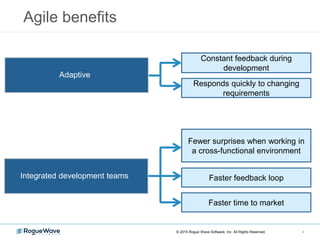
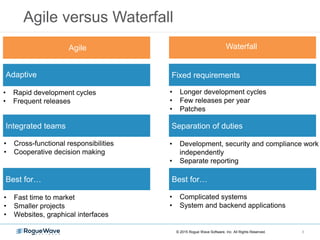
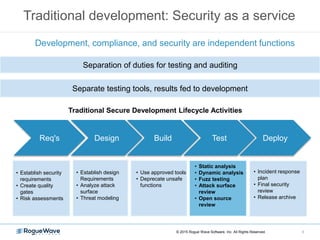
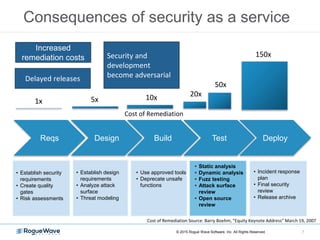
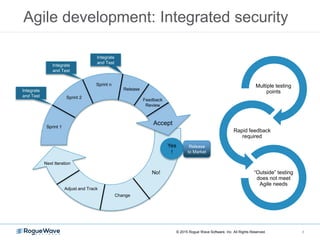
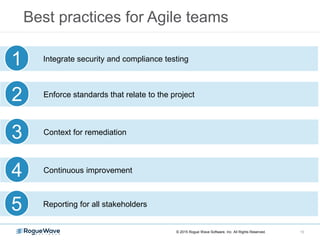
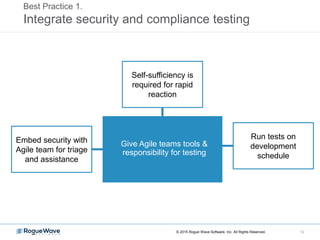
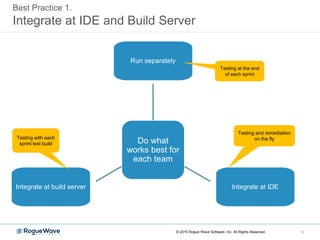
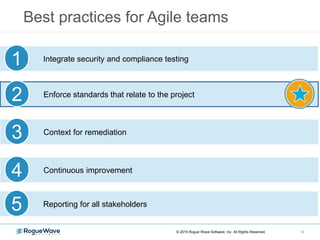
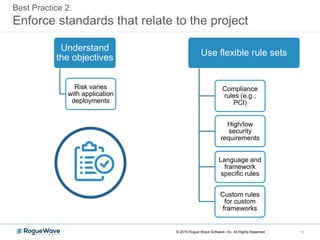
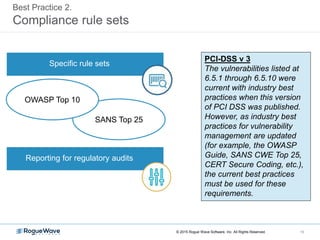
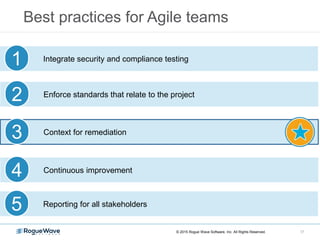
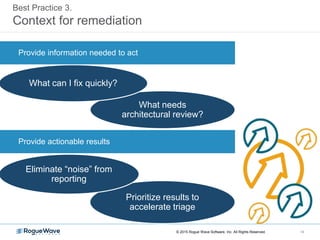
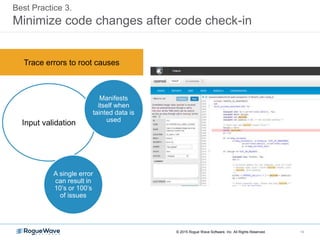
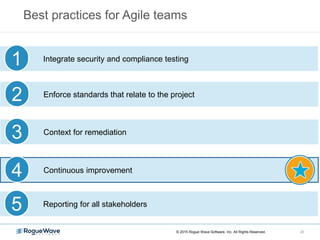
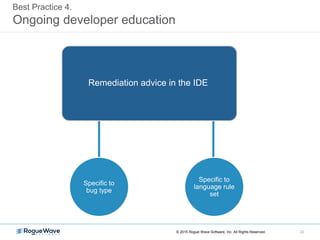
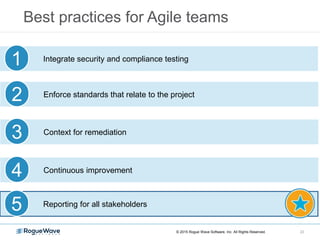
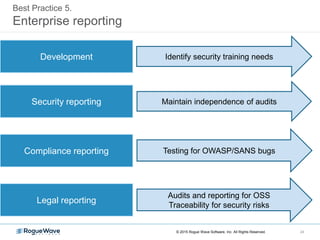
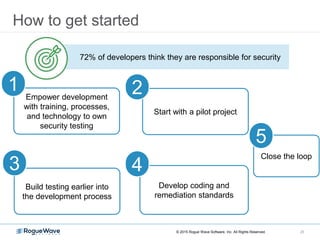
The document discusses best practices for integrating security within agile development processes to enhance application security. It emphasizes the importance of adaptive methodologies, continuous improvement, and providing developers with the tools and training necessary for self-sufficient security testing. Key strategies include integrating security testing early in the development cycle, enforcing compliance standards, and promoting ongoing developer education.