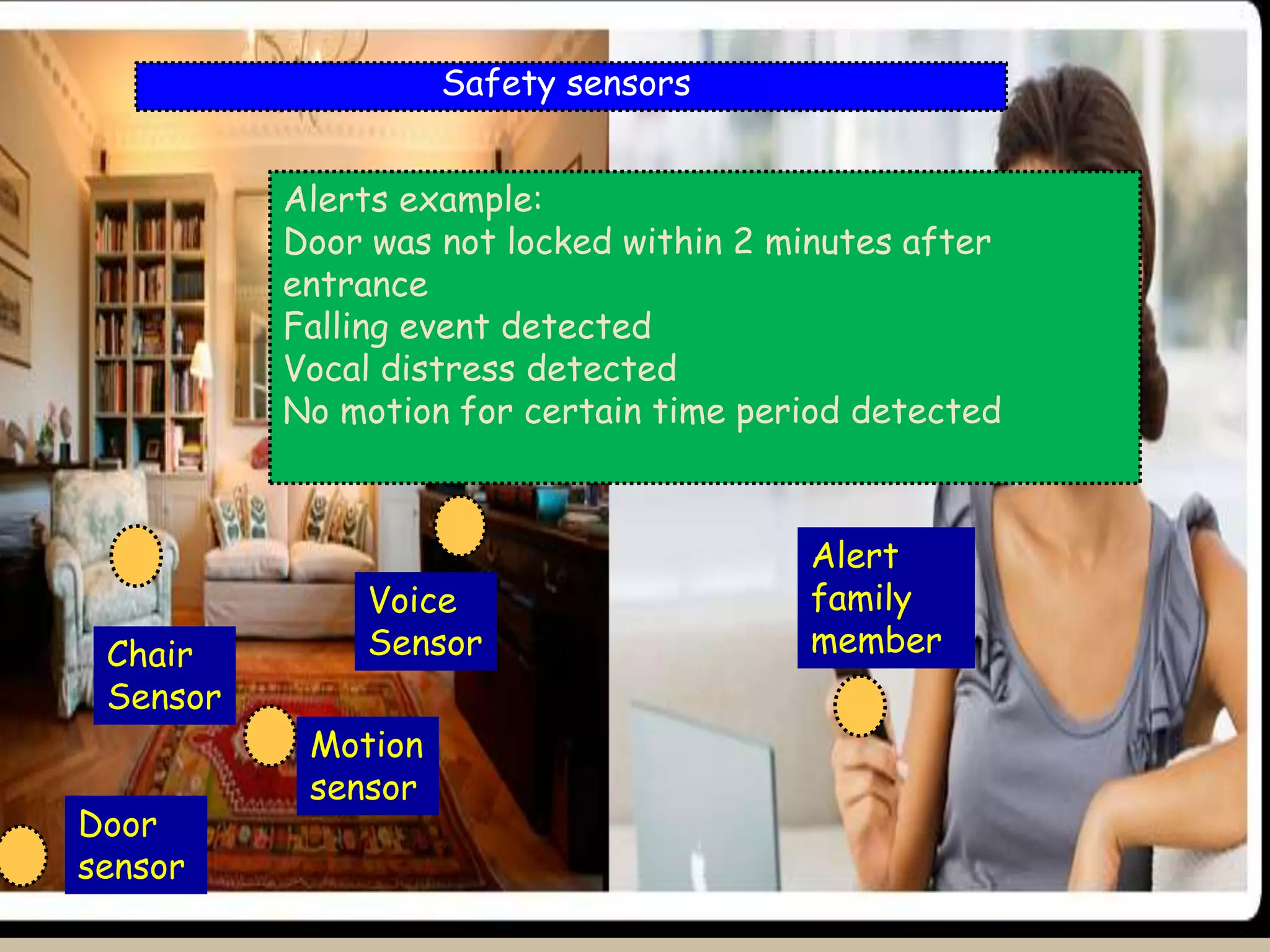
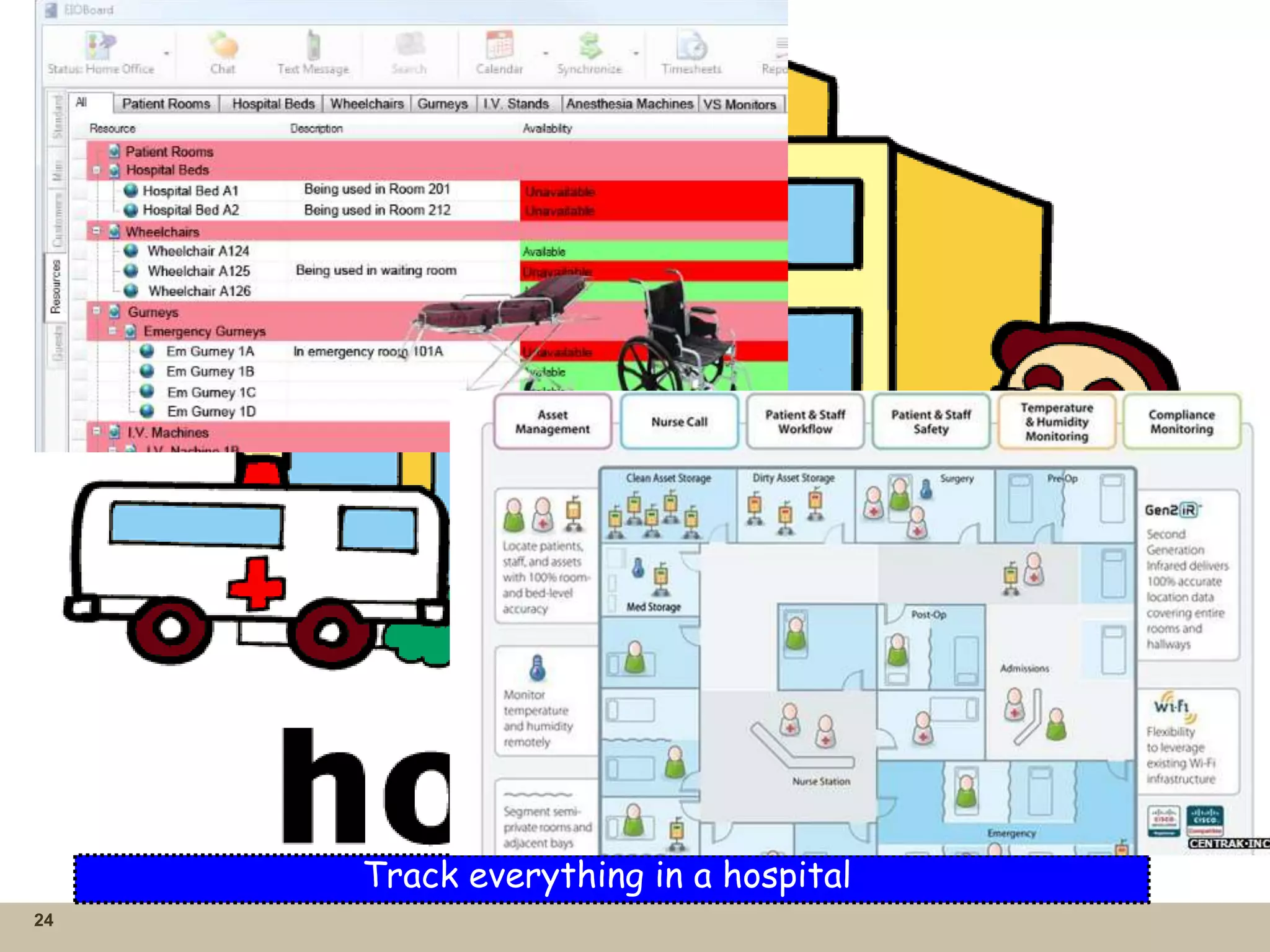
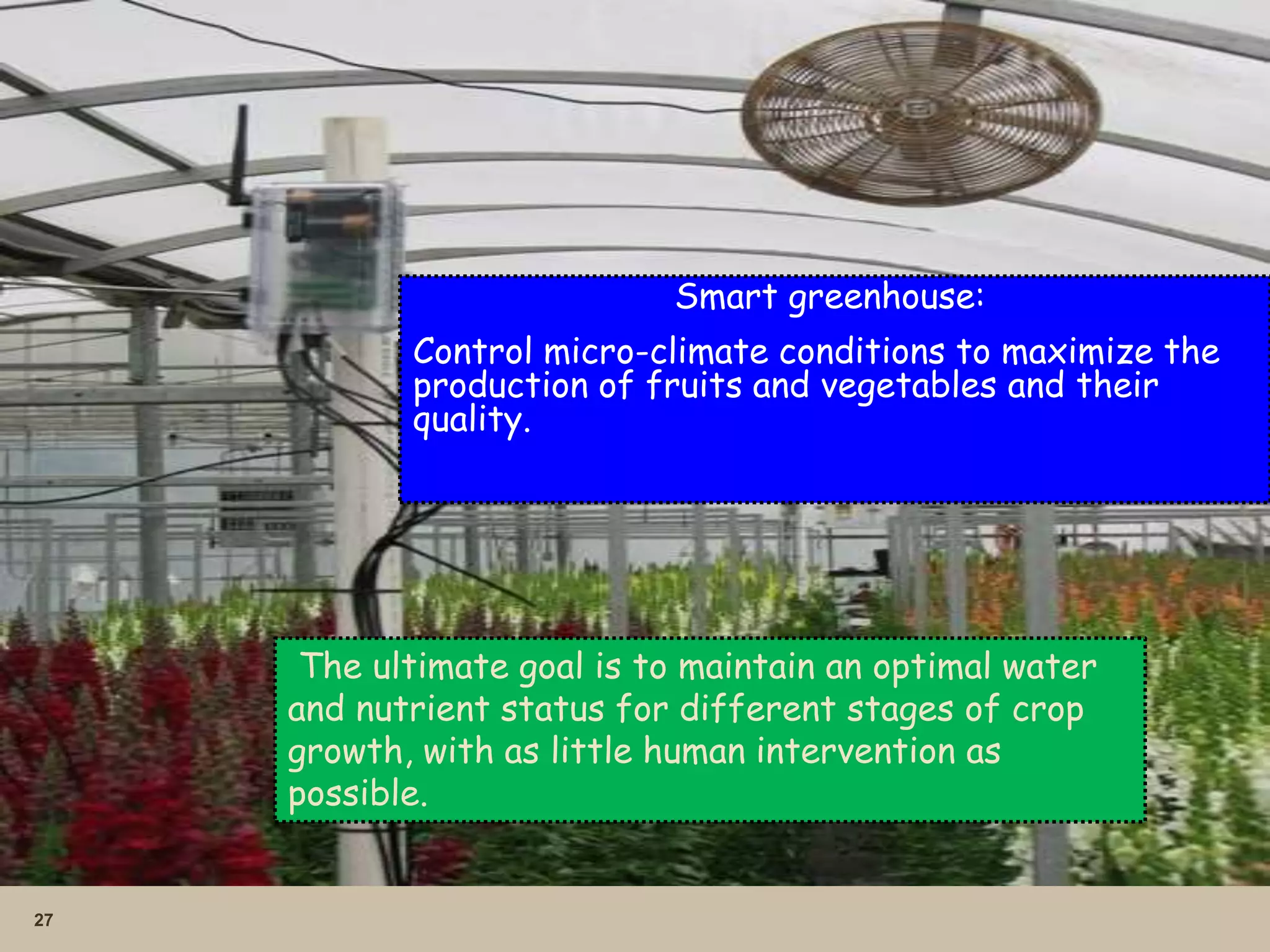
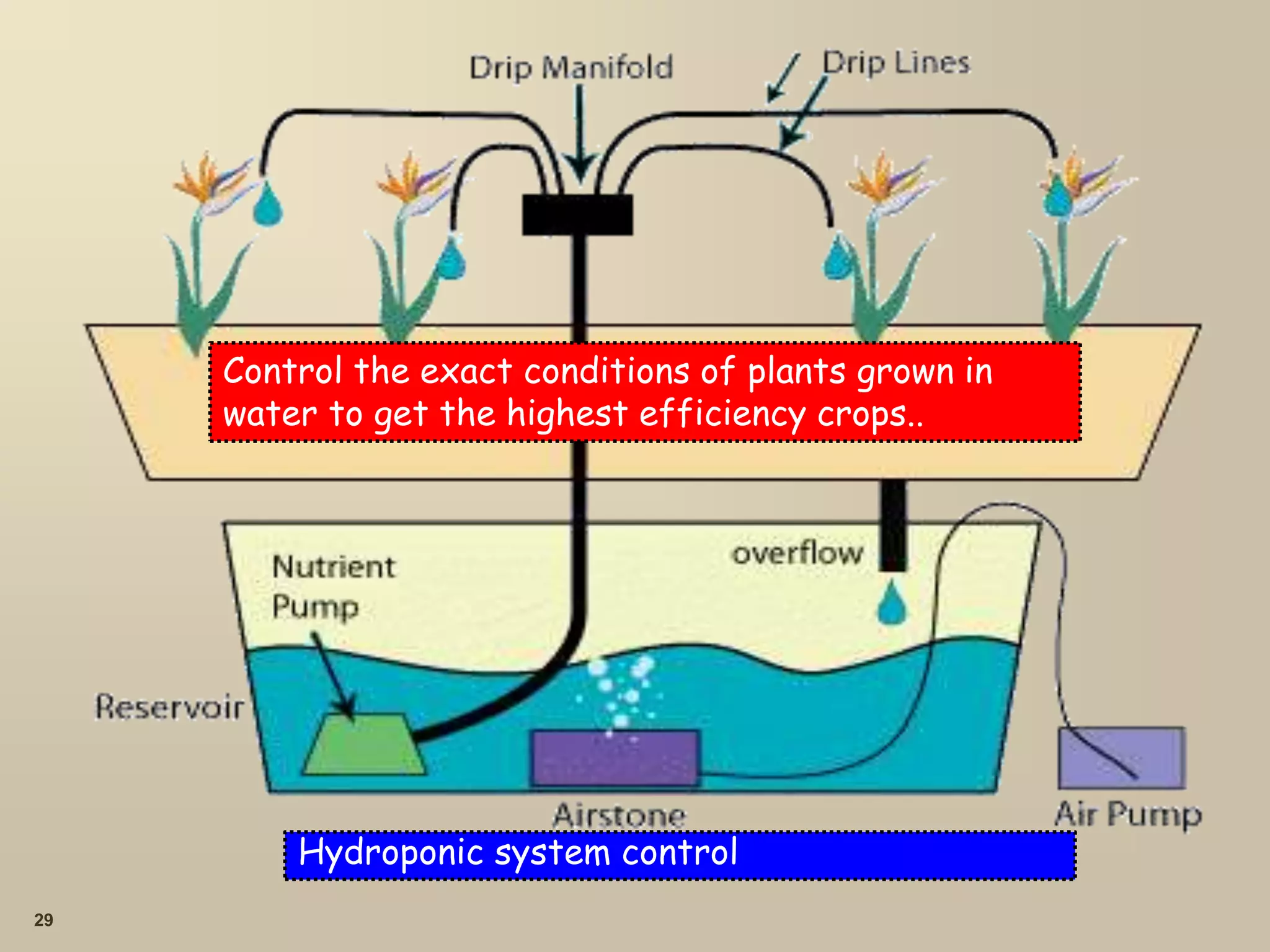
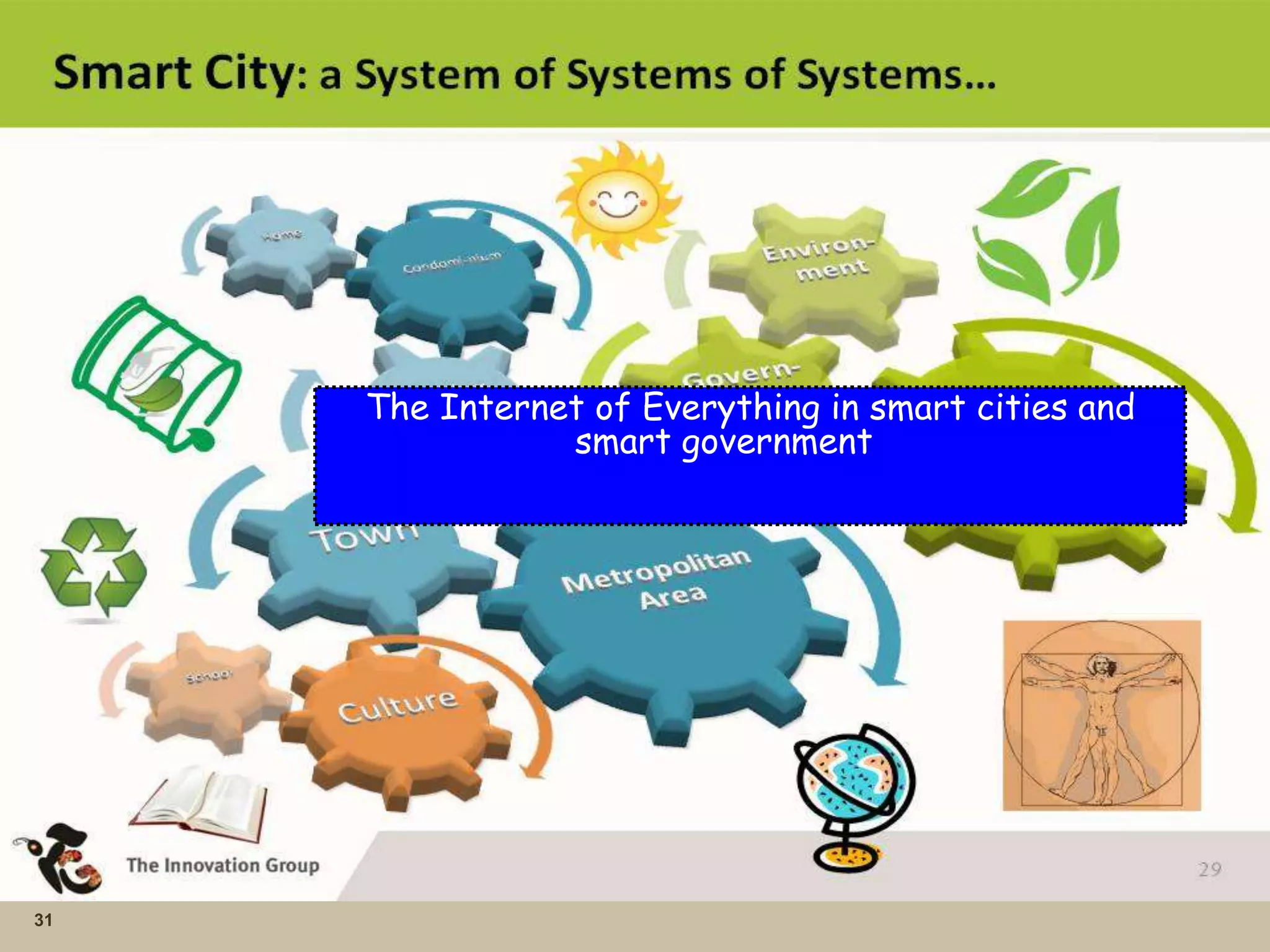
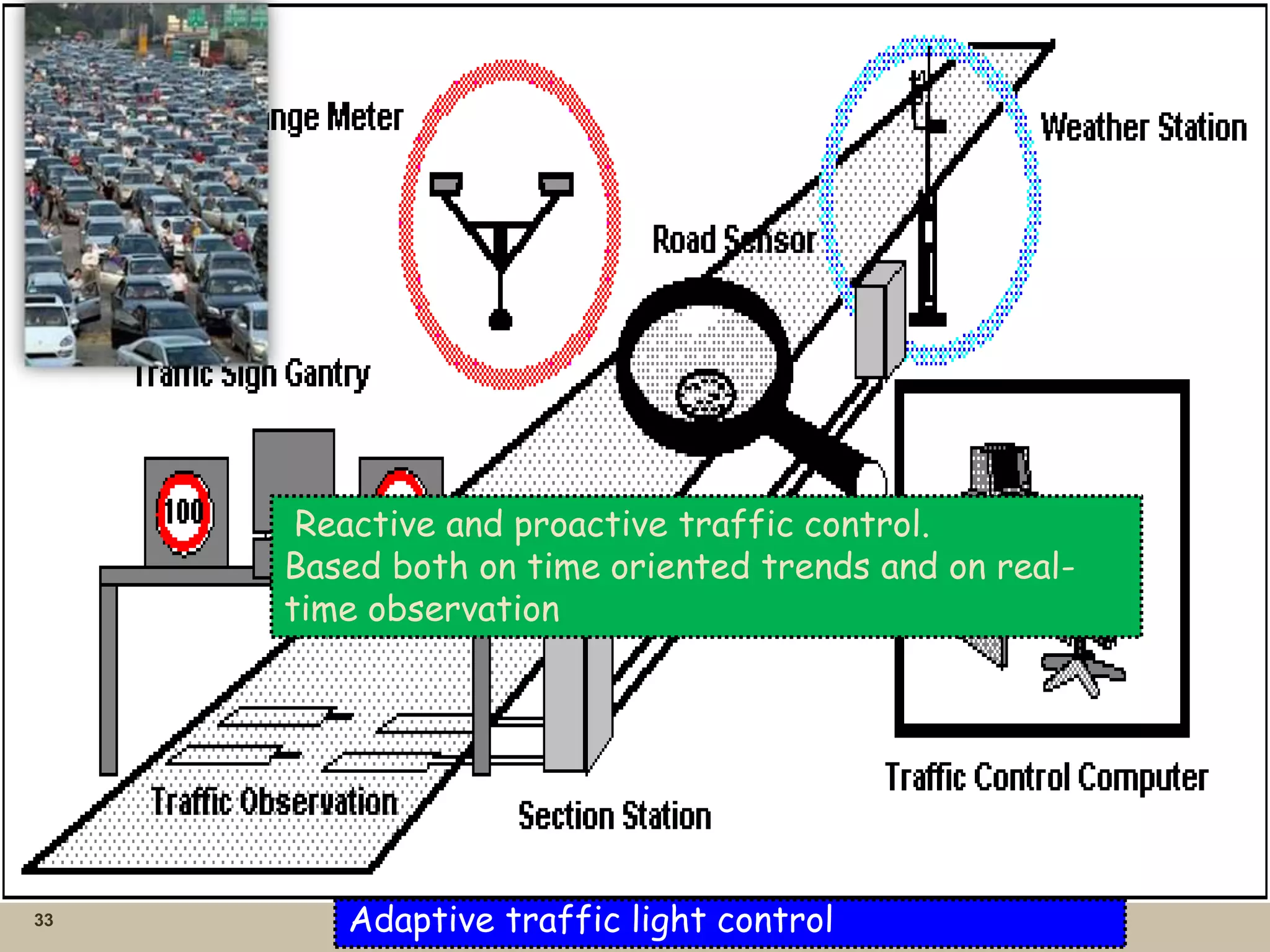
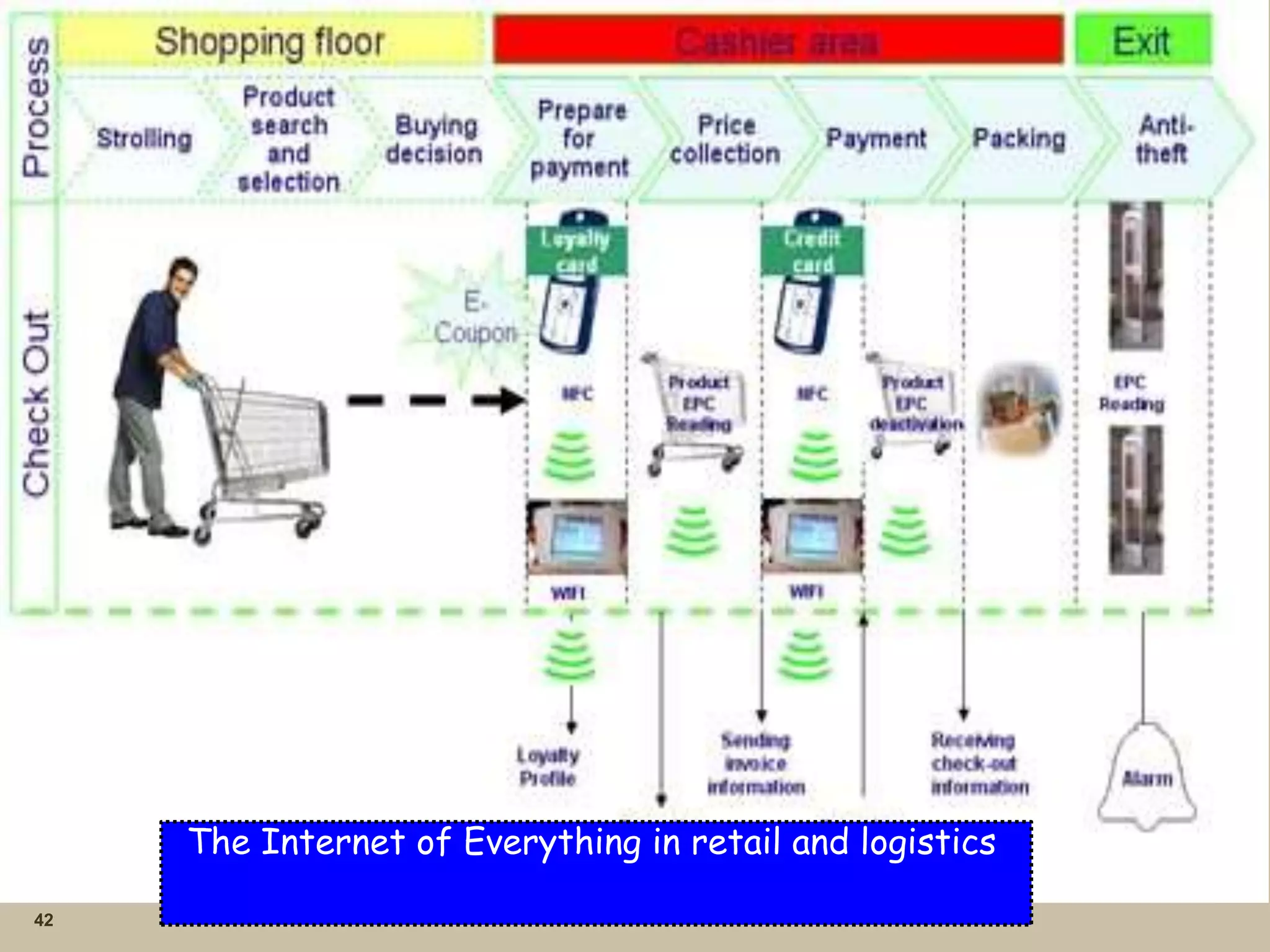
