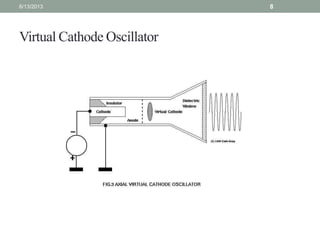
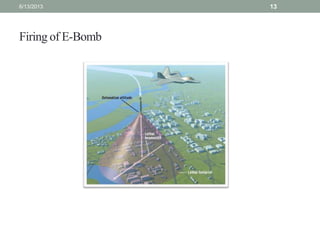
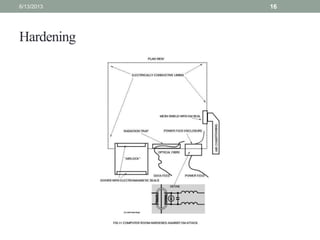
This document discusses electromagnetic bombs (E-bombs) that use electromagnetic pulses (EMPs) to damage electrical systems over large areas with minimal physical destruction. It describes the basic principles of E-bombs and two technologies used to generate EMPs - flux compression generators and virtual cathode oscillators. The document outlines potential targets of E-bombs, methods of delivery, and defenses against EMP attacks. It argues that E-bombs could provide strategic advantages by disabling electronics without loss of life and reducing thresholds for air and missile strikes.