Embed presentation
Downloaded 13 times
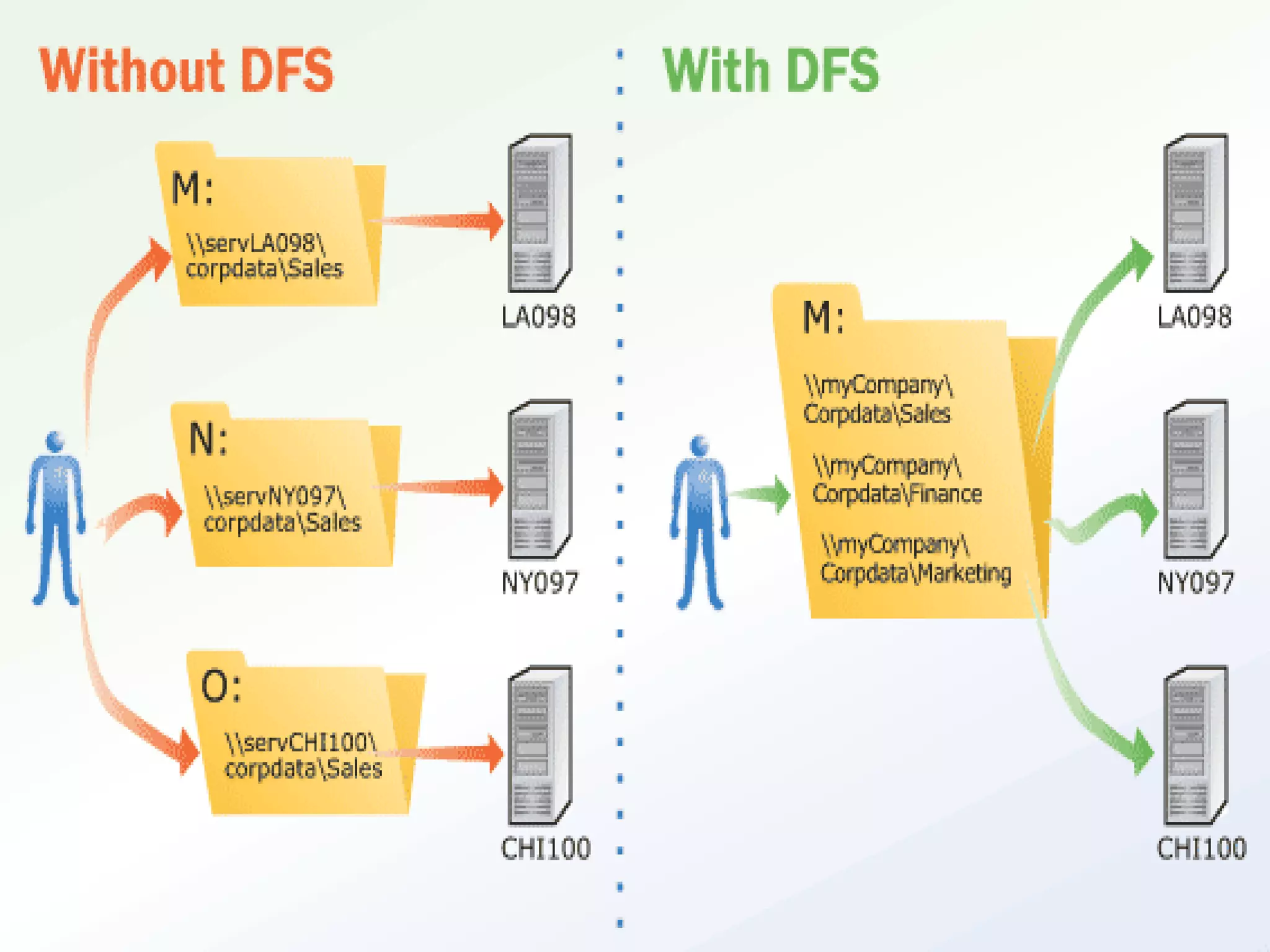
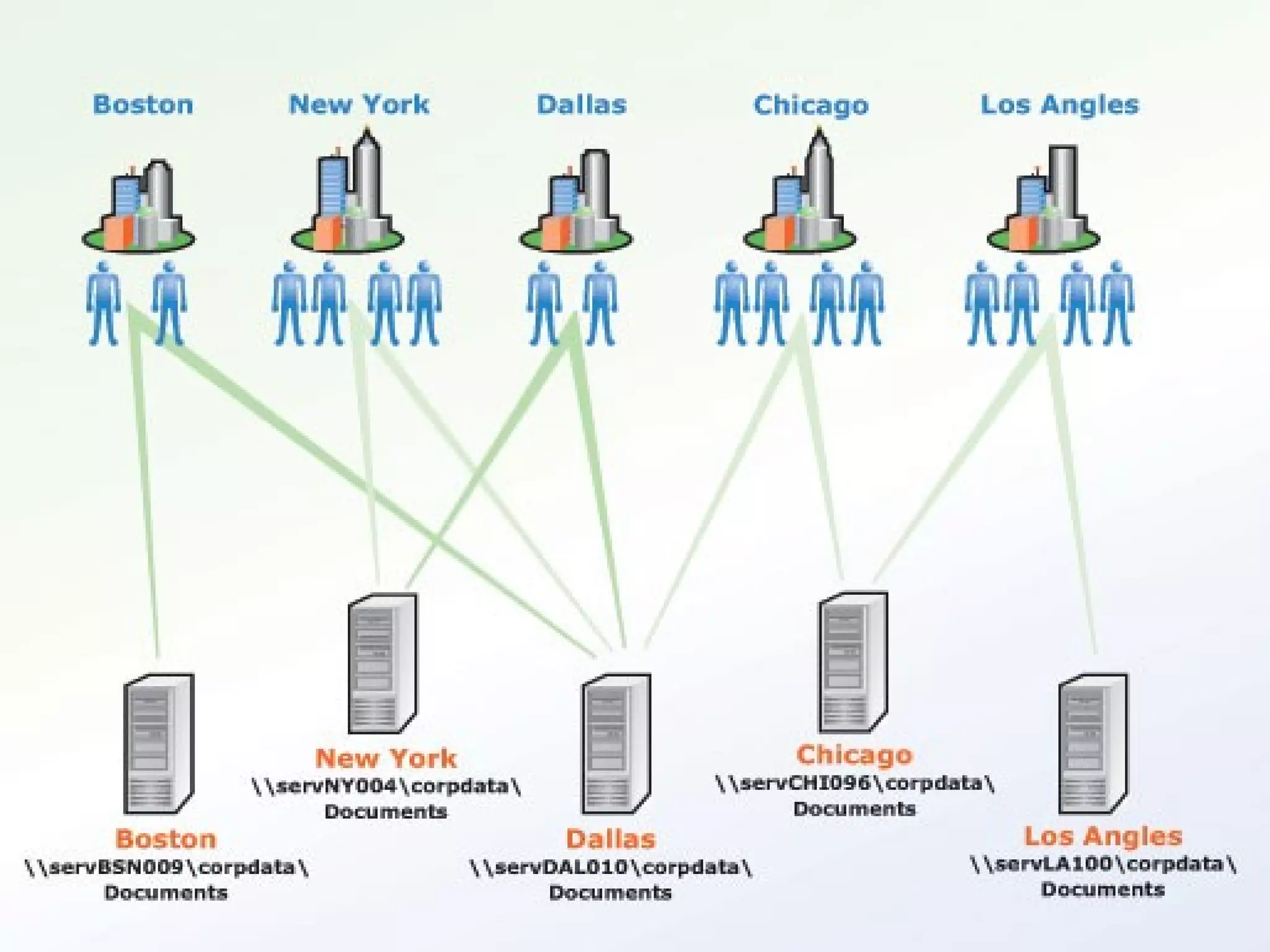