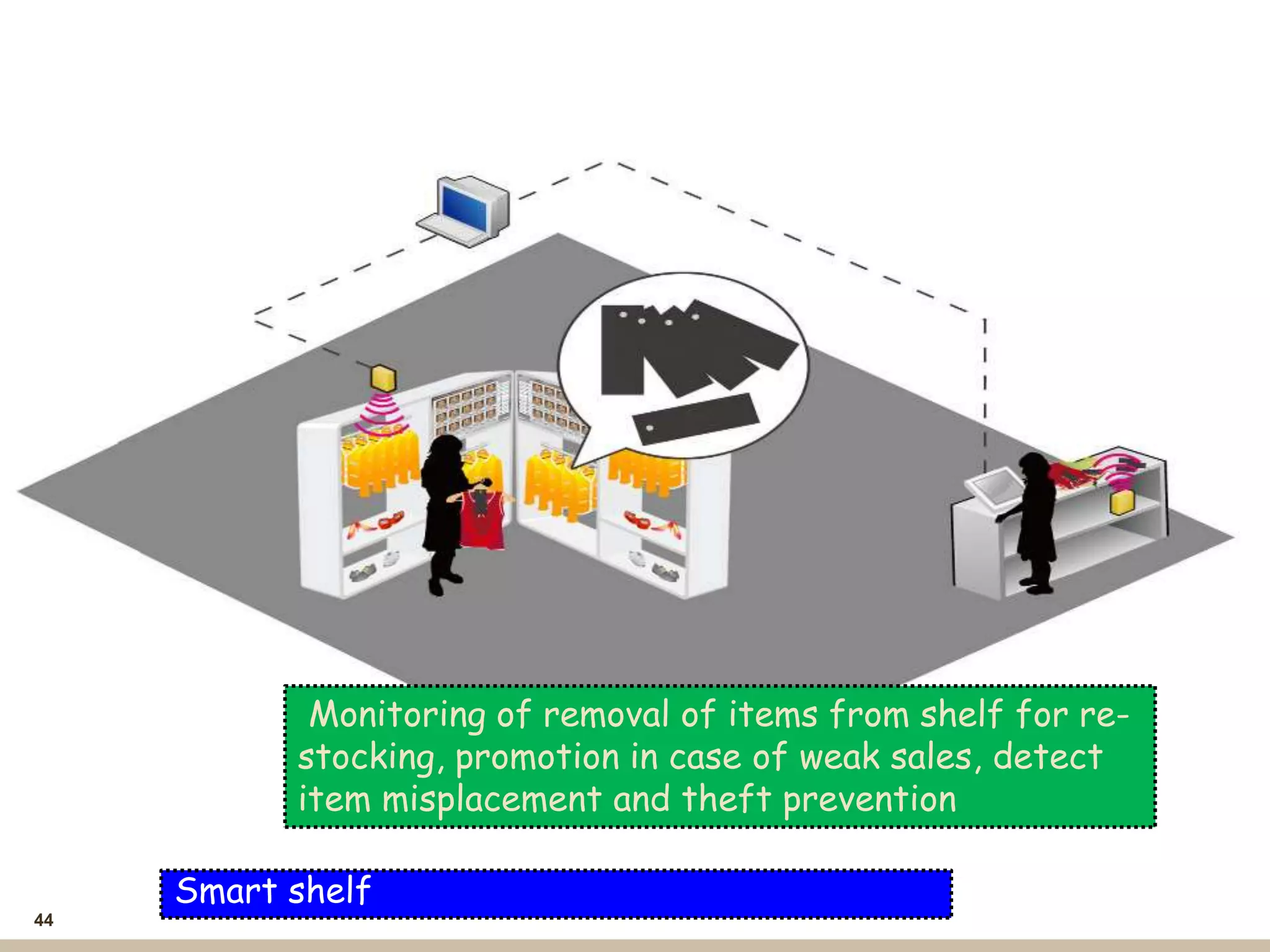
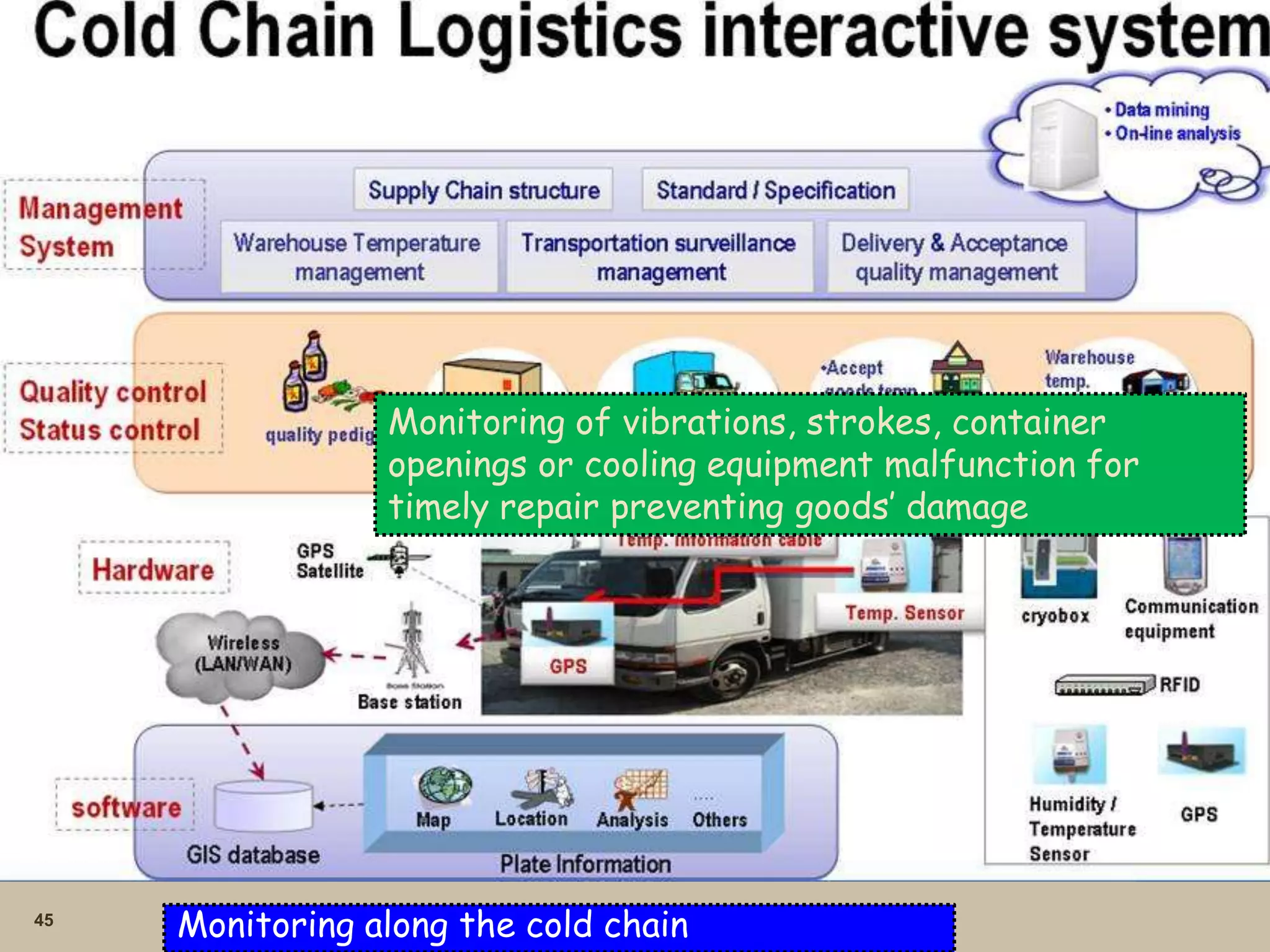
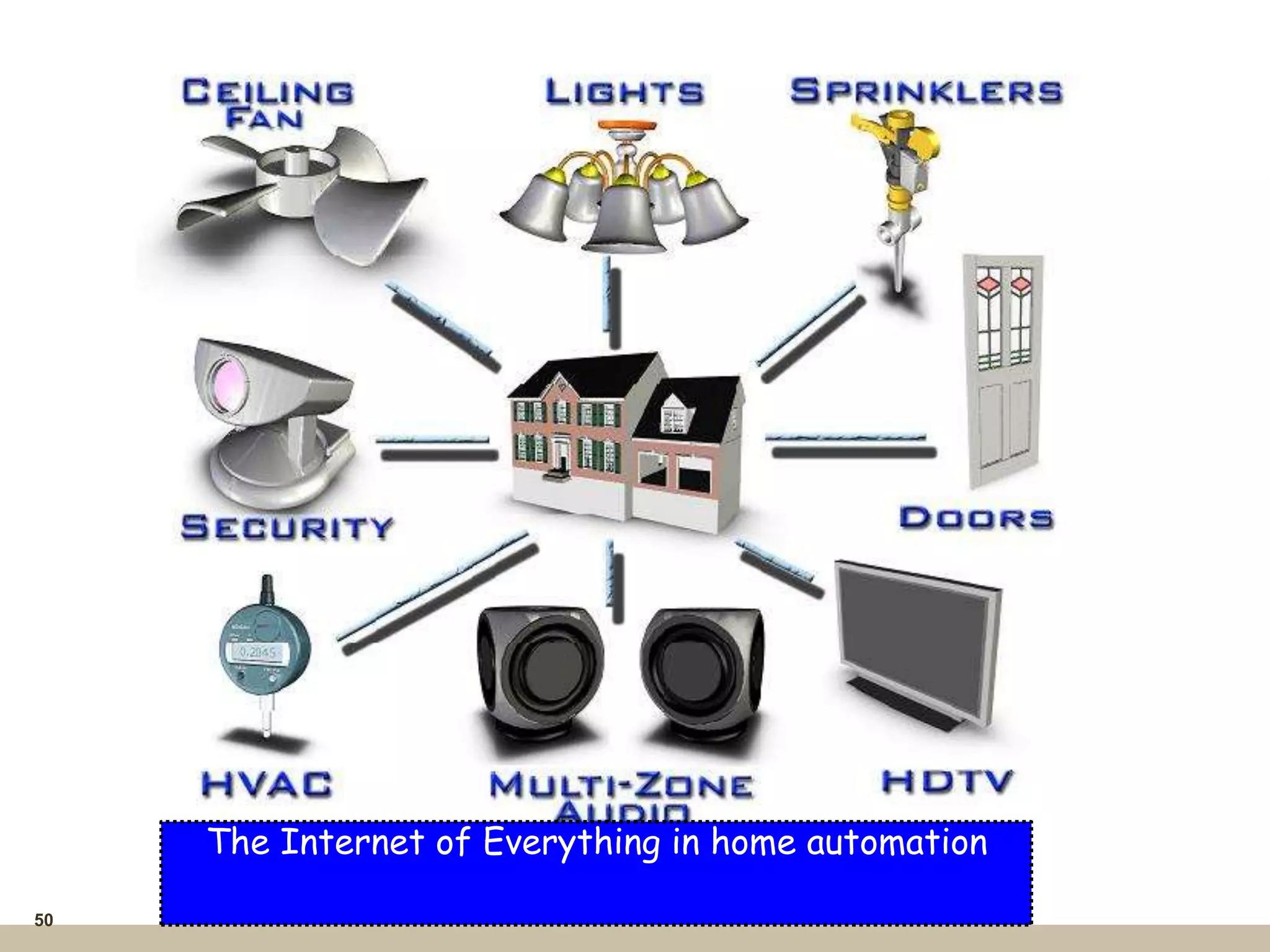
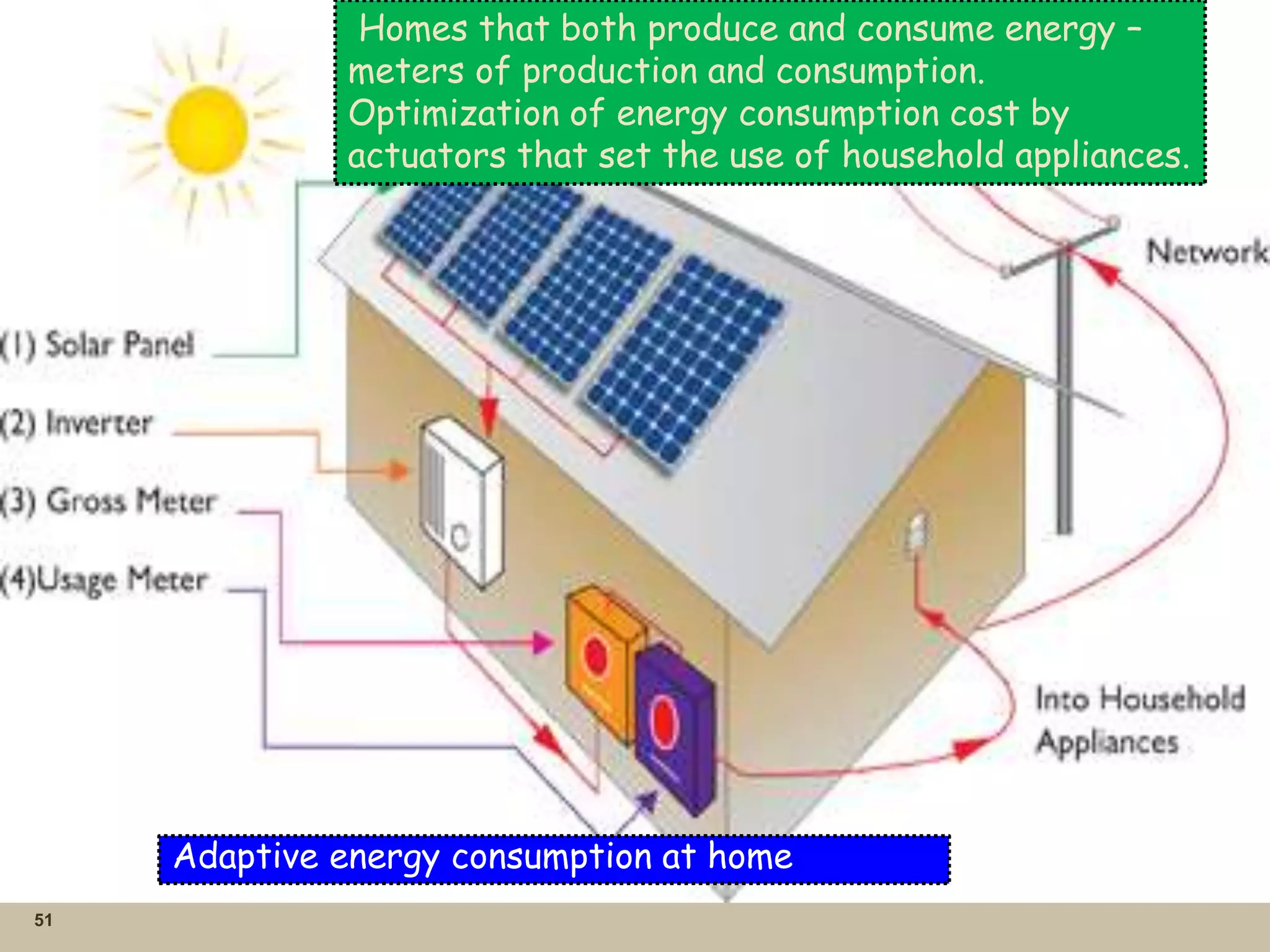
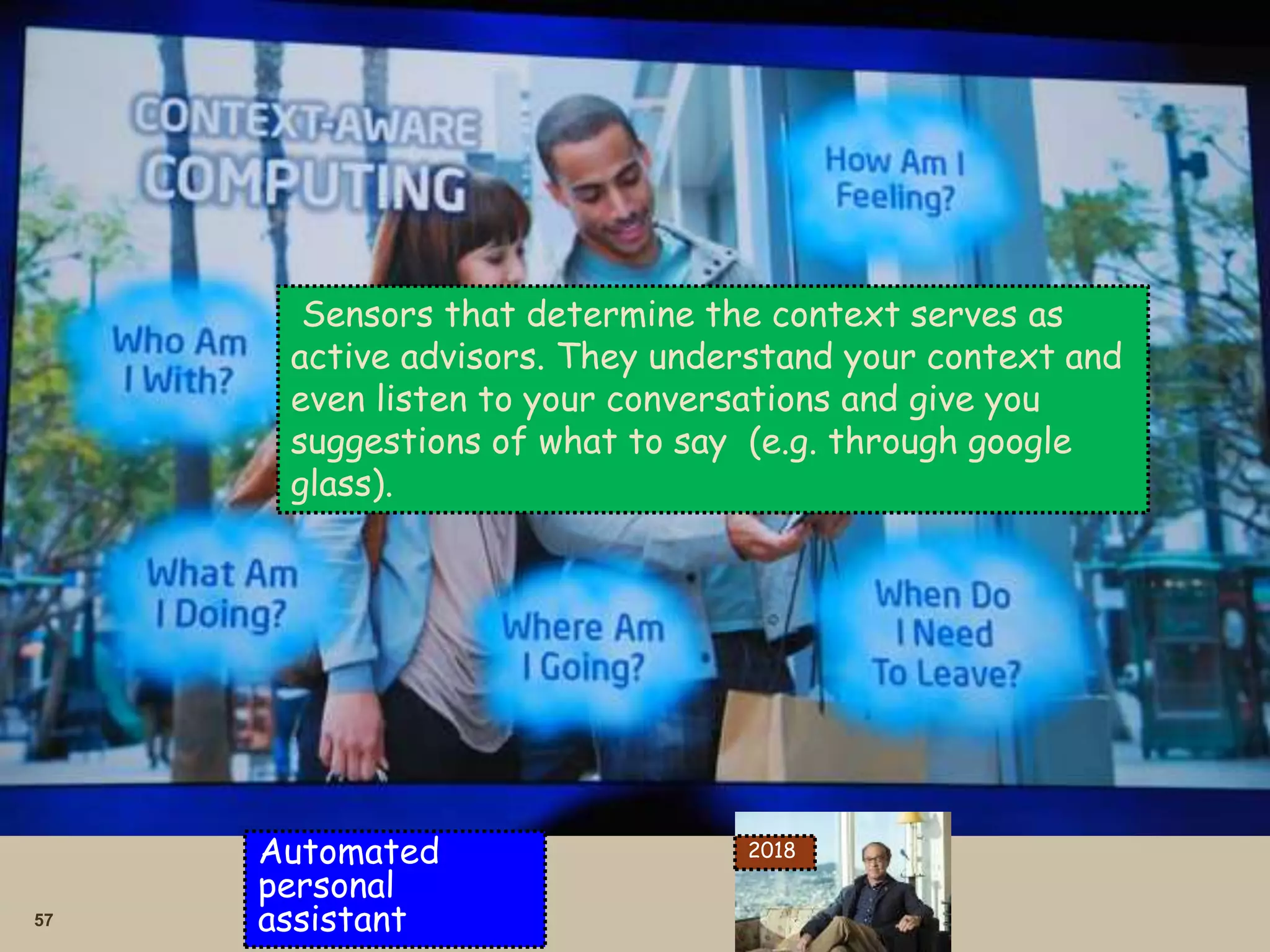
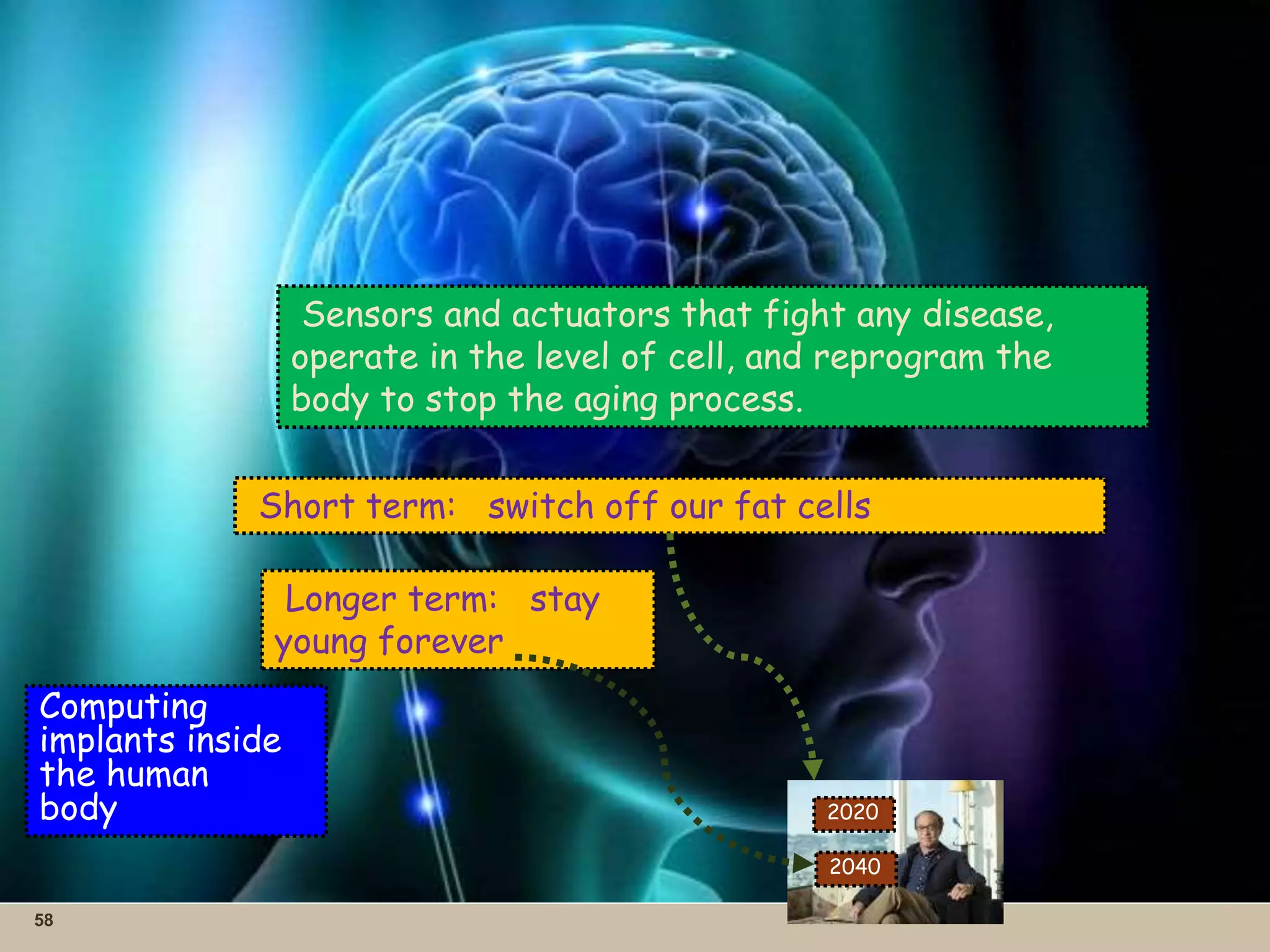
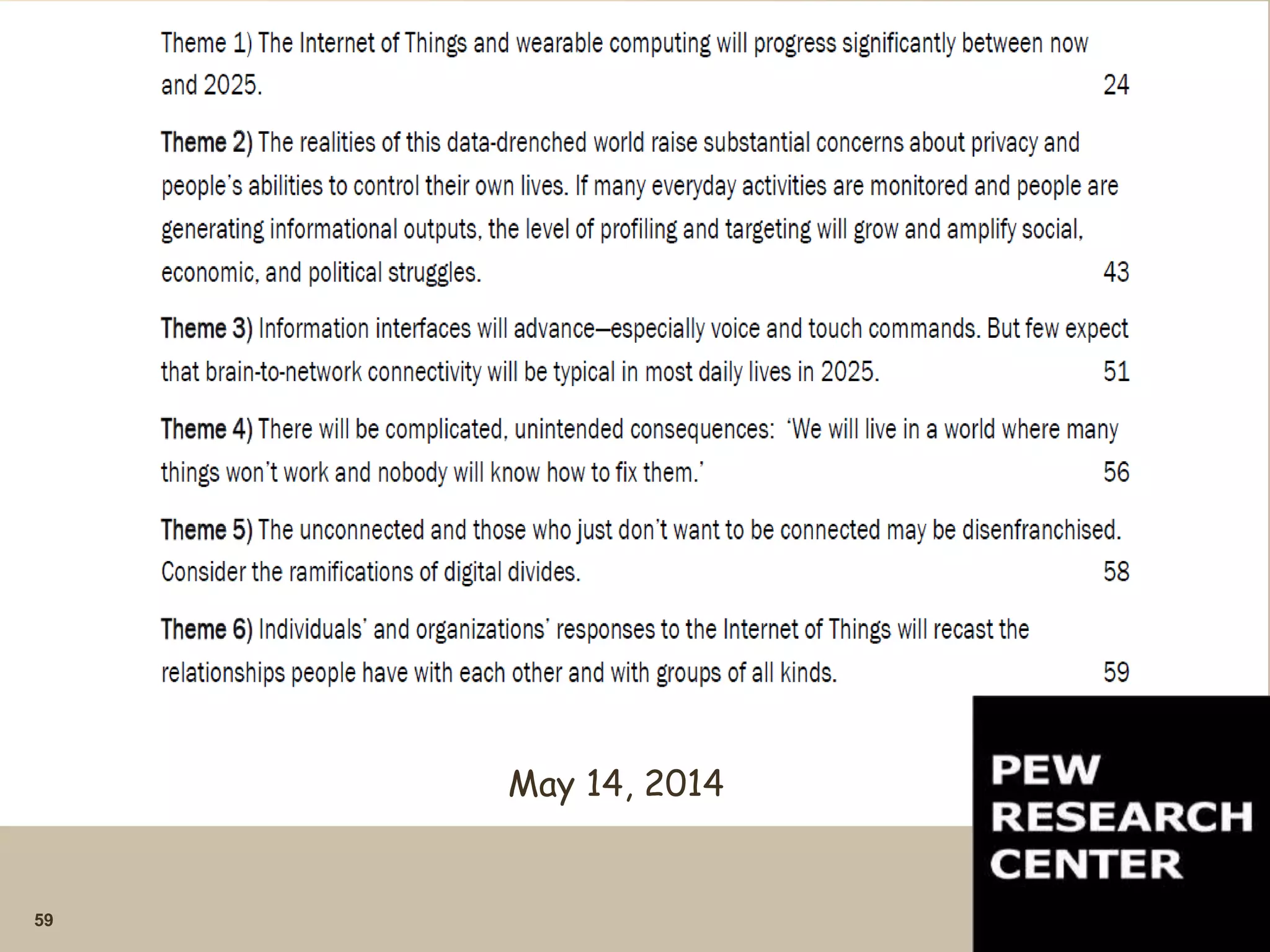
