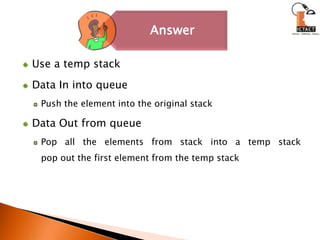
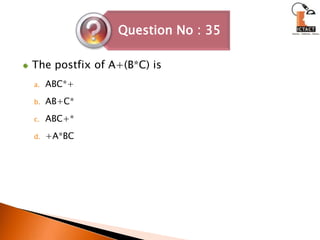
The binary search is faster than the sequential search. The complexity of binary search is O(log n) whereas the complexity of a sequential search is O(n). Stacks are used to evaluate algebraic or arithmetic expressions using prefix or postfix notations. Heap sort involves creating a max heap from the array and then replacing the root with the last element and rebuilding the heap for the remaining elements, repeating this process to sort the entire array.


![heapsort() { n = array(); // Convert the tree into an array.makeheap(n); // Construct the initial heap. for(i=n; i>=2; i--) { swap(s[1],s[i]);heapsize--;keepheap(i); }}makeheap(n) {heapsize=n; for(i=n/2; i>=1; i--)keepheap(i);}keepheap(i) { l = 2*i; r = 2*i + 1; p = s[l]; q = s[r]; t = s[i];](https://image.slidesharecdn.com/ds-111011055724-phpapp01/85/Data-Structure-97-320.jpg)
![if(l<=heapsize && p->value > t->value)largest = l; else largest = i; m = s[largest]; if(r<=heapsize && q->value > m->value) largest = r; if(largest != i) { swap(s[i], s[largest]);keepheap(largest); }}](https://image.slidesharecdn.com/ds-111011055724-phpapp01/85/Data-Structure-98-320.jpg)
![Bubble sort algorithmvoid bubble_sort(int a[], int n){ int i, j, temp; for(j = 1; j < n; j++) { for(i = 0; i < (n - j); i++) { if(a[i] >= a[i + 1]) { //Swap a[i], a[i+1] } } }}](https://image.slidesharecdn.com/ds-111011055724-phpapp01/85/Data-Structure-100-320.jpg)
![To improvise this basic algorithm, keep track of whether a particular pass results in any swap or not. If not, you can break out without wasting more cycles. void bubble_sort(int a[], int n){ int i, j, temp; int flag; for(j = 1; j < n; j++) {flag = 0; for(i = 0; i < (n - j); i++) { if(a[i] >= a[i + 1]) {//Swap a[i], a[i+1] flag = 1;} } if(flag==0)break; }}](https://image.slidesharecdn.com/ds-111011055724-phpapp01/85/Data-Structure-101-320.jpg)
![Selection Sort Algorithmvoid selection_sort(int a[], int n) { int i, j, small, pos, temp; for(i = 0; i < (n - 1); i++) { small = a[i]; pos = i; for(j = i + 1; j < n; j++) { if(a[j] < small) { small = a[j]; pos = j; } } temp = a[pos]; a[pos] = a[i]; a[i] = temp; }}](https://image.slidesharecdn.com/ds-111011055724-phpapp01/85/Data-Structure-102-320.jpg)
![Quick Sort Algorithmint partition(int a[], int low, int high){ int i, j, temp, key; key = a[low]; i = low + 1; j = high; while(1) { while(i < high && key >= a[i])i++; while(key < a[j])j--; if(i < j) { temp = a[i]; a[i] = a[j]; a[j] = temp; } else { temp = a[low]; a[low] = a[j]; a[j] = temp; return(j); } }}](https://image.slidesharecdn.com/ds-111011055724-phpapp01/85/Data-Structure-103-320.jpg)
![void quicksort(int a[], int low, int high) { int j; if(low < high) { j = partition(a, low, high);quicksort(a, low, j - 1);quicksort(a, j + 1, high); }}int main() { // Populate the array aquicksort(a, 0, n - 1);}](https://image.slidesharecdn.com/ds-111011055724-phpapp01/85/Data-Structure-104-320.jpg)
![Insertion Sort Algorithmvoid insertion_sort(int a[], int n){ int i, j, item; for(i = 0; i < n; i++) { item = a[i]; j = i - 1; while(j >=0 && item < a[j]) { a[j + 1] = a[j]; j--; } a[j + 1] = item; }}](https://image.slidesharecdn.com/ds-111011055724-phpapp01/85/Data-Structure-105-320.jpg)