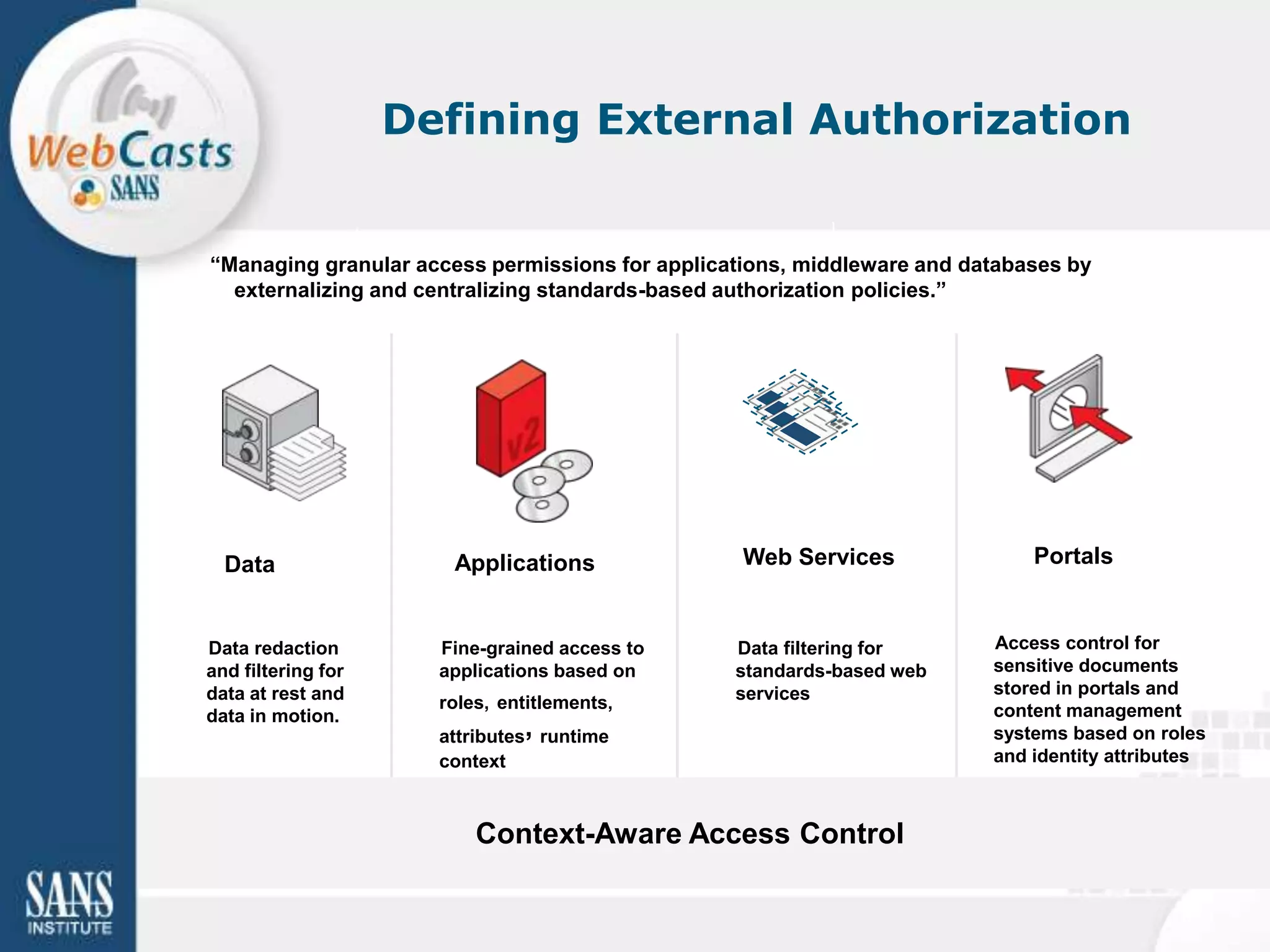
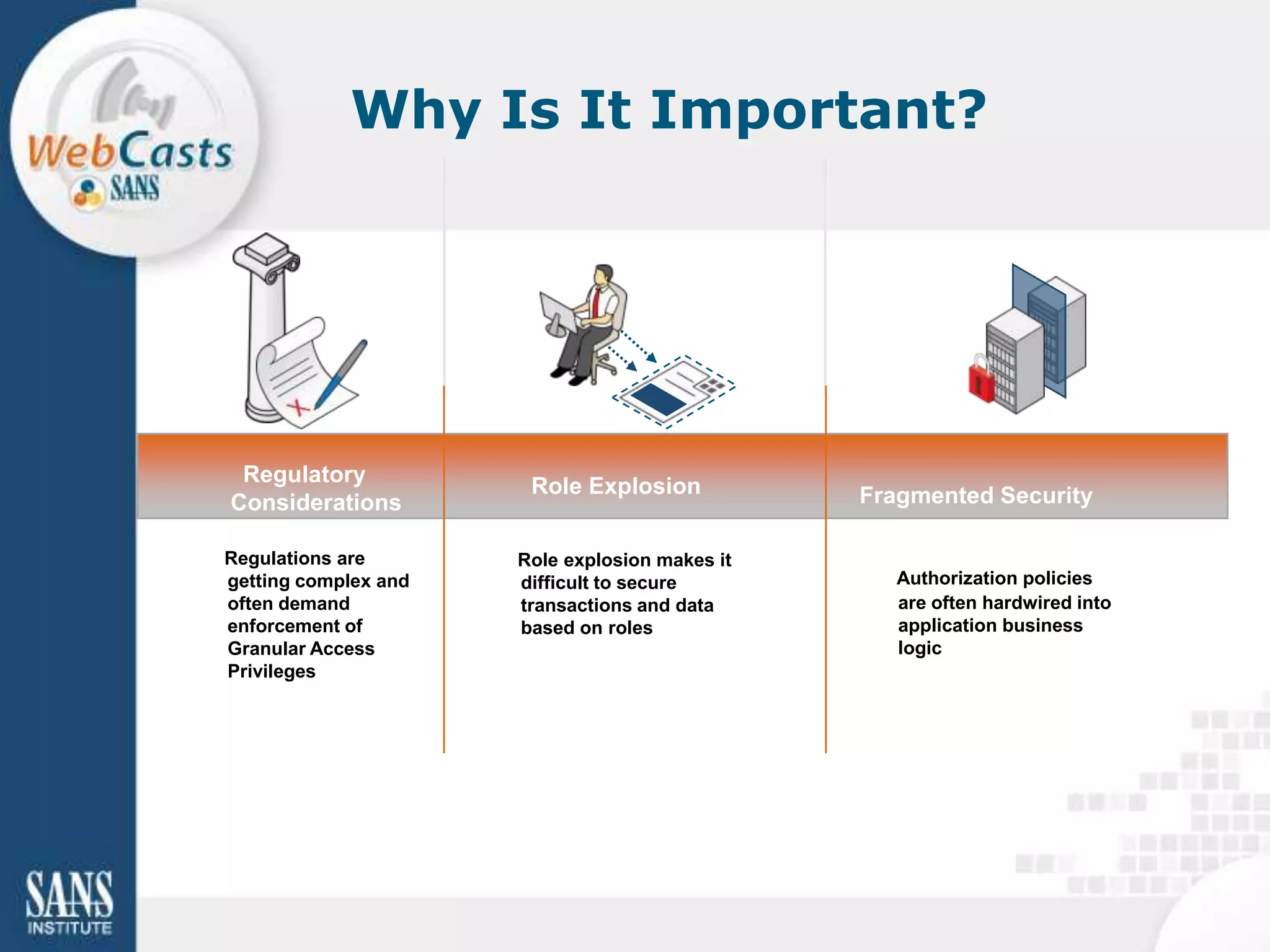
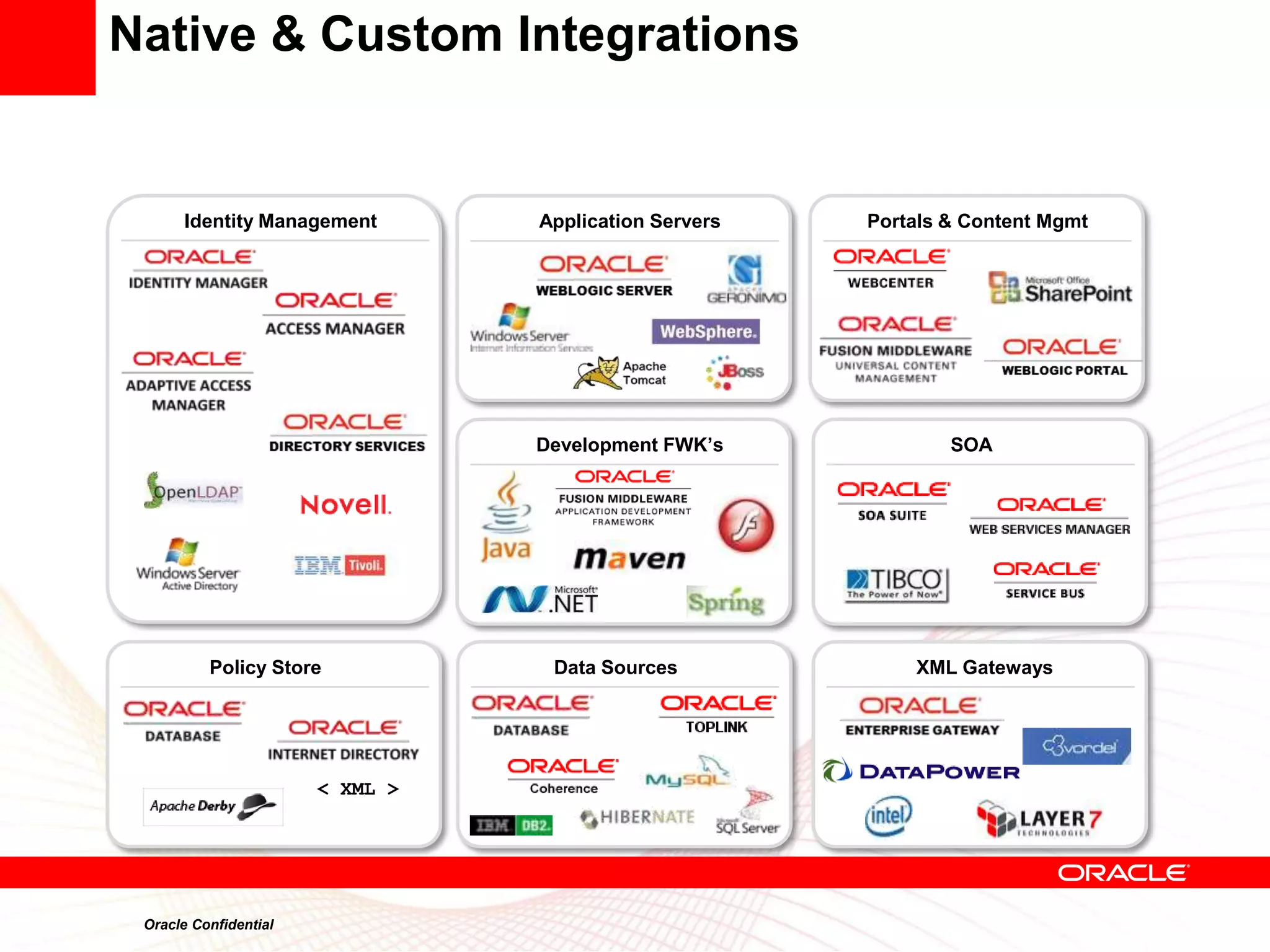
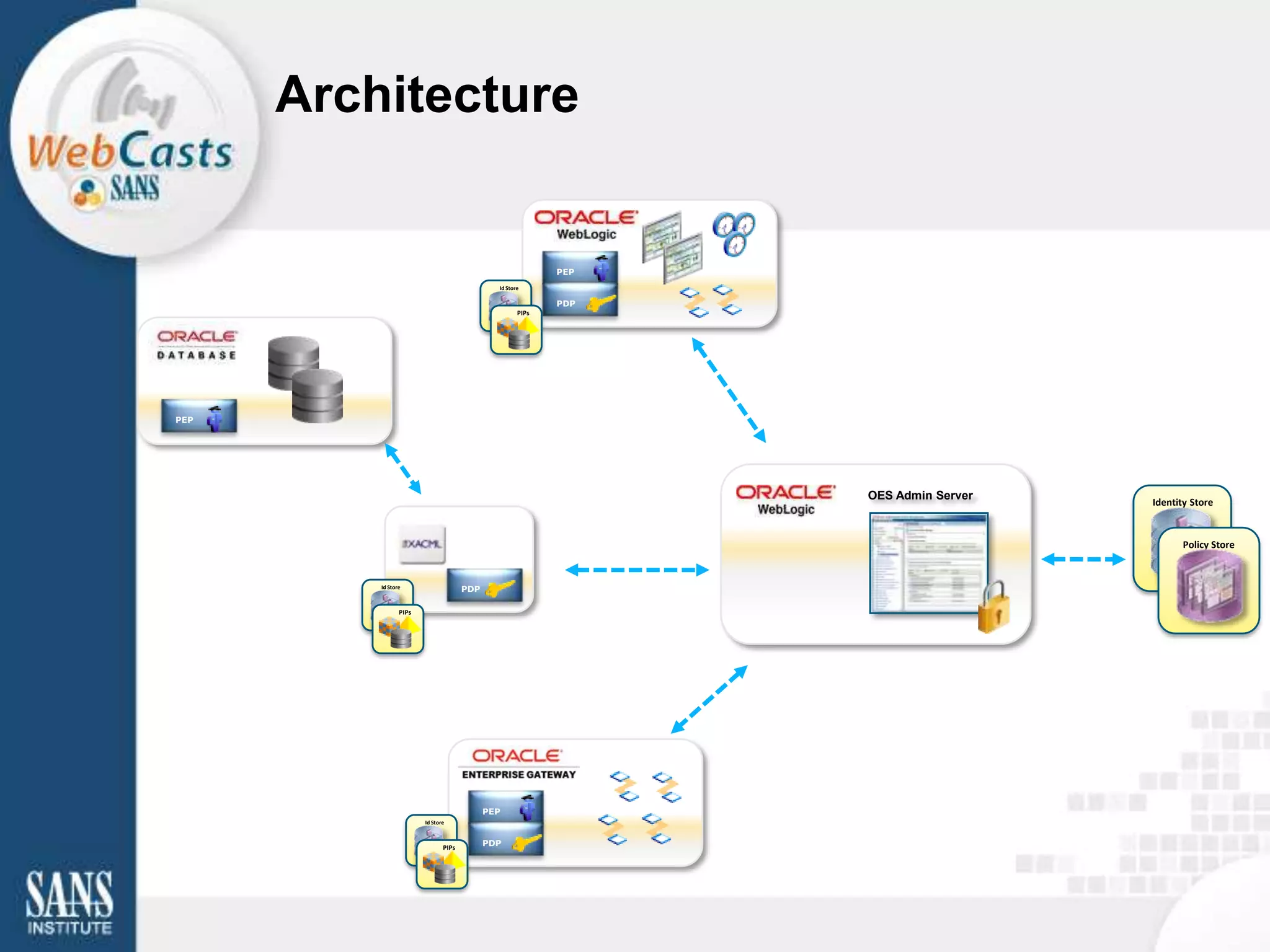
The document provides an overview of Oracle Entitlements Server, an external authorization product that provides unified authorization for applications, web services, portals and databases. It discusses common use cases for external authorization and how Oracle Entitlements Server addresses them through a standards-based declarative security model and real-time authorization enforcement. The presentation then reviews Oracle Entitlements Server's architecture, integration capabilities, and how it can be used for application access control, data security, SharePoint security and web services security.