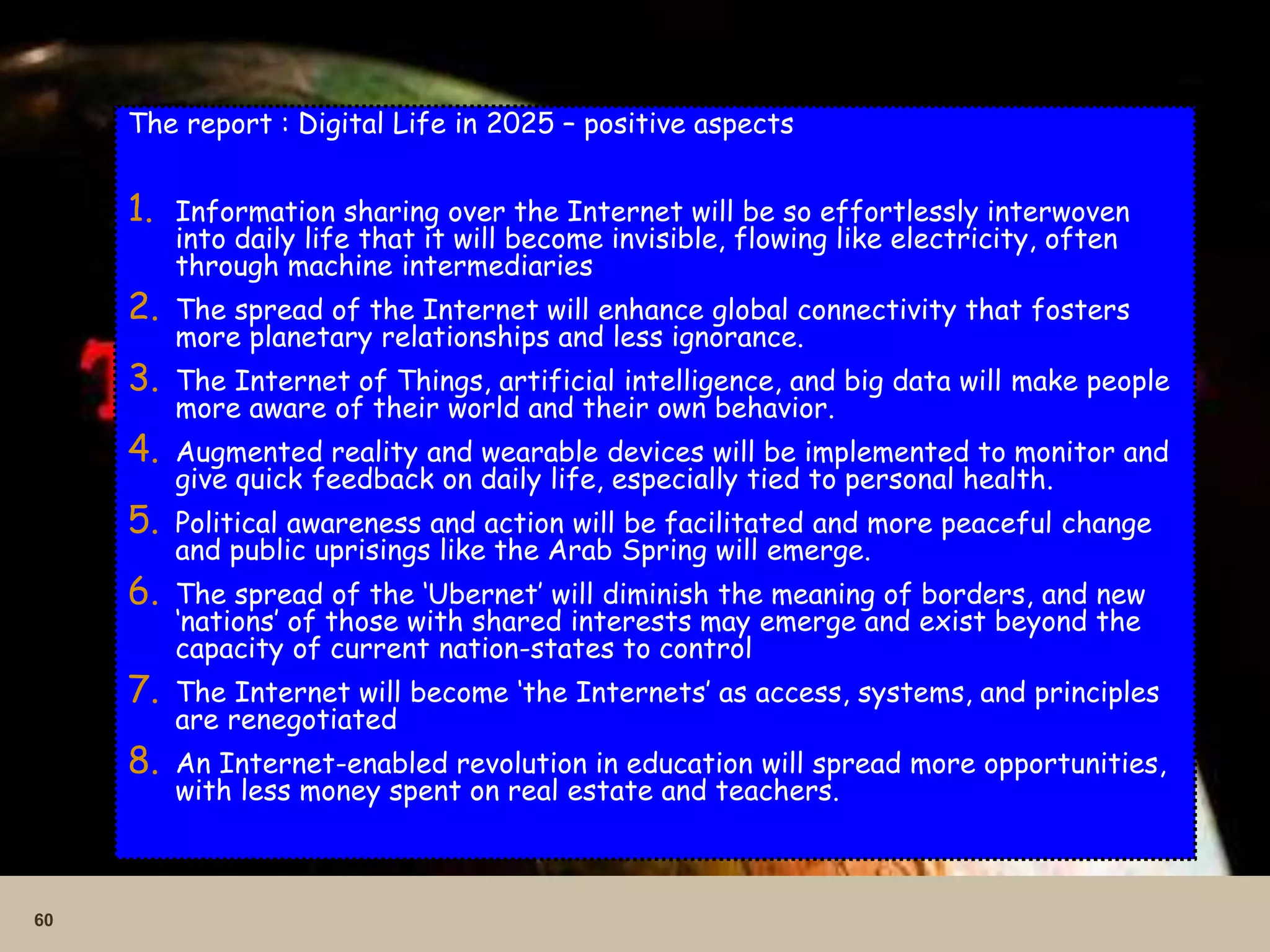
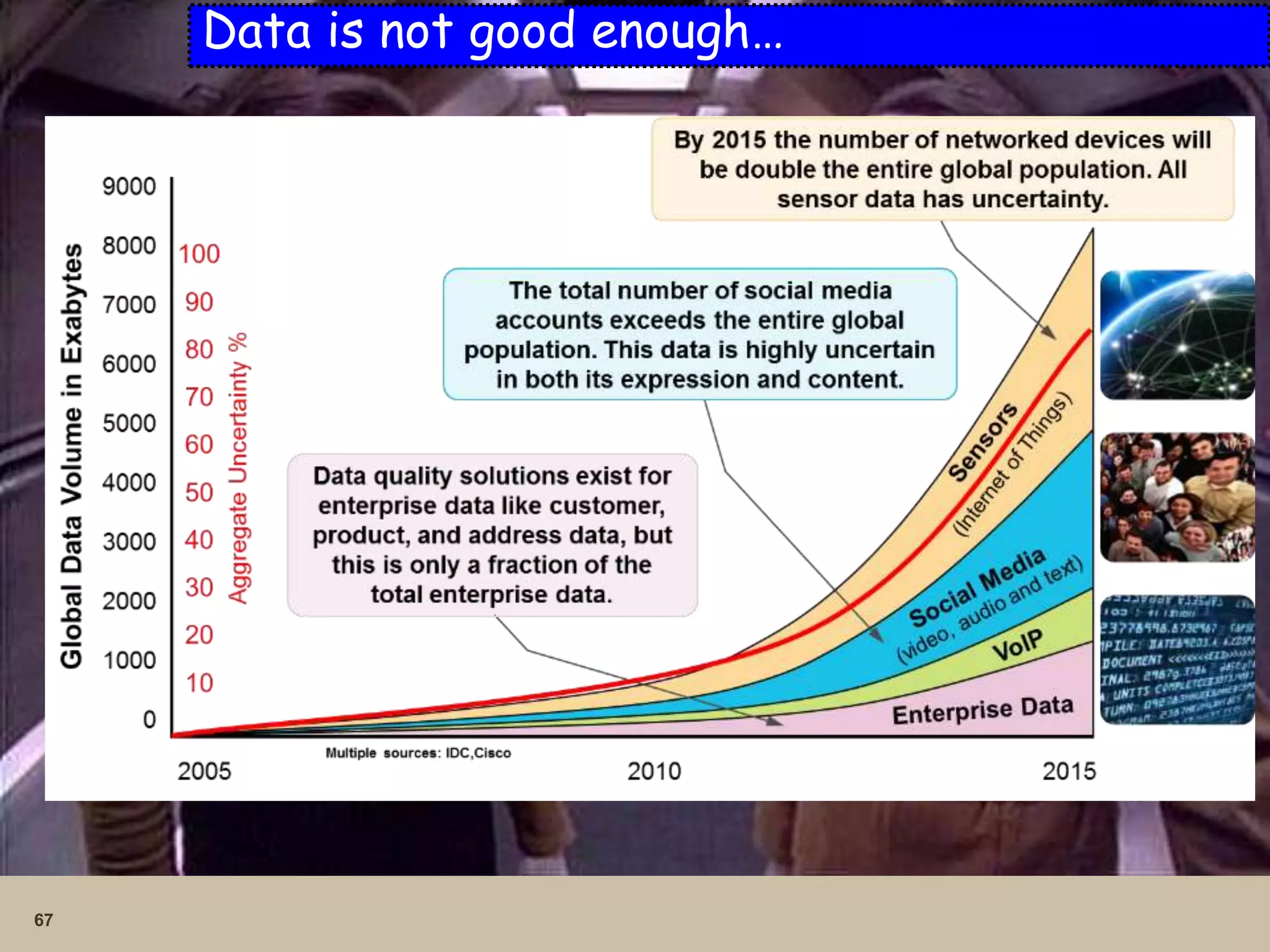
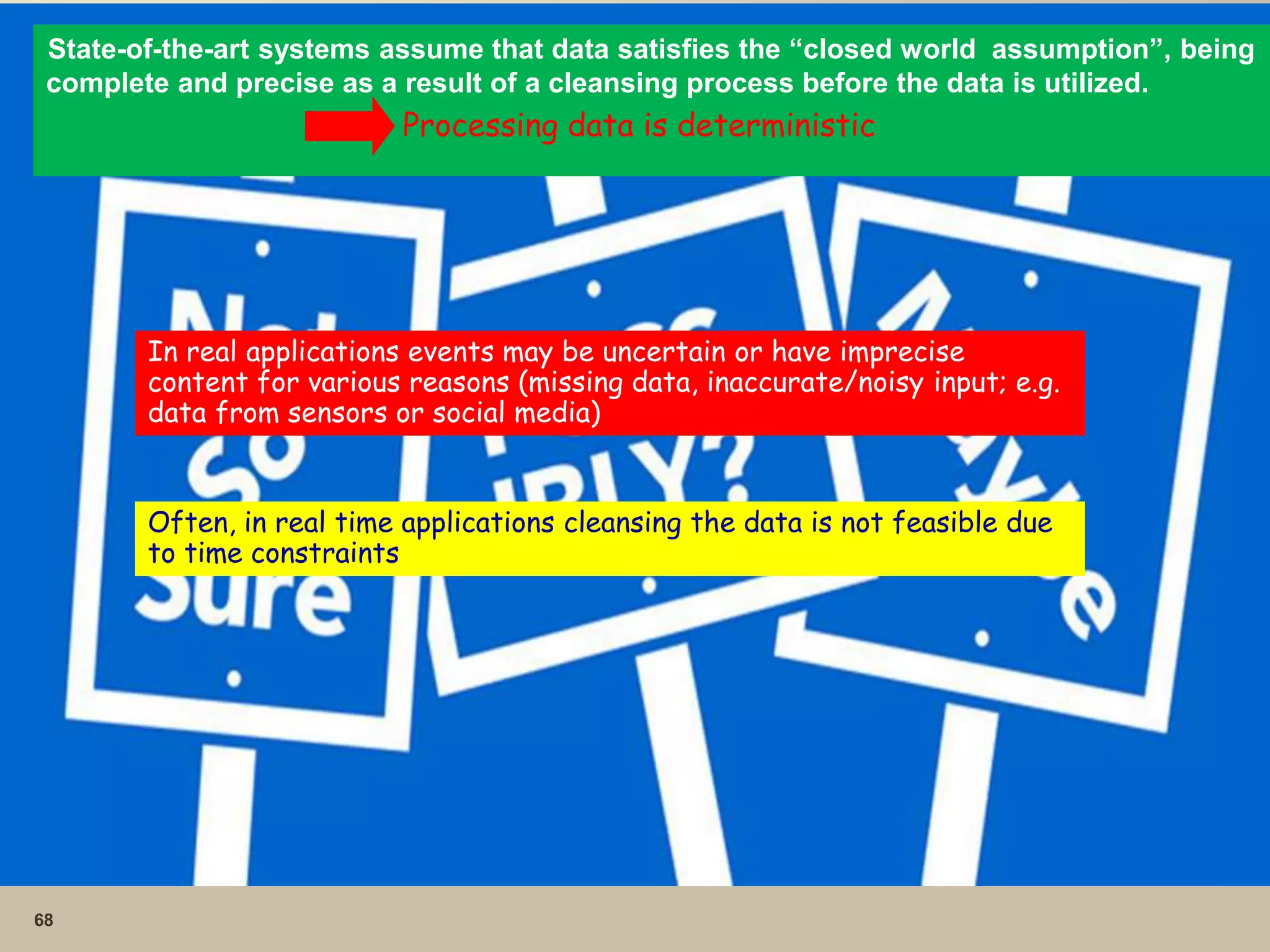
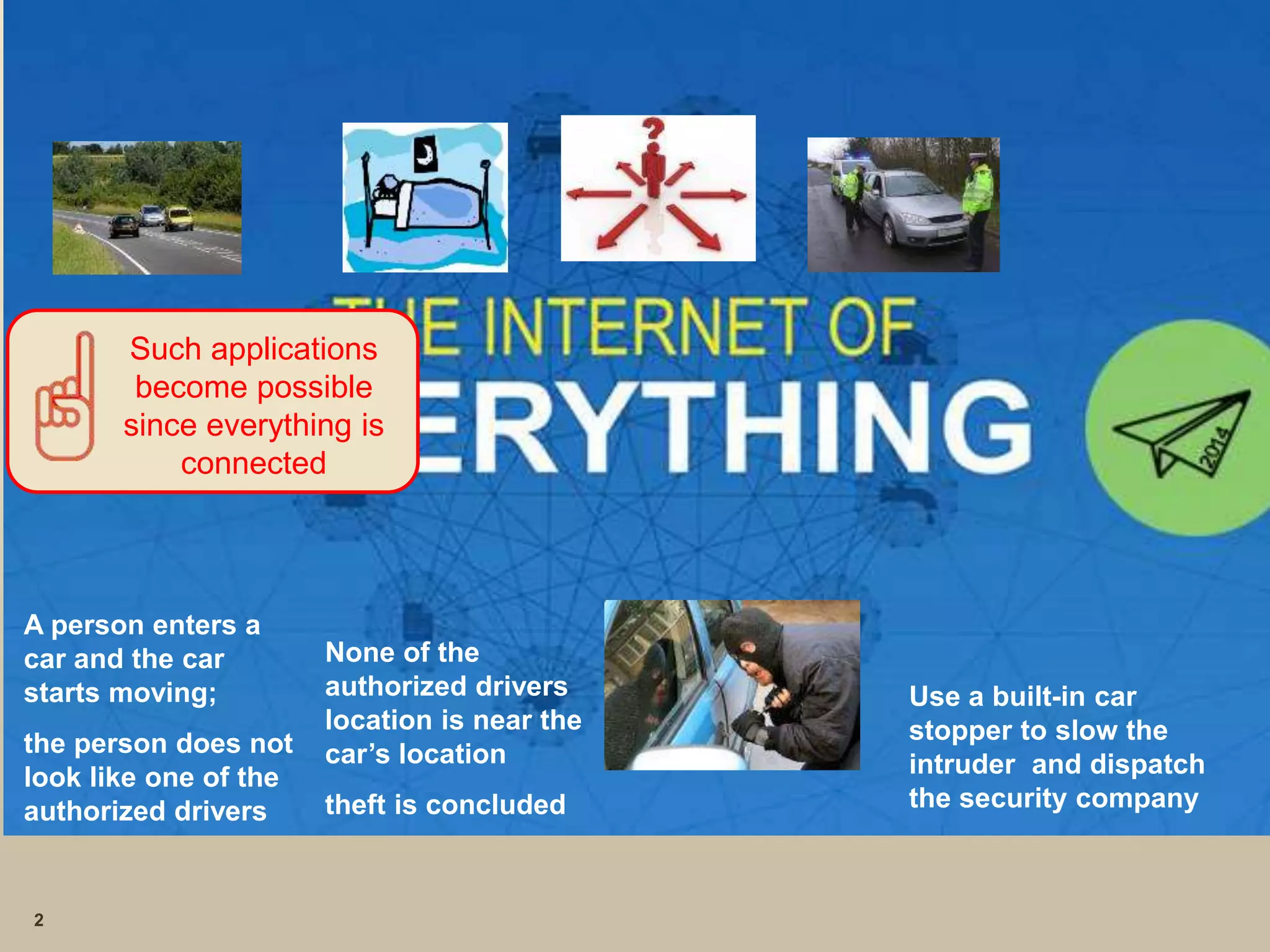
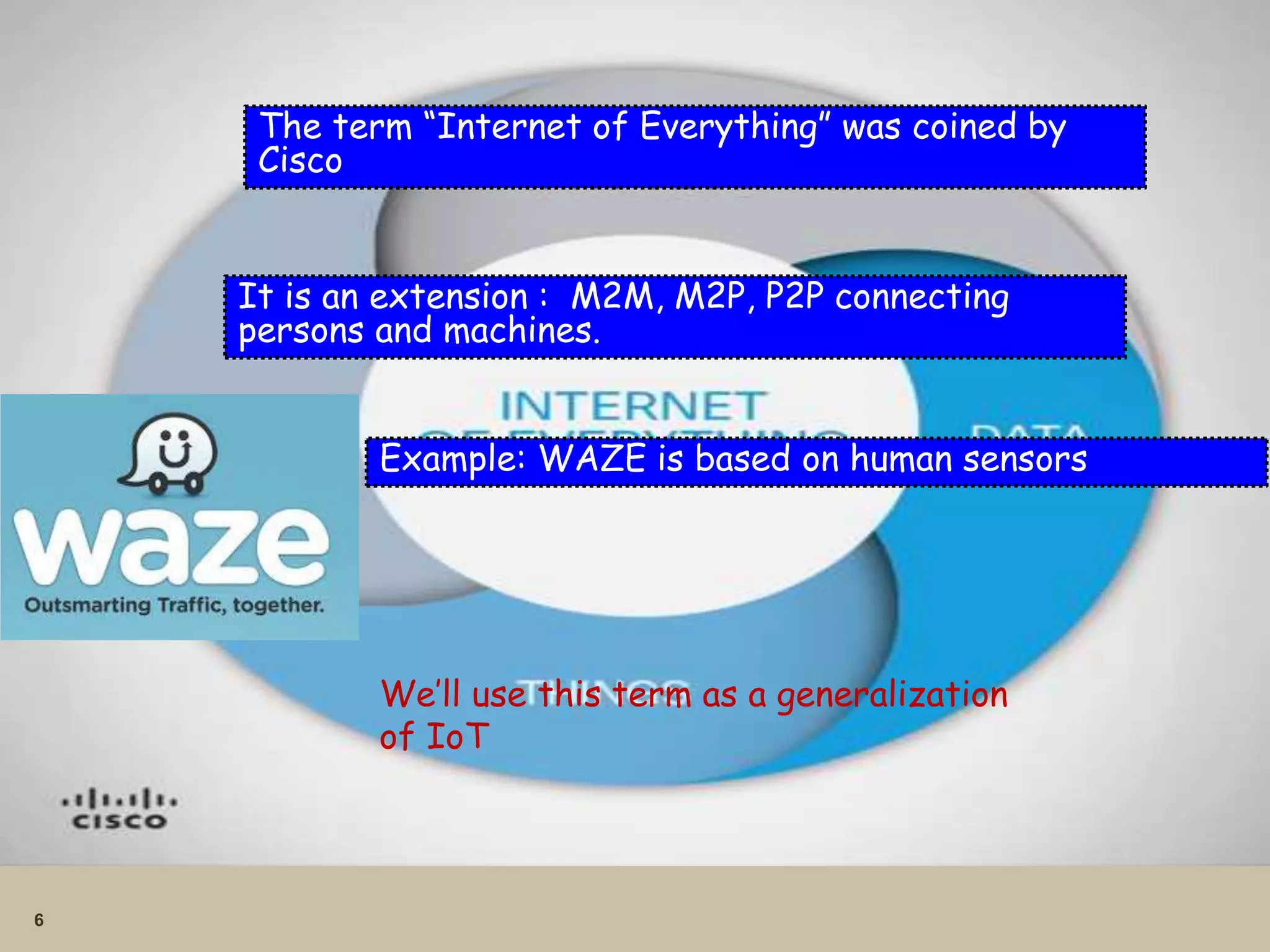
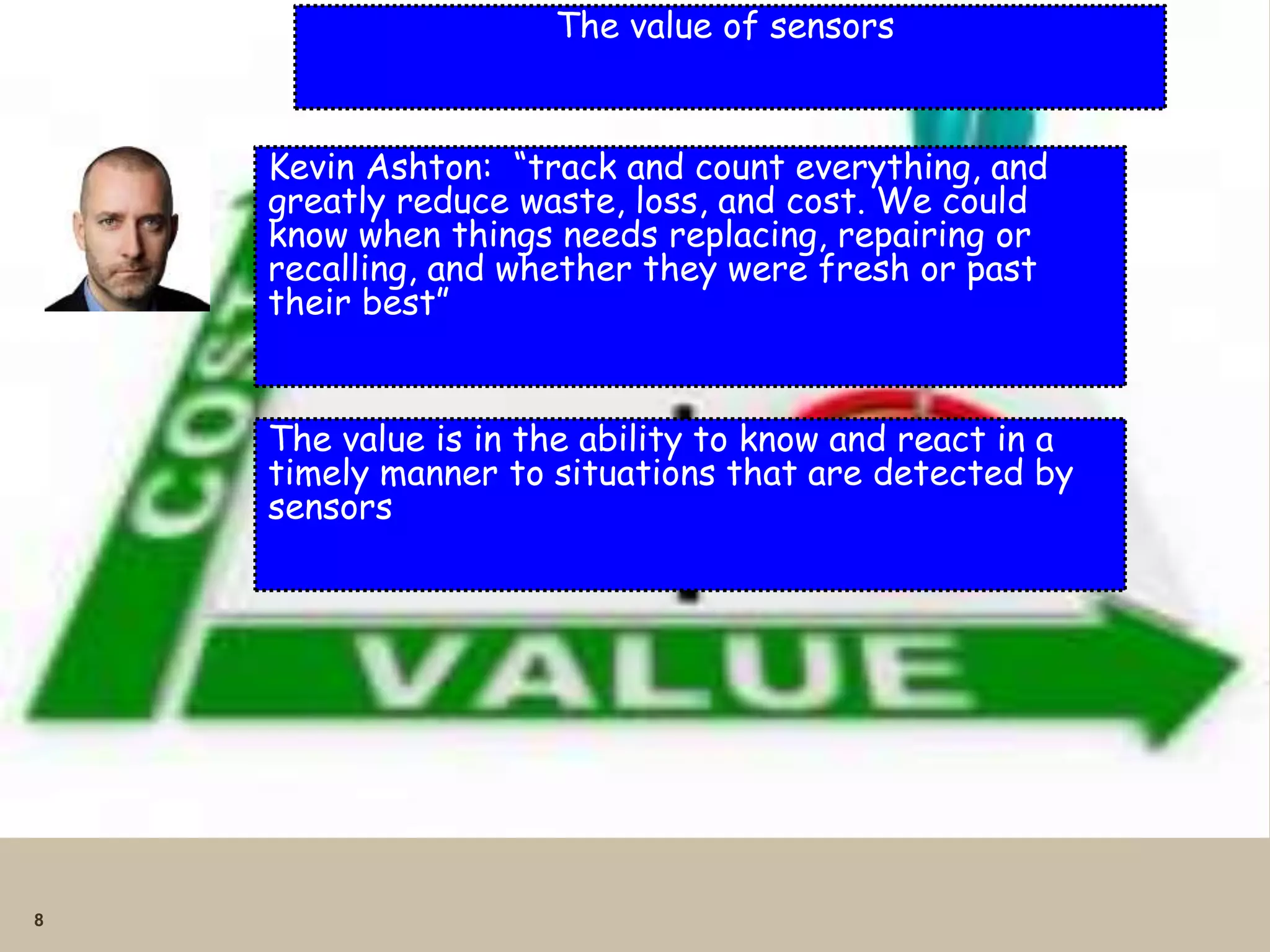
