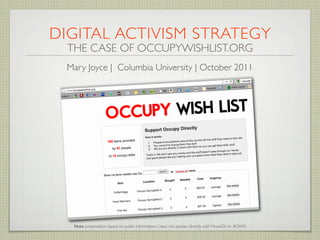
Digital Activism Strategy: The Case of OccupyWishList.org
•
5 likes•2,011 views
Presents a Goal > Assets > Actions framework for digital activism strategy while using the Occupy Wish List website as an example.
Report
Share
Report
Share
Download to read offline
Recommended
Développement d'un logiciel de réseau social comme soutien à une communauté d...

Mémoire présenté pour l’obtention du DESS STAF
Sciences et Technologies de l’Apprentissage et de la Formation
TECFA, Faculté de Psychologie et de Sciences de l'Education, Université de Genève
juin 2008
1. INTRODUCTION
2. REVUE DE LITTERATURE
2.1. RESEAU SOCIAL
2.1.1. THEORIE DES SIX DEGRES
2.1.2. THEORIE DES LIENS FAIBLES ET DES LIENS FORTS
2.1.3. NOMBRE DE DUNBAR
2.2. LOGICIEL SOCIAL
2.2.1. COMMUNAUTES SUR INTERNET ET INTERACTIONS SOCIALES
2.2.2. TYPOLOGIE DES LOGICIELS SOCIAUX
2.2.3. TYPOLOGIE DES LOGICIELS DE RESEAUX SOCIAUX
2.2.4. FOAF – FRIEND OF A FRIEND
2.3. RESUME
3. ANALYSE DES LOGICIELS SOCIAUX
3.1. LINKEDIN
3.2. 6NERGIES
3.3. LAST.FM
4. LOGICIEL SOCIAL DE TECFA
5. CONCLUSIONS ET PERSPECTIVES
6. BIBLIOGRAPHIE
ANNEXE 1 : LDAP ATTRIBUTS
3.4. RESUME
12 Tendances en Marketing Digital pour 2013

Que nous réserve le marketing digital en 2013 ? Voici 12 tendances sélectionnées par le pôle Planning Digital de l'agence NiceToMeetYou - présentées lors de la matinée conférence du 17 novembre 2012 à Lille.
Une stratégie digitale, c'est quoi ?

La stratégie digitale doit être perçue comme un fil d’Ariane assurant une agilité suffisante pour pouvoir se poser les bonnes questions régulièrement et ne pas hésiter à reconnaitre ses erreurs afin de ne pas se retrouver dans une situation inextricable.
Atelier : comment mettre en place un plan de communication sur les réseaux so...

Méthodologie en 7 étapes pour créer une plan de communication 2.0. De la recherche des objectifs à l'évaluation des retombées.
Batir une stratégie editoriale cyrille frank

Pour se démarquer des concurrents et émerger dans la masse des contenus disponibles, il vous faut une stratégie éditoriale. Afin d'offrir la bonne offre au bon public. Voici les étapes indispensables pour y parvenir.
The 7 Drivers of Social Media Management

The 7 Drivers of Social Media Management Framework is adapted from the Marketing Communications Framework as taught at the Edinburgh Business School. This presentation walks the reader through the seven necessary steps to successfully manage social media activities in a company or for a brand.
All pictures/graphs taken/created by the author, except where stated/sourced differently.
DevRelCon 2018 - Influence with Purpose How to Identify, Execute and Measure ...

Creating a successful DevRel program means identifying and implementing strategy based on key pillars that allow developers to be positive influencers in their community. MessageMedia’s Benjamin Mostafa shares planning, implementation, metric tips and key insights learned along the way.
Recommended
Développement d'un logiciel de réseau social comme soutien à une communauté d...

