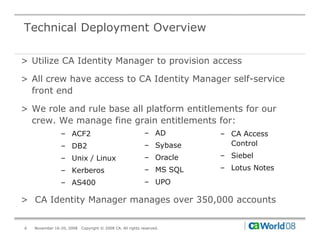
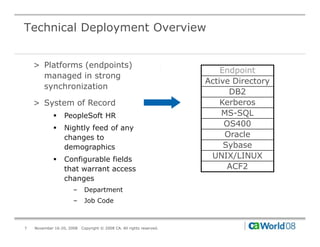
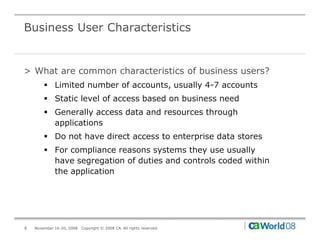
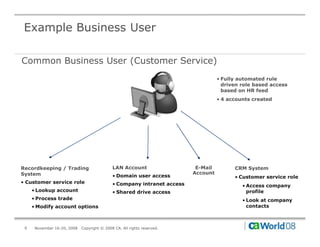
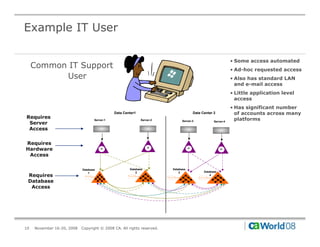
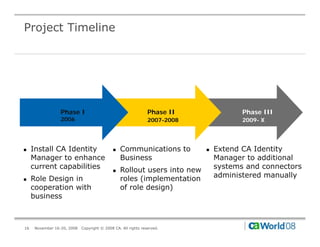
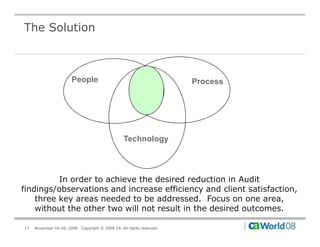
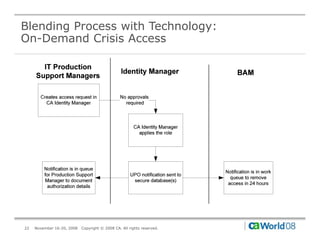
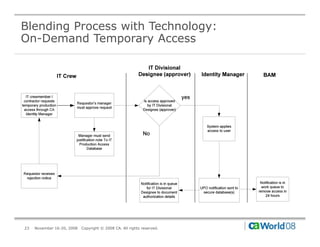
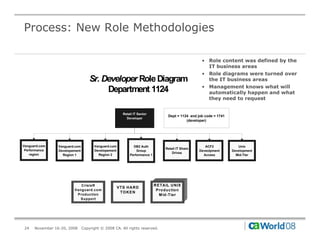
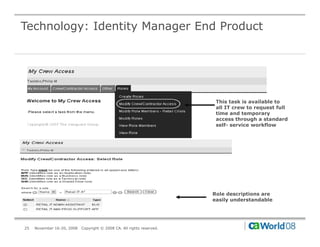
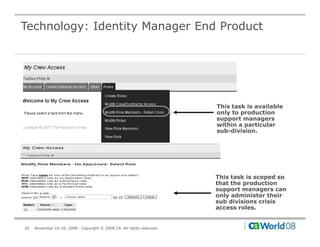
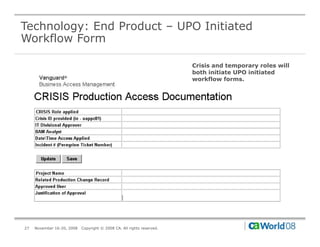
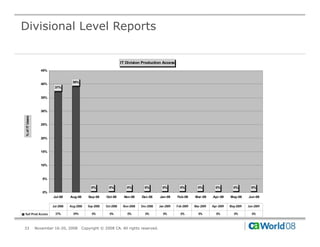
The document discusses Vanguard's use of CA Identity Manager to provision access for both IT and business users. It describes how business users typically have a limited number of static accounts while IT users often require dynamic access across many systems. The presentation outlines how CA Identity Manager helps automate provisioning for business users while also granting necessary access more quickly for IT users to resolve outages. It provides insights into Vanguard's deployment and how their environment improved by gaining control and auditability of access requests after implementing CA Identity Manager.