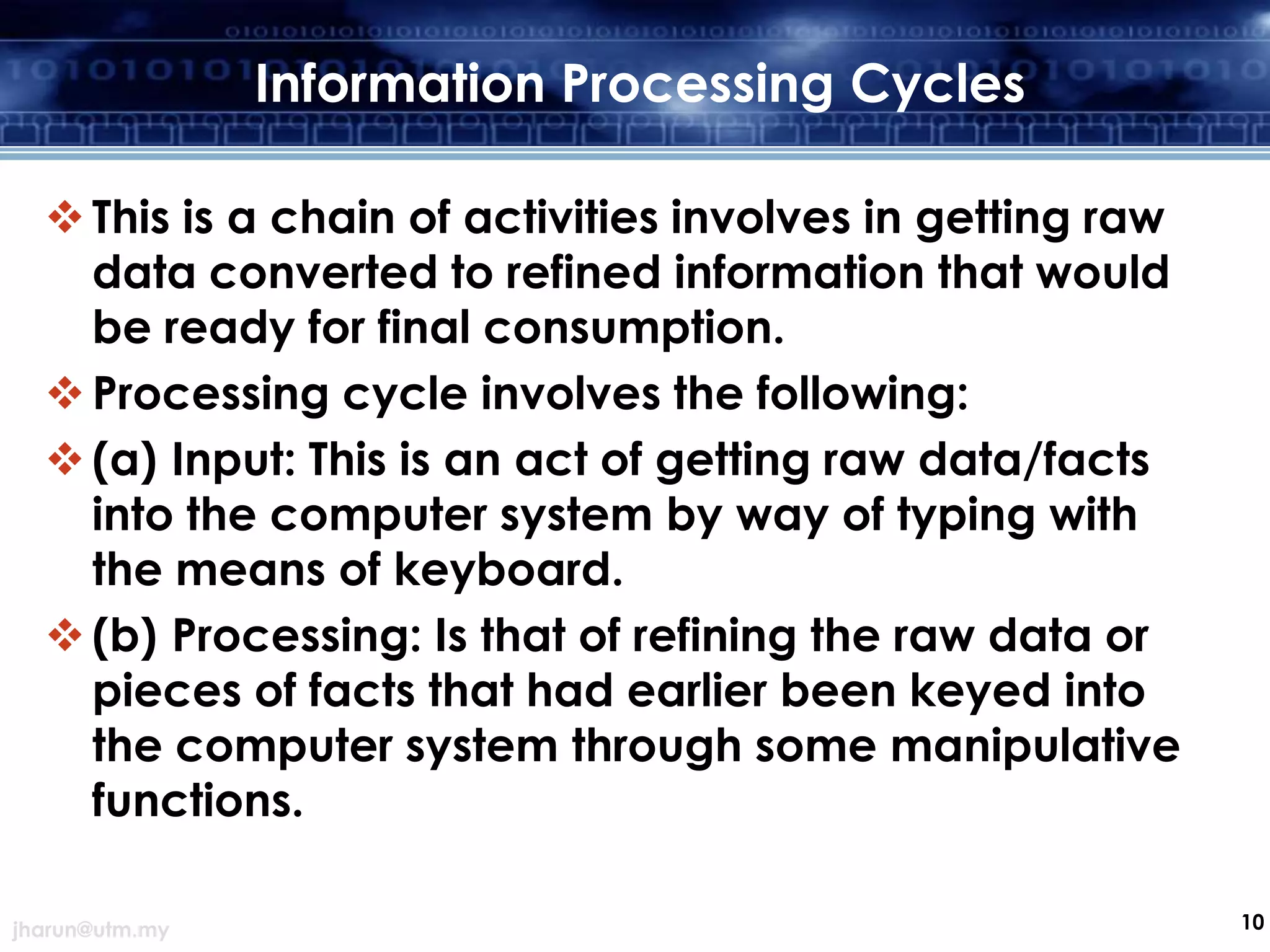
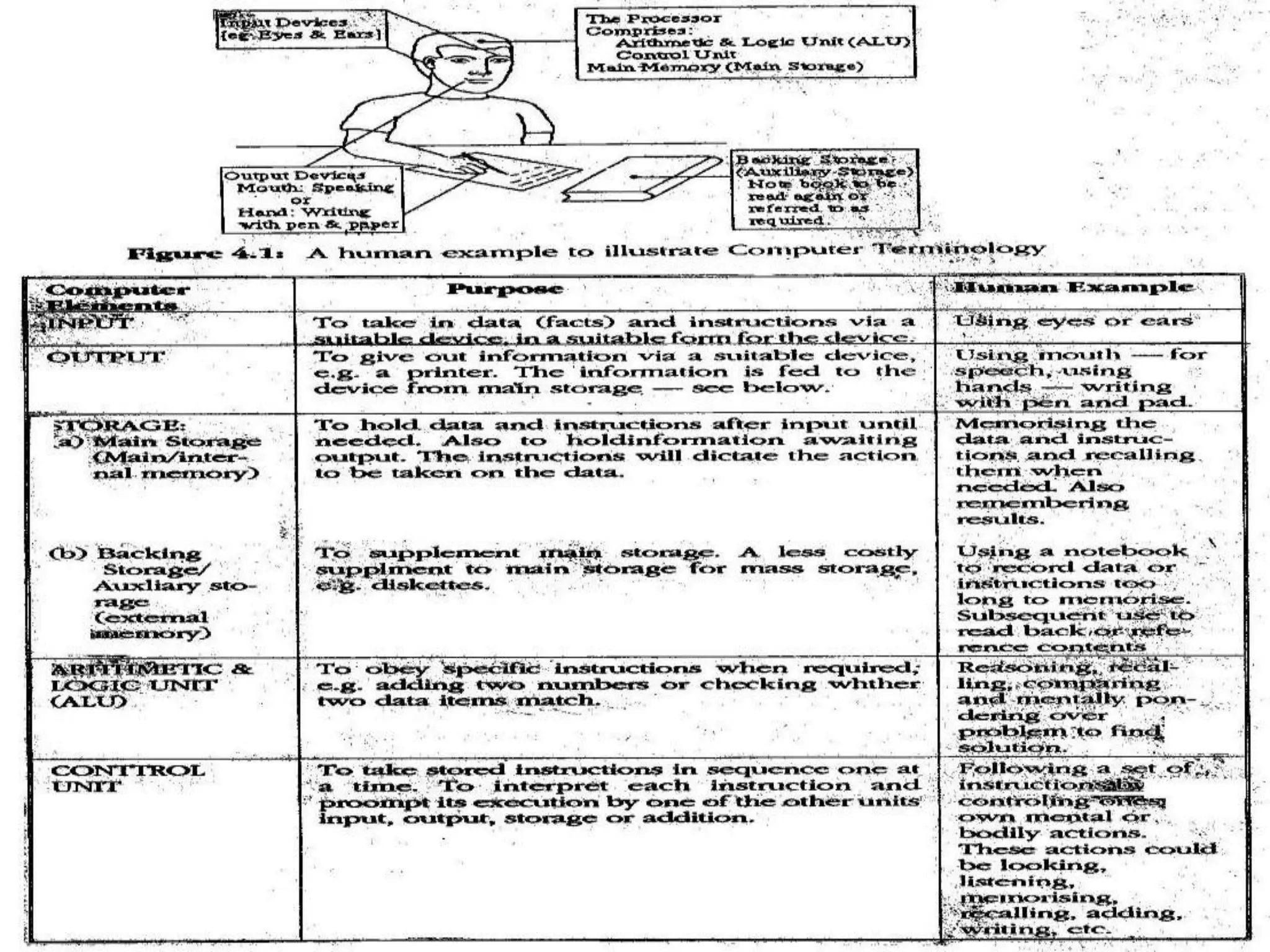
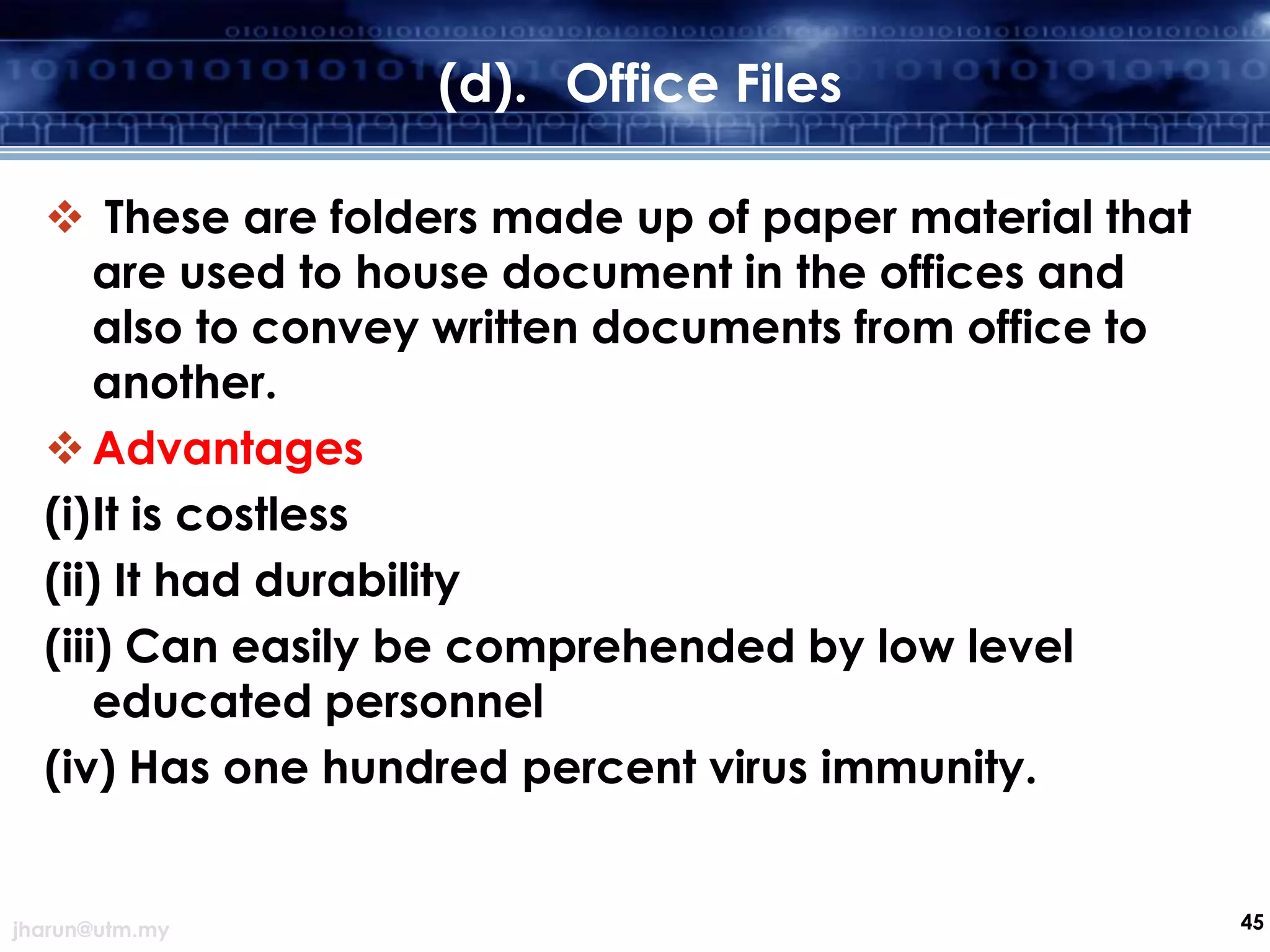