Mémoire présenté pour l’obtention du DESS STAF
Sciences et Technologies de l’Apprentissage et de la Formation
TECFA, Faculté de Psychologie et de Sciences de l'Education, Université de Genève
juin 2008
1. INTRODUCTION
2. REVUE DE LITTERATURE
2.1. RESEAU SOCIAL
2.1.1. THEORIE DES SIX DEGRES
2.1.2. THEORIE DES LIENS FAIBLES ET DES LIENS FORTS
2.1.3. NOMBRE DE DUNBAR
2.2. LOGICIEL SOCIAL
2.2.1. COMMUNAUTES SUR INTERNET ET INTERACTIONS SOCIALES
2.2.2. TYPOLOGIE DES LOGICIELS SOCIAUX
2.2.3. TYPOLOGIE DES LOGICIELS DE RESEAUX SOCIAUX
2.2.4. FOAF – FRIEND OF A FRIEND
2.3. RESUME
3. ANALYSE DES LOGICIELS SOCIAUX
3.1. LINKEDIN
3.2. 6NERGIES
3.3. LAST.FM
4. LOGICIEL SOCIAL DE TECFA
5. CONCLUSIONS ET PERSPECTIVES
6. BIBLIOGRAPHIE
ANNEXE 1 : LDAP ATTRIBUTS
3.4. RESUME
12 Tendances en Marketing Digital pour 2013

Que nous réserve le marketing digital en 2013 ? Voici 12 tendances sélectionnées par le pôle Planning Digital de l'agence NiceToMeetYou - présentées lors de la matinée conférence du 17 novembre 2012 à Lille.
Une stratégie digitale, c'est quoi ?

La stratégie digitale doit être perçue comme un fil d’Ariane assurant une agilité suffisante pour pouvoir se poser les bonnes questions régulièrement et ne pas hésiter à reconnaitre ses erreurs afin de ne pas se retrouver dans une situation inextricable.
Atelier : comment mettre en place un plan de communication sur les réseaux so...

Méthodologie en 7 étapes pour créer une plan de communication 2.0. De la recherche des objectifs à l'évaluation des retombées.
Batir une stratégie editoriale cyrille frank

Pour se démarquer des concurrents et émerger dans la masse des contenus disponibles, il vous faut une stratégie éditoriale. Afin d'offrir la bonne offre au bon public. Voici les étapes indispensables pour y parvenir.
The 7 Drivers of Social Media Management

The 7 Drivers of Social Media Management Framework is adapted from the Marketing Communications Framework as taught at the Edinburgh Business School. This presentation walks the reader through the seven necessary steps to successfully manage social media activities in a company or for a brand.
All pictures/graphs taken/created by the author, except where stated/sourced differently.
DevRelCon 2018 - Influence with Purpose How to Identify, Execute and Measure ...

Creating a successful DevRel program means identifying and implementing strategy based on key pillars that allow developers to be positive influencers in their community. MessageMedia’s Benjamin Mostafa shares planning, implementation, metric tips and key insights learned along the way.
Know Thyself: How Suffering Through An Existential Crisis Will Help you Plan ...

Know Thyself: How Suffering Through An Existential Crisis Will Help you Plan ...Smithsonian Institution Archives
A presentation on coming up with institutional strategy before planning for metrics. Given as part of the "Clicks that Count: Achieve and Measure Online Success with Google Analytics & Adwords" workshop at Museums and the Web 2012, San Diego, CA, USA. museumsandtheweb.com
Details the process through which the Smithsonian Institution Archives eventually decided on their measurements for a metrics dashboard, using case studies illustrating how the Archives came up with the goals, strategies, tactics, and finally, measurements that drive their dashboard. Consideration was also given to a broader analytics approach, using other techniques to gain insight pertaining into other, non-web program elements. What is a Social Media Strategy?

