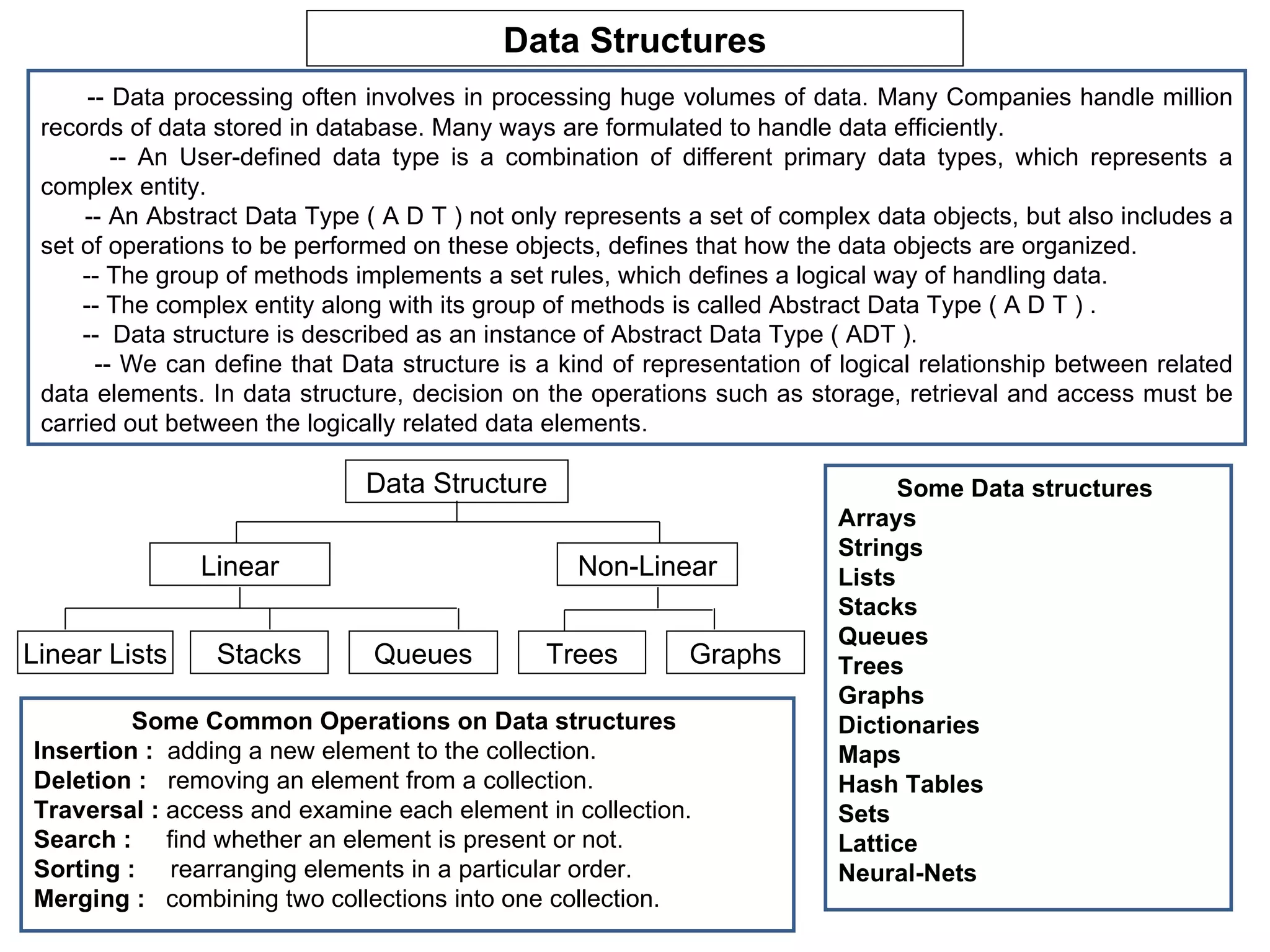
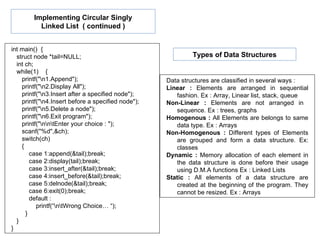
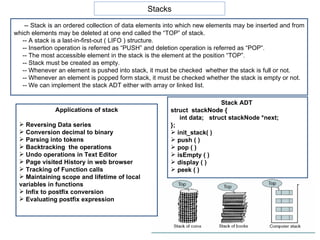
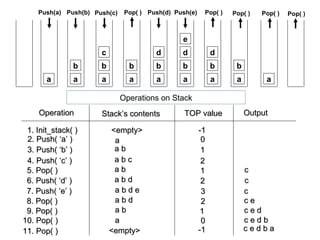
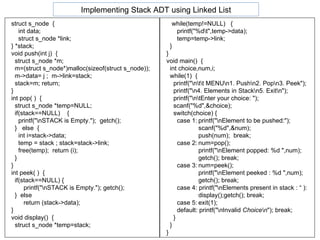
- Data structures allow for efficient handling of large volumes of data through logical organization and relationships between data elements. Common linear data structures include arrays, lists, stacks, and queues, while trees and graphs are examples of non-linear data structures.
