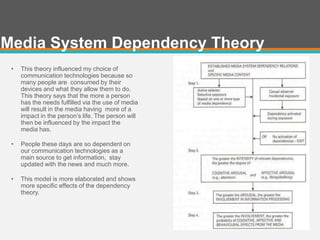
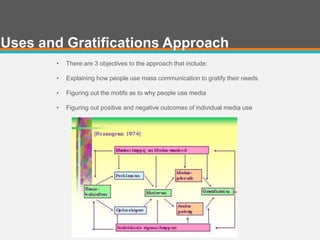
This document provides a history of the development of communication technology over time. It discusses the evolution from the telephone to cell phones to smartphones, and the development of computers from desktops to laptops to tablets. It also outlines the creation of the internet and how it enabled new forms of communication like email, social media, and user-generated content on wikis. The document analyzes how theories like media dependency theory, uses and gratifications theory, and the diffusion of innovations help explain people's adoption of new communication technologies.