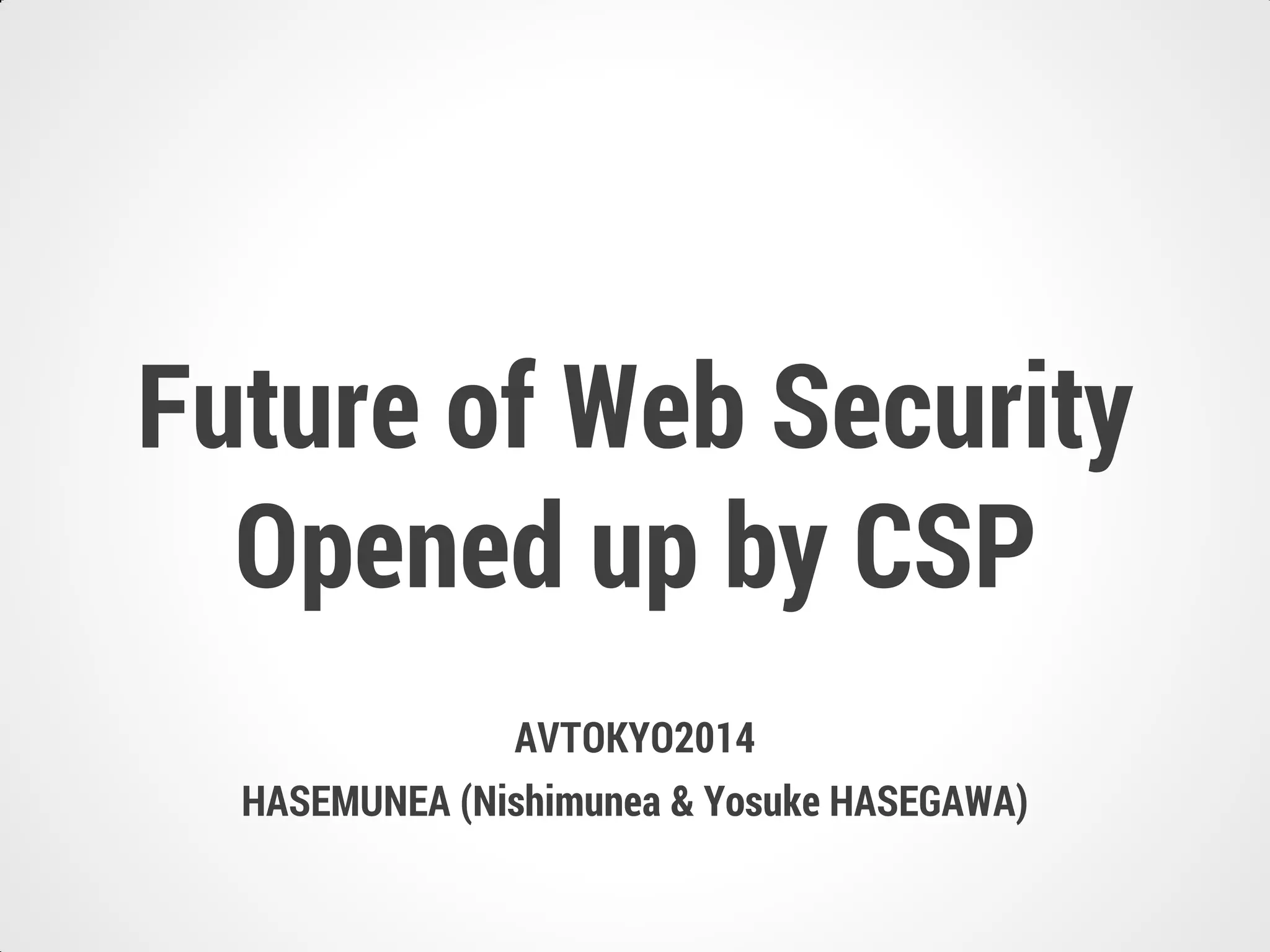
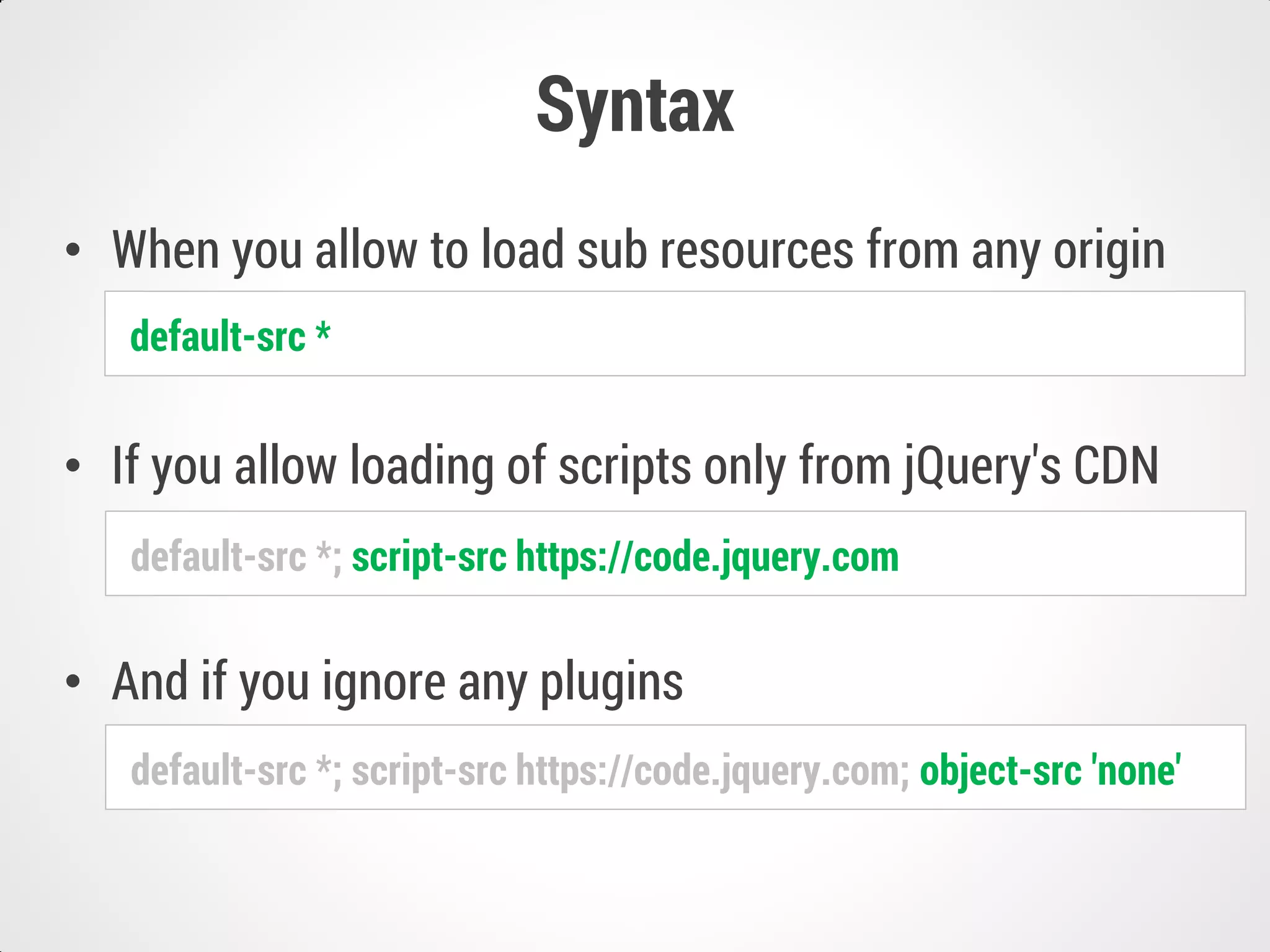
This document summarizes Content Security Policy (CSP), a browser feature that helps mitigate cross-site scripting and other attacks. It discusses CSP's directives for controlling resource loading, browser support, syntax, and violation reporting. It also notes potential issues with abuse of CSP violation reports if not properly validated and formatted on the server-side.


