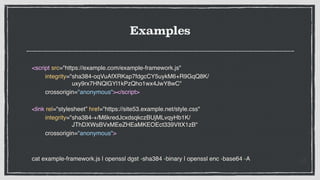
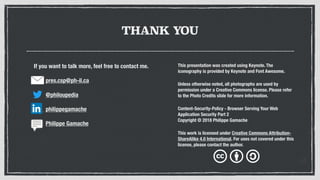
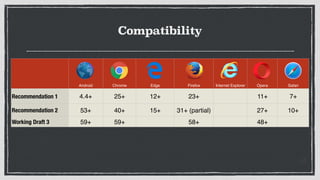
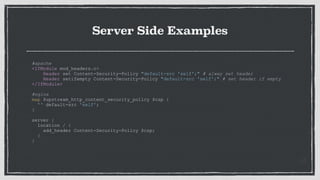
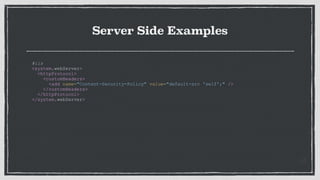
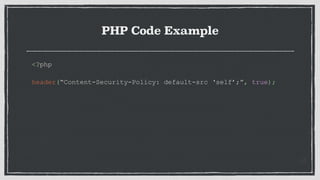
The document provides an overview of Content Security Policy (CSP) as a security measure for web applications, detailing its purpose in protecting against attacks like cross-site scripting and data injection. It outlines CSP specifications, directives, server-side examples in various web servers, and PHP code examples, while discussing compatibility with different browsers. The document concludes with considerations for the implementation of report directives and the use of Subresource Integrity (SRI) to verify resource integrity.


![Logic Structure
Content-Security-Policy: <policy-directive>; <policy-directive>;...
policy-directive:
[<fetch-directive> <fetch-value>[ <fetch-value>]|
<document-directive> <document-value>[ <document-value>]|
<navigation-directive> [<navigation-value>[ <navigation-value>]]|
<report-directive> <report-value>]](https://image.slidesharecdn.com/csp2018-en-180823192543/85/Content-Security-Policy-2018-0-11-320.jpg)
![Fetch Directives
Content-Security-Policy: <policy-directive>; <policy-directive>;...
policy-directive:
[<fetch-directive> <fetch-value>[ <fetch-value>]|
<document-directive> <document-value>[ <document-value>]|
<navigation-directive> [<navigation-value>[ <navigation-value>]]|
<report-directive> <report-value>]](https://image.slidesharecdn.com/csp2018-en-180823192543/85/Content-Security-Policy-2018-0-12-320.jpg)


![Fetch Directives Values
Content-Security-Policy: <policy-directive>; <policy-directive>;...
policy-directive:
[<fetch-directive> <fetch-value>[ <fetch-value>]|
<document-directive> <document-value>[ <document-value>]|
<navigation-directive> [<navigation-value>[ <navigation-value>]]|
<report-directive> <report-value>]](https://image.slidesharecdn.com/csp2018-en-180823192543/85/Content-Security-Policy-2018-0-15-320.jpg)



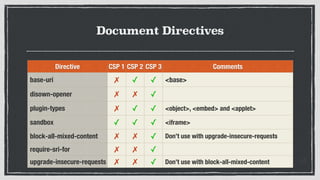
![Document Directives
Content-Security-Policy: <policy-directive>; <policy-directive>;...
policy-directive:
[<fetch-directive> <fetch-value>[ <fetch-value>]|
<document-directive> <document-value>[ <document-value>]|
<navigation-directive> [<navigation-value>[ <navigation-value>]]|
<report-directive> <report-value>]](https://image.slidesharecdn.com/csp2018-en-180823192543/85/Content-Security-Policy-2018-0-22-320.jpg)
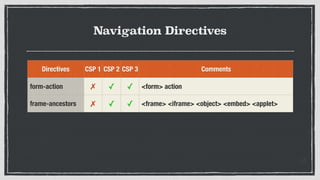
![Navigation Directives
Content-Security-Policy: <policy-directive>; <policy-directive>;...
policy-directive:
[<fetch-directive> <fetch-value>[ <fetch-value>]|
<document-directive> <document-value>[ <document-value>]|
<navigation-directive> [<navigation-value>[ <navigation-value>]]|
<report-directive> <report-value>]](https://image.slidesharecdn.com/csp2018-en-180823192543/85/Content-Security-Policy-2018-0-25-320.jpg)
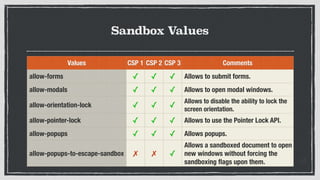
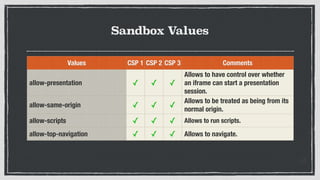
![Sandbox Value
Content-Security-Policy: <policy-directive>; <policy-directive>;...
policy-directive:
[<fetch-directive> <fetch-value>[ <fetch-value>]|
<document-directive> <document-value>[ <document-value>]|
<navigation-directive> [<navigation-value>[ <navigation-value>]]|
<report-directive> <report-value>]
document-directive: [sandbox|...]](https://image.slidesharecdn.com/csp2018-en-180823192543/85/Content-Security-Policy-2018-0-28-320.jpg)
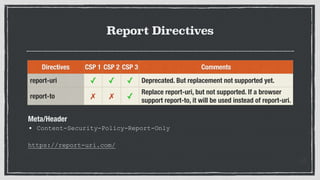
![Report Directives
Content-Security-Policy: <policy-directive>; <policy-directive>;...
policy-directive:
[<fetch-directive> <fetch-value>[ <fetch-value>]|
<document-directive> <document-value>[ <document-value>]|
<navigation-directive> [<navigation-value>[ <navigation-value>]]|
<report-directive> <report-value>]](https://image.slidesharecdn.com/csp2018-en-180823192543/85/Content-Security-Policy-2018-0-32-320.jpg)
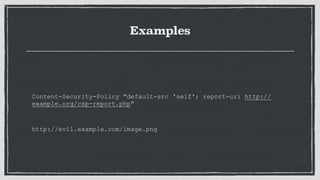
![EXAMPLE
Report-To: { "group": "csp-endpoint",
"max-age": 10886400,
"endpoints": [
{ "url": "https://example.com/csp-reports" }
]
},
{ "group": "hpkp-endpoint",
"max-age": 10886400,
"endpoints": [
{ "url": "https://example.com/hpkp-reports" }
]
}
Content-Security-Policy: ...; report-to csp-endpoint](https://image.slidesharecdn.com/csp2018-en-180823192543/85/Content-Security-Policy-2018-0-36-320.jpg)