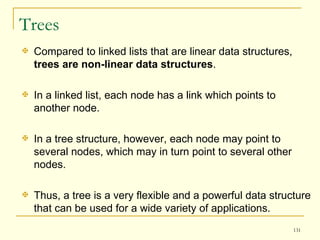
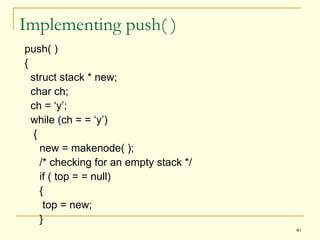
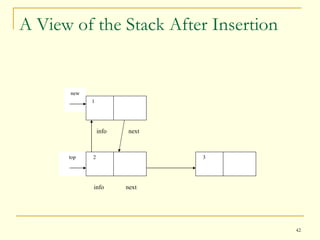
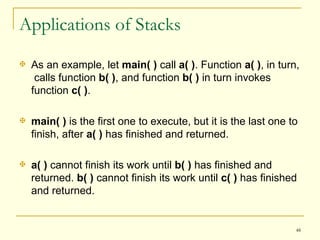
This document provides an overview of data structures and algorithms. It introduces common linear data structures like stacks, queues, and linked lists. It discusses the need for abstract data types and different data types. It also covers implementing stacks as a linked list and common stack operations. Key applications of stacks include function call stacks which use a LIFO structure to remember the order of function calls and returns.







![Array Usage – A Perspective Consider the following example: #include<stdio.h> main( ) { int num_array[50],i; for( i=0; i < 50; i++ ) { num_array[i]=0; scanf( "%d",&num_array[i] ); fflush(stdin); } }](https://image.slidesharecdn.com/datastructures-110225222818-phpapp01/85/Data-structures-9-320.jpg)


![Dynamic Data Structures A structure in C is a collection of items, each of which has its own identifier. Each item is called a member of the structure. To access the members of a structure, we need to create objects or instances of the structure. A structure is declared as: struct <structure name> ex: struct employee { { char name[50]; members; char designation[25]; }object; float salary; } emp;](https://image.slidesharecdn.com/datastructures-110225222818-phpapp01/85/Data-structures-13-320.jpg)

![The malloc( ) Function Consider the following example: #include<stdio.h> main() { struct marks_data { char name[11]; int marks; }; struct marks_data *ptr; /* declaration of a stack variable */ ptr = (struct marks_data *)malloc(sizeof(struct marks_data)); /* declaration of a block of memory on the heap and the block in turn being referenced by ptr */ }](https://image.slidesharecdn.com/datastructures-110225222818-phpapp01/85/Data-structures-17-320.jpg)














































![Circular Queue In circular queue, the elements of a given queue can be stored efficiently in an array so as to “wrap around” in such a way that the rear of the queue is followed by the front of the queue. Allows the entire array to store the elements without shifting any data within the queue. Assume that circular queue contains only one item as shown in the next slide [fig (a)]. In this case, the rear end identified by r is 0 and the front end identified by f is also 0. Since only r is incremented upon item insertion, its initial value has to be -1 and f should be 0.](https://image.slidesharecdn.com/datastructures-110225222818-phpapp01/85/Data-structures-75-320.jpg)

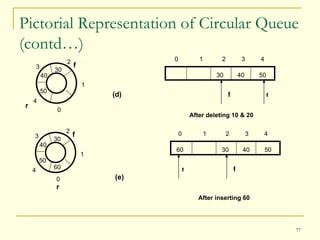

![In case of items being deleted, as in an ordinary queue, the front end identifier f is updated accordingly [fig (d)] and is made to point to the next front item in the queue. The statement used to increment f is: f = (f+1)%QUEUE_SIZE; In case of this kind of queue, to check for overflow or underflow, a variable is used that contains the number of items in the queue at any time. When an item is inserted or deleted, the variable is incremented or decremented by 1 respectively. Pictorial Representation of Circular Queue (contd…) >>Program](https://image.slidesharecdn.com/datastructures-110225222818-phpapp01/85/Data-structures-79-320.jpg)