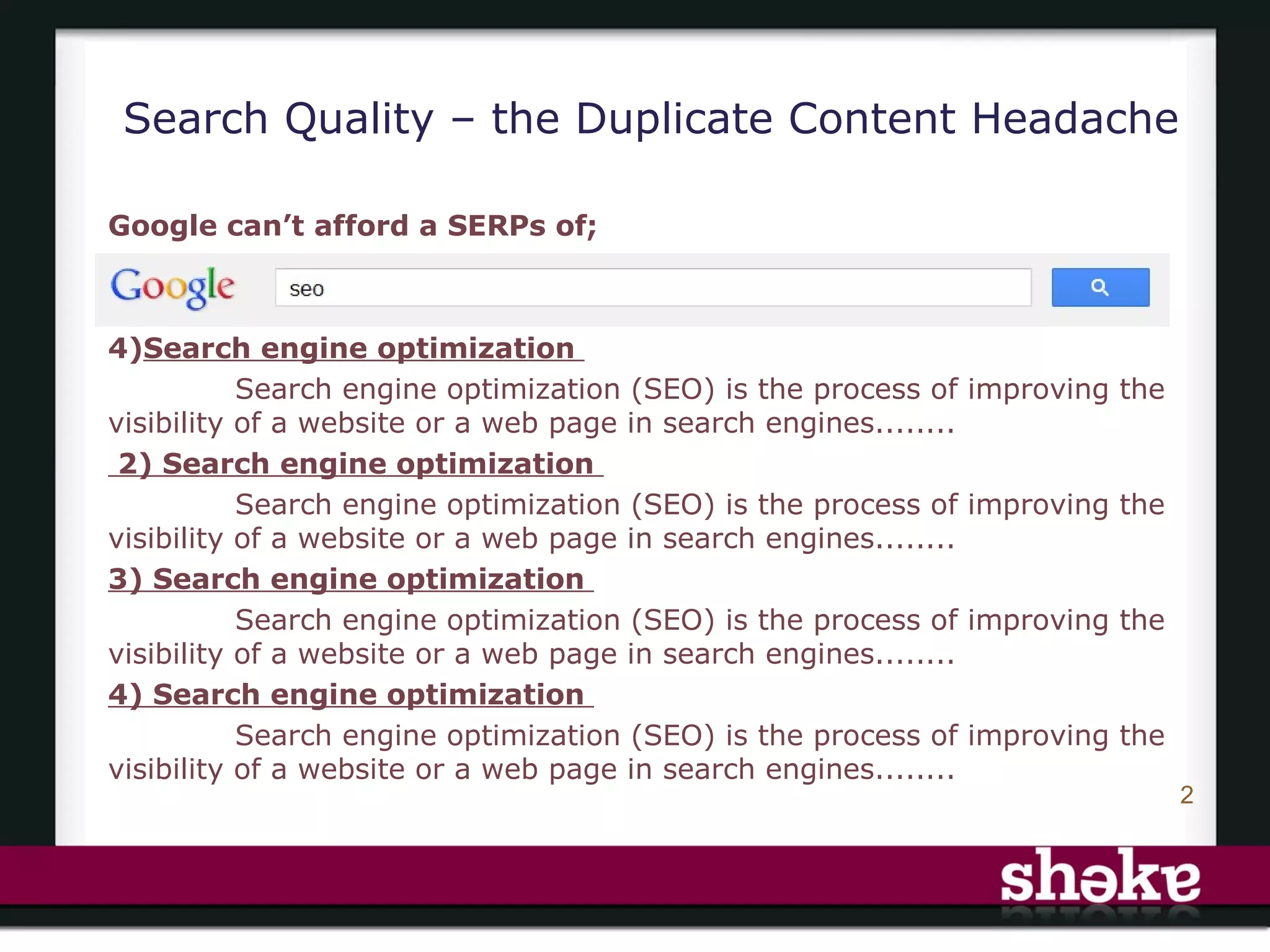
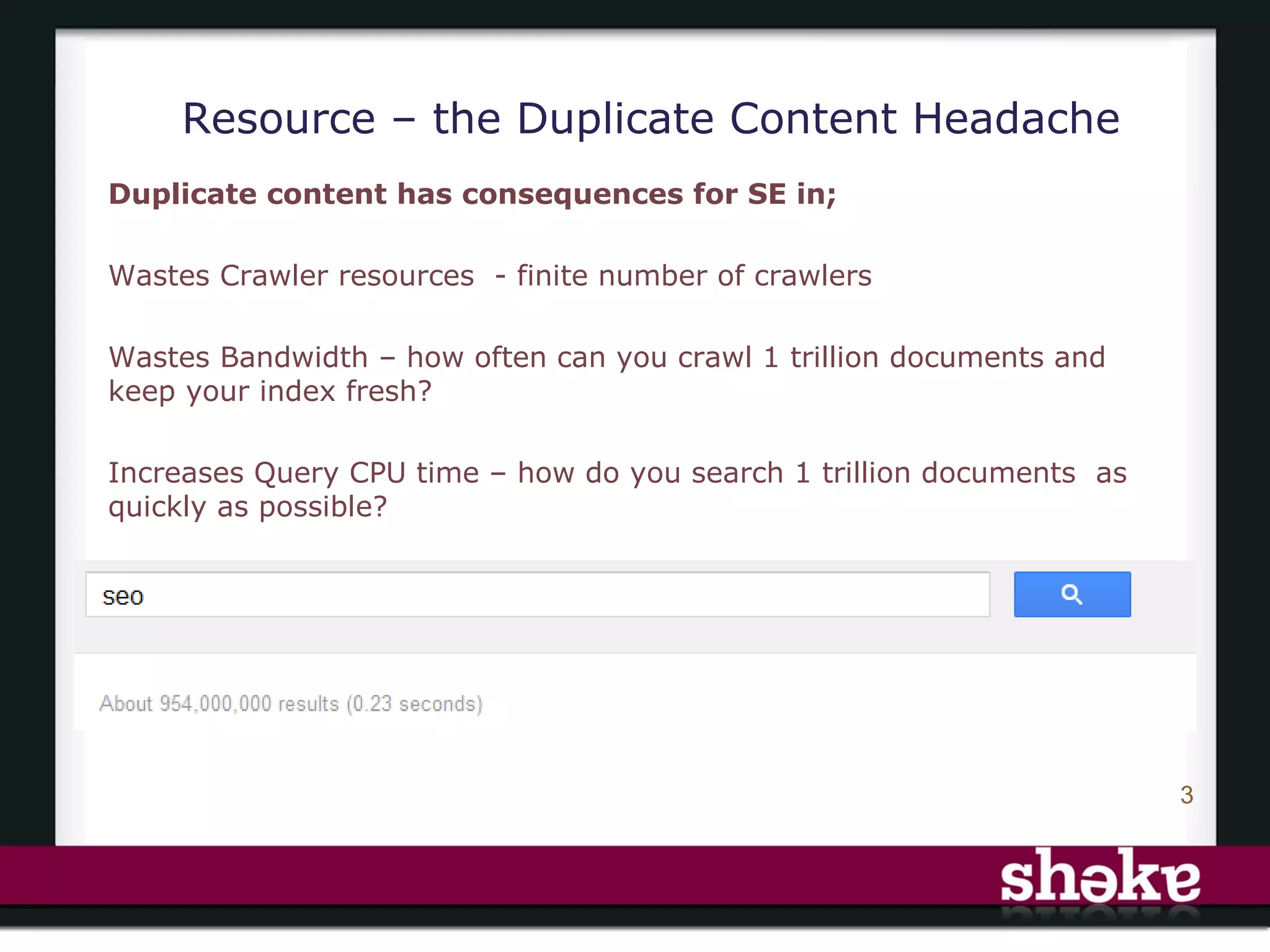
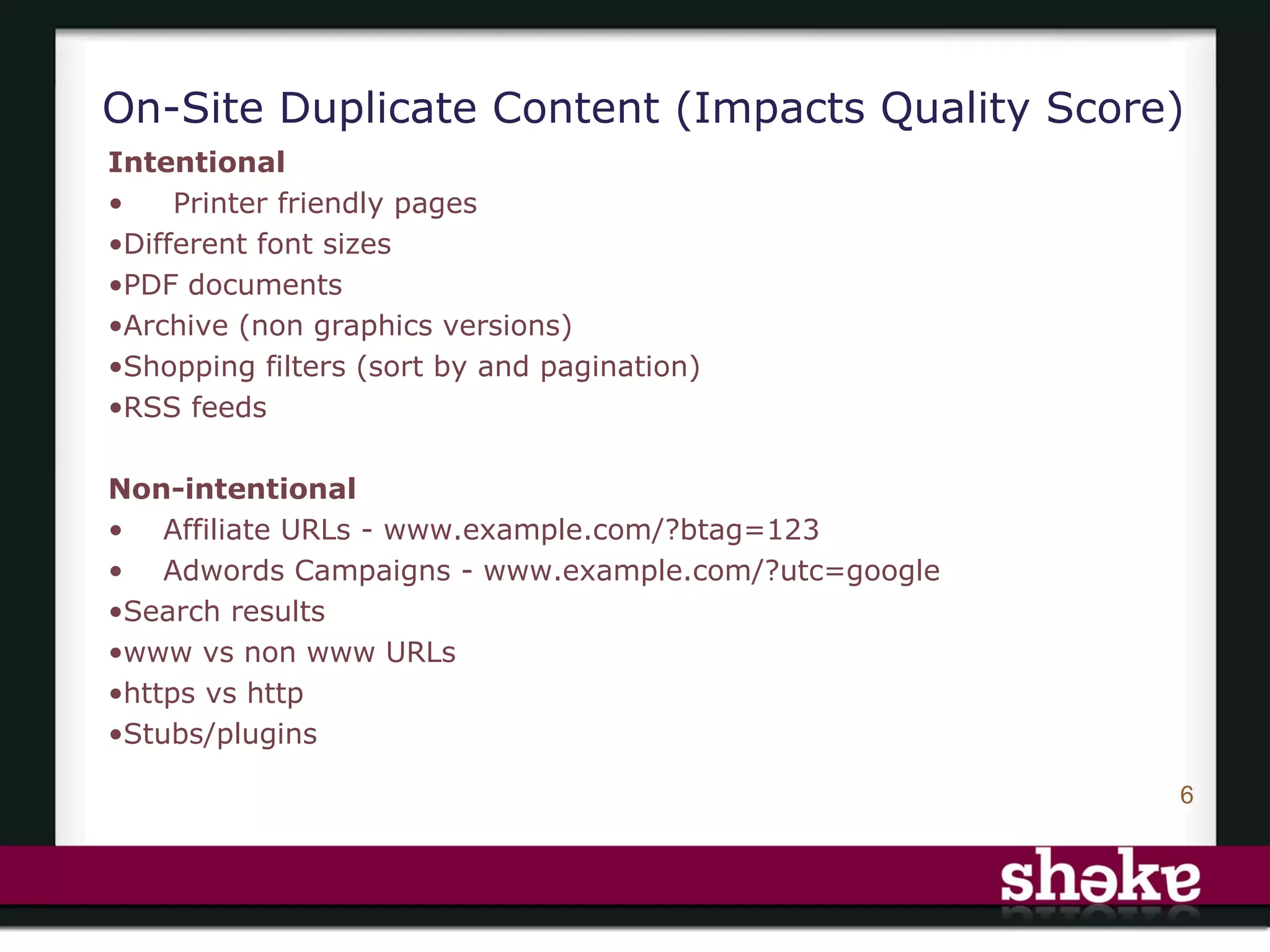