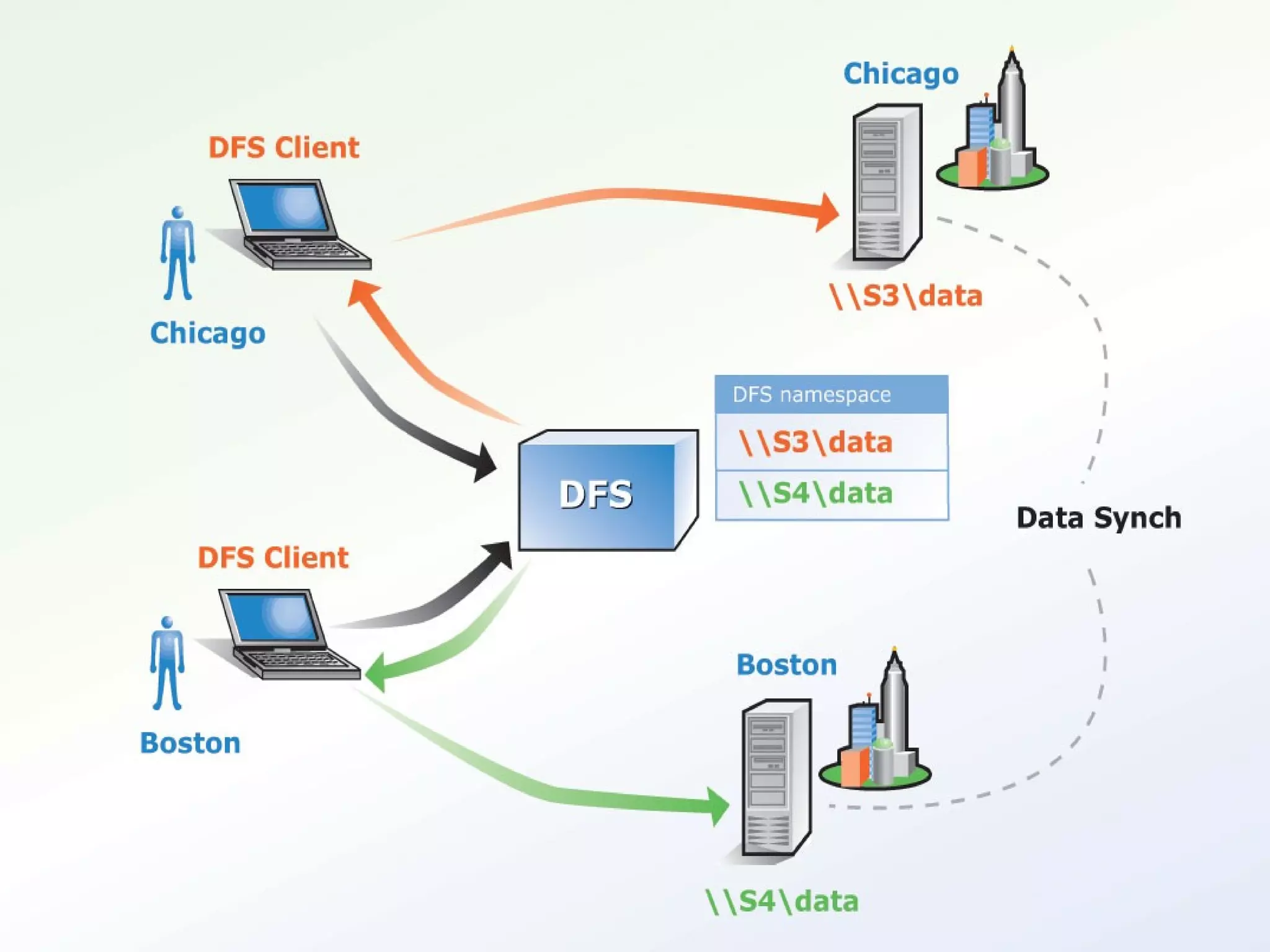

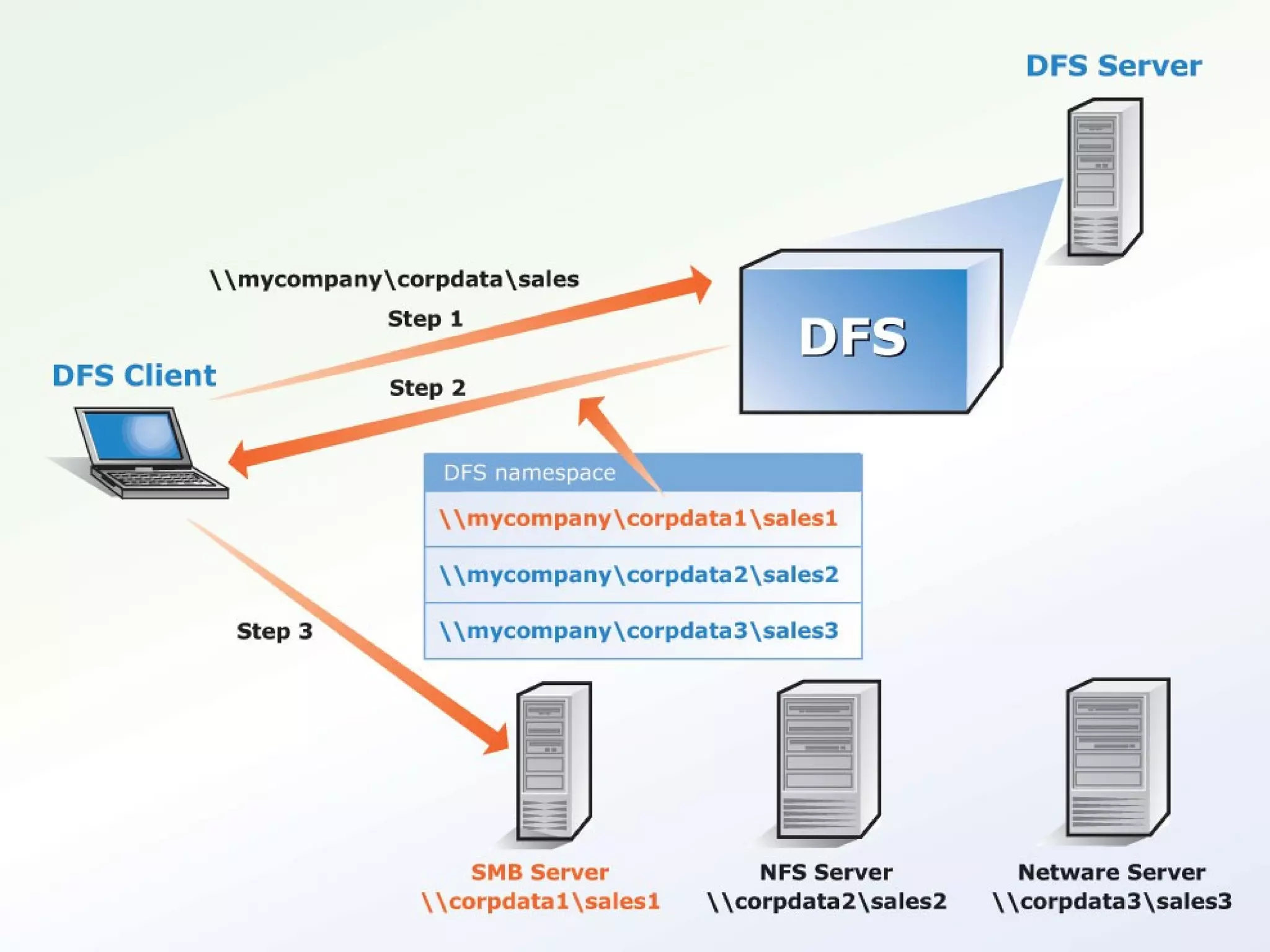
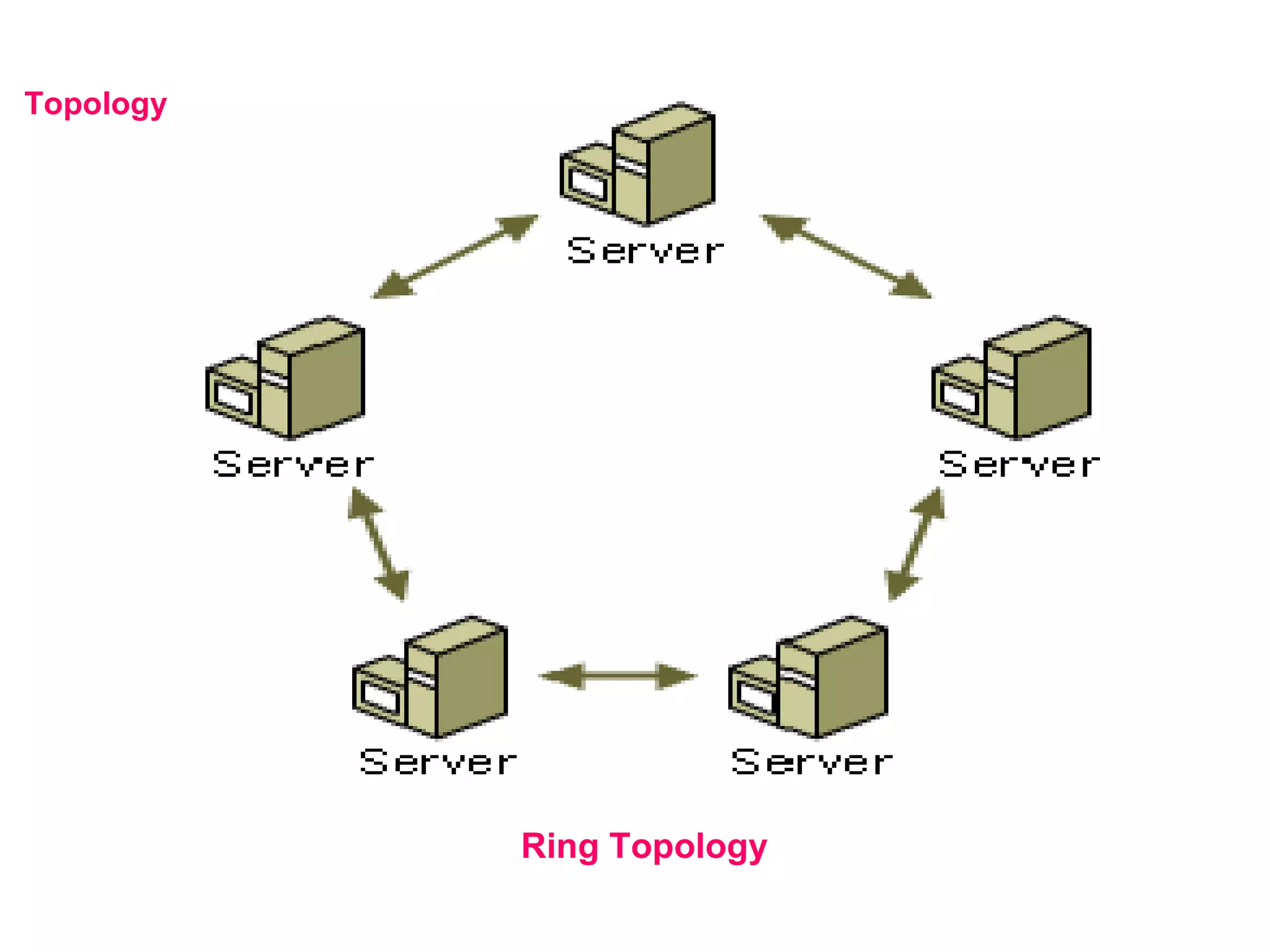
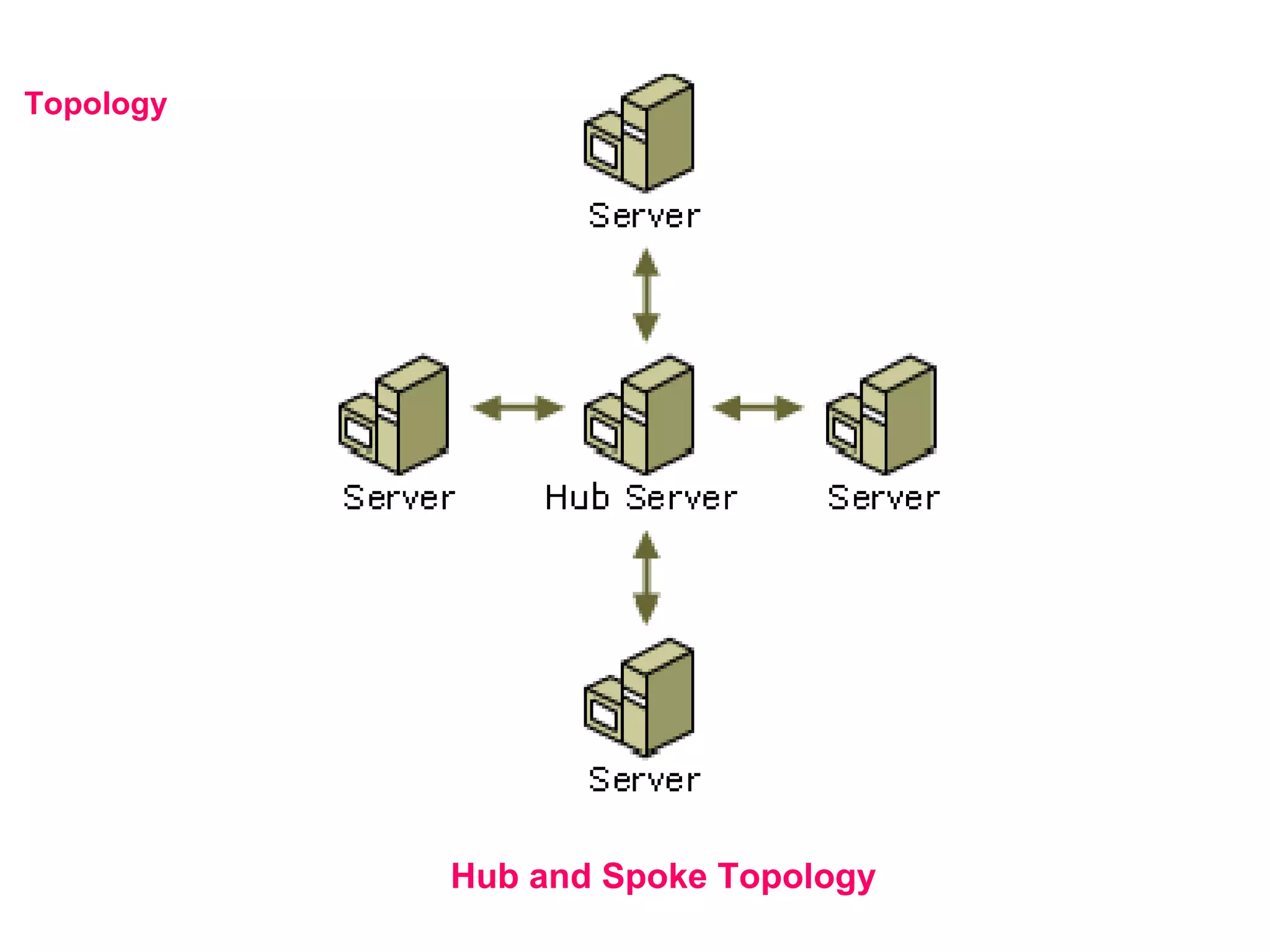
