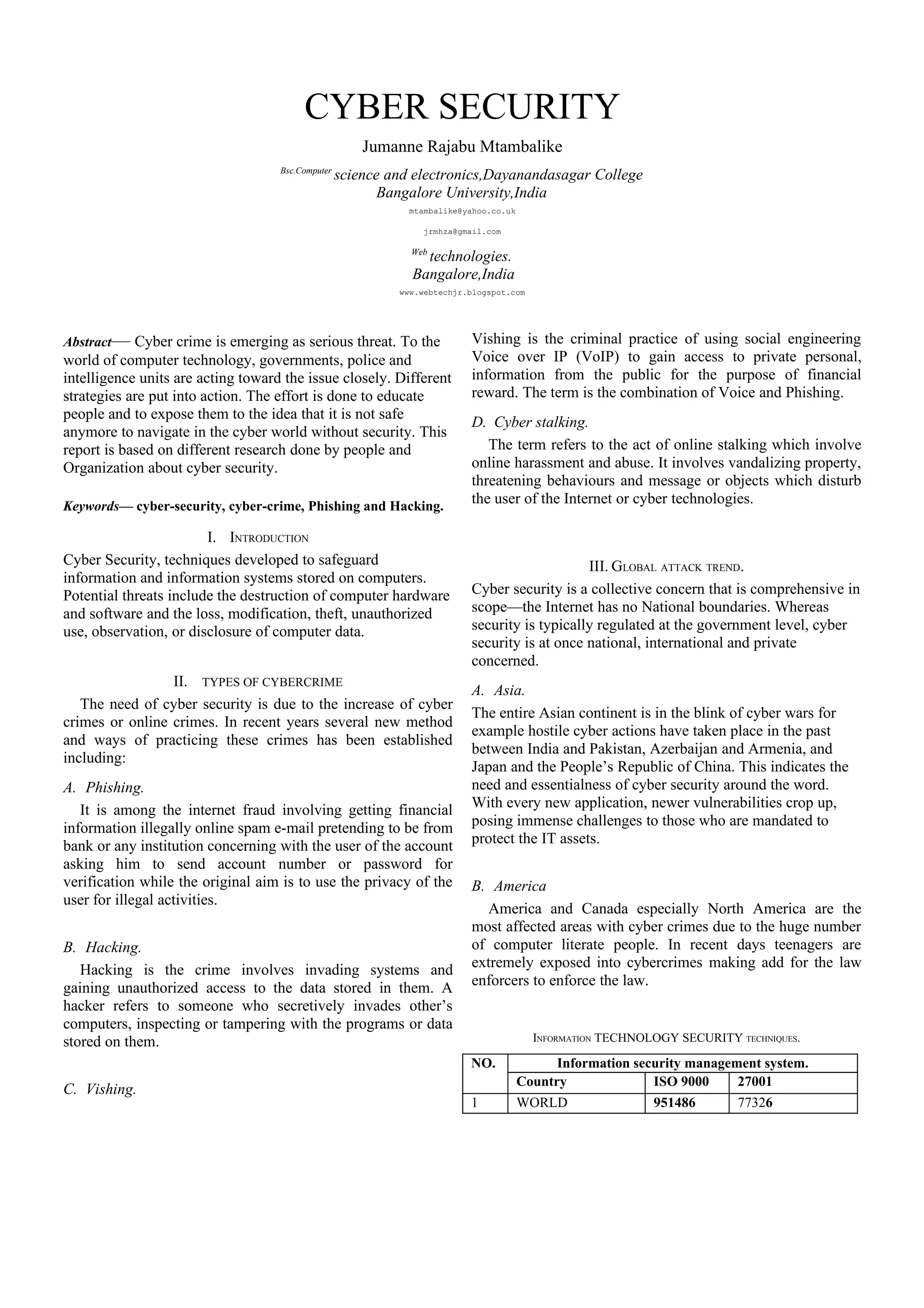
This document discusses cyber security and cyber crimes. It begins by defining cyber security and the need for it due to increasing cyber crimes like phishing, hacking, vishing and cyber stalking. It then examines global attack trends in different regions like Asia, America, Europe, Africa and Australia. It discusses information technology security techniques used and terminologies like malicious codes and scam. It explores overcoming cyber crimes through security policies, law enforcement, research and international collaboration. Finally, it concludes that cyber security is about managing future risks and incidents through a standardized model and coordinated international efforts.


![REFERENCES
[1] Microsoft student Encarta 2009 edition
[2] www.verisign.com
[3] Dr.B.Muthukumaran “CYBER CRIME SCENARIO IN INDIA”
[4] www.wikipedia.com/cybersecurity.
[5] www.itu.com
[6] www.google.com.](https://image.slidesharecdn.com/cybersecurity-1285085396396-phpapp02/85/Cybersecurity-4-320.jpg)