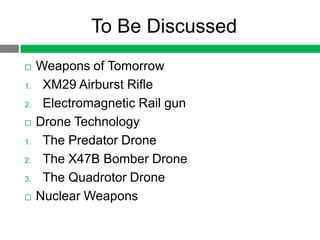
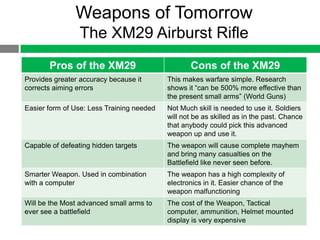
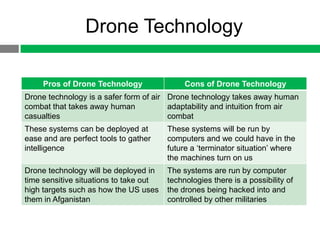
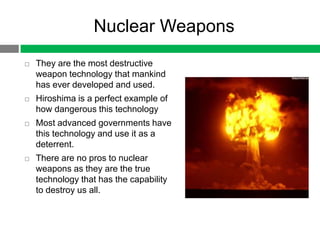
The document discusses emerging military technologies including the XM29 airburst rifle, electromagnetic rail gun, Predator and X47B drones, quadrotor drones, and nuclear weapons. It analyzes the pros and cons of each technology, noting their destructive capabilities but also their potential to cause harm if misused or hacked. The author argues that if these advanced weapons were used together, they could potentially destroy the planet.

![Weapons of Tomorrow
The XM 29 Airburst Rifle
This Modern Weapon Created
by OIWC [Object Individual
Combat Weapon] Began in Late
1986 (World Guns)
The weapon is used in
combination with a tactical
computer (fire control system)
and helmet mounted display
system.
The fire control system
automatically judges distances
of targets and will allow for
greater aiming errors (World
Guns)
http://www.youtube.com/watch?
v=XNdLFRhDhtk](https://image.slidesharecdn.com/mediapresentationproject-120807221901-phpapp01/85/Media-presentation-project-4-320.jpg)
![References
Adams, E. (2004, June 1). Electromagnetic Railgun. Retrieved from
http://www.popsci.com/scitech/article/2004-06/electromagnetic-railgun
Daily Mail. (2011, Sept 30). Rise of the machines: Navy’s first unmanned stealth drone
one step closer to aircraft carrier landing. Retrieved from
http://www.dailymail.co.uk/news/article-2043887/Navys-unmanned-stealth-drone-X-
47B-step-closer-aircraft-carrier-landing.html
Dmine45. (2007, Dec 1). Demonstration of the Navy Electromagnetic Rail Gun prototype
[Video file]. Retrieved from http://www.youtube.com/watch?v=4OqlTXwLG40
Hamburg, D. (2012, July 16). Armed Quadrotors Are Coming. Retrieved from
http://www.popularmechanics.com/technology/military/planes-uavs/armed-
quadrotors-are-coming-10720086
Manjoo, F. (2012, March 5). I Love You, Killer Robots. Retrieved from
http://www.slate.com/articles/technology/technology/2012/03/quadrotor_drones_are_
amazing_and_cute_and_they_will_probably_destroy_us_all_.html](https://image.slidesharecdn.com/mediapresentationproject-120807221901-phpapp01/85/Media-presentation-project-13-320.jpg)
![References
Northrop Grumman media. (2011, Sept 29). X-47B UCAS Flight Test Highlights --
Summer 2011 [Video file]. Retrieved from
http://www.youtube.com/watch?feature=player_embedded&v=0Oq4qah5LQ0
Pravda. (2012, Jan 2). Americans get Closer to building weapon of the Future. Retrieved
from http://english.pravda.ru/science/tech/01-02-2012/120391-railgun-0/
The Dmel. (2010, May 21). Aggressive Maneuvers for Autonomous Quadrotor Flight
[Video file]. Retrieved from
http://www.youtube.com/watch?v=MvRTALJp8DM&feature=player_embedded
U.S. Air Force. (2012, Jan 5). MQ-IB PREDATOR. Retrieved from
http://www.af.mil/information/factsheets/factsheet.asp?id=122
World Guns. (n.d.). Alliant Techsystems / Heckler-Koch XM-29 SABR / OICW assault
rifle (USA). Retrieved from http://world.guns.ru/assault/usa/xm29-oicw-e.html
ytblows. (2007, Feb 13). XM29 [Video file]. Retrieved from
http://www.youtube.com/watch?v=XNdLFRhDhtk](https://image.slidesharecdn.com/mediapresentationproject-120807221901-phpapp01/85/Media-presentation-project-14-320.jpg)