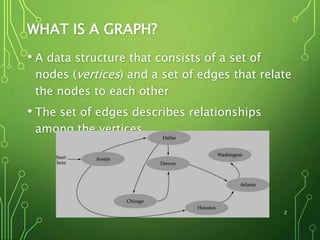
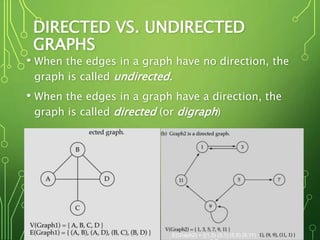
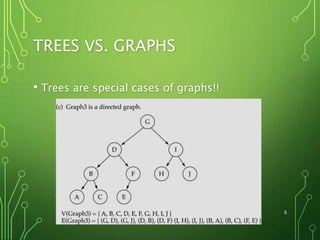
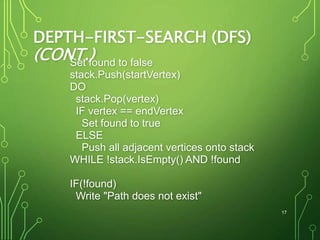
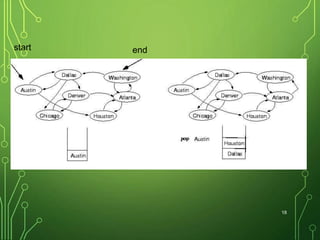
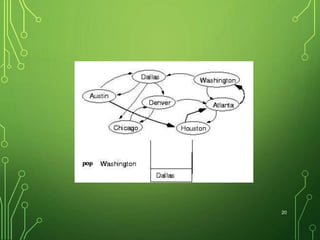
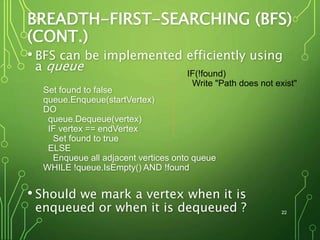
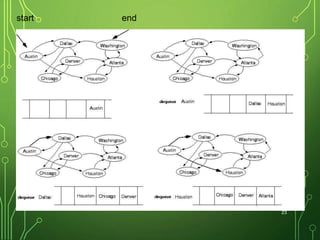
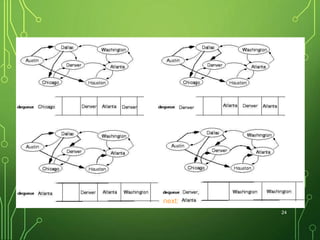
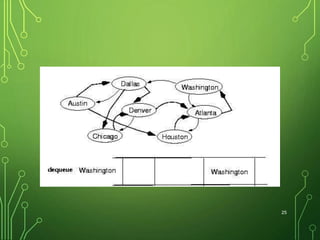
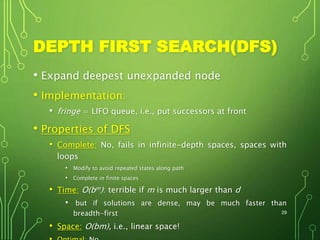
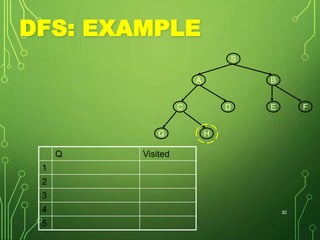
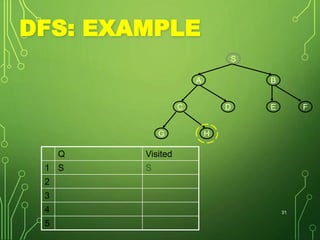
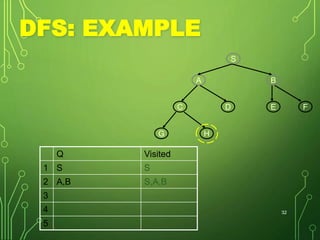
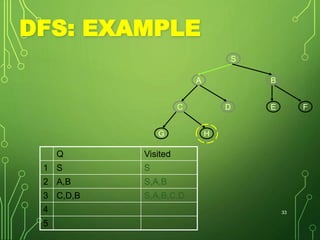
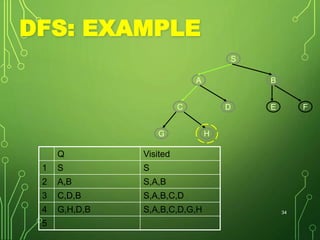
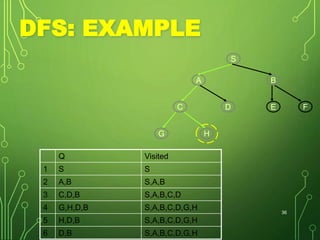
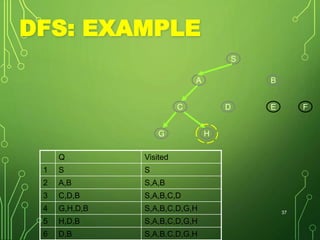
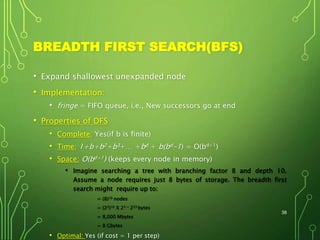
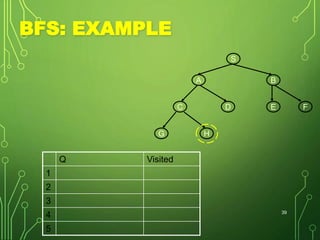
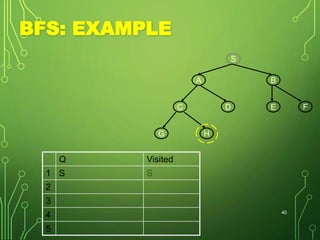
