Embed presentation
Downloaded 104 times



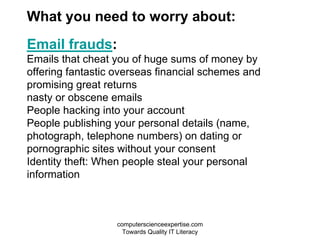
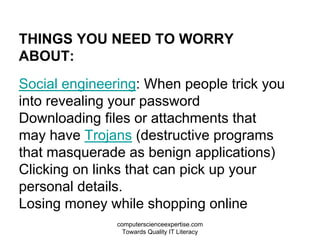
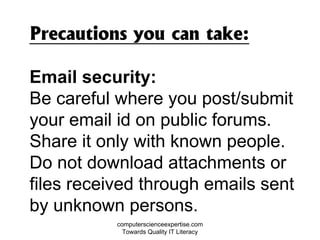
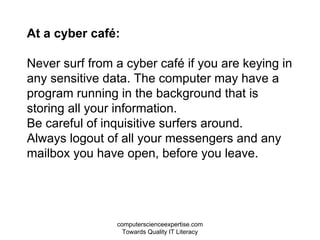

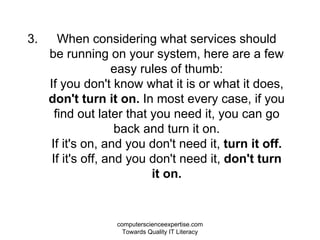
This document discusses various computing ethics and security best practices. It recommends regularly updating software, using antivirus software, strong and unique passwords, and caution when downloading files or entering personal information online. It warns about phishing scams, social engineering tricks, and protecting information in public places like internet cafes. The overall message is that practicing basic online safety and being wary of potential threats can help avoid most cyber dangers.