Cybercrime act of Pakistan 2015 Report
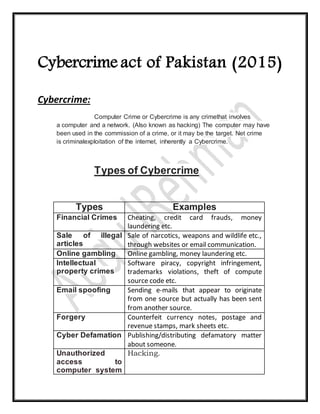
- 1. Cybercrime act of Pakistan (2015) Cybercrime: Computer Crime or Cybercrime is any crimethat involves a computer and a network. (Also known as hacking) The computer may have been used in the commission of a crime, or it may be the target. Net crime is criminalexploitation of the internet, inherently a Cybercrime. Types of Cybercrime Types Examples Financial Crimes Cheating, credit card frauds, money laundering etc. Sale of illegal articles Sale of narcotics, weapons and wildlife etc., through websites or email communication. Online gambling Online gambling, money laundering etc. Intellectual property crimes Software piracy, copyright infringement, trademarks violations, theft of compute source code etc. Email spoofing Sending e-mails that appear to originate from one source but actually has been sent from another source. Forgery Counterfeit currency notes, postage and revenue stamps, mark sheets etc. Cyber Defamation Publishing/distributing defamatory matter about someone. Unauthorized access to computer system Hacking.
- 2. or networks Theft of information in electronic form Stealing information on computer hard disks, removable storage media etc. Email bombing Sending a large number of emails crashing email accounts or servers. Data diddling Altering data. Salami attacks Commissioning financial crimes. Denial of service attack Flooding systems by sendingexcessivedemands etc. Virus attacks Spread of viruses and worms. Logic bombs Triggering programs at events. Trojan attacks Unauthorized programs. Internet time theft Stealing internet hours. Web jacking Stealing control over websites. Theftor damaging of computer system Theft of a computer, peripherals etc. Unauthorized access The Cybercrime of “gaining entry into, instructing or communicating with the logical, arithmetical, or memory function resources of a computer, computer system or computer network”11 known as access has the greatest impact Packet sniffing, tempest attack,password cracking and buffer overflow etc. are some techniques for gaining access. Offences and Punishments Illegal access to information system: 1. Cause an information system to perform any function with intent to secure access to the whole or any part of any information system or to enable any such access to be secured ;
- 3. 2. At the time, when he causes the information system to perform the function he knows that the access he intends to secure or to be enable to be secured is unauthorized under this section. Fine Punishment Both 6 Months 100,000PKR Yes Illegal access to program or data: (a) Whoever intentionally, whether temporarily or not, 1. Causes to any program or data to be secured or to be enabled. 2. The access to the program or data he intends to secure, or to enable to be secured, is unauthorized under this section. 3. At the time, when he accesses the program or data he knows that the access he intends to secure, or to enable to be secured, is unauthorized under this section. Fine Punishment Both 200,000PKR 9 Months Yes (b) Whoever recklessly, whether temporarily or not, 1. Causes to any program or data to be secured or to be enabled. 2. The access to the program or data he intends to secure, or to enable to be secured, is unauthorized under this section. 3. At the time, when he accesses the program or data he knows that the access he intends to secure, or to enable to be secured, is unauthorized under this section. Fine Punishment Both 100,000PKR 6 Months Yes Illegal Interface with Program or Data: (a)Whoever intentionally, whether temporarily or not, does any unauthorized act in relation to an information system, or at
- 4. the time when he does the act he knows that it is unauthorized, and acts with intent; 1. To destroy, damage, delete, erase, generate, modify or alter any program or data; 2. To render any program or data inaccessible, meaningless, useless or ineffective; 3. To obstruct, interface or interrupt with any program or data or any aspect or attribute related to the program or data; 4. To obstruct, interface or interrupt with any person in the use of any program or data or any aspect or attribute related to the program or data; 5. To deny, prevent, suppress or hinder access to any program or data to any person entitled to it; 6. To impair the operation of any program or any aspect or attribute related to the program or data; Fine Punishment Both 500,000PKR 3 Years Yes (a) Whoever recklessly, whether temporarily or not, does any unauthorized act in relation to an information system, or at the time when he does the act he knows that it is unauthorized, and acts with intent; 1. Causing destruction, damage, deletion, eraser, generation modification or alteration of any program or data or any aspect or attribute related to the program or data; 2. Rendering any program or data meaningless, useless or ineffective; 3. Causing impairment to the operation of any program; 4. Causing impairment to the reliability of any program or data or any aspect or attribute related to the program or data;