This webinar is designed for the nonprofit organization that wants to understand a social media strategy, and what goes into developing one. During the webinar, we’ll discuss the following:
- Benefits of creating a strategy
- How a social media strategy supports overall organizational goals
- Research needed to before you create your strategy
- The major components of a social media strategy
- Tying the social media strategy into the website
- How a social media strategy supports fundraising
Learning about CHAOSS - Ana Jimenez Santamaria, Daniel Izquierdo

This talk seeks to introduce the CHAOSS -Community Health Analytics for Open Source Projects- to the InnerSource practitioners. Metrics and KPIs are of importance for the InnerSource Commons as seen in the several talks and discussions during the last summits.
CHAOSS was born in 2017 under the Linux Foundation umbrella and this is a hub of OSS projects and organizations participating in the definition of metrics of interest for Open Source projects.
As active members of CHAOSS, there are some lessons learnt when dealing with those metrics and KPIs, either at the theoretical definition and from a software implementation that might be worth exploring across the InnerSource ecosystem.
This talk will bring this discussion and how to potentially build bridges between both
Social Media Strategie in 1 dag - 5 juli 2011 

De 7 stappen van de Social Media Strategie - Workshop 'Social Media Strategie in 1 dag' tijdens #socialsummer in Seats2meet.com Maarssen (#s2m0346)
Social Media Training Workshop Coaching Advies >>> Socialbites.com
Noew 2012 presentation

Online Marketing, Social Media and SEO presentation at New Orleans Entrepreneurs Week 2012 by McKenzie Coco and Tiffany Starnes of FSC Interactive.
Achieving Success with Limited Resources

A look at how to create a theory of change and strategy screen to evaluate opportunities.
Entering The Blogosphere: The Nucleus Of Your Healthcare Social Media Strateg...

Presentation from Eric Brody, President of NJ-based branding and marketing firm Trajectory – Entering The Blogosphere: The Nucleus Of Your Healthcare Social Media Strategy from the IQPC Strategic Social Media For Healthcare Conference in NYC.
NOEW 2012 presentation

Online marketing, social media and SEO presented to New Orleans Entrepreneur Week by McKenxzie Coco and Tiffany Starnes of FSC Interactive.
Strategic Planning for Networks

Strategic planning. You know you should be doing more of it. But the way you normally do it requires lots of up-front time to do and lots of follow-up time to get buy-in. And frankly, you have trouble with the buy-in part. All that trouble, minimal follow-through.
Great strategic planning processes are lightweight and participatory. This is nice-to-have for organizations, and it's critical for networks, where you don't have the benefit of hierarchy to influence its behavior. Networks will do what they do.
In this Leadership Learning Community webinar, I describe how to do strategic planning for networks. I draw heavily from my experience leading the open strategic planning process for the Wikimedia movement, which drew over 1,000 participants and led to a movement-wide shift in focus on increasing reach and participation in developing countries. I share how you can leverage these types of processes for both your network and your organization
Nonprofit data-driven leadership 

Presentation by Debra Askanase, Steve Backman, Marc Baizman at the 2011 Massachusetts Nonprofit Network/Associated Grantmakers of Massachusetts annual conference.
About Do Big Good - March 2020

This one-pager describes the work of Do Big Good, a Seattle-based impact measurement firm. More at www.dobiggood.com.
Measuring Network Impact

Slide deck for a workshop for client Code for America. Do Big Good is designing an impact measurement system for their network of 80+ civic tech volunteer Brigades.
More Related Content
Similar to Digital Activism Strategy: The Case of OccupyWishList.org
Know Thyself: How Suffering Through An Existential Crisis Will Help you Plan ...

Know Thyself: How Suffering Through An Existential Crisis Will Help you Plan ...Smithsonian Institution Archives
A presentation on coming up with institutional strategy before planning for metrics. Given as part of the "Clicks that Count: Achieve and Measure Online Success with Google Analytics & Adwords" workshop at Museums and the Web 2012, San Diego, CA, USA. museumsandtheweb.com
Details the process through which the Smithsonian Institution Archives eventually decided on their measurements for a metrics dashboard, using case studies illustrating how the Archives came up with the goals, strategies, tactics, and finally, measurements that drive their dashboard. Consideration was also given to a broader analytics approach, using other techniques to gain insight pertaining into other, non-web program elements. What is a Social Media Strategy?

