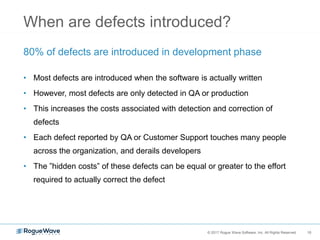
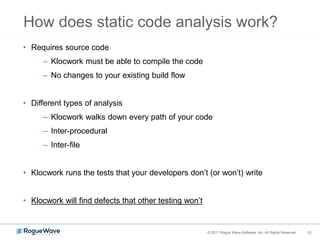
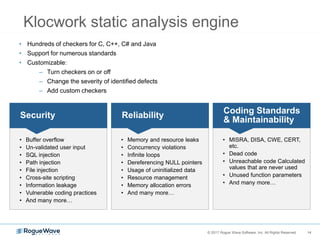
The document discusses the use of C/C++ in developing secure and robust software for embedded and IoT systems, emphasizing the need for proper language choice and security training for developers. It highlights the importance of static code analysis (SCA) and implementing zero-tolerance policies for security issues to improve software reliability. The document also details various coding standards and tools that can assist in identifying and fixing vulnerabilities throughout the development process.