- 5. 5. Causing denial, suppression or hindrance of access to any program or data or any aspect or attribute related to the program or data; Fine Punishment Both 250,000PKR 2 Years Yes Illegal Interface with Information System: (a) Whoever intentionally, whether temporarily or not, does any unauthorized access in relation to an information system, at the time when he does the act he knows that is unauthorized, and acts with intent to severely; 1. Interfere, hinder, damage, prevent, suppress, impair or obstruct the functioning of an information system; 2. Interfere with or hinder access to any information system; 3. Impair the operation of any information system; 4. Impair the reliability of any information system; 5. Impair the security of any information system; Fine Punishment Both 500,000PKR 5 Years yes (b)Whoever recklessly, whether temporarily or not, does any unauthorized access in relation to an information system, at the time when he does the act he knows that is unauthorized, and acts recklessly thereby cause severe; 1. Interference, damage, hindrance, prevention, suppression or obstruction to the function of an information system; 2. Interference or hindrance to the access of any information system; 3. Impairment to the operation of any information system; 4. Impairment to the reliability of any information system; 5. Impairment to the security of any information system; Fine Punishment Both
- 6. 250,000PKR 2 years Yes (c)Whoever commits any offence under sub-section (a) By circumventing or infringing security with respect to any information system, program or data shall be punished with imprisonment of Fine Punishment Both 500,000PKR 3 Years Yes (d) Whoever commits any offenceunder sub-section (b) by circumventing or infringing security with respect to any information system, programor data shall be punished with imprisonmentof Fine Punishment Both 250,000PKR 2 Years Yes (d) Whoever commits any offence under sub section (a) with respect to any Government controlled critical infrastructure information system; program or data that performs a critical public function shall be punished with imprisonment of Fine Punishment Both 7000000 PKR 7 Years Yes Cyber Terrorism: (a) Whoever commits or threatens to commit any of the offences under 1. The use or threat is designed to coerce, intimidate, overawe or create a sense of fear in Government or public section.
- 7. 2. The use or threat of purposes the advancing of the cause where political or religious with intention of— 3. Interfering or disrupting the system, 4. Severe interfere, serious disrupting or damaging the payment system of multiple institutions, 5. Severe Interfere, seriously damage the system at the public scale, 6. Severe interfere, serious disrupting or damaging the system of Civil forces, Armed forces and security forces, Fine Punishment Both 50,000,000 PKR 14 Years Yes Electronic Forgery: (a) Whoever; 1. Without authority, 2. In excess of authority, 3. Through an unauthorized act, Inputs, generates, modifies, delete or suppress data resulting in inauthentic data with any person or an information system shall be punished, Fine Punishment Both 250,000PKR 2 Years Yes (b)Whoever commits any offence; 1. for wrongfulgain; 2. for wrongfulloss; 3. for any economic benefit for oneself or for another person, Fine Punishment Both 250,000PKR 2 Years Yes (c) Whoever commits any offence, fraudulently, dishonestly or with similar intent;
- 8. 1. To influence the public servantin the exercise of a public duty; 2. To influence a Governmentcontrolled information systemor public information system Shall be punished Fine Punishment Both 500,000PKR 3 Years Yes Electronic Fraud: Whoever with fraudulent or dishonest intent; 1. Without authority; 2. In excess of authority; 3. Through an unauthorized act; 4. Any illegal access to information system; 5. Any input, alteration or deletion or suppression theprogramor data 6. Any inference or hindrance data; 7. Copying , transferring the data or moving to any other information system i. Wrongful gain; ii. Wrongful loss; iii. Any economic benefit for oneself or another person; Shall be punished Fine Punishment Both 10,000,000PKR 5 Years Yes Making, Supplying or obtaining devices for use in offence: 1. Whoever produces, makes any device intending it primarily to be used or believing that it is primarily to be used to commit;
- 9. Fine Punishment Both 50,000 PKR 6 Months Yes 2. Whoever transfer, imports, shares or distributes any device that it to be primarily used to commit; Fine Punishment Both 100,000 PKR 1 Years Yes Identify Crime: 1. Whoever knowingly obtains or process of any person’s identity information without law justification and use in offensivework shallbe punished; Fine Punishment Both 50,000 PKR 3 Months Yes 2. Whoever transmits or makes available identity of any person without permission for Fraud or deceit etc shall be punished ; Fine Punishment Both 100,000 PKR 6 Months Yes Special Protection of Women: 1. Whoever knowingly or publically displays electronic communication that harms the reputation of women, threatens sexual acts against women or any explicit images Shall be punished Fine Punishment Both 10,000,00 PKR 1 Year Yes