This webinar is designed for the nonprofit organization that wants to understand a social media strategy, and what goes into developing one. During the webinar, we’ll discuss the following:
- Benefits of creating a strategy
- How a social media strategy supports overall organizational goals
- Research needed to before you create your strategy
- The major components of a social media strategy
- Tying the social media strategy into the website
- How a social media strategy supports fundraising
Learning about CHAOSS - Ana Jimenez Santamaria, Daniel Izquierdo

This talk seeks to introduce the CHAOSS -Community Health Analytics for Open Source Projects- to the InnerSource practitioners. Metrics and KPIs are of importance for the InnerSource Commons as seen in the several talks and discussions during the last summits.
CHAOSS was born in 2017 under the Linux Foundation umbrella and this is a hub of OSS projects and organizations participating in the definition of metrics of interest for Open Source projects.
As active members of CHAOSS, there are some lessons learnt when dealing with those metrics and KPIs, either at the theoretical definition and from a software implementation that might be worth exploring across the InnerSource ecosystem.
This talk will bring this discussion and how to potentially build bridges between both
Social Media Strategie in 1 dag - 5 juli 2011 

De 7 stappen van de Social Media Strategie - Workshop 'Social Media Strategie in 1 dag' tijdens #socialsummer in Seats2meet.com Maarssen (#s2m0346)
Social Media Training Workshop Coaching Advies >>> Socialbites.com
Noew 2012 presentation

Online Marketing, Social Media and SEO presentation at New Orleans Entrepreneurs Week 2012 by McKenzie Coco and Tiffany Starnes of FSC Interactive.
Achieving Success with Limited Resources

A look at how to create a theory of change and strategy screen to evaluate opportunities.
Entering The Blogosphere: The Nucleus Of Your Healthcare Social Media Strateg...

Presentation from Eric Brody, President of NJ-based branding and marketing firm Trajectory – Entering The Blogosphere: The Nucleus Of Your Healthcare Social Media Strategy from the IQPC Strategic Social Media For Healthcare Conference in NYC.
NOEW 2012 presentation

Online marketing, social media and SEO presented to New Orleans Entrepreneur Week by McKenxzie Coco and Tiffany Starnes of FSC Interactive.
Strategic Planning for Networks

Strategic planning. You know you should be doing more of it. But the way you normally do it requires lots of up-front time to do and lots of follow-up time to get buy-in. And frankly, you have trouble with the buy-in part. All that trouble, minimal follow-through.
Great strategic planning processes are lightweight and participatory. This is nice-to-have for organizations, and it's critical for networks, where you don't have the benefit of hierarchy to influence its behavior. Networks will do what they do.
In this Leadership Learning Community webinar, I describe how to do strategic planning for networks. I draw heavily from my experience leading the open strategic planning process for the Wikimedia movement, which drew over 1,000 participants and led to a movement-wide shift in focus on increasing reach and participation in developing countries. I share how you can leverage these types of processes for both your network and your organization
Nonprofit data-driven leadership 

Presentation by Debra Askanase, Steve Backman, Marc Baizman at the 2011 Massachusetts Nonprofit Network/Associated Grantmakers of Massachusetts annual conference.
Similar to Digital Activism Strategy: The Case of OccupyWishList.org (20)
Know Thyself: How Suffering Through An Existential Crisis Will Help you Plan ...

Know Thyself: How Suffering Through An Existential Crisis Will Help you Plan ...
Learning about CHAOSS - Ana Jimenez Santamaria, Daniel Izquierdo

Learning about CHAOSS - Ana Jimenez Santamaria, Daniel Izquierdo
Socialbiteskeynoteworkshop05072011socialmediastrategie 110705222950-phpapp02

Socialbiteskeynoteworkshop05072011socialmediastrategie 110705222950-phpapp02
Entering The Blogosphere: The Nucleus Of Your Healthcare Social Media Strateg...