- Abstract data types (ADTs) define a set of complex data objects and operations that can be performed on those objects without specifying their implementation. Data structures provide a way to implement the logical relationships and operations defined in an ADT.
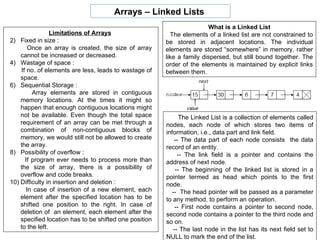
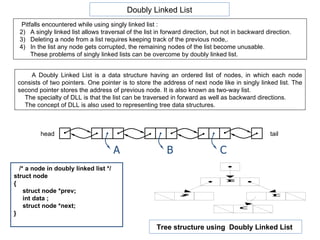
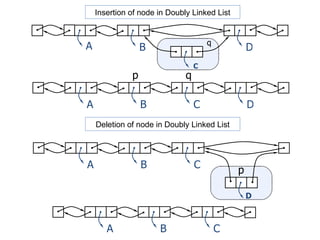
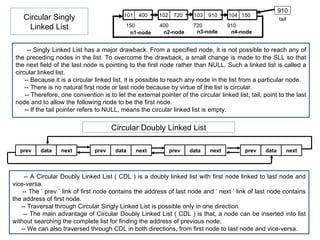
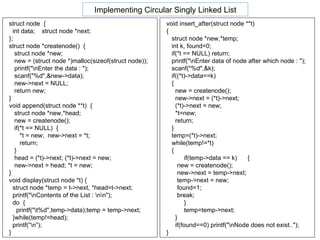
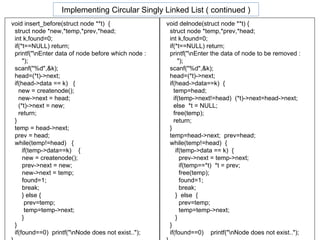
- Linked lists provide an alternative to arrays for storing data by linking each data element to the next using pointers, rather than requiring contiguous memory locations. This allows for more flexible insertion and deletion compared to arrays.
![#define SIZE 50 int stack[SIZE]; int top; void init_stack() { top=-1; } void push( int n ) { if( top==SIZE-1) printf("\nStack is full"); else stack[++top]= n; } int pop( ) { if(top== -1) { printf("\nStack is empty"); return -1; } else return stack[top--]; } void display( ) { int i; if(top== -1) printf("\nStack is empty."); else { printf("\nElements are : \n"); for(i=0;i<=top;i++) printf("%5d ",stack[i]); } } int isEmpty( ) { if ( top== -1 ) return 1; else return 0; } int peek( ){ return stack[top]; } int main() { int choice,item; init_stack(); do { printf("\n\t\t\tMenu\n\t1.Push.\n\t2.Pop."); printf("\n\t3.Peek.\n\t4.Display.\n\t5.Exit.\n"); printf("\nYour Choice: "); scanf("%d",&choice); switch(choice) { case 1:printf("\nEnter the element to push : "); scanf("%d",&item); push(item); break; case 2:item = pop(); printf("\nElement poped : %d",item); printf("\nPress a key to continue..."); getche(); break; case 3:item = peek(); printf("\nElement at top : %d",item); printf("\nPress a key to continue..."); getche(); break; case 4:display(); printf("\nPress a key to continue..."); getche(); break; case 5:exit(0); } }while(1); } Implementing Stack ADT using Array](https://image.slidesharecdn.com/unit7-111030013945-phpapp01/85/Unit7-C-19-320.jpg)
![int queue[10] ,front, rear ; void init_queue() { front = rear = -1 ; } void addq ( int item ){ if ( rear == 9 ) { printf("\nQueue is full"); return ; } rear++ ; queue [ rear ] = item ; if ( front == -1 )front = 0 ; } int delq( ){ int data ; if ( front == -1 ) { printf("\nQueue is Empty"); return 0; } data = queue[front] ; queue[front] = 0 ; if ( front == rear ) front = rear = -1 ; else front++ ; return data ; } void display() { int i; if(front==-1) printf("\nQueue is empty."); else { printf("\nElements are : \n"); for (i=front;i<=rear;i++) printf("%5d",queue[i]); } } int main() { int ch,num; init_queue(); do { printf("\n\tMENU\n\n1. Add to Queue”); printf(“\n2. Delete form Queue"); printf("\n3. Display Queue\n4. Exit."); printf("\n\n\tYour Choice: "); scanf("%d",&ch); switch(ch) { case 1: printf("\nEnter an element : "); scanf("%d",&num); addq(num);break; case 2: num=delq(); printf("\nElement deleted : %d",num); break; case 3: display(); break; case 4: exit(0); default: printf("\nInvalid option.."); } }while(1); } Implementing Queue ADT using Array](https://image.slidesharecdn.com/unit7-111030013945-phpapp01/85/Unit7-C-22-320.jpg)
