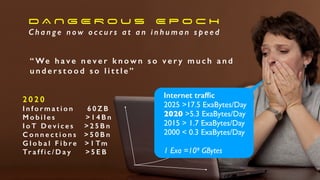
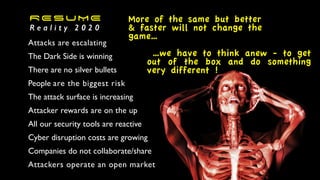
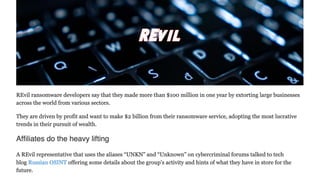
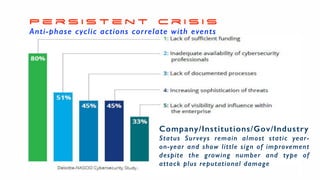
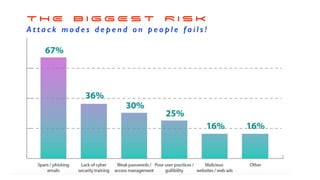
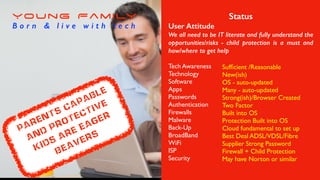
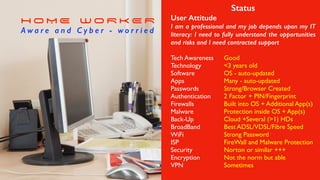
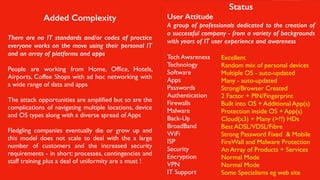
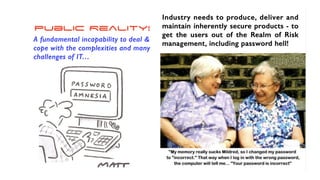
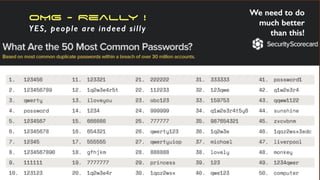
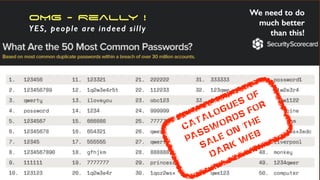
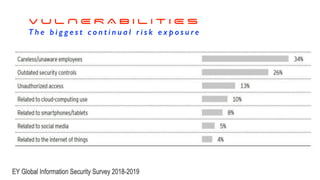
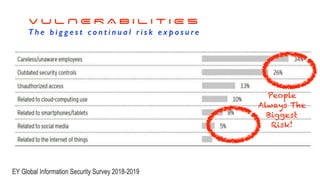
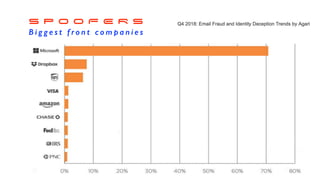
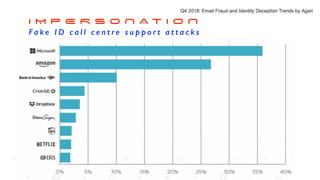
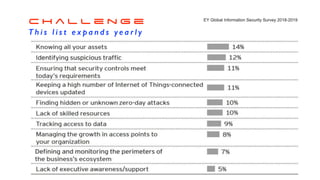
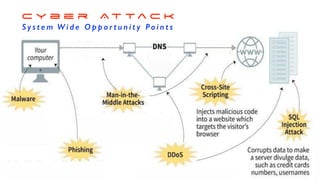
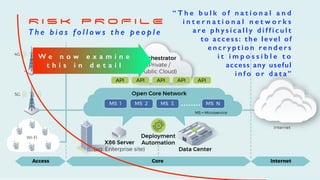
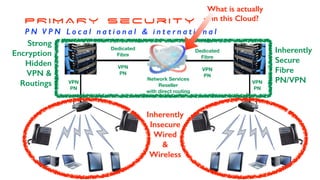
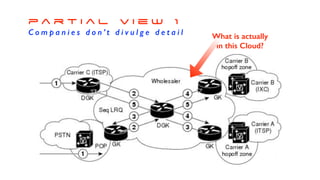
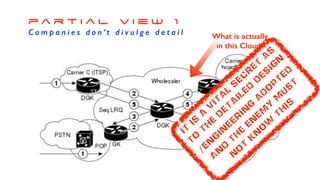
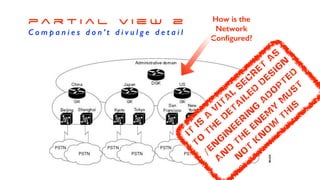
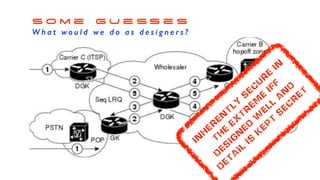
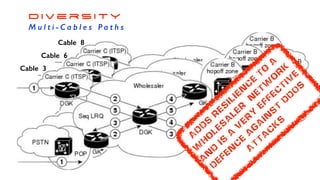
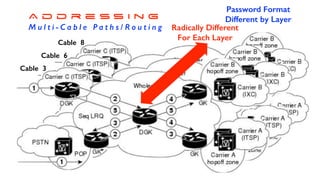
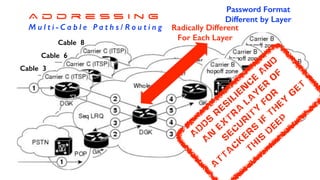