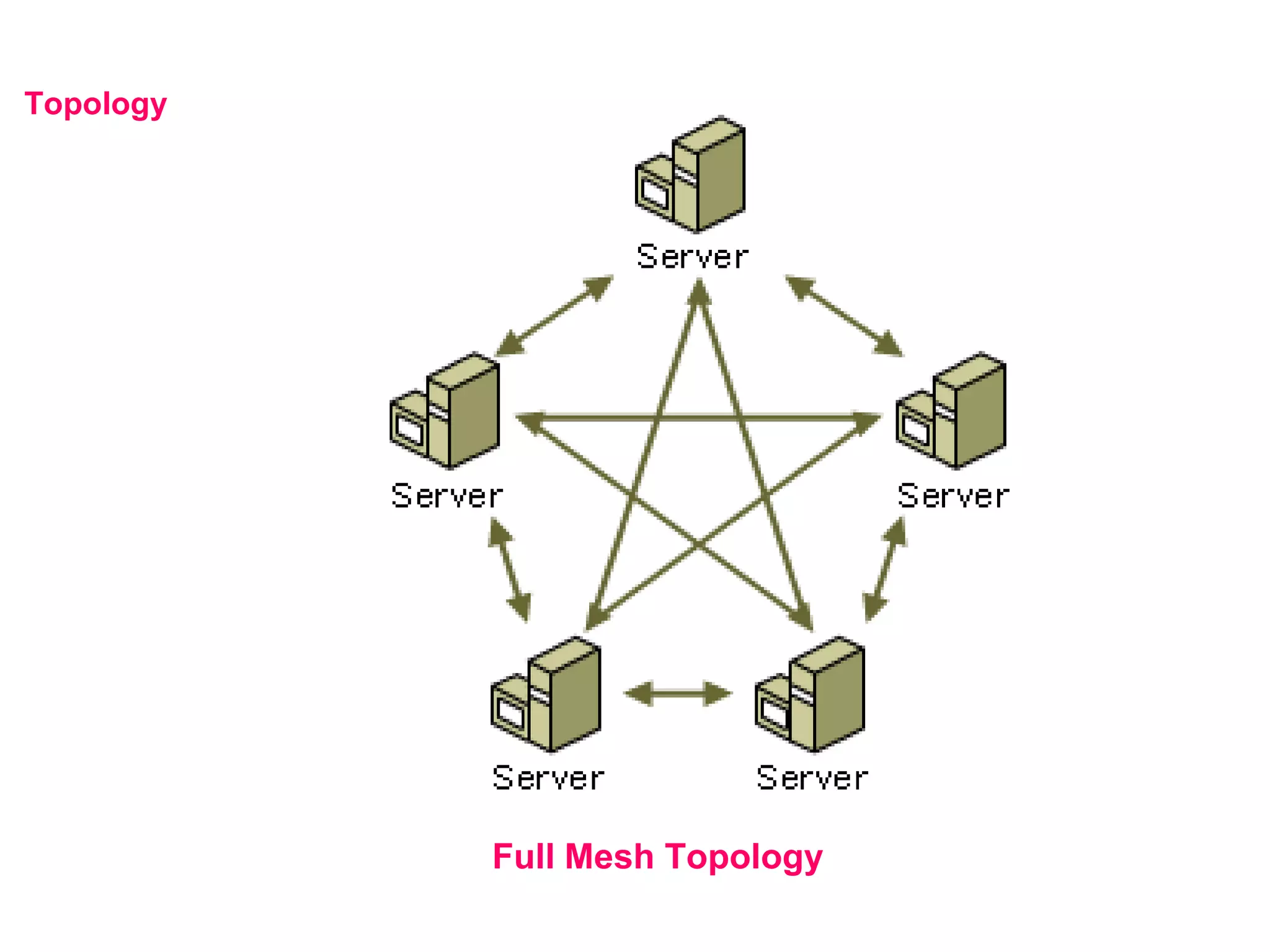
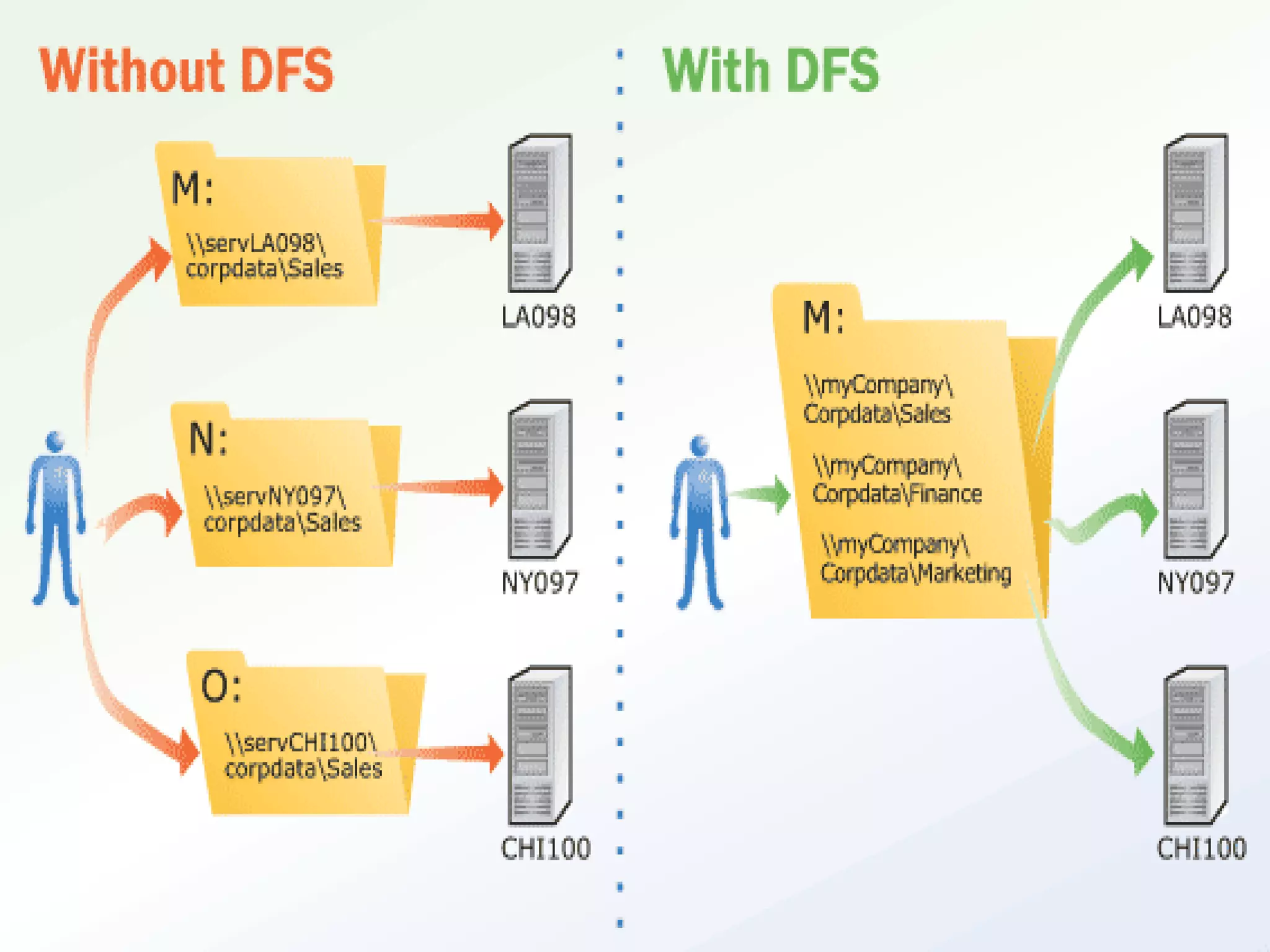
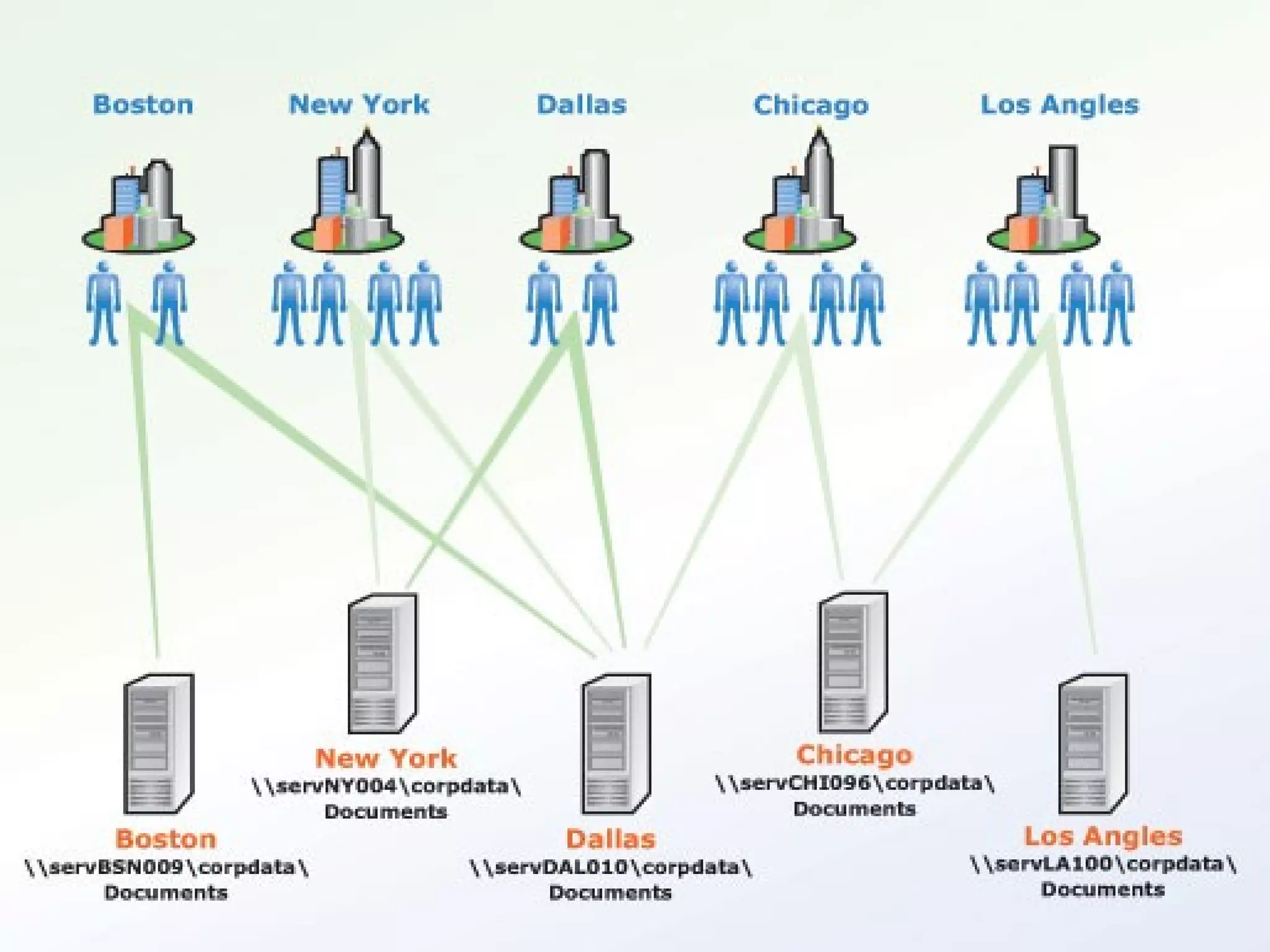
