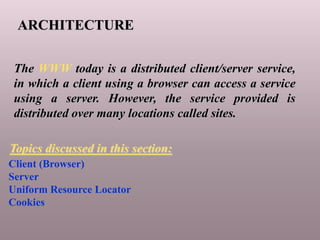
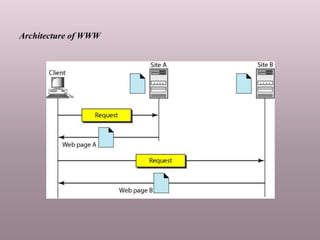
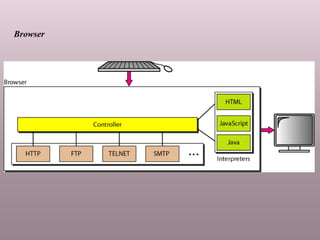
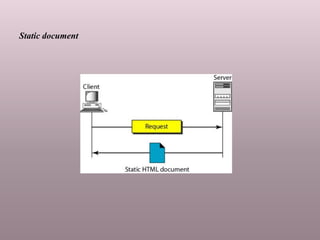
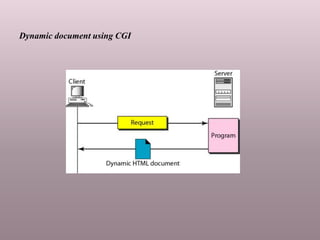
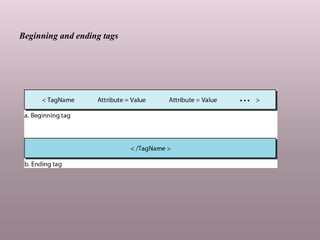
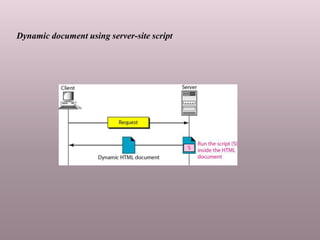
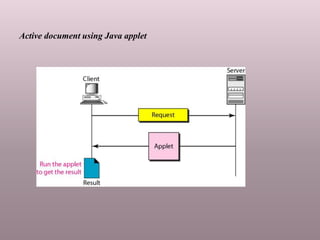
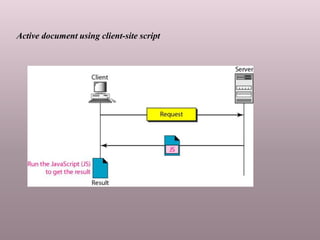
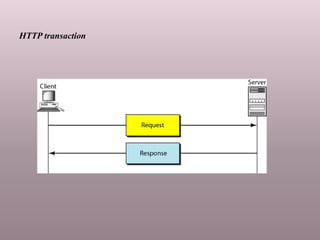
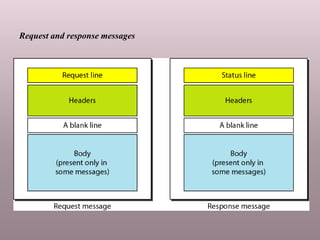
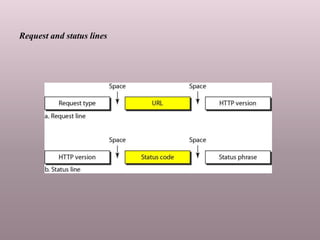
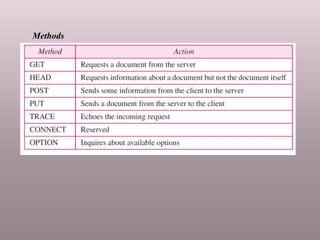
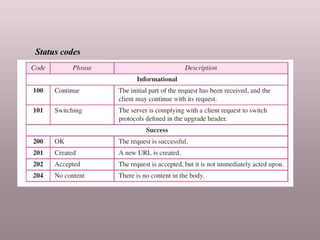
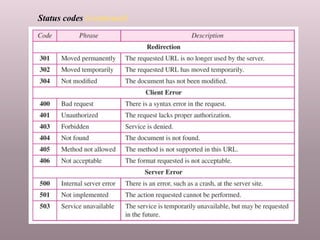
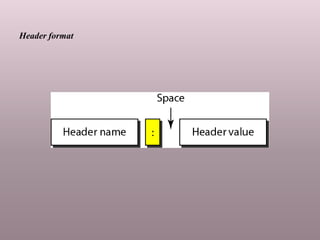
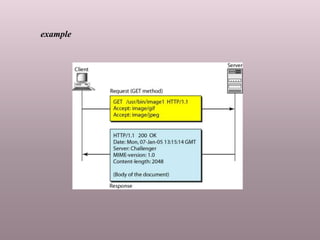
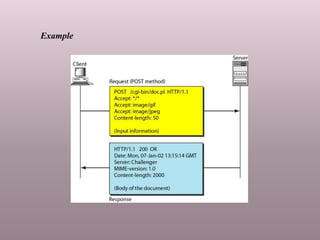
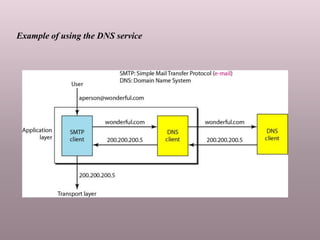
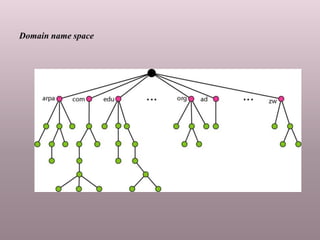
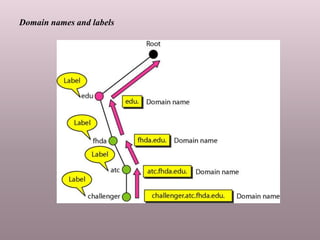
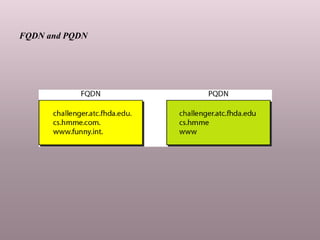
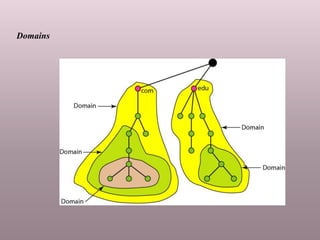
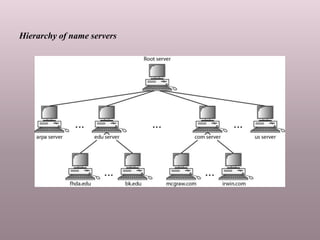
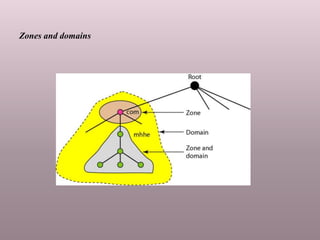
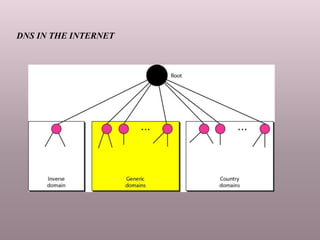
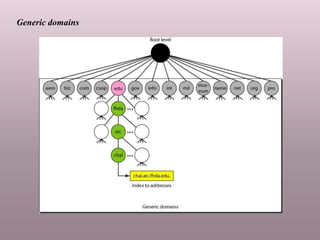
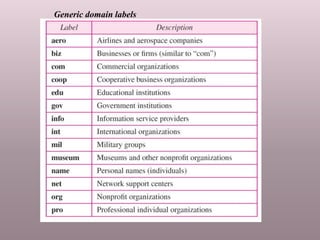
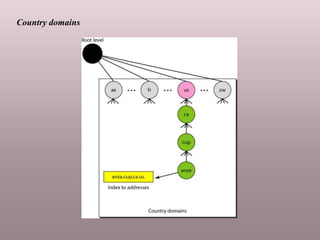
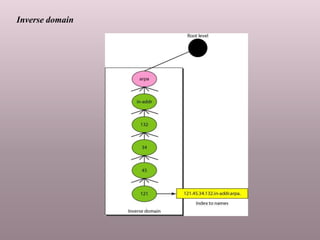
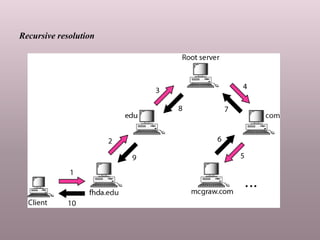
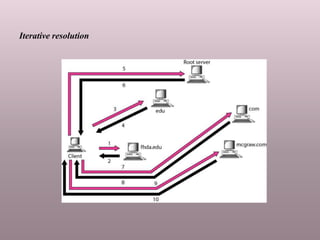
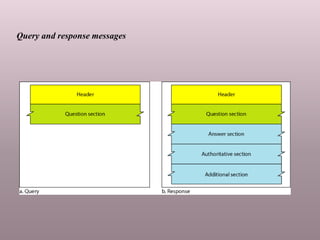
The document outlines the architecture of the World Wide Web (WWW) as a distributed client/server service, detailing the various types of web documents: static, dynamic, and active. It also explains the Hypertext Transfer Protocol (HTTP) and the hierarchical structure of domain name systems (DNS), along with how DNS resolves names to addresses. Key topics include the design and distribution of domain names, server types, and DNS messaging formats.