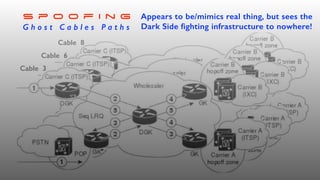
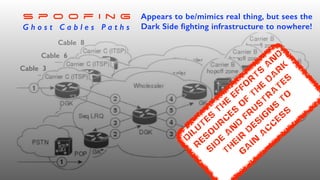
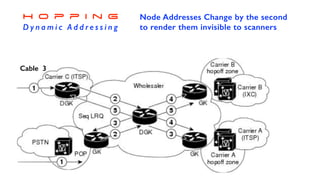
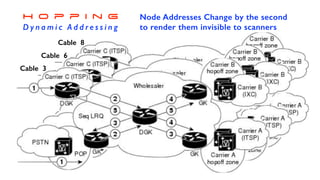
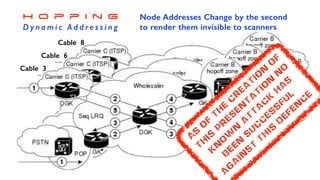
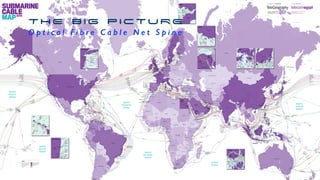
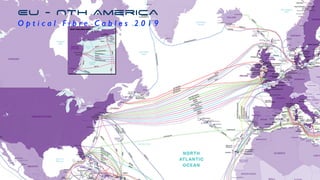
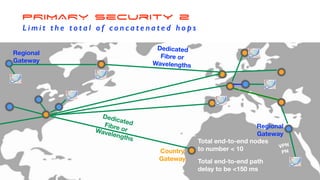
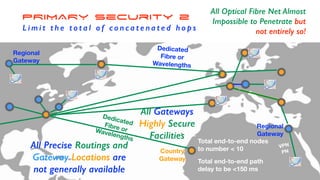
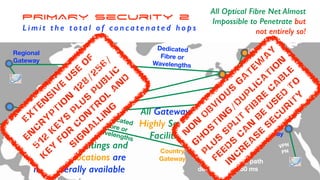
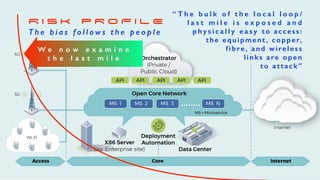
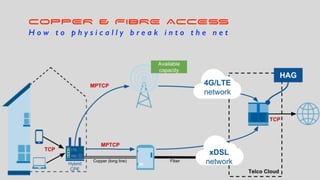
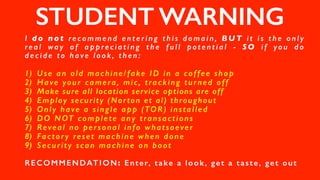
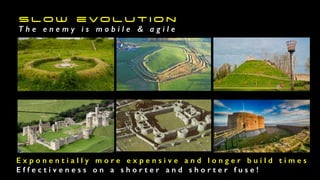
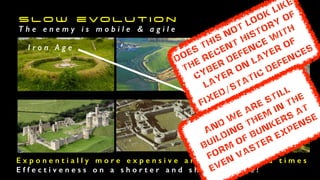
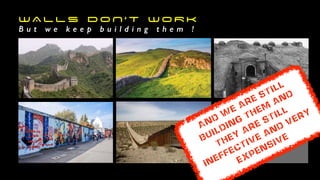
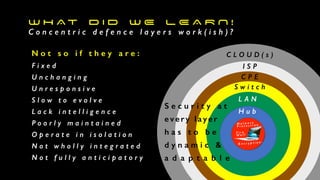
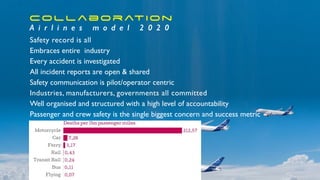
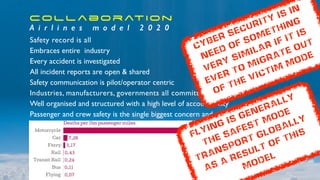
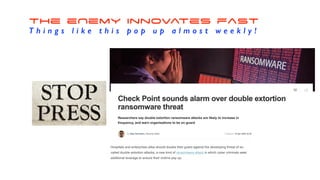
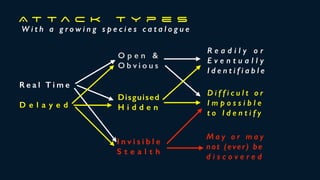
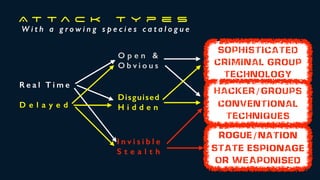
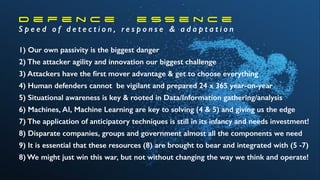
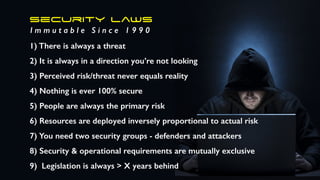
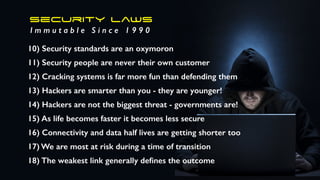
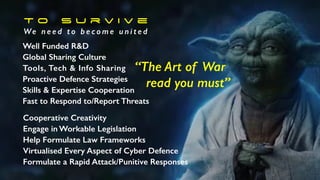