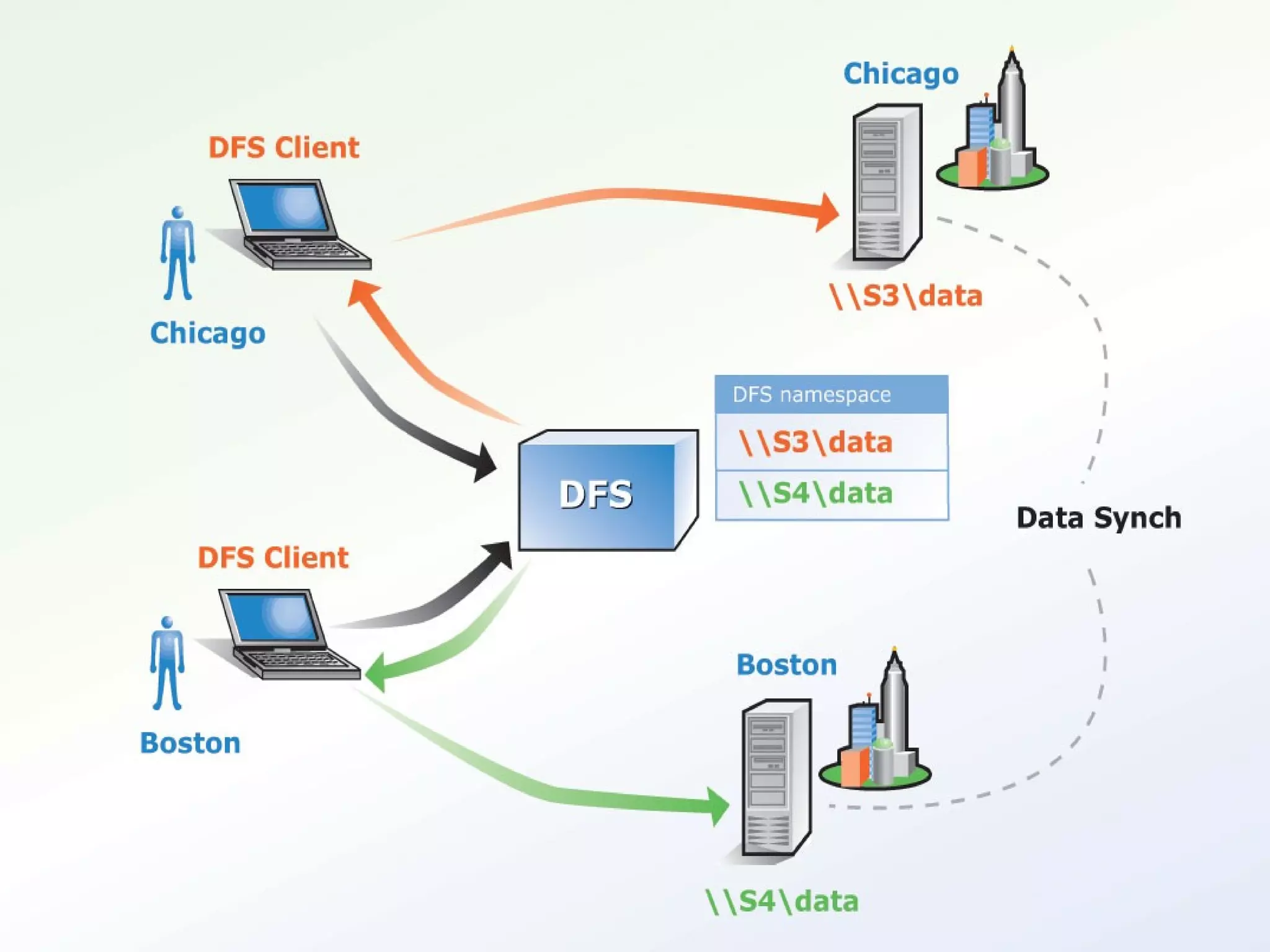
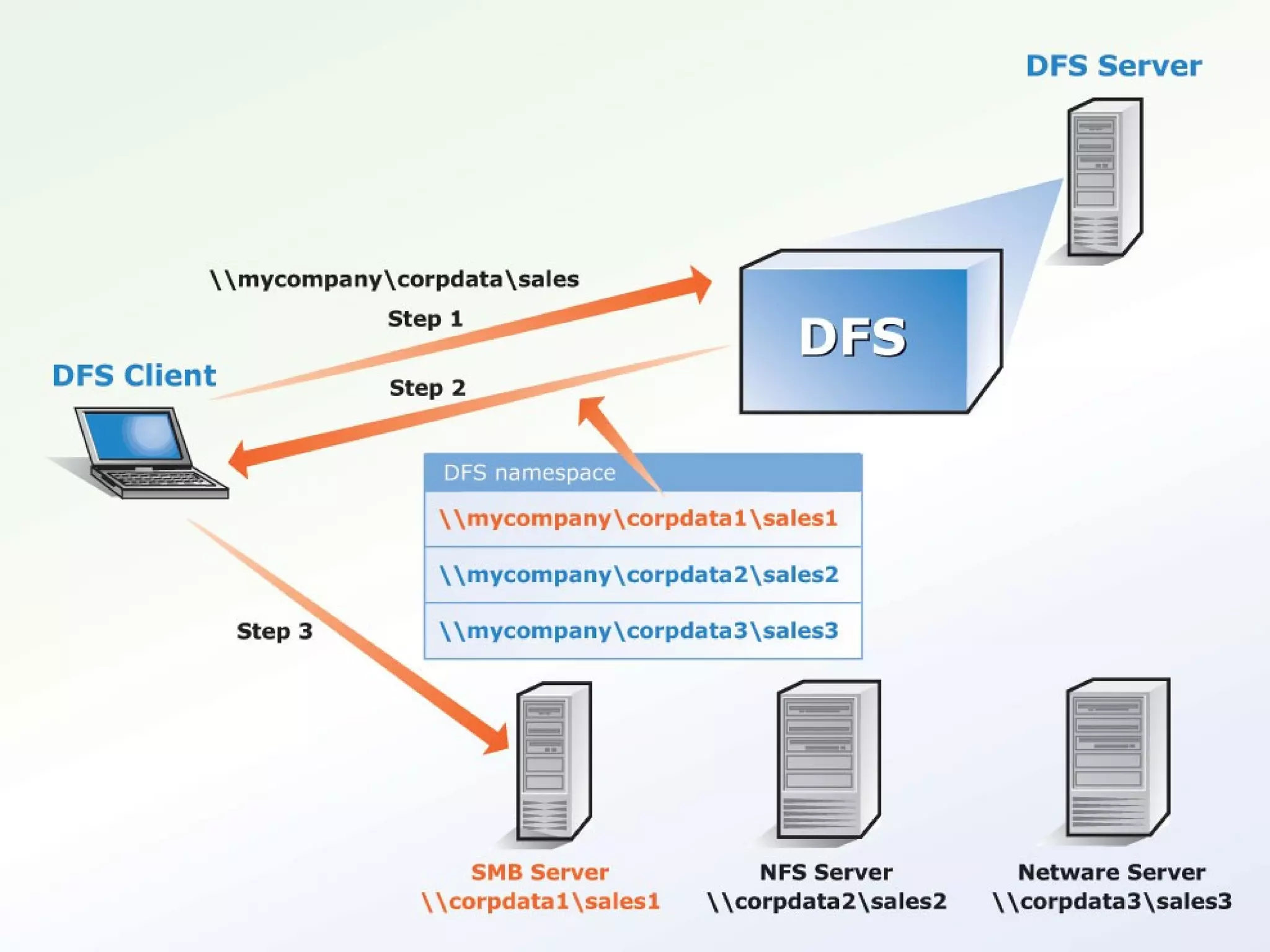
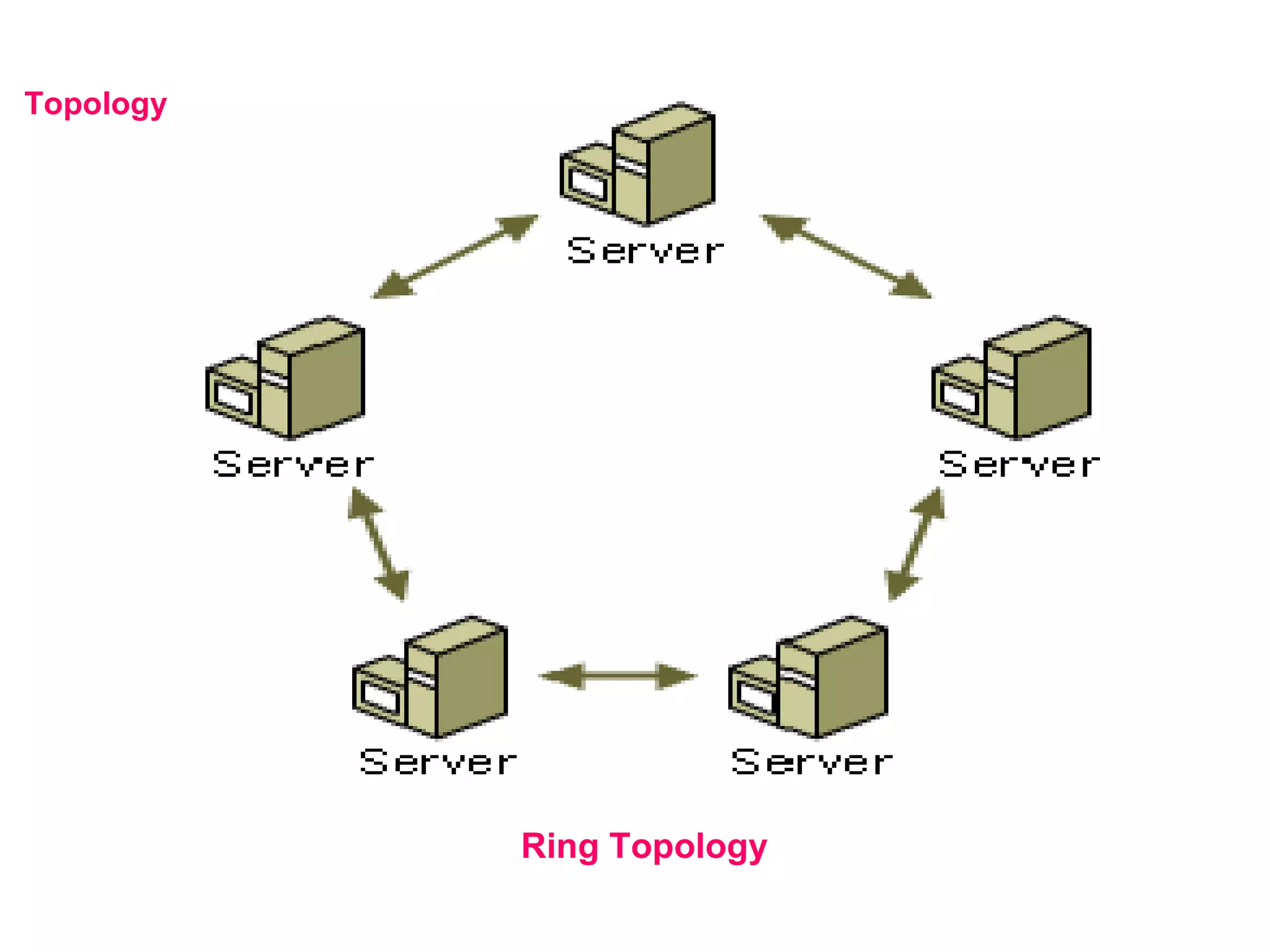