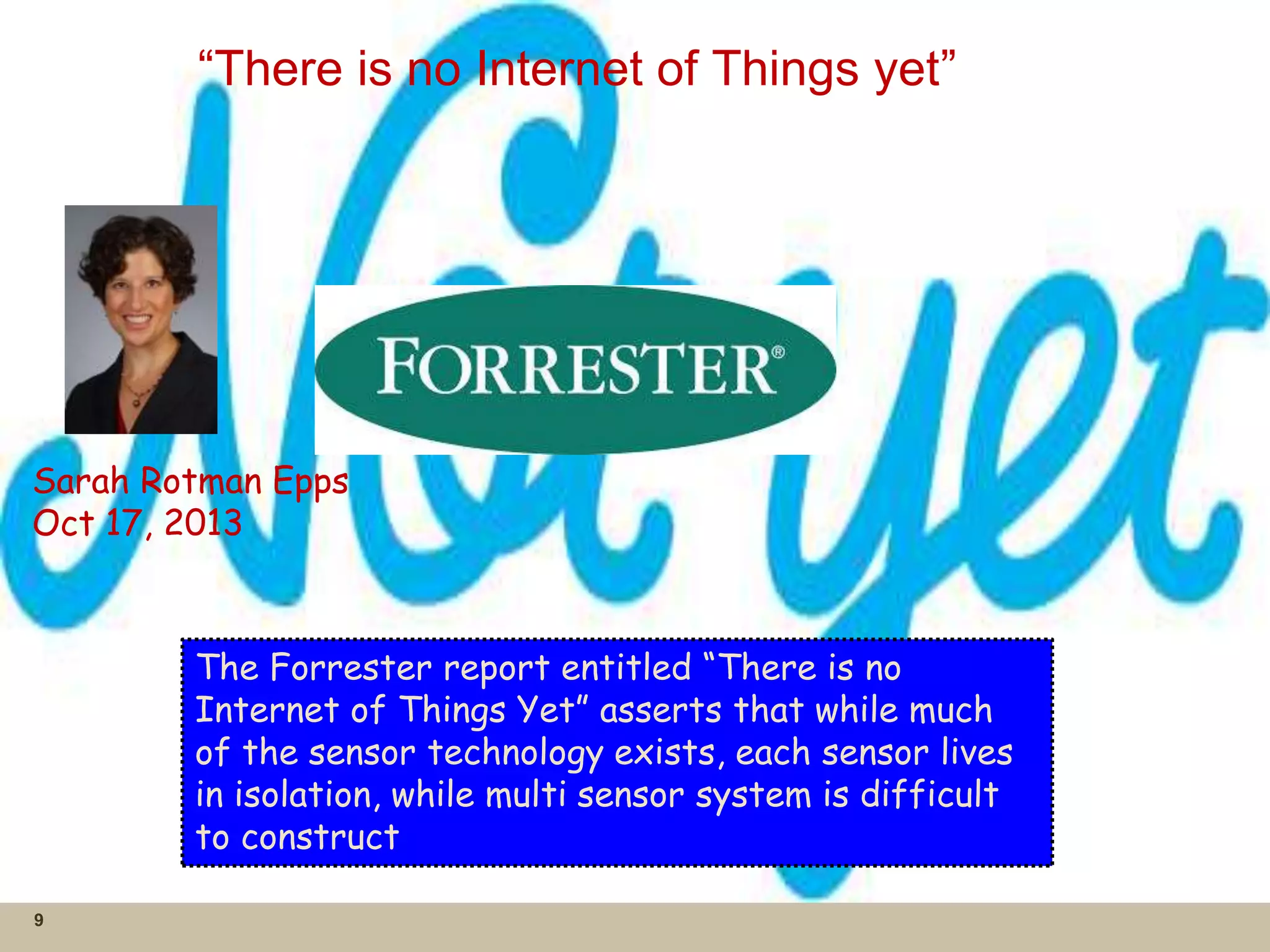
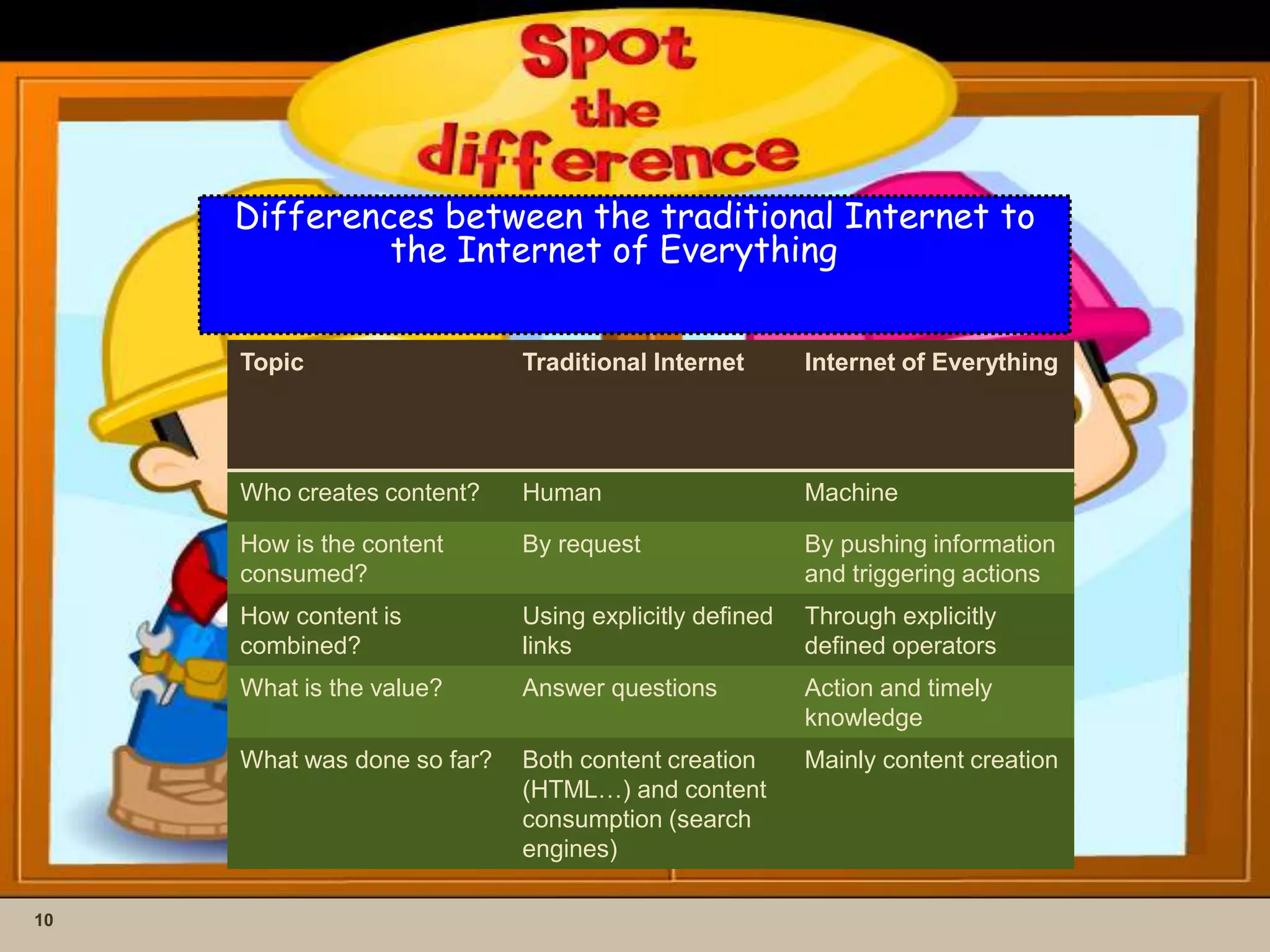
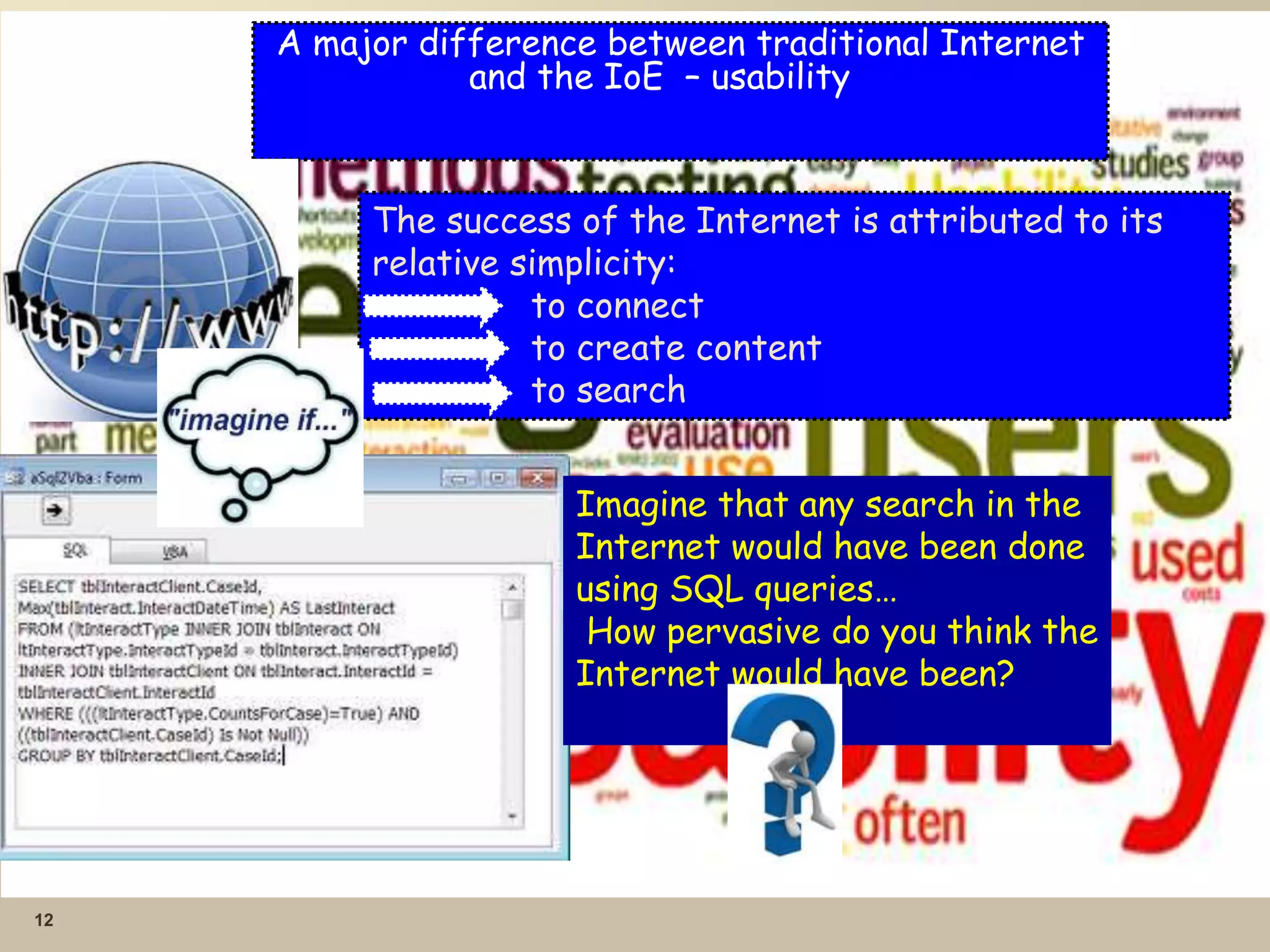
This document provides an overview of the Internet of Everything (IoE) and event processing. It discusses how IoE is an extension of concepts like the Internet of