Entering The Blogosphere: The Nucleus Of Your Healthcare Social Media Strateg...
Leadership and management of social organisations clara

Leadership and management of social organisations clara
More from Mer Joyce
About Do Big Good - March 2020

This one-pager describes the work of Do Big Good, a Seattle-based impact measurement firm. More at www.dobiggood.com.
Measuring Network Impact

Slide deck for a workshop for client Code for America. Do Big Good is designing an impact measurement system for their network of 80+ civic tech volunteer Brigades.
Do Big Good - About Us - Oct. 2019

This one-pager describes the work of Do Big Good, a Seattle-based in social impact measurement firm.
Job Description: Research Assistant

The role of Research Assistant is a flexible contract position.
It will allow a young professional, graduate student, or skilled undergraduate interested in social change the opportunity to practice and learn a range of skills related to qualitative research methods as they are used in the measurement of social change projects.
The role will be largely virtual, with occasional in-person meetings with a project supervisor if the applicant lives in Seattle. Though the Research Assistant will have some scheduled work when surveying research subjects, work will be largely independent. Over the next four months, working time is not expected to exceed five (5) hours per week.
Job Description: Data Assistant

The position of Data Assistant is a flexible contract position.
It will allow a young professional, graduate student, or skilled undergraduate interested in social change the opportunity to practice a range of skills related to basic statistical analysis as it is used to measure the effectiveness of social change projects.
The role is extremely flexible. It will be largely virtual, with occasional in-person meetings with a project supervisor if the applicant lives in Seattle. The Data Assistant will thus work largely independently and be free to determine their own work hours. Over the next four months, total work is not expected to exceed thirty (30) hours total and will also not exceed five (5) hours in any given week.
Activism Success: A Concept Explication

A thesis submitted by Mary Joyce in partial fulfillment of the requirements of the degree of Master of Arts in Communication (University of Washington, 2014)
A Plea to Defend our Institutions

Memo to Sen. Lisa Murkowski asking her to oppose Judge Kavanaugh's nomination on institutional grounds, hand-delivered to her DC office on October 4, 2018, by the author.
The Election Blogging Guide (2006)

An early effort to apply digital tools to political uses, co-written with Zephyr Teachout and Solana Larsen.
Video Impact Assessment: Closing the Impact Gap

Last month I created an assessment for an international foundation on the impact of their video grants. The assessment (below) includes analysis and visualization of how 37 grantees used video in their advocacy work, and the effects of that use.
For this project I first analyzed grantee self-reports on how they were using video. I then developed a model comparing grantee activities and outcomes and finally visualized this analysis in the form of an easily skimmable “report card” for each grantee. This public version includes 10 representative reports from among the original 37.
90-Minute Guru: Communication Strategy

These slides present and explain the three fundamental stages of communication strategy – vision, audit, and snapshot – along with the steps needed to achieve them.
Advocacy Gardening: Help Your Campaign Grow

A process for workshopping multiple campaign projects in a diverse group that includes grantee campaigners, grantee non-campaigners, funders, and consultants.
Video Advocacy Tips

What video can do for your campaign; How to get people to watch your video; Social proofing; Measurement
Contention Beyond Social Movements: Activism and its Benefits

Talk for the Preconference on Qualitative Political Communication Research | International Communication Association | May 22, 2014
9 Quick-Start Blog Posts for Activists

1) The Pass-it-Along Post
2) The “We’re Real People” Post
3) The Community Appreciation Post
4) The “Our Response” Post
5) The Informative Listicle
6) The Mobilization Post
7) The Ignored News Story
8) The Guest Post
9) The Email Interview
Coder Training Slides (v2.3)

These are the coder training slides for my current study of digital activism campaign effectiveness.
Social Media Promotion in 5 Easy Steps

Just like the title says: schedule, listen, connect, mobilize, save the "starter"
Video Advocacy Styles

