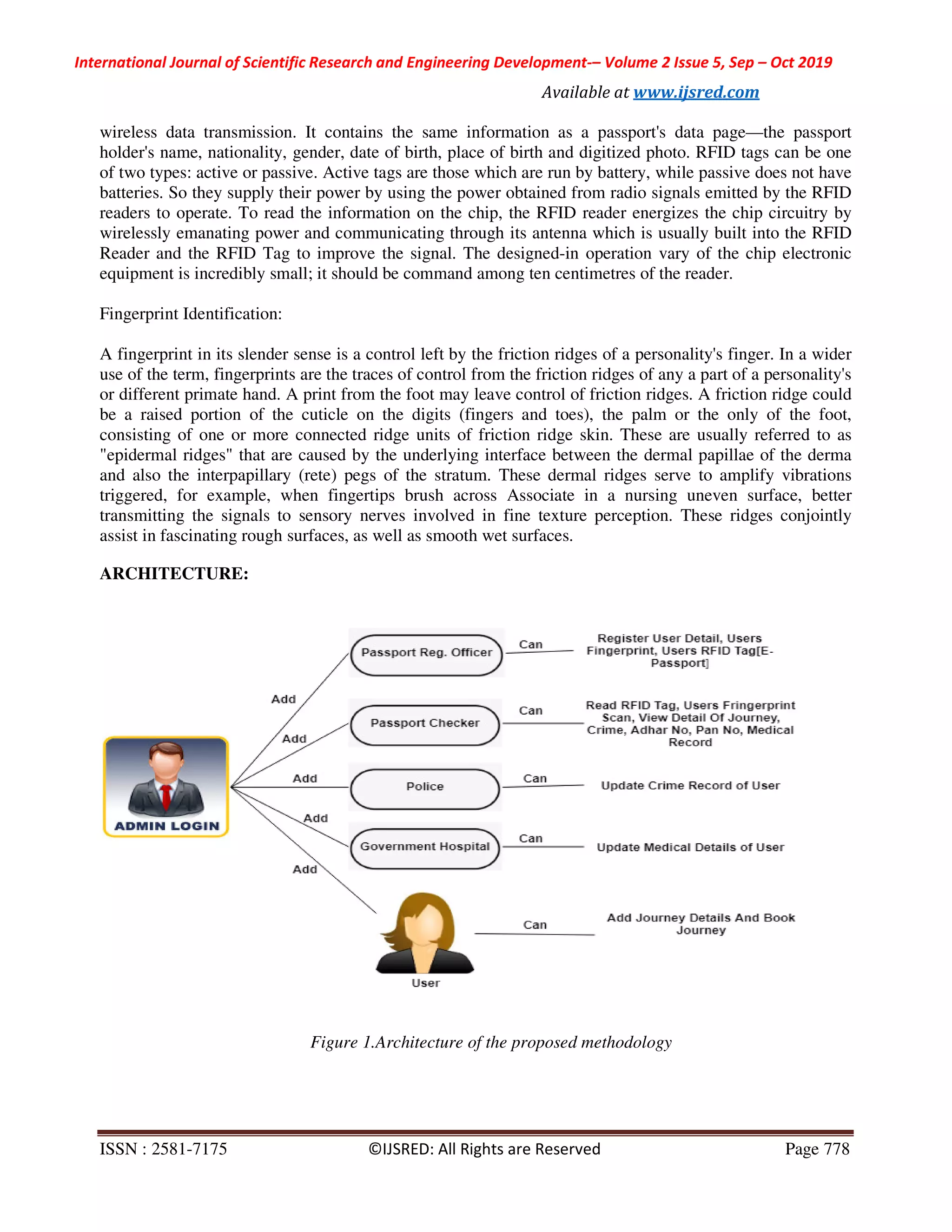
This document summarizes a research paper on using RFID tags and fingerprint sensors in electronic passports (e-passports). The paper analyzes how embedding biometric fingerprints on RFID tags in e-passports can improve security by allowing for more accurate identification of passport holders. It discusses how e-passports work by storing the holder's biometric and personal data on an RFID chip. The paper also presents the architecture of an e-passport system using RFID technology and fingerprint sensors to identify individuals and limit the use of fake documents. It concludes that combining RFID and biometrics can enhance the security of e-passports against fraud.
![International Journal of Scientific Research and Engineering Development-– Volume 2 Issue 5, Sep – Oct 2019
Available at www.ijsred.com
ISSN : 2581-7175 ©IJSRED: All Rights are Reserved Page 779
V. CONCLUSION
The project has analysed the key current and
potential uses of RFID in distinguishing documents.
The vital feature of this project is security and time
wastage concerned invalidation of passports. The
inclusion of RFID technology into computer-
readable documents can improve their lustiness
against fraud.
ACKNOWLEDGMENT
We are very great thankful to our guide Prof.
Jayshree Shinde, project Co-ordinatar Prof.
Prashant kale & H.O.D Dr.(Prof.) Nilesh
Wankhede, Computer Department & Library, Late
G.N. Sapkal College of Engineering for guidance
and advice which helped to improve the present
Paper and for reading the paper and giving
valuable suggestions to improve the paper.
REFERENCES
[1] A.K.Jian, “Biometrics personal identification in networked society”
Technical report 1999.
[2] HOME AFFAIRS JUSTICE (2006), “EU standard specifications for
security features and biometrics in passports and travel documents”,
Technical report, European Union.
[3] ICAO (2006), “Machine-readable travel documents”, Technical
report, ICAO.
[4] KLUGLER, D. (2005), “Advance security mechanisms for machine
readable travel documents, Technical report”, Federal Office for
Information Security (BSI), Germany.
[5] ICAO, “Machine-Readable Travel Documents”, Part 1 Machine
Readable Passports, 5th Edition, 2003
[6] Riscure Security Lab, “E-passport privacy attack”, Cards Asia
Singapore, April 2006.
[7] D. Wagner, “Security and privacy problems in e-passports”,
Cryptology ePrint, Report 2005.
[8] ICAO, “Biometrics Deployment of Machine Readable Travel
Documents”, Version 2.0, May 2004.](https://image.slidesharecdn.com/ijsred-v2i5p68-200209150846/75/E-Passport-Using-RFID-Tag-and-Finger-Print-Sensor-4-2048.jpg)