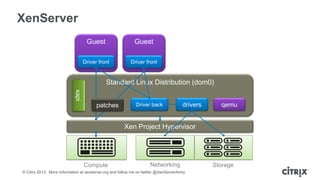
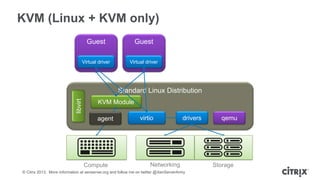
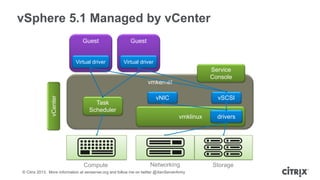
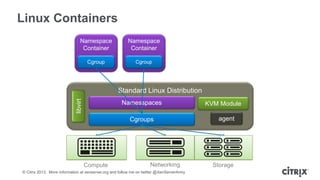