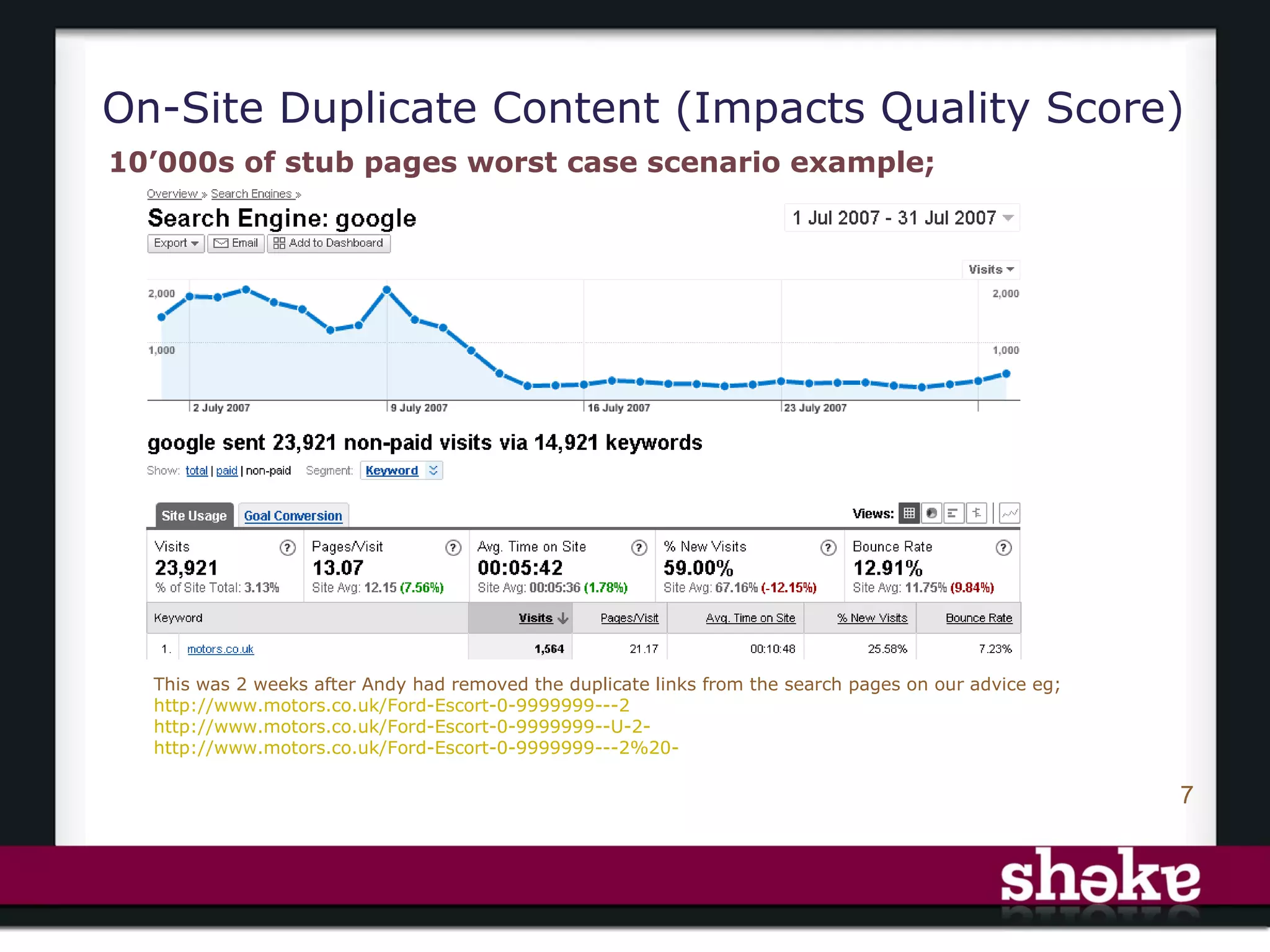
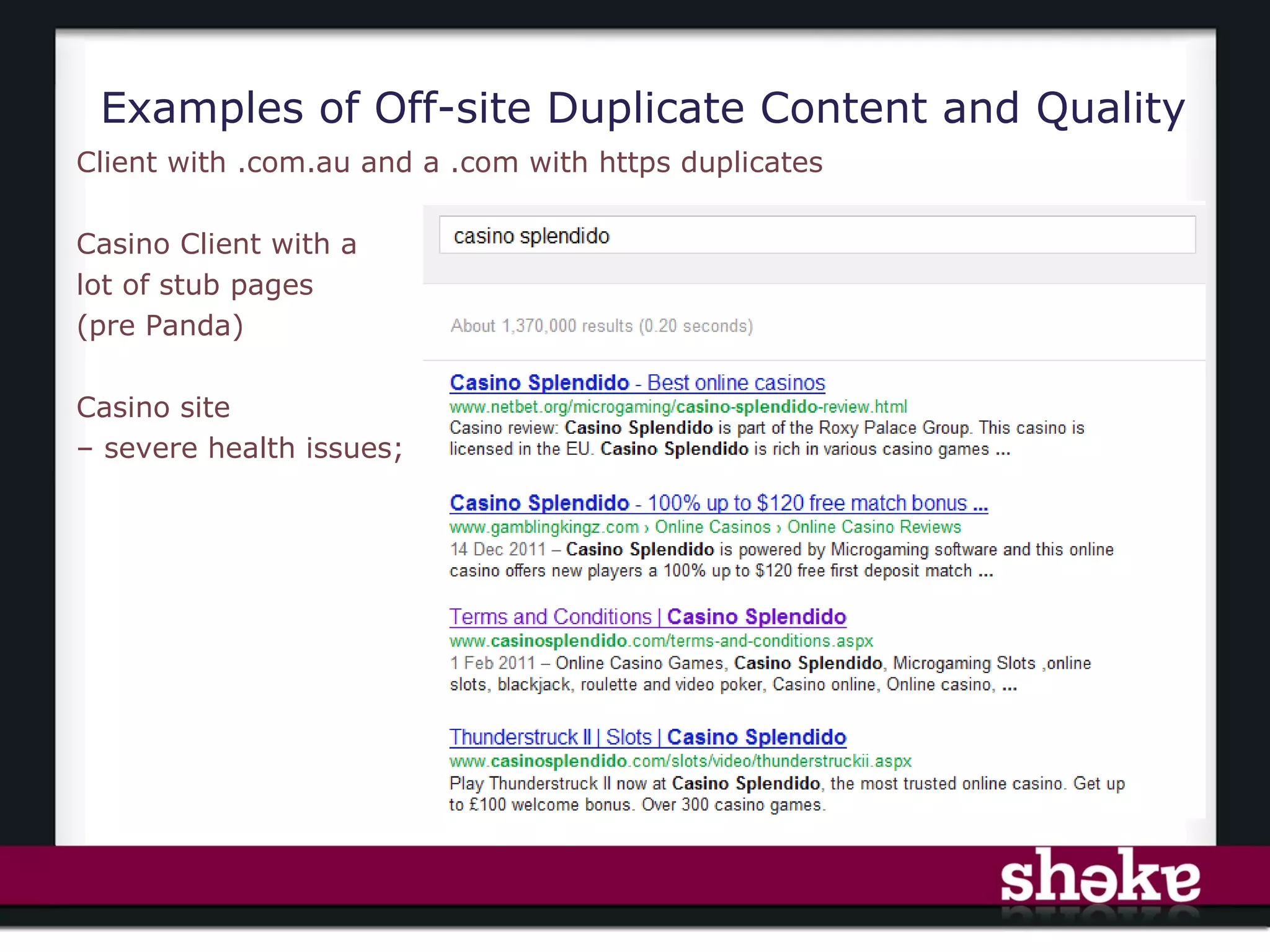
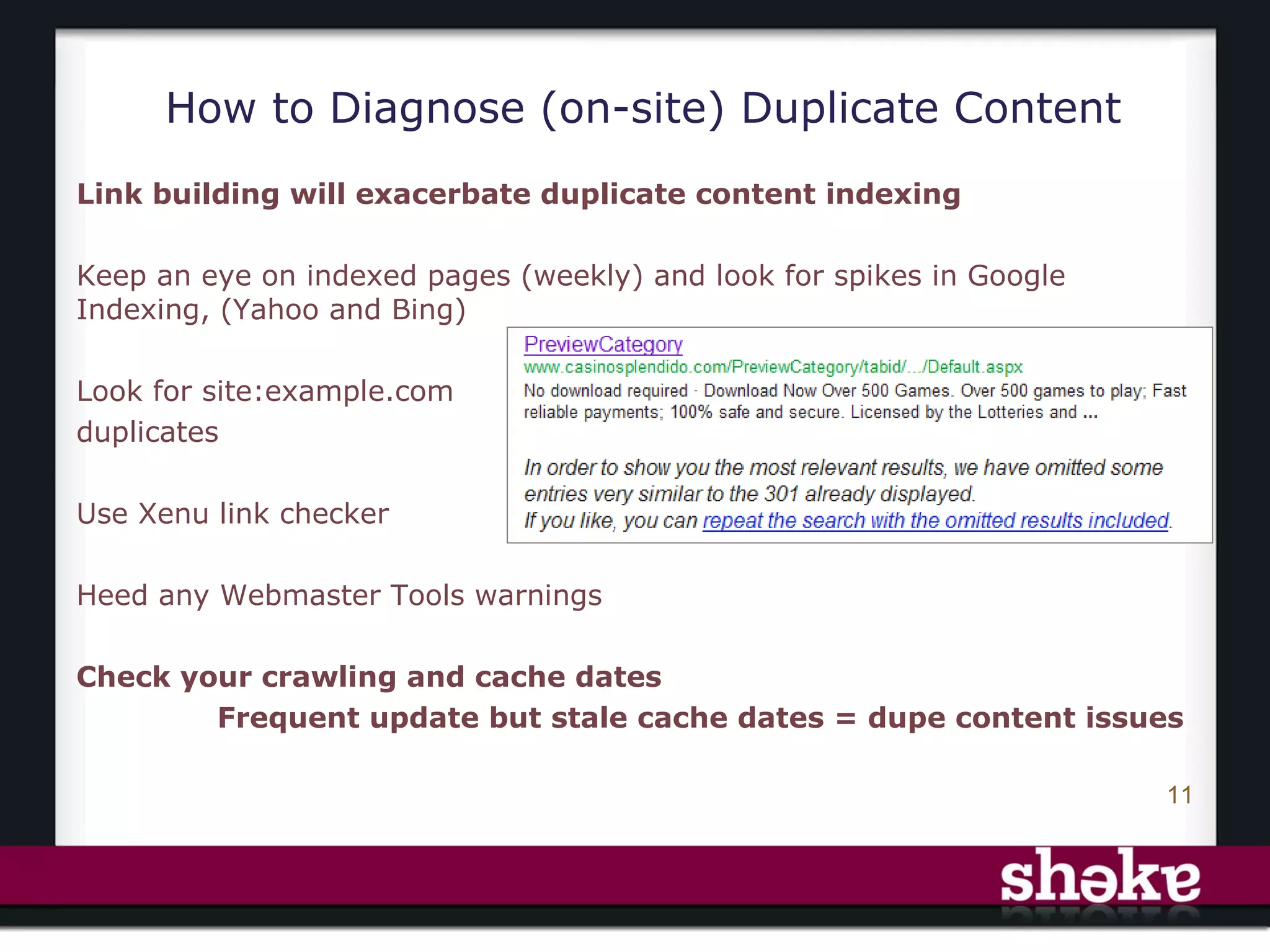