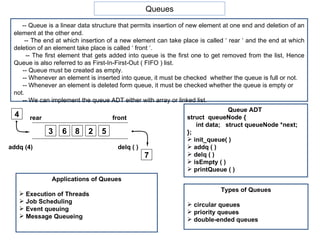
![#define STACKSIZE 20 typedef struct { int top; char items[STACKSIZE]; }STACK; /*pushes ps into stack*/ void push(STACK *sptr, char ps) { if(sptr->top == STACKSIZE-1) { printf("Stack is full\n"); exit(1); } else sptr->items[++sptr->top]= ps; } char pop(STACK *sptr) { if(sptr->top == -1) { printf("Stack is empty\n"); exit(1); } else return sptr->items[sptr->top--]; } int main() { int i; STACK s; char x, y, E[20] ; s.top = -1; /* Initialize the stack is */ printf("Enter the Infix Expression:"); scanf("%s",E); for(i=0;E[i] != '\0';i++) { x= E[i]; /* Consider all lowercase letter from a to z are operands */ if(x<='z' && x>='a') printf("%c",x); else if(x == '(') push(&s ,x); else if( x == ')‘ ){ y=pop(&s) ; while(y != '(') { printf("%c",y); y=pop(&s) ; } } else { if(s.top ==-1 || s.items[s.top] == '(') push(&s ,x); else { /* y is the top operator in the stack*/ y = s.items[s.top]; /* precedence of y is higher/equal to x*/ if( y=='*' || y=='/'){ printf("%c", pop(&s)); push(&s ,x); } else if ( y=='+' || y=='-') /* precedence of y is equal to x*/ if( x=='+' || x=='-') { printf("%c", pop(&s)); push(&s ,x); } /* precedence of y is less than x*/ else push(&s ,x); } } } while(s.top != -1) printf("%c",pop(&s)); } In-Fix To Post-Fix convertion](https://image.slidesharecdn.com/unit7-111030013945-phpapp01/85/Unit7-C-25-320.jpg)
![#include<stdio.h> #include<ctype.h> #include<math.h> float stack[10]; int top=-1; void push(char c) { stack[++top]=c; } float pop() { float n; n=stack[top--]; return (n); } float evaluate(char expr[], float data[]) { int j=0; float op1=0,op2=0; char ch; while(expr[j]!='\0') { ch = expr[j]; if(isalpha(expr[j])) { push(data[j]); } else { op2=pop(); op1=pop(); switch(ch) { case '+':push(op1+op2);break; case '-':push(op1-op2);break; case '*':push(op1*op2);break; case '/':push(op1/op2);break; case '^':push(pow(op1,op2)); break; } } j++; } return pop(); } int main() { int j=0; char expr[20]; float number[20],result; printf("\nEnter a post fix expression : "); gets(expr); while(expr[j]!='\0') { if(isalpha(expr[j])) { fflush(stdin); printf("\nEnter number for %c : ",expr[j]); scanf("%f",&number[j]); } j++; } result = evaluate(expr,number); printf("\nThe result of %s is %f",expr,result); } Evaluation of Post-Fix Expression](https://image.slidesharecdn.com/unit7-111030013945-phpapp01/85/Unit7-C-26-320.jpg)