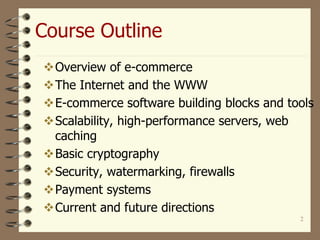
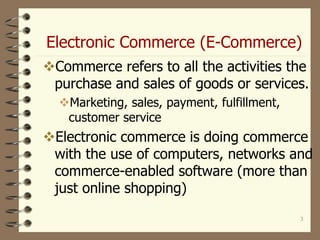
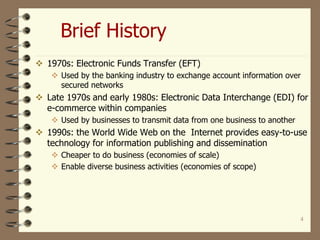
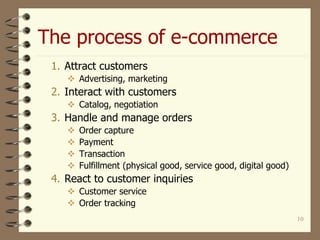
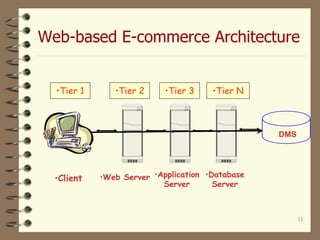
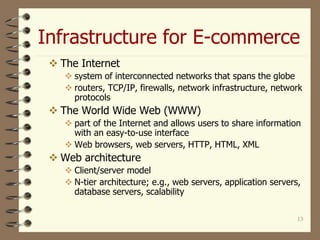
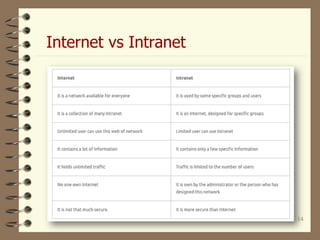
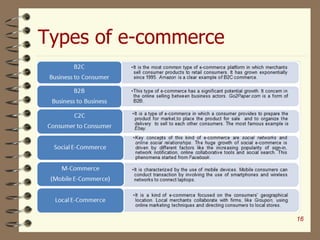
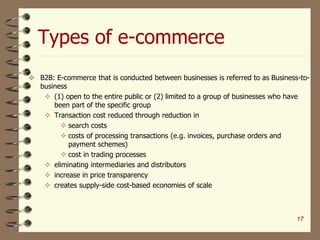
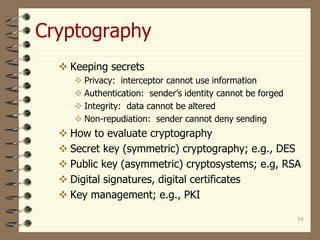
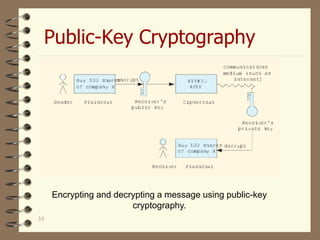
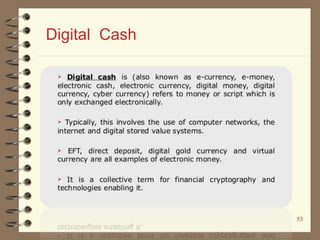
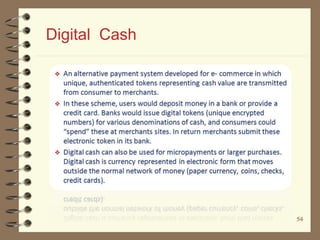
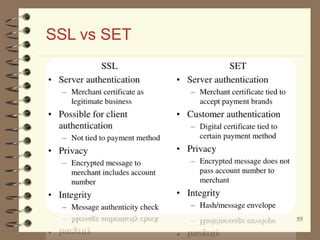
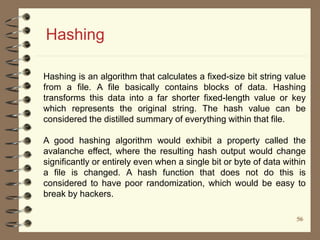
The document provides a comprehensive overview of e-commerce, detailing its definition, historical development, various applications, and infrastructure. It explores different types of e-commerce such as B2B, B2C, B2G, and C2C, along with their advantages and disadvantages. Additionally, it discusses e-commerce technologies, security concerns, payment systems, and the critical components required for successful e-commerce operations.