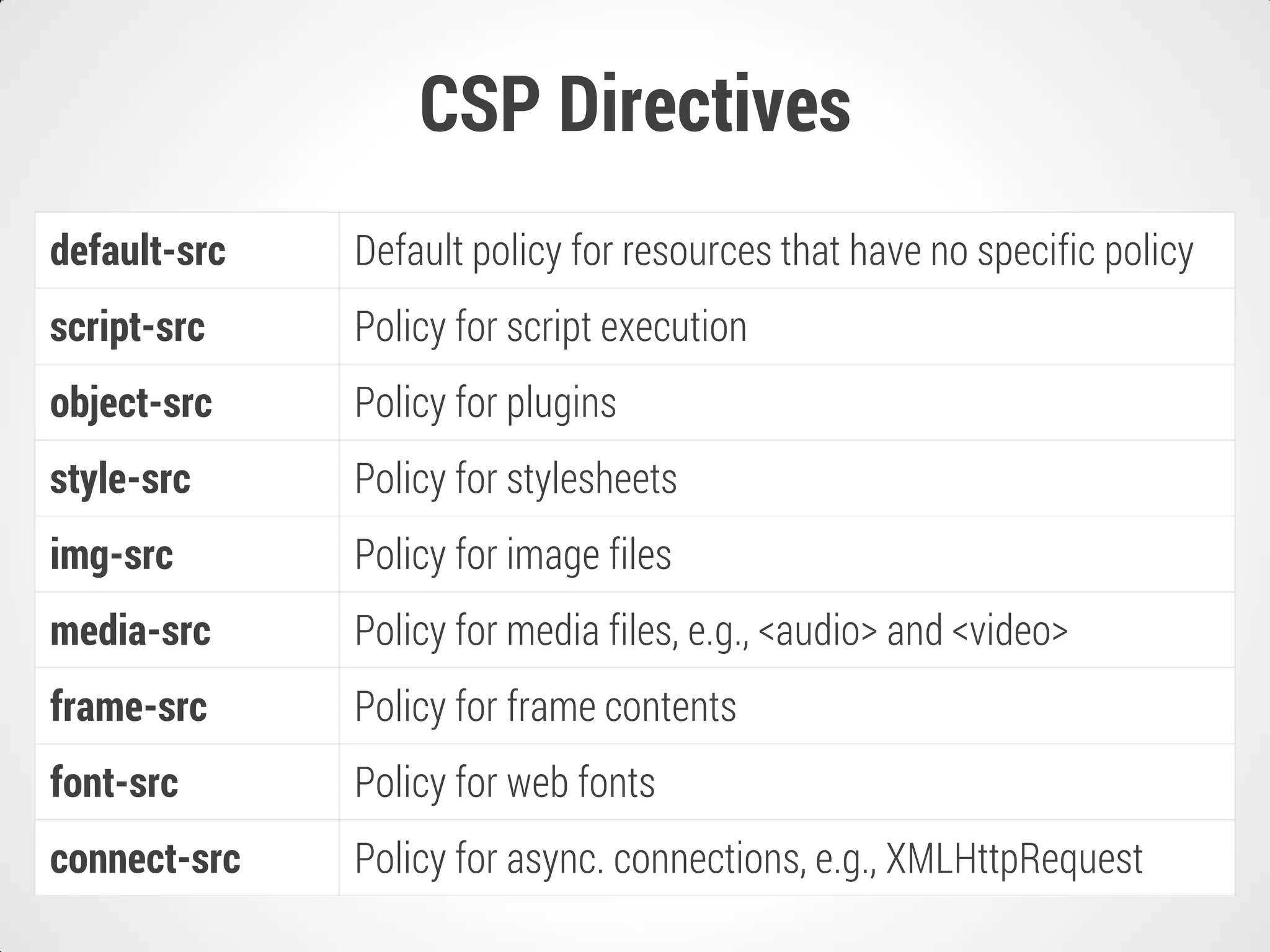
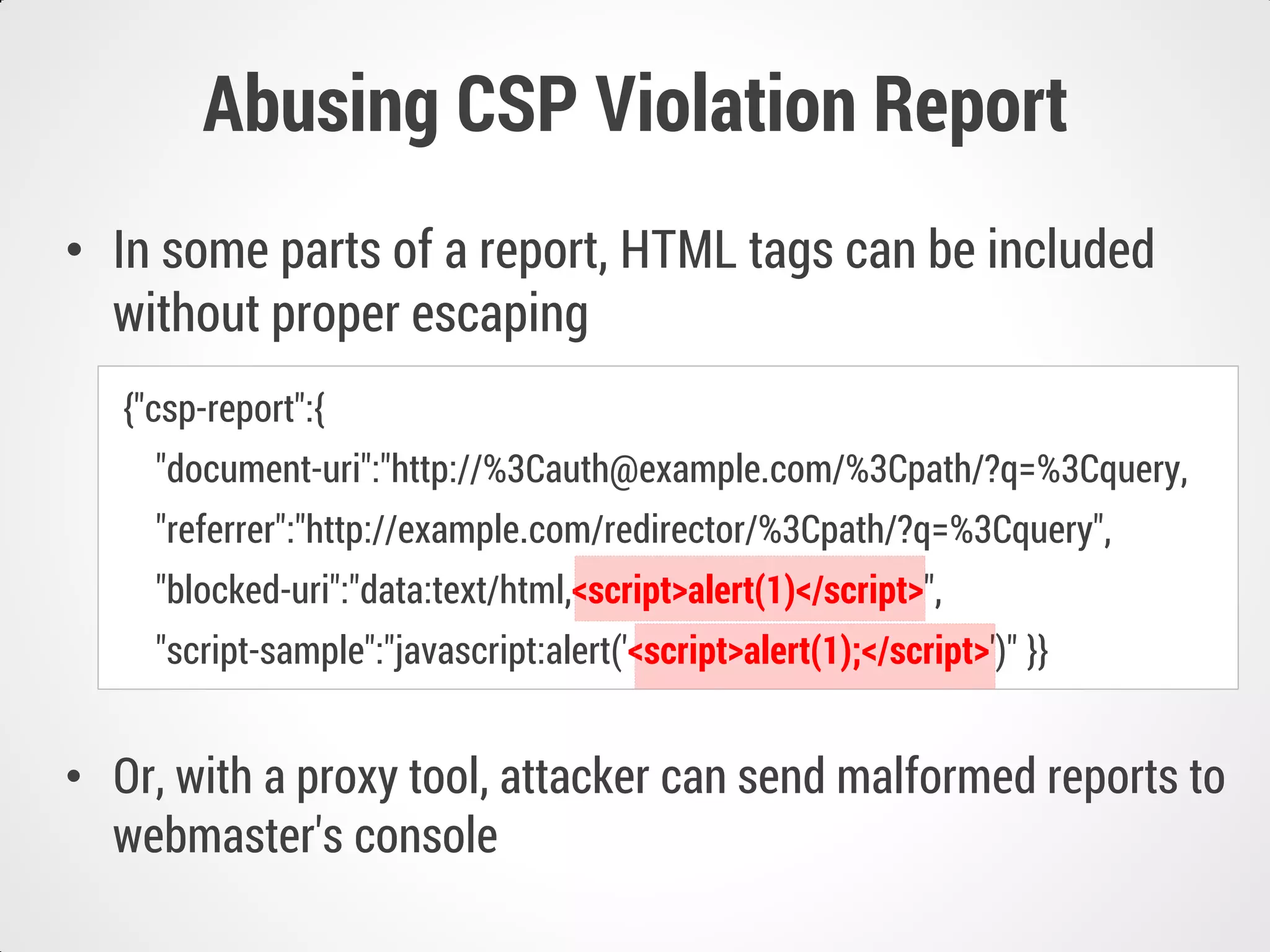
![CSP Level2 Directives
base-uri Policy for base[href]
form-action Policy for form[action]
plugin-types Policy for executable plugin MIME types
referrer Nearly identical to meta[name=referrer]
frame-ancestors Nearly identical to X-Frame-Options
xss-protection Nearly identical to X-XSS-Protection
child-src Policy for child contents e.g., frames and workers
sandbox Sandbox that is applied to the document](https://image.slidesharecdn.com/avtokyo2014hasemunea-141115093752-conversion-gate01/75/Future-of-Web-Security-Opened-up-by-CSP-8-2048.jpg)