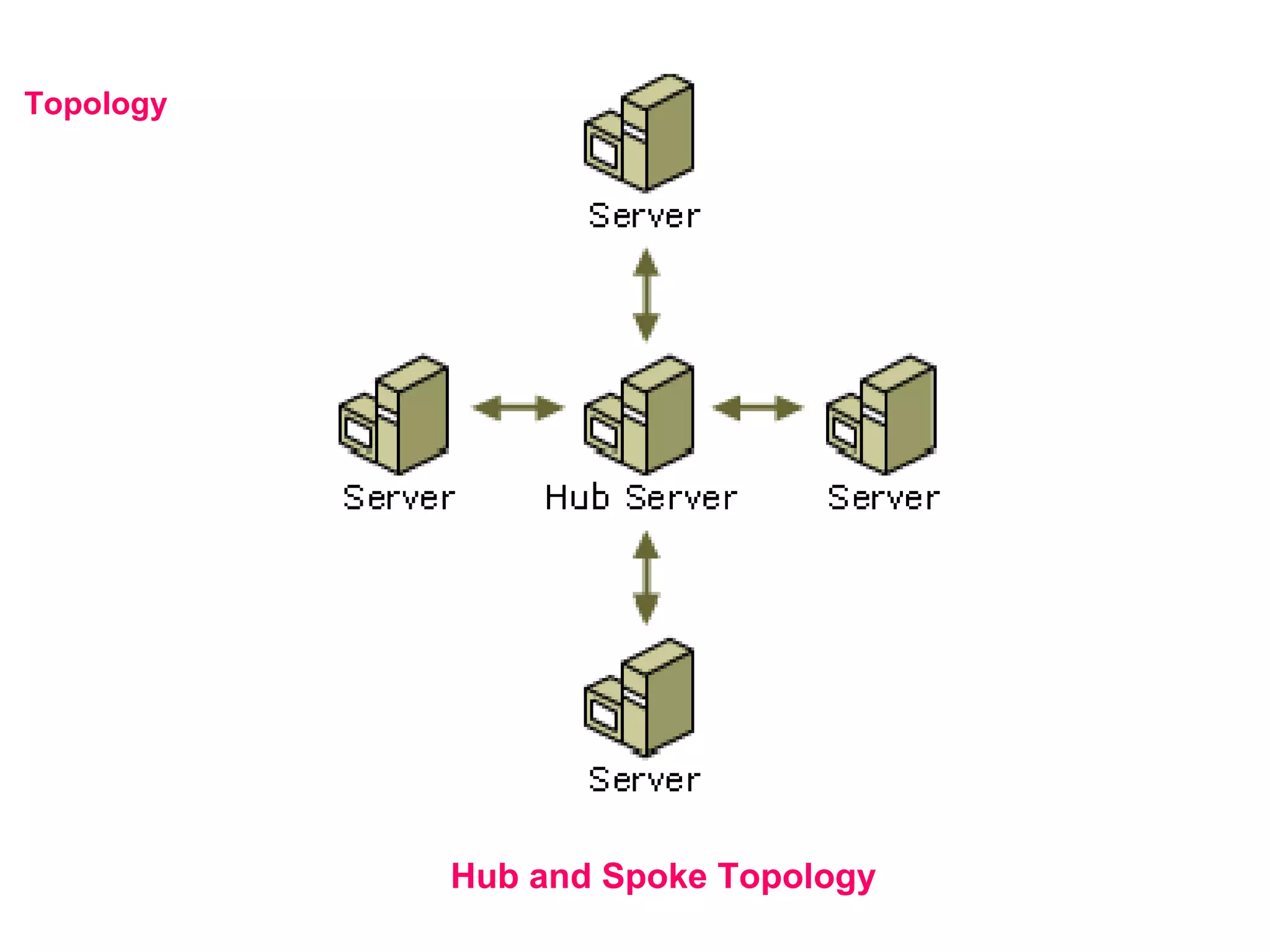
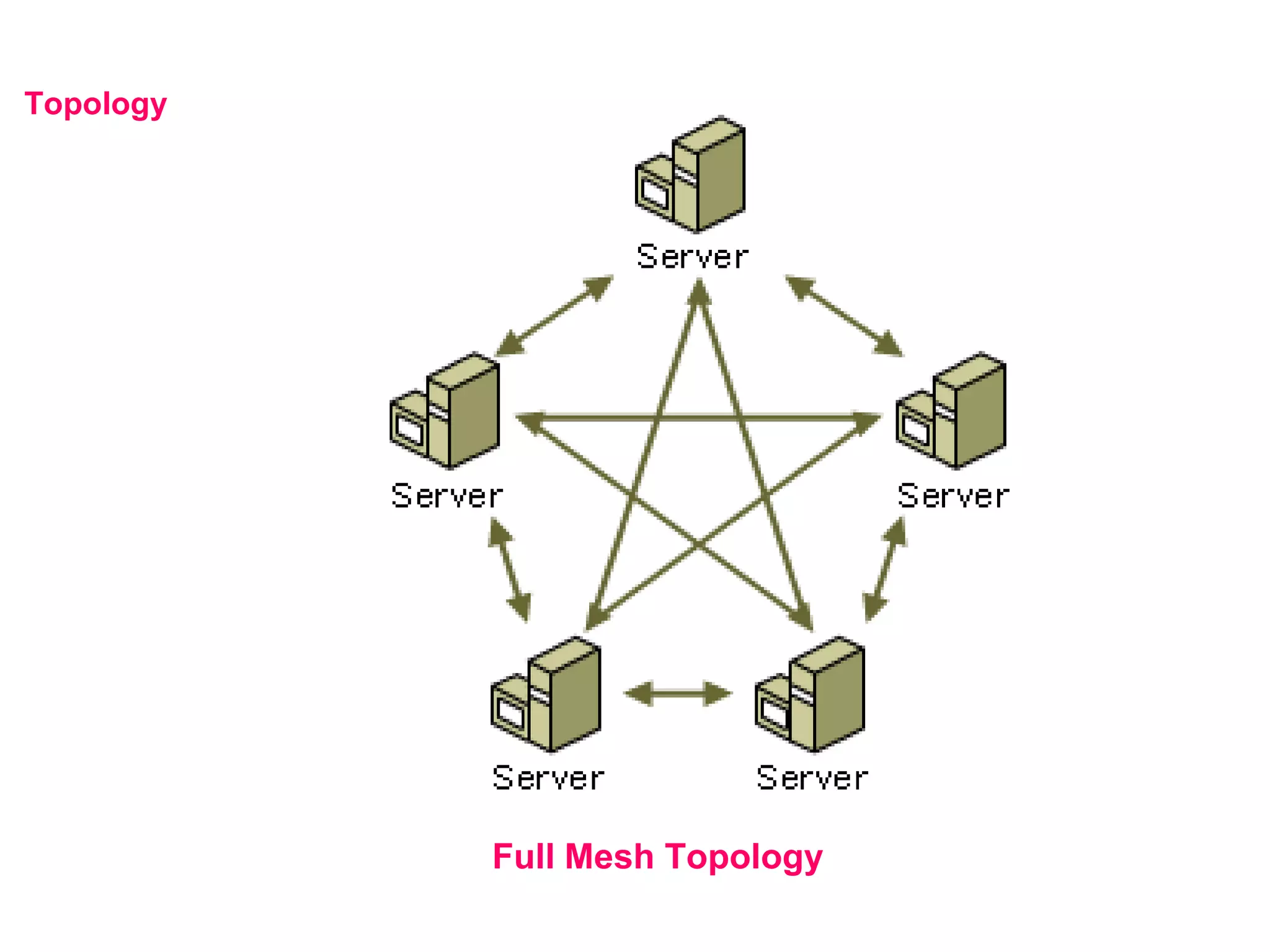
Distributed file system (DFS) allows administrators to make shared files across multiple servers appear to users as if they are in a single location, improving access and management. DFS uses DFSroots, DFSlinks, and targets to map the logical DFS structure to physical shared folders. Disk quotas track and limit disk space usage on NTFS partitions to prevent users from exceeding allotted space and log events when limits are reached, helping manage storage usage.