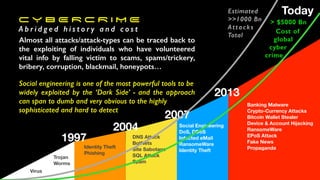
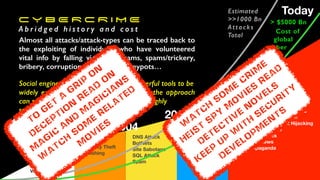
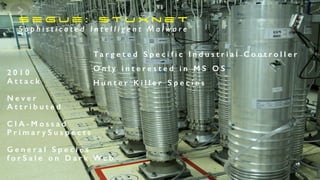
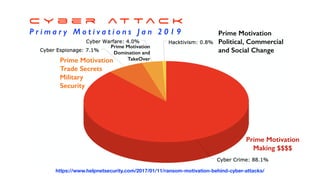
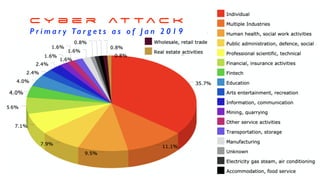
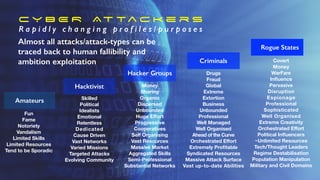
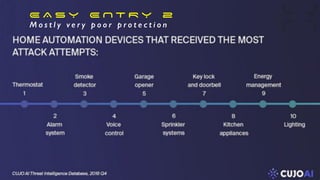
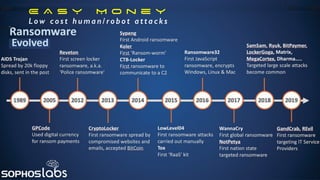
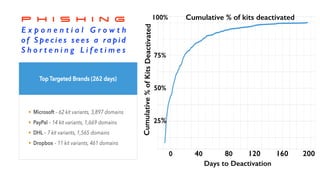
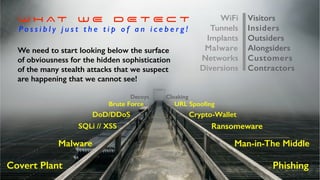
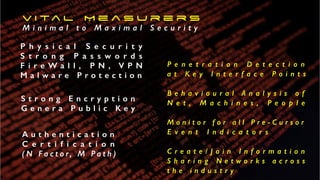
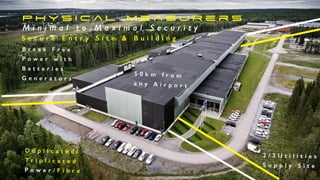
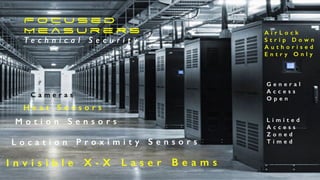
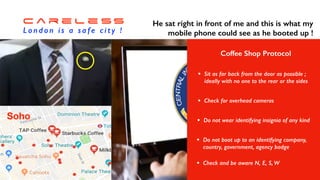
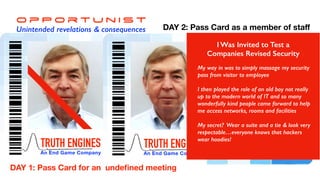
The document discusses the escalating risks of cyber attacks in a fully mobile world, emphasizing that humans are the biggest risk factor. It highlights the rapid increase in technology users and the inadequate protective measures currently in place, calling for innovative thinking in cybersecurity. The overall message underscores the need for improved awareness and hardening of security practices against a growing threat landscape.