Embed presentation
Download as PDF, PPTX
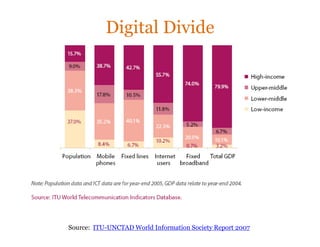
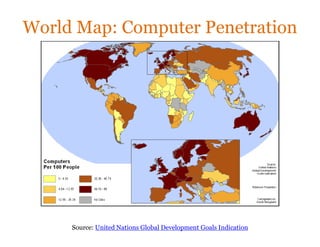
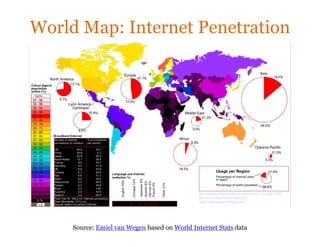
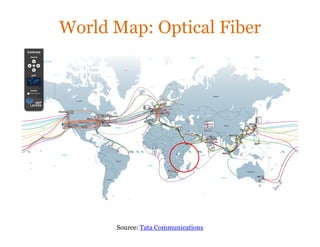
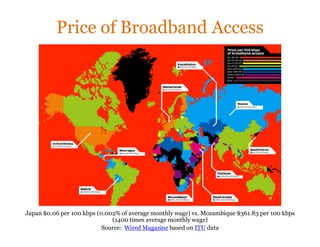
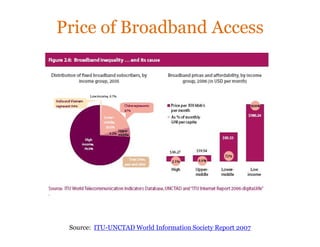

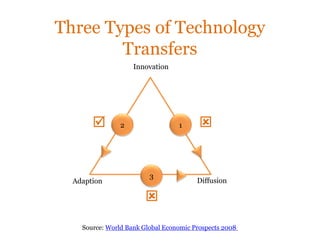
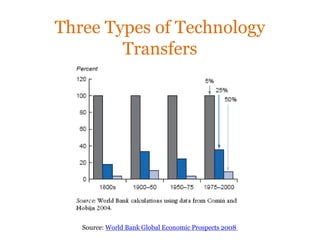
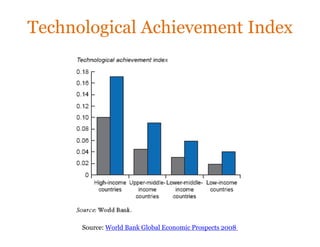
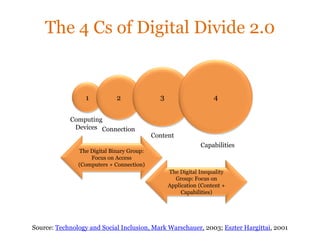
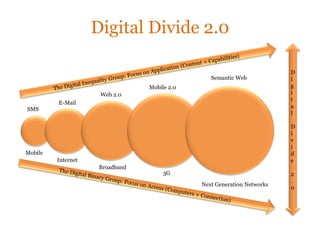
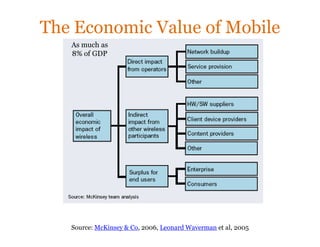
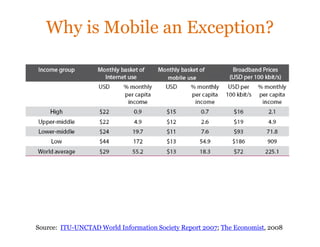
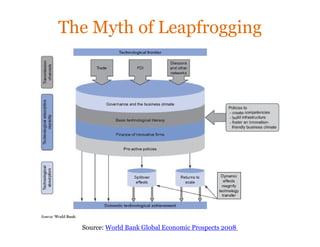
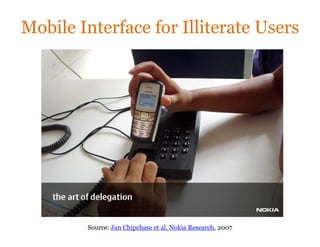
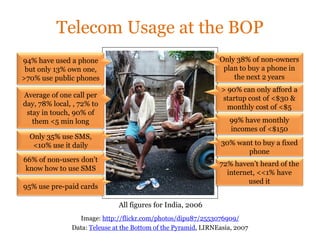
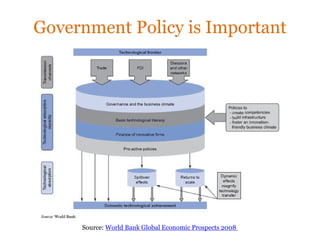


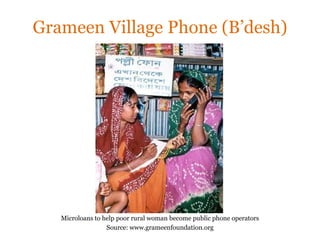
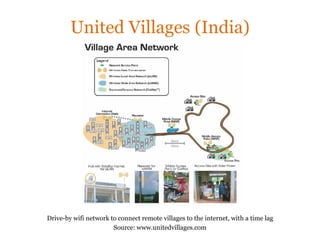
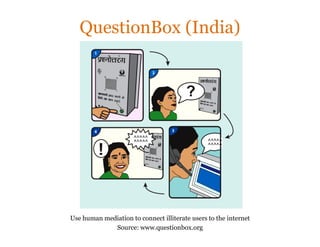