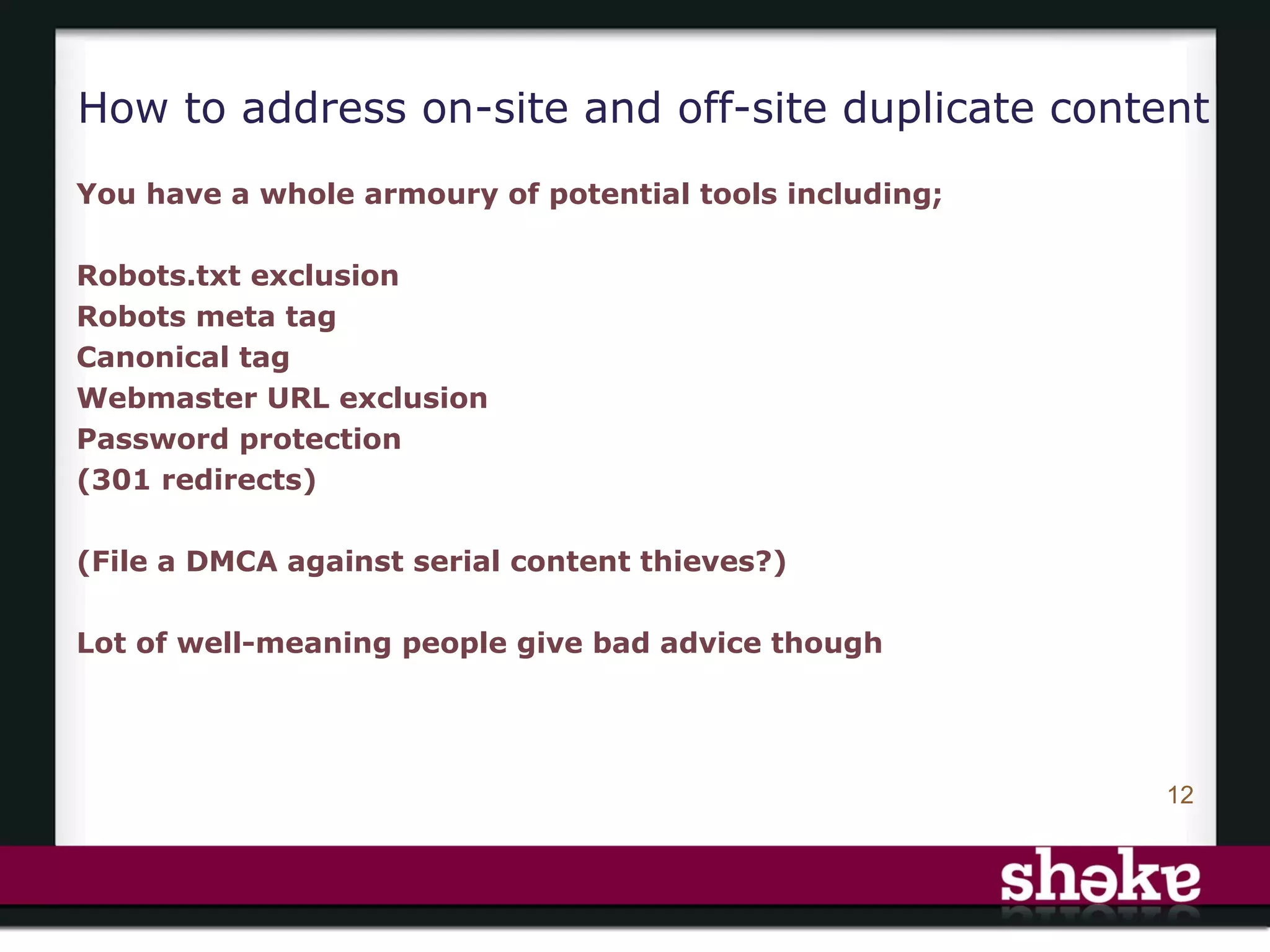
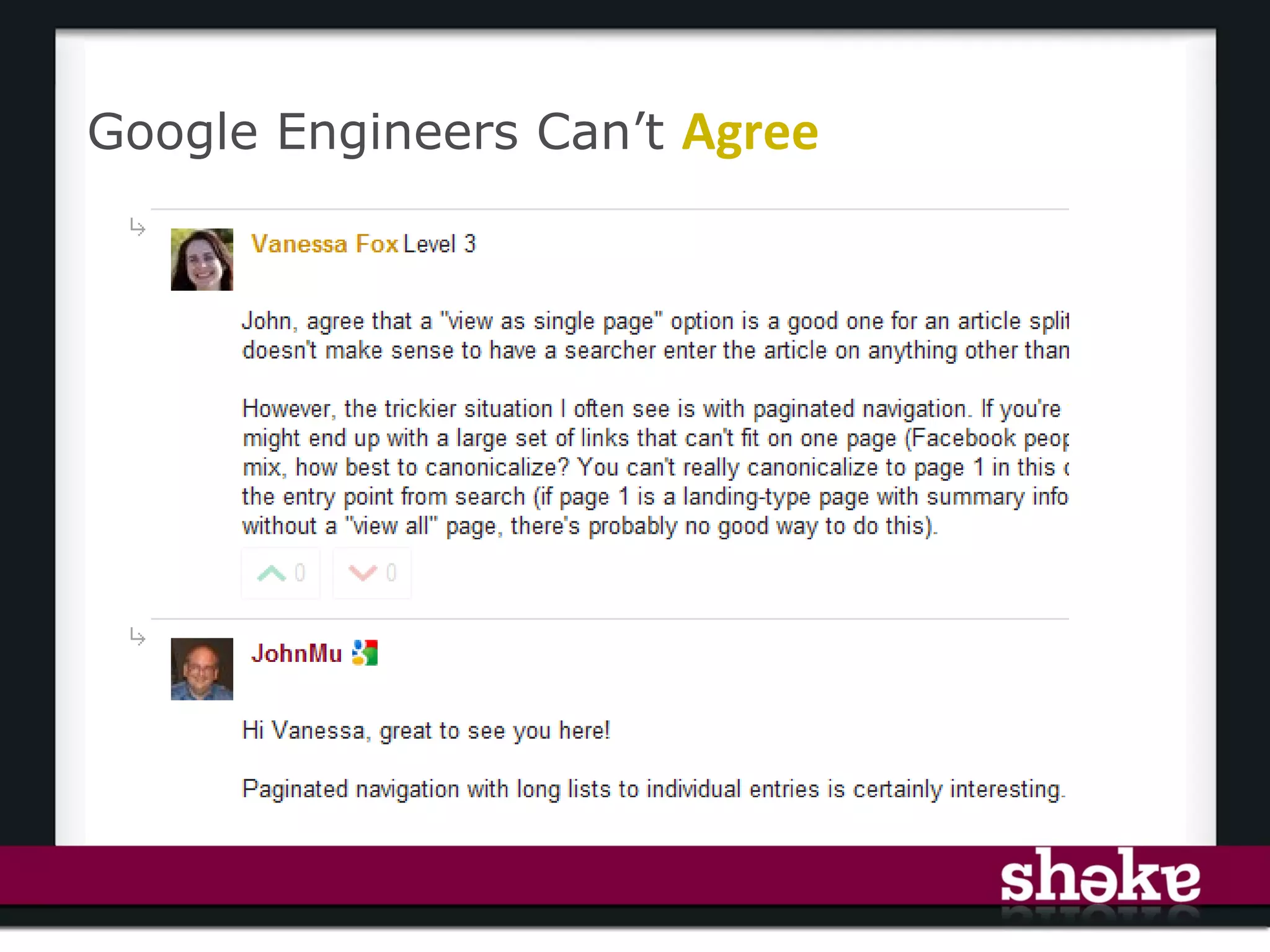
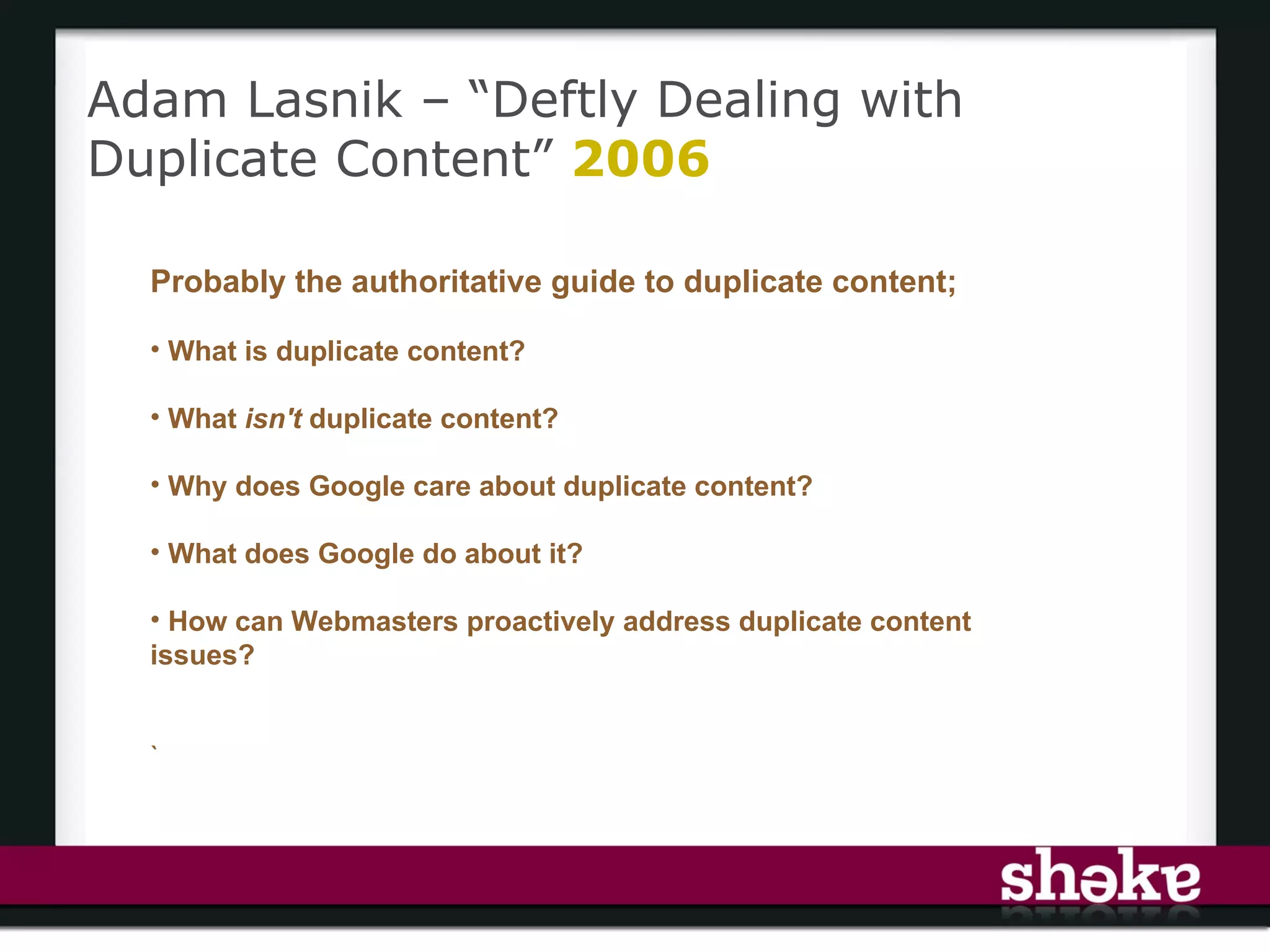