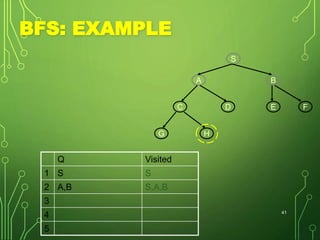
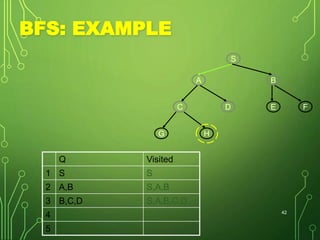
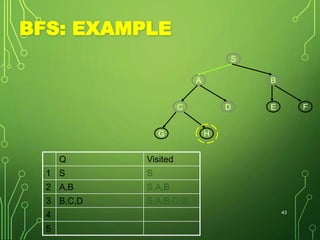
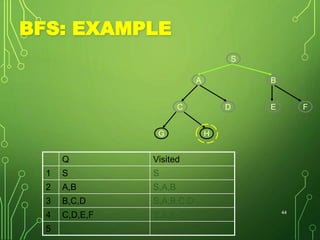
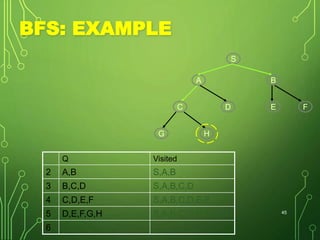
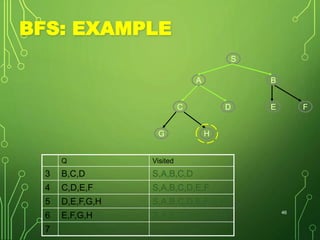
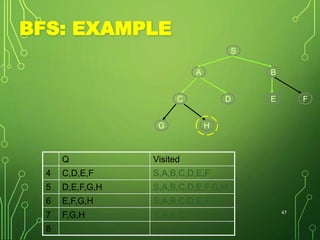
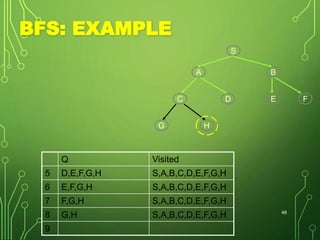
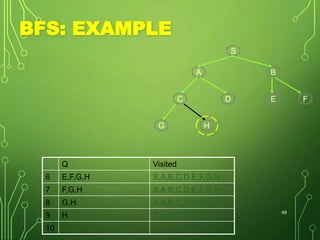
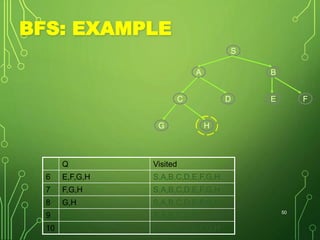
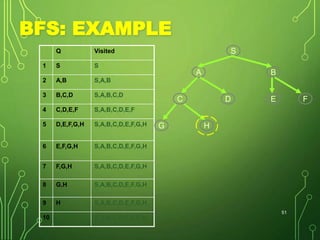
Graphs are data structures consisting of nodes and edges connecting nodes. They can be directed or undirected. Trees are special types of graphs. Common graph algorithms include depth-first search (DFS) and breadth-first search (BFS). DFS prioritizes exploring nodes along each branch as deeply as possible before backtracking, using a stack. BFS explores all nodes at the current depth before moving to the next depth, using a queue.