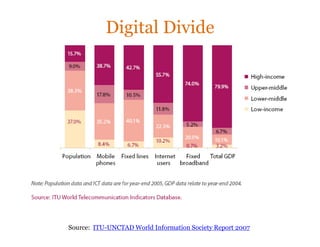
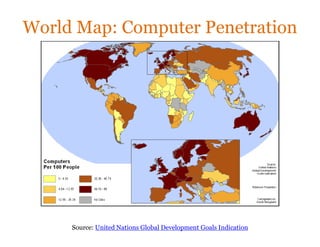
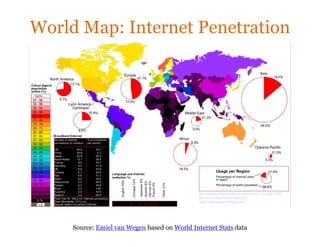
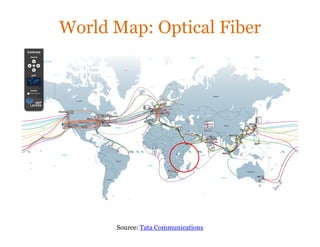
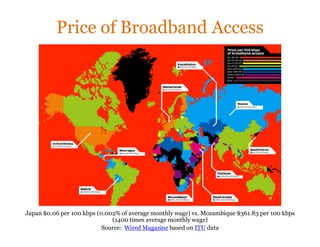
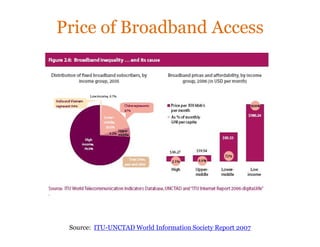
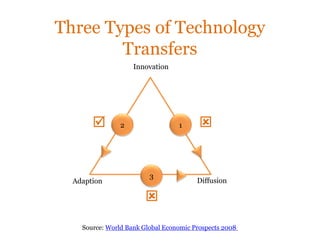
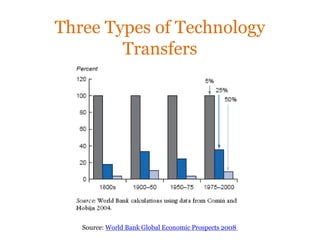
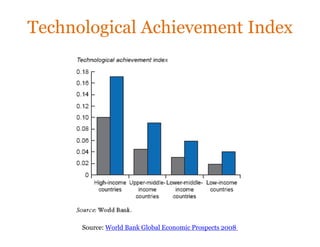
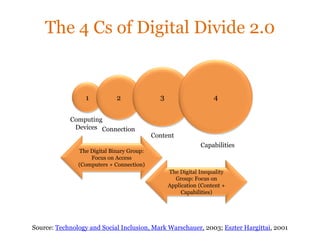
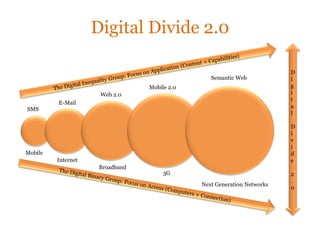
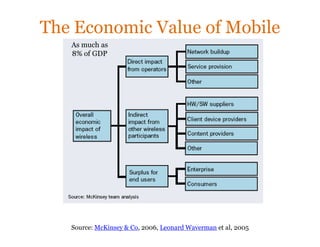
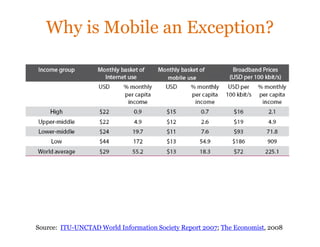
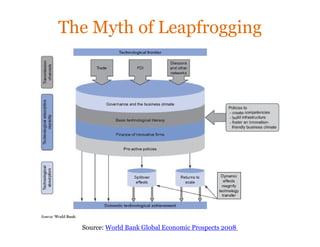
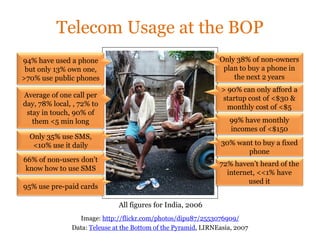
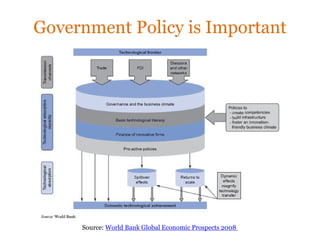
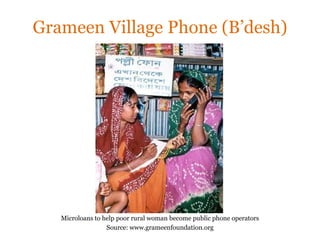
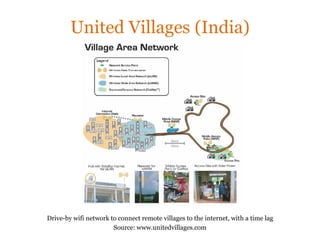
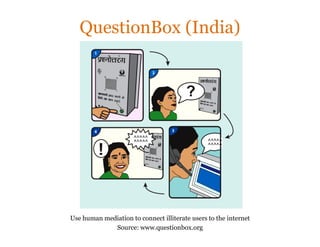
The document discusses the concept of "Digital Divide 2.0" which focuses not just on access to computing devices and internet connections, but also access to digital content and capabilities. It examines differences in technology adoption and access across the world, with developing regions facing significant barriers due to cost and infrastructure limitations. While mobile phones have provided some countries an avenue for "leapfrogging" technology gaps, the reality is that most of the world's poor can only afford very basic mobile access and services. The document argues that both government policies and grassroots innovations are needed to help bridge Digital Divide 2.0 and ensure greater global access to emerging technologies.