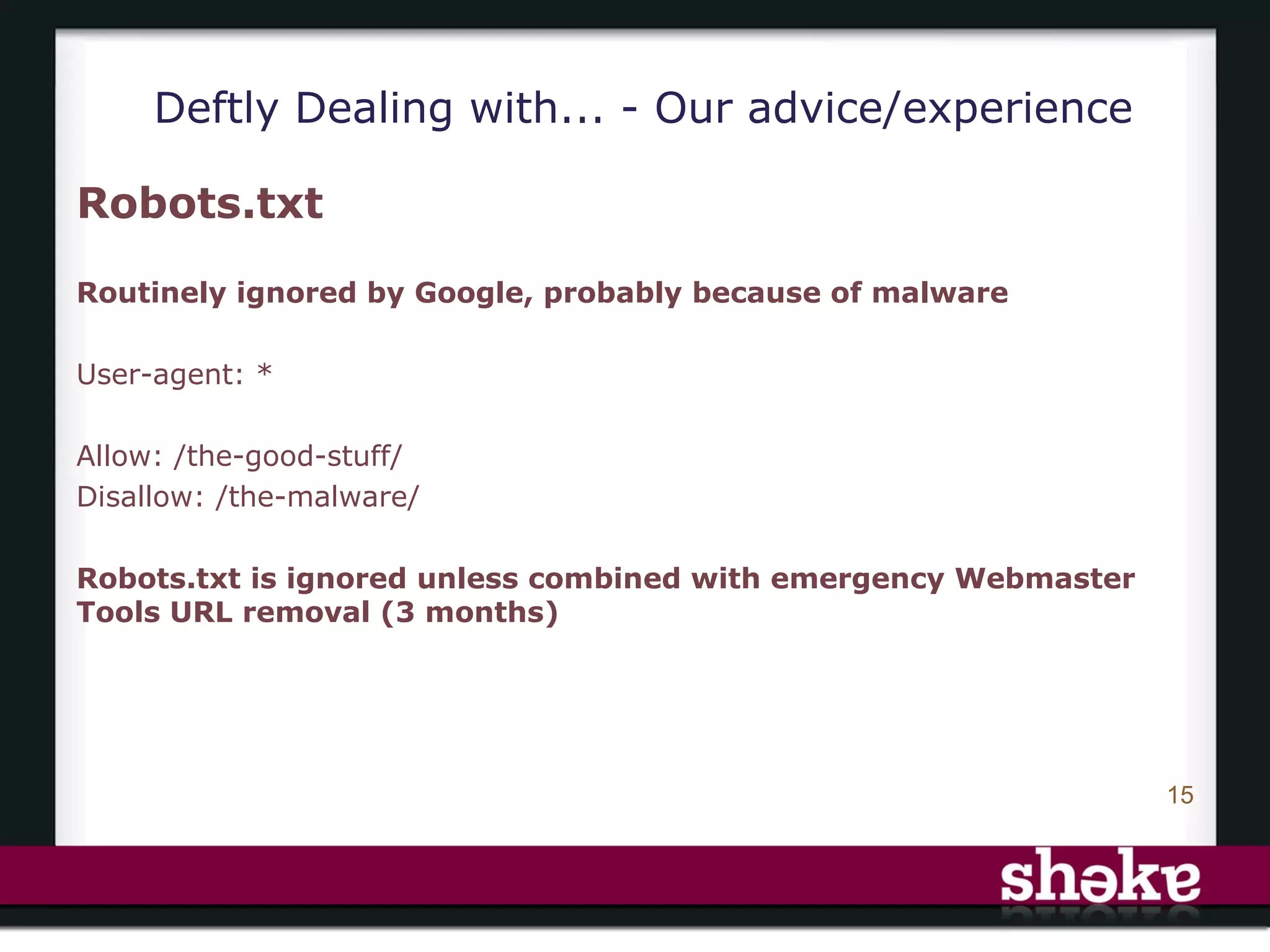
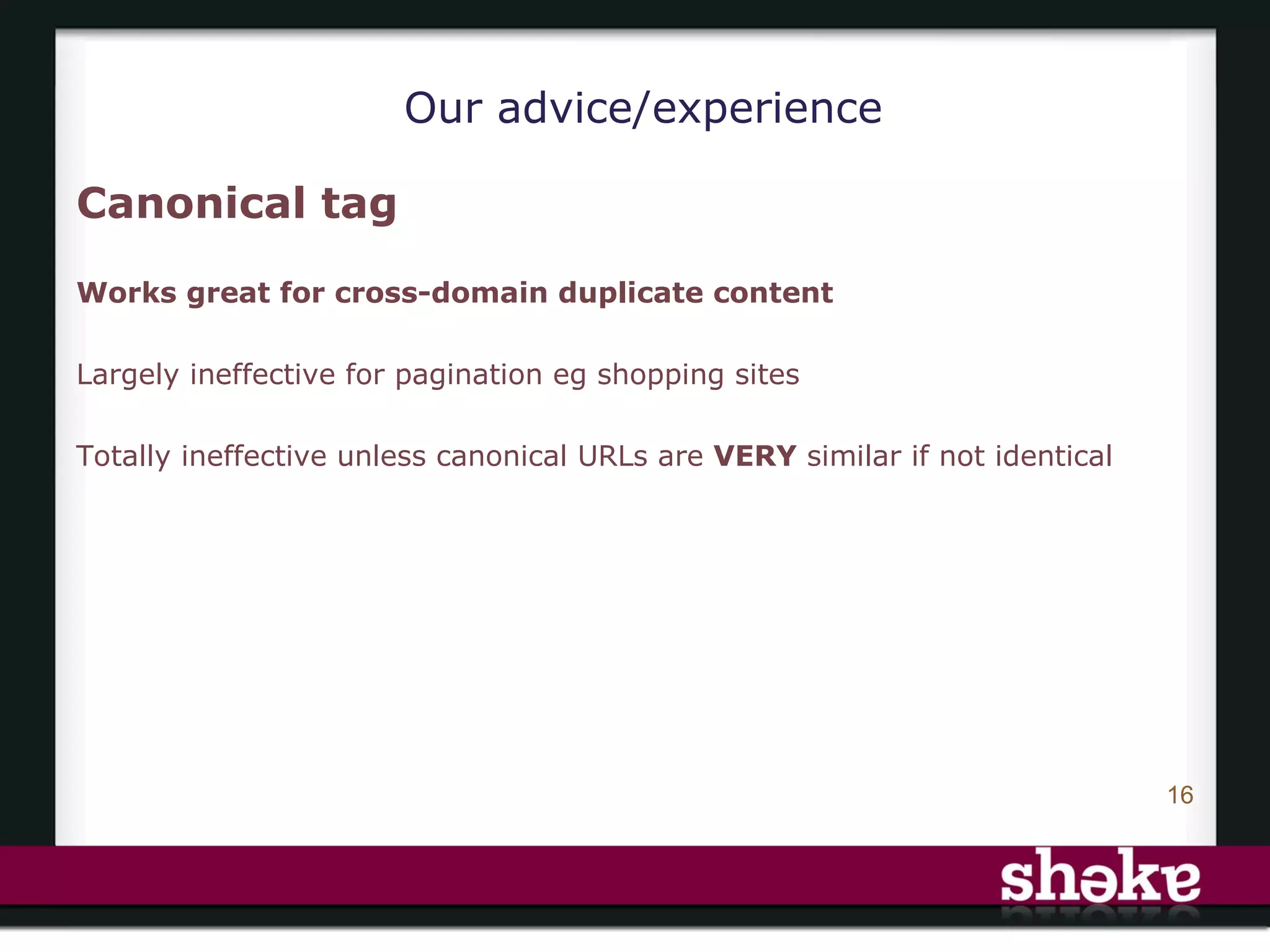
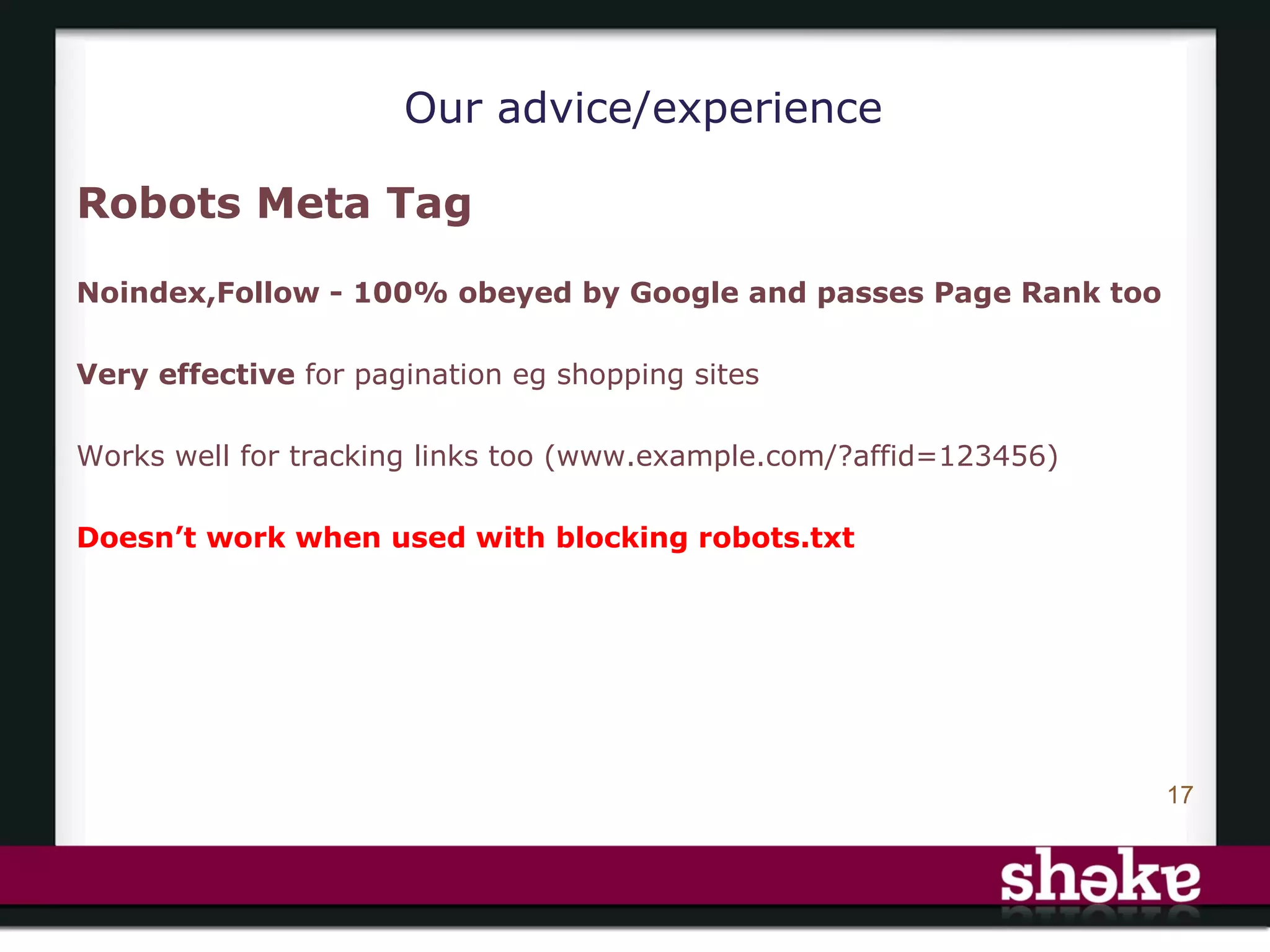
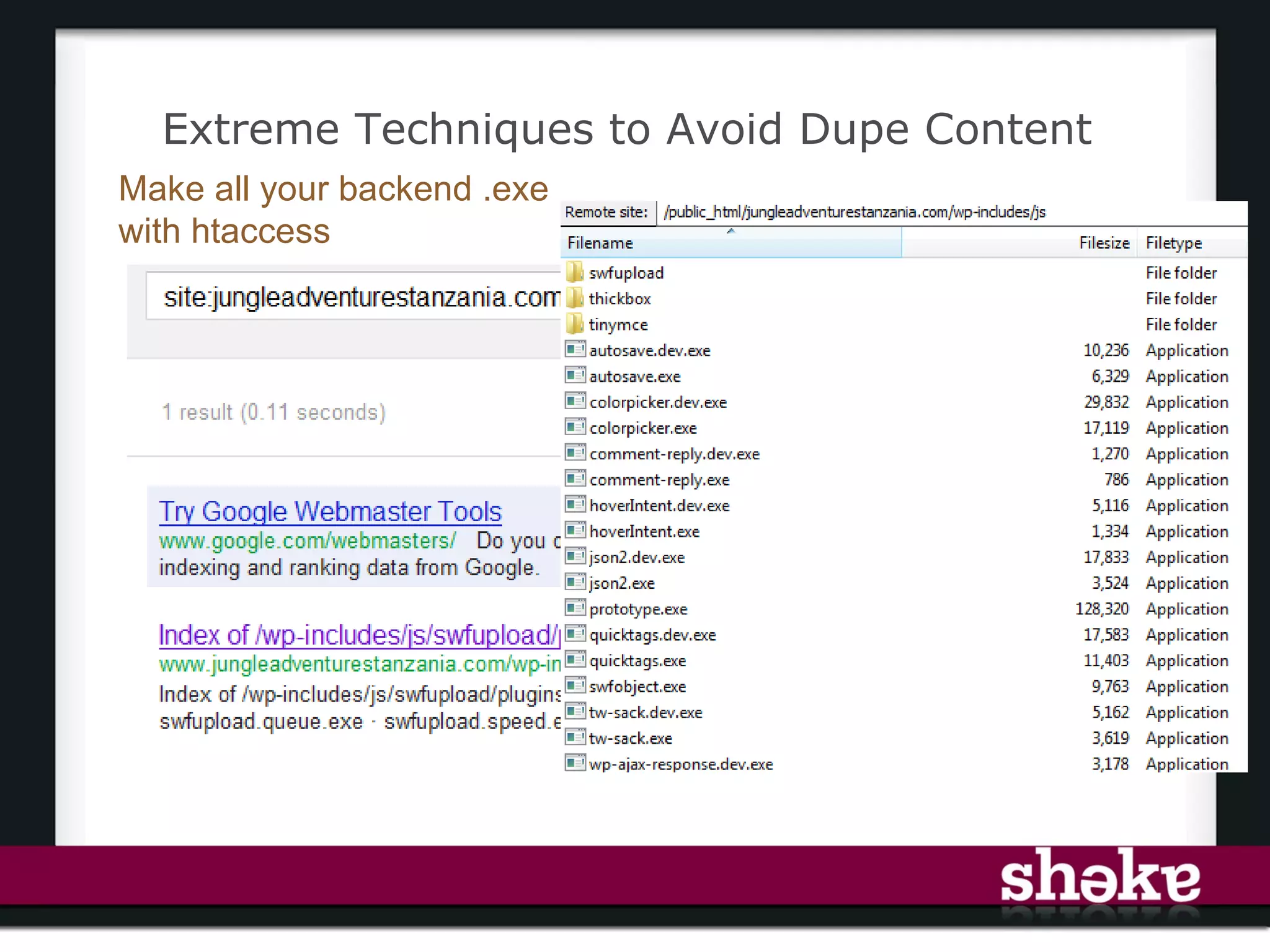
The document discusses the challenges and implications of duplicate content in search engine optimization (SEO), highlighting how it can waste resources, increase bandwidth issues, and affect website rankings. It outlines the types of duplicate content, both intentional and non-intentional, as well as strategies for diagnosing and mitigating these issues. Key recommendations include using canonical tags, robots meta tags, and monitoring indexed pages to improve site quality and performance.