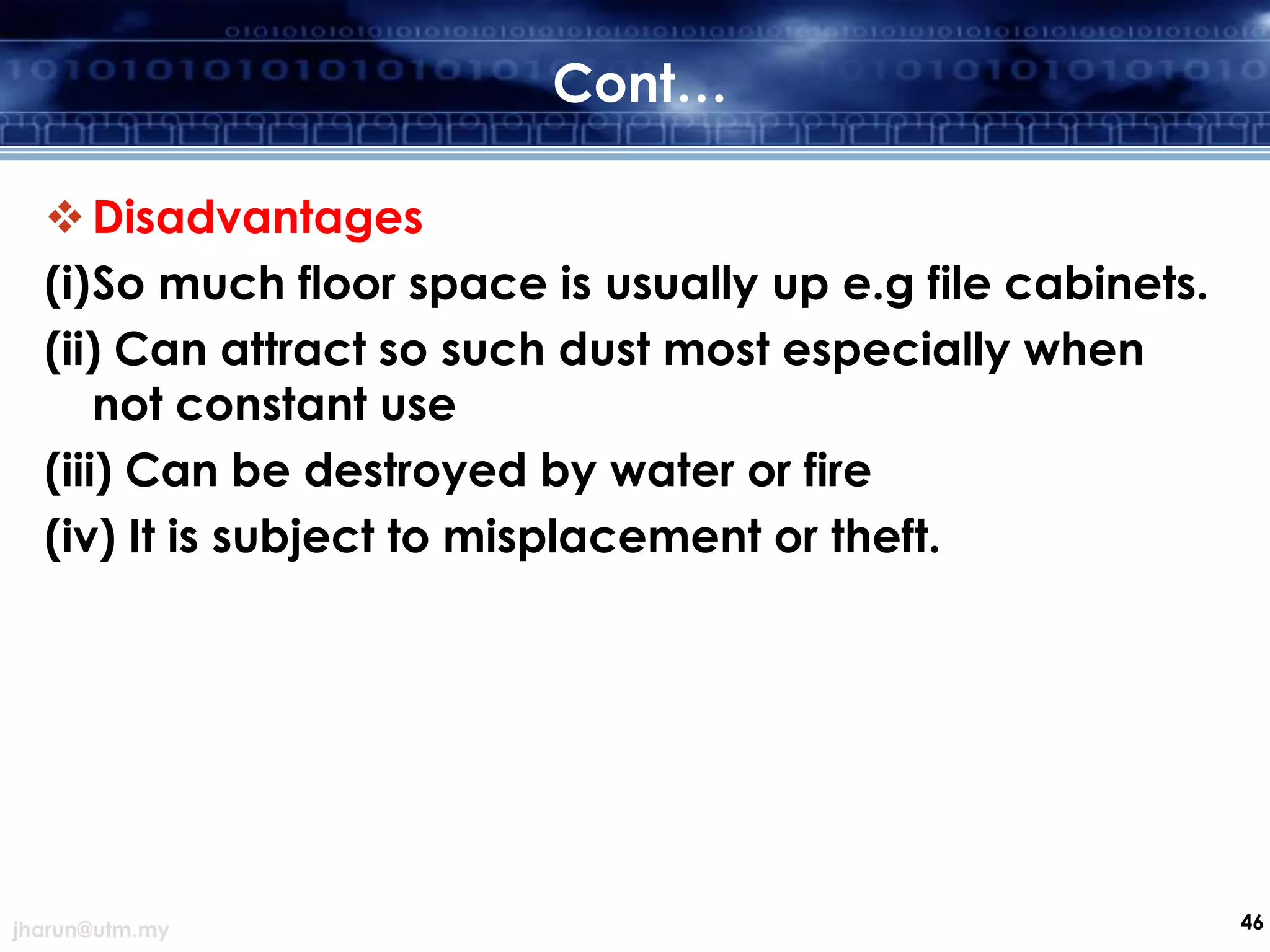
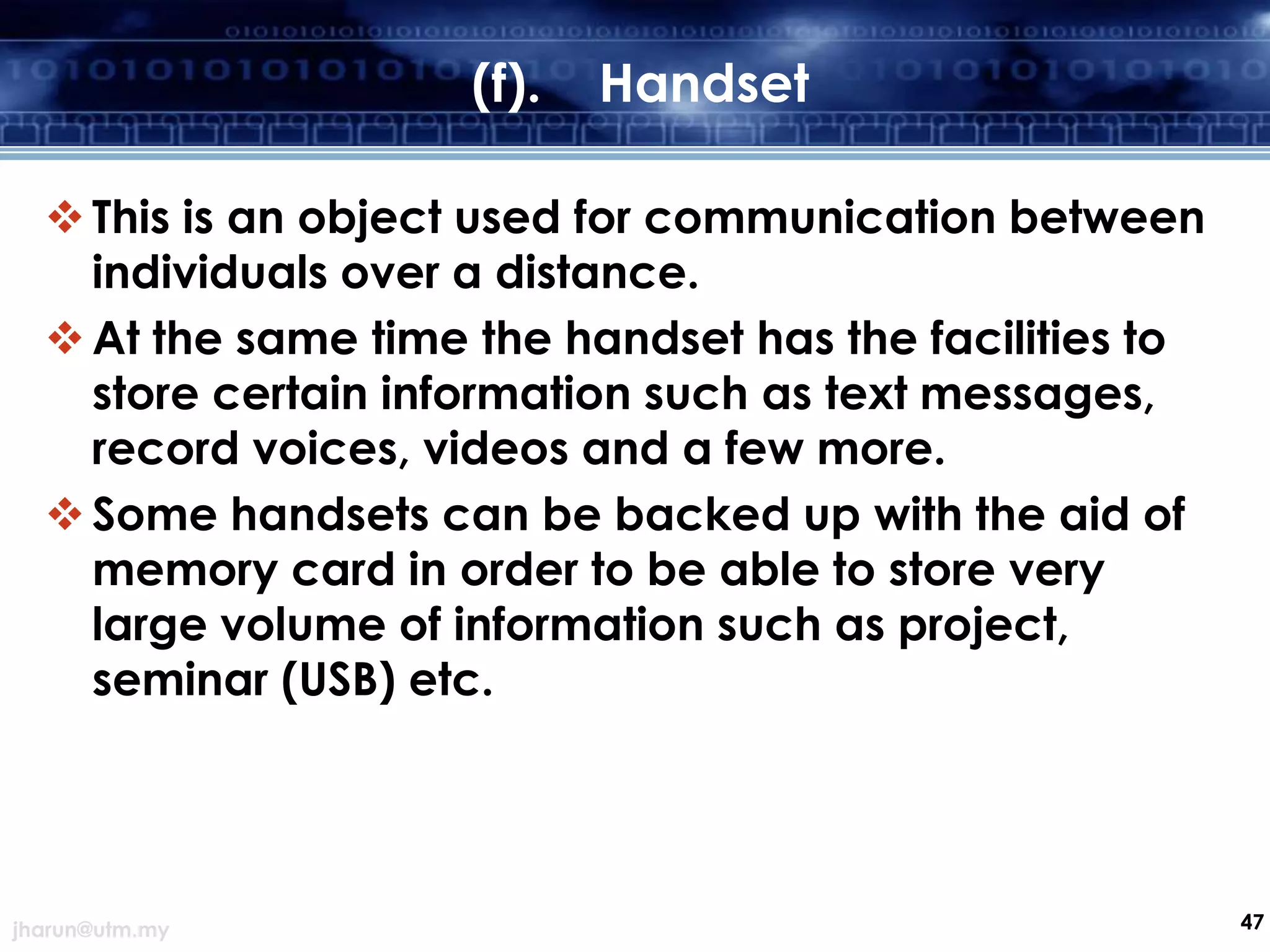
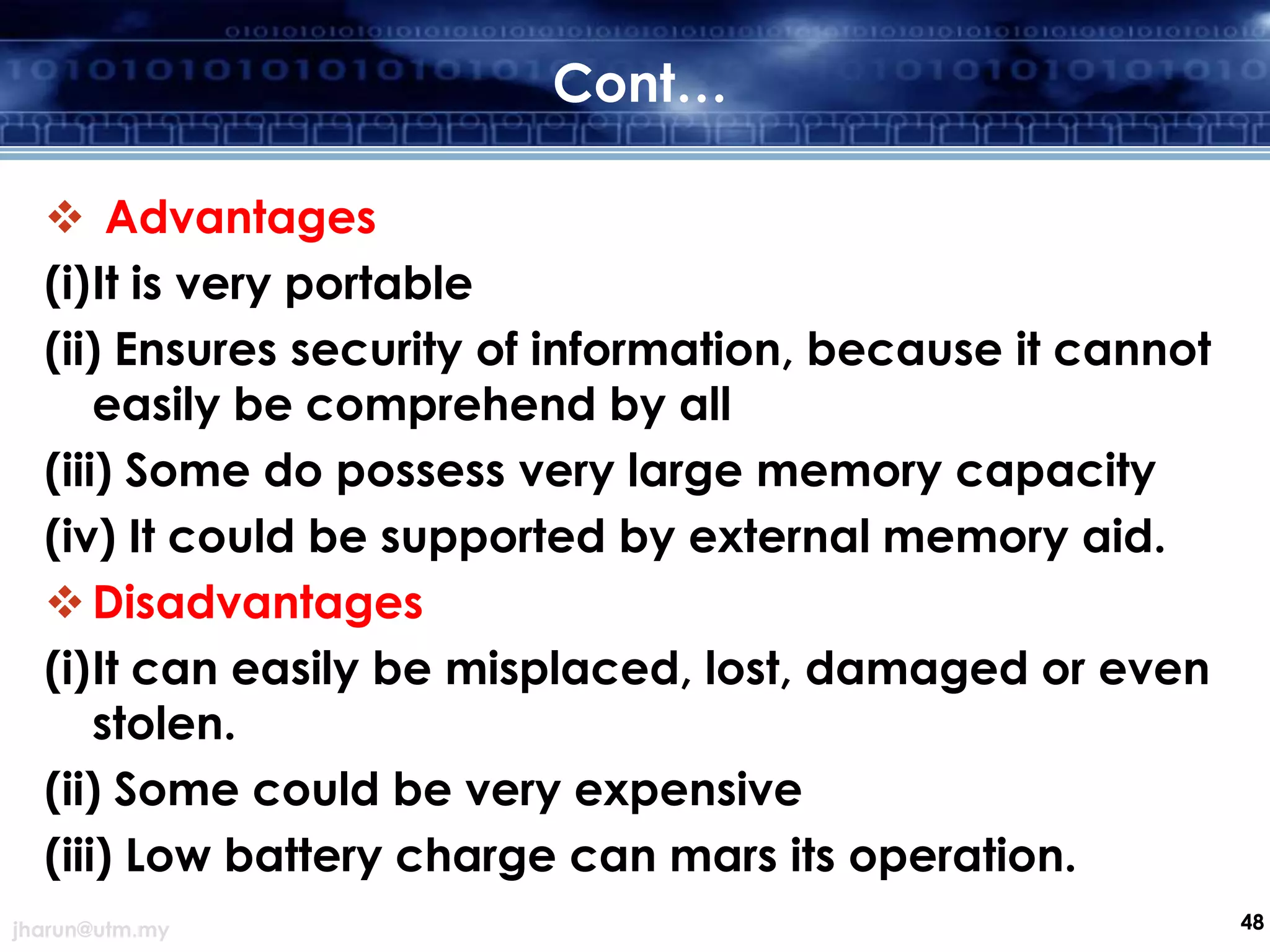
The document discusses effective document filing systems and was presented at a 3-day workshop on productivity enhancement for secretaries. It covers various topics related to document filing including the importance of record keeping, types of records, information processing cycles, methods of filing, indexing, the record cycle, and storage of documents. The key aspects of effective filing systems discussed are classification, accessibility, simplicity, and ensuring important records are properly stored and retained.