3 styles of video advocacy (lobbying, vertical campaign, horizontal campaign) prepared for the Health Media Initiative of the Open Society Foundations and presented in Geneva Switzerland June 13th, 2013.
GDADS2 Coder Training Introduction v. 2.0

Used at coding party May 18, 2013 for Global Digital Activism Data Set.
Hybrid Civil Society: How New and Historic Networks Collaborate for Change

Presentation for YMCA national leadership symposium, April 2013
21st Century Civil Society: Implications for Open Government

Presentation for the Open Government Partnership regional meeting in Santiago, Chile, January 2013. The Open Government Partnership is a new multilateral initiative that aims to secure concrete commitments from governments to promote transparency, empower citizens, fight corruption, and harness new technologies to strengthen governance. In the spirit of multi-stakeholder collaboration, OGP is overseen by a steering committee of governments and civil society organizations.
More from Mer Joyce (20)
Contention Beyond Social Movements: Activism and its Benefits

Contention Beyond Social Movements: Activism and its Benefits
Hybrid Civil Society: How New and Historic Networks Collaborate for Change

Hybrid Civil Society: How New and Historic Networks Collaborate for Change
21st Century Civil Society: Implications for Open Government

21st Century Civil Society: Implications for Open Government
Recently uploaded
SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf

Building better applications for business users with SAP Fiori.
• What is SAP Fiori and why it matters to you
• How a better user experience drives measurable business benefits
• How to get started with SAP Fiori today
• How SAP Fiori elements accelerates application development
• How SAP Build Code includes SAP Fiori tools and other generative artificial intelligence capabilities
• How SAP Fiori paves the way for using AI in SAP apps
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

Dr. Sean Tan, Head of Data Science, Changi Airport Group
Discover how Changi Airport Group (CAG) leverages graph technologies and generative AI to revolutionize their search capabilities. This session delves into the unique search needs of CAG’s diverse passengers and customers, showcasing how graph data structures enhance the accuracy and relevance of AI-generated search results, mitigating the risk of “hallucinations” and improving the overall customer journey.
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
GridMate - End to end testing is a critical piece to ensure quality and avoid...

End to end testing is a critical piece to ensure quality and avoid regressions. In this session, we share our journey building an E2E testing pipeline for GridMate components (LWC and Aura) using Cypress, JSForce, FakerJS…
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
National Security Agency - NSA mobile device best practices

Threats to mobile devices are more prevalent and increasing in scope and complexity. Users of mobile devices desire to take full advantage of the features
available on those devices, but many of the features provide convenience and capability but sacrifice security. This best practices guide outlines steps the users can take to better protect personal devices and information.
Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...

The choice of an operating system plays a pivotal role in shaping our computing experience. For decades, Microsoft's Windows has dominated the market, offering a familiar and widely adopted platform for personal and professional use. However, as technological advancements continue to push the boundaries of innovation, alternative operating systems have emerged, challenging the status quo and offering users a fresh perspective on computing.
One such alternative that has garnered significant attention and acclaim is Nitrux Linux 3.5.0, a sleek, powerful, and user-friendly Linux distribution that promises to redefine the way we interact with our devices. With its focus on performance, security, and customization, Nitrux Linux presents a compelling case for those seeking to break free from the constraints of proprietary software and embrace the freedom and flexibility of open-source computing.
Communications Mining Series - Zero to Hero - Session 1

This session provides introduction to UiPath Communication Mining, importance and platform overview. You will acquire a good understand of the phases in Communication Mining as we go over the platform with you. Topics covered:
• Communication Mining Overview
• Why is it important?
• How can it help today’s business and the benefits
• Phases in Communication Mining
• Demo on Platform overview
• Q/A
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
Recently uploaded (20)
SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf

SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
GridMate - End to end testing is a critical piece to ensure quality and avoid...

GridMate - End to end testing is a critical piece to ensure quality and avoid...
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
National Security Agency - NSA mobile device best practices

National Security Agency - NSA mobile device best practices
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...

Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...
Communications Mining Series - Zero to Hero - Session 1

Communications Mining Series - Zero to Hero - Session 1
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
Digital Activism Strategy: The Case of OccupyWishList.org
- 1. DIGITAL ACTIVISM STRATEGY THE CASE OF OCCUPYWISHLIST.ORG Mary Joyce | Columbia University | October 2011 Note: presentation based on public information, I have not spoken directly with MoveOn or #OWS
- 2. 3 STRATEGIC DECISIONS Goal What the organization wants to achieve
- 3. 3 STRATEGIC DECISIONS Goal What the organization wants to achieve •an older organization •did not start #OWS but shares goals •hopes to support #OWS and benefit itself
- 4. 3 STRATEGIC DECISIONS 1. support #OWS 2. benefit MoveOn Goal What the organization wants to achieve
- 5. 3 STRATEGIC DECISIONS 1. support #OWS 2. benefit MoveOn Assets Goal What the What assets can the organization organization work wants to with to help it achieve achieve its goal?
- 6. 3 STRATEGIC DECISIONS External Internal Allies Resources Review Human and Material Assets
- 7. 3 STRATEGIC DECISIONS External Internal Allies Resources #OWS supporters coders #OWS occupiers developers MoveOn supporters social media presence Review Human and Material Assets
- 8. 3 STRATEGIC DECISIONS 1. support #OWS 1. sympathizers (donors) 2. benefit MoveOn 2. occupiers (recipients) 3. coders Goal Assets What the What assets can the organization organization work wants to with to help it achieve achieve its goal?
- 9. 3 STRATEGIC DECISIONS 1. support #OWS 1. sympathizers (donors) 2. benefit MoveOn 2. occupiers (recipients) 3. coders Goal Assets Action What the organization What assets can How can the wants to the organization organization best achieve work with to help use its assets to it achieve its goal? achieve its goal? Specific Measurable Achievable Realistic Timely
- 10. 3 STRATEGIC DECISIONS Time/ Resources Ally Org’s Media Media Attention Access Best Media Action
- 11. 3 STRATEGIC DECISIONS Resources coders and developers Twitter Attention Access sites,Twitter, FB
- 12. 3 STRATEGIC DECISIONS Resources coders and developers Twitter Attention Access sites,Twitter, FB Action: Build custom site to crowdsource supplies for #OWS and collect email addresses, promote on Twitter
- 13. 3 STRATEGIC DECISIONS 1. support #OWS 1. sympathizers (donors) Occupy Wish List 2. benefit MoveOn 2.occupiers (recipients) website 3. coders Goal Assets Action What the What assets can the organization How can the organization work organization use wants to with to help it achieve its assets to achieve its goal? achieve its goal?
- 14. 3 STRATEGIC DECISIONS 1. support #OWS 1. sympathizers (donors) Occupy Wish List 2. benefit MoveOn 2.occupiers (recipients) website 3. coders Goal Assets Action Implement What the What assets can the organization How can the organization work organization use wants to with to help it achieve its assets to achieve its goal? achieve its goal?
- 15. IMPLEMENTATION BUILDING THE SITE
- 16. IMPLEMENTATION BUILDING THE SITE
- 18. THE BACKLASH KNOW YOUR ALLIES
- 19. THE BACKLASH KNOW YOUR ALLIES HTTP://WWW.RITHOLTZ.COM/BLOG/2011/10/MOVE-ON-TRIES-TO-CO-OPT-THE-PROTESTS/
- 20. EVALUATION IS OCCUPY WISH LIST A SUCCESS? only 5 new items, 2 new donors, and 2 new occupy sites added all day (Oct. 26)
- 21. STRATEGIC LESSONS Goal Assets Action 1. MoveOn had a clear strategic process (matching goal to digital action). 2. Their implementation (site construction and promotion) was strong. 3. They just didn’t understand their allies well enough. They forgot the fierce independence of #OWS. 4.This misjudgment was a critical blow to their digital activism tactic.