Things (IoT) and how everything will become connected. The document outlines how IoE will impact different areas like healthcare, agriculture, cities, retail, homes and more. It also presents a futuristic view where driverless cars and automated personal assistants become common due to advances in sensors and connectivity.
![For situational awareness….
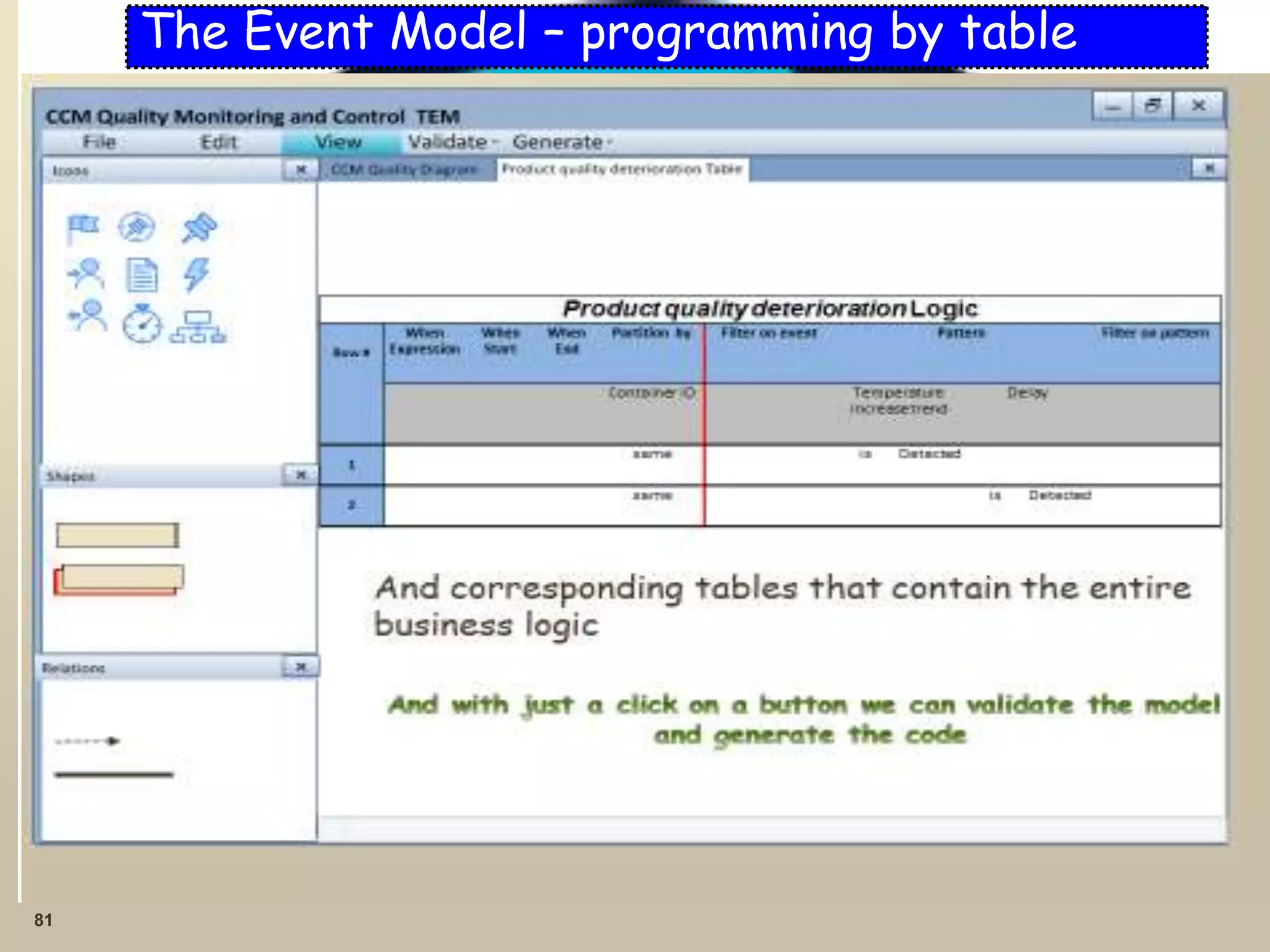
Languages are actually more complex than
SQL
13
// Large cash deposit
insert into LargeCashDeposit
select * from Cash deposit where amount > 100,000
// Frequent (At least three) large cash deposits
create context AccountID partition by accountId on Cash deposit;
Context AccountID
Insert into FrequentLargeCashDeposits select count(*) from LargeCashDeposit
having count(*)>3;
// Frequent cash deposits followed by transfer abroad
Context AccountID
insert into SuspiciousAccount select * from pattern [
every f=FrequentCashDeposit -> t=TransferAbroad where timer.within(10 days)]](https://image.slidesharecdn.com/debs2014tutorial2-140526114708-phpapp01/75/DEBS-2014-tutorial-on-the-Internet-of-Everything-13-2048.jpg)