Embed presentation
Download to read offline
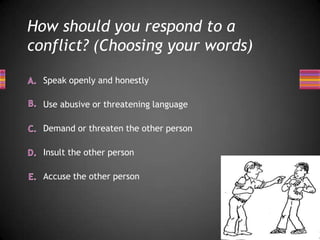

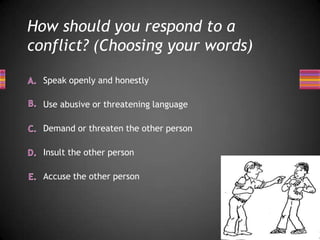
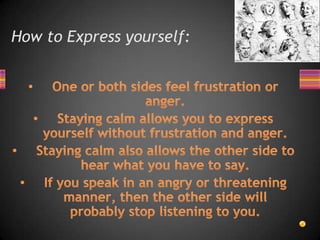
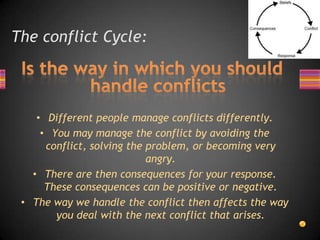
The document discusses conflict resolution and communication. It advises that during a conflict, one should [1] speak openly and honestly without insults, accusations, demands or threats, [2] understand that different people handle conflicts differently which can have positive or negative consequences, and [3] actively listen to fully understand the other person's perspective rather than interrupt or avoid listening.