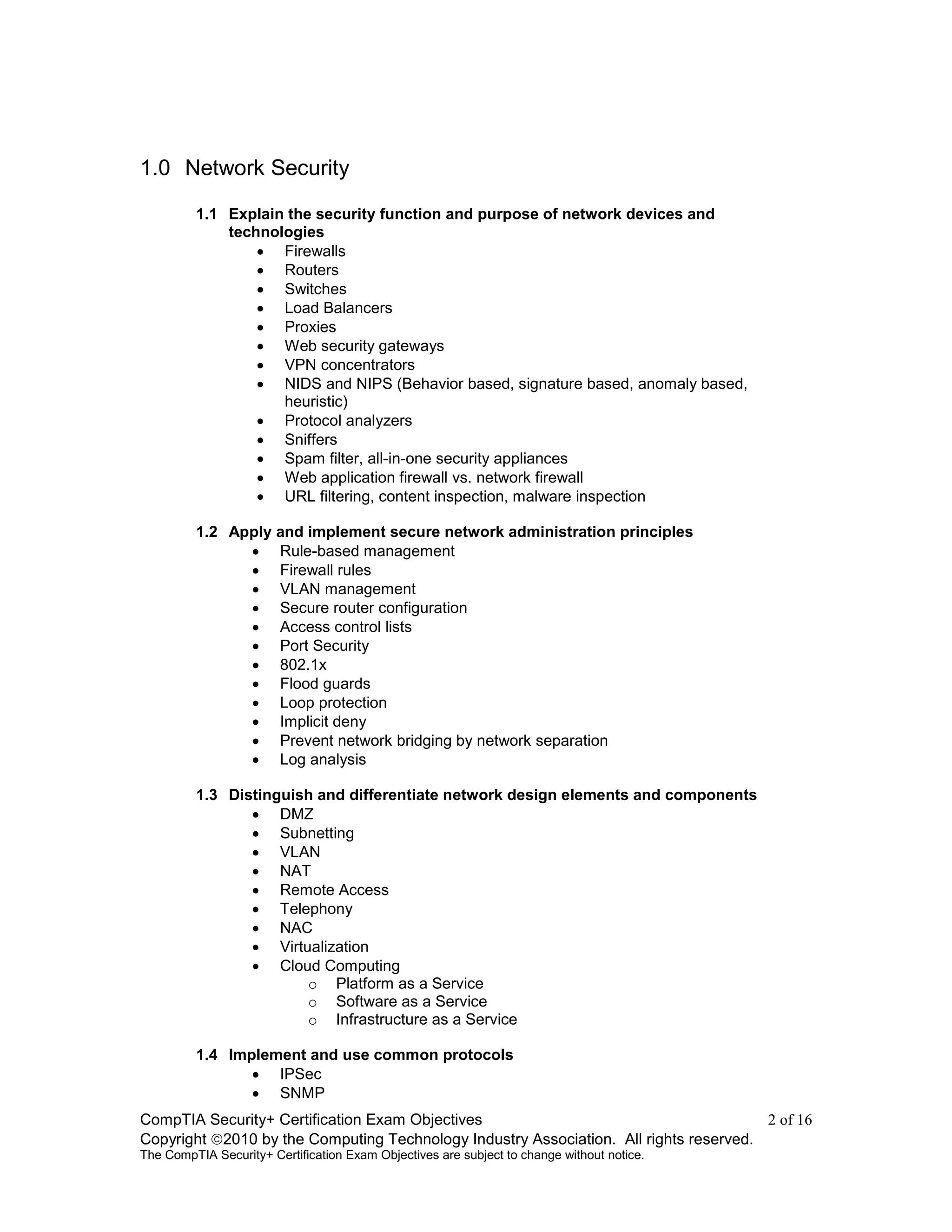
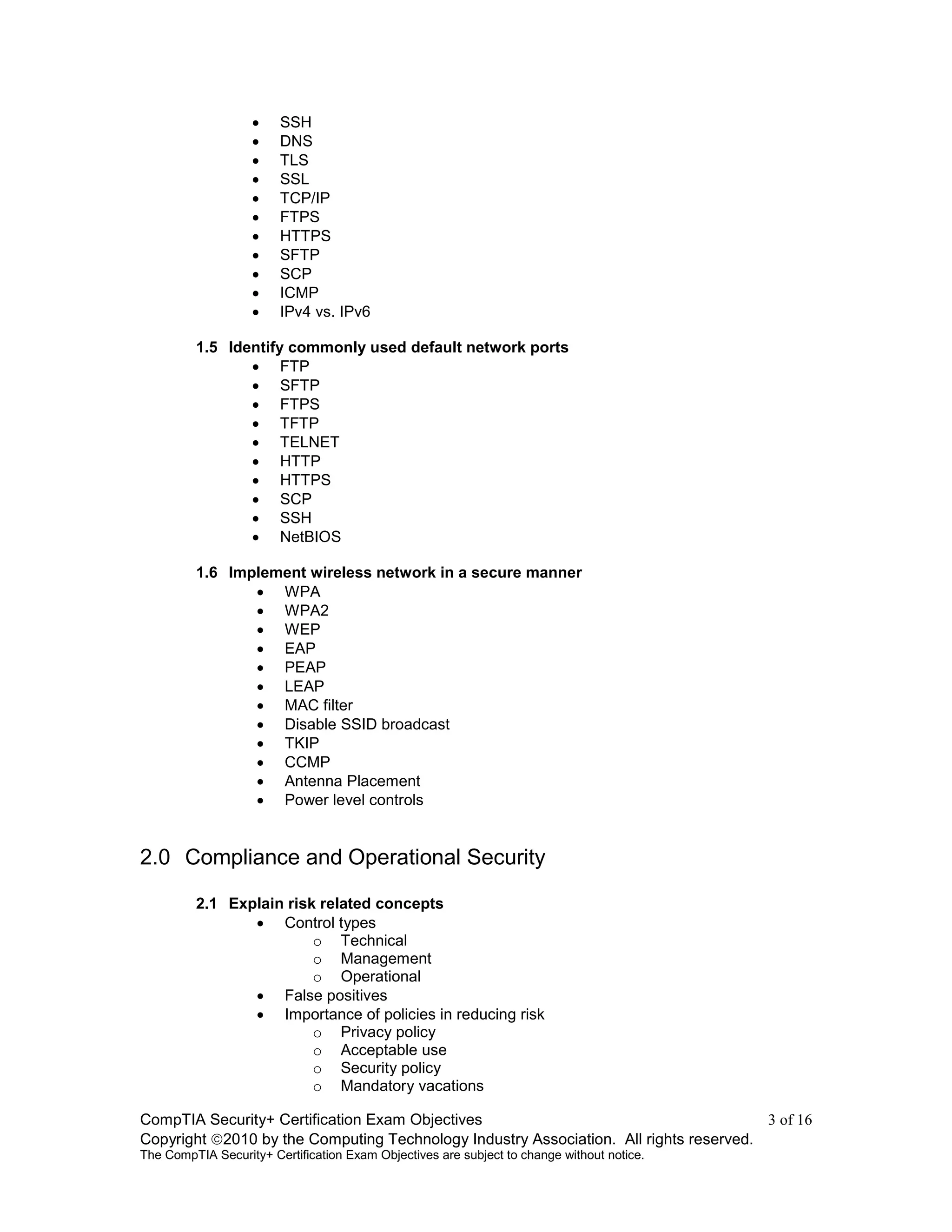
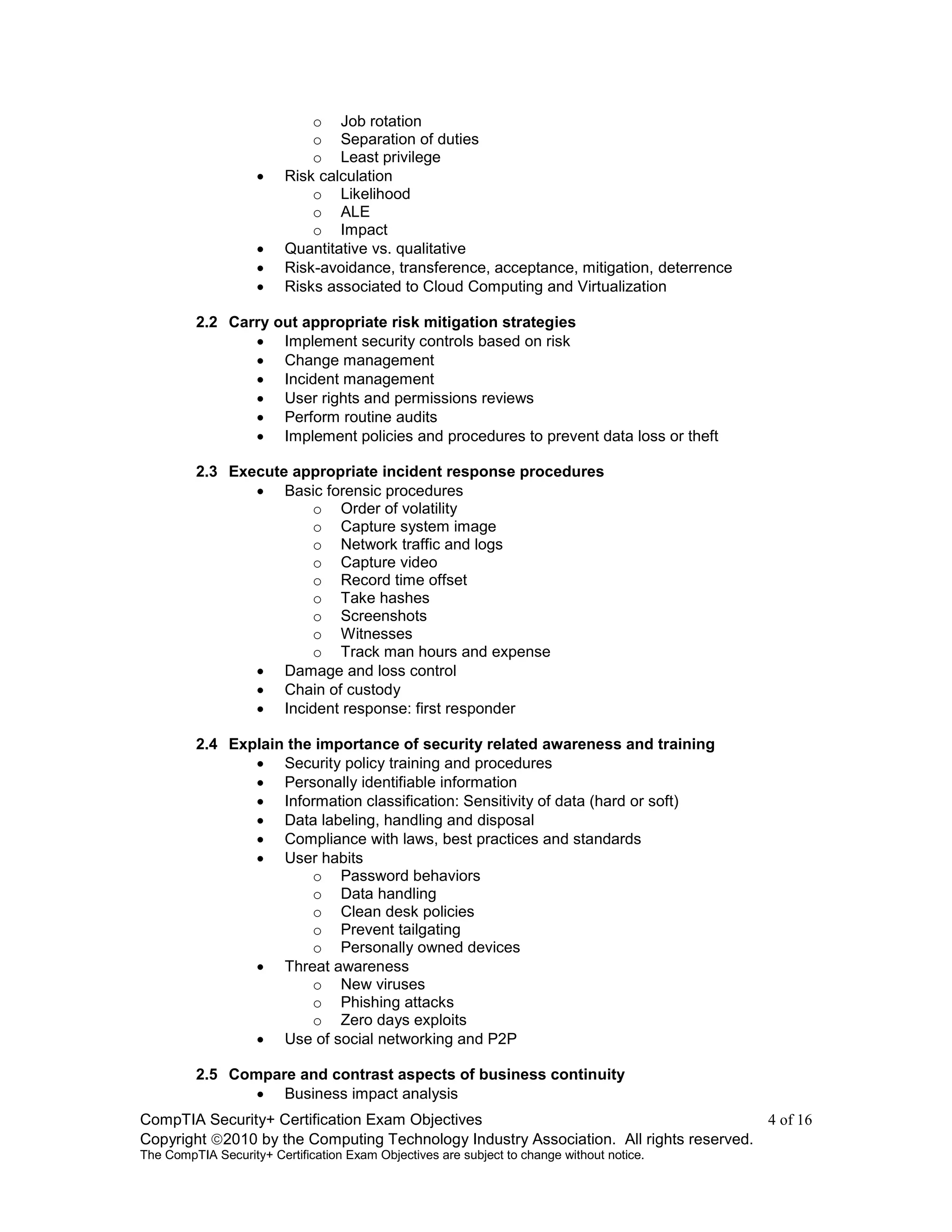
The document provides an overview of the CompTIA Security+ certification exam objectives. It describes the purpose of the exam as validating foundational security skills and knowledge for IT security professionals with 2 years of experience. It outlines the 6 domains covered in the exam, including network security, compliance and operational security, threats and vulnerabilities, application/data/host security, access control and identity management, and cryptography. For each domain, it lists the objectives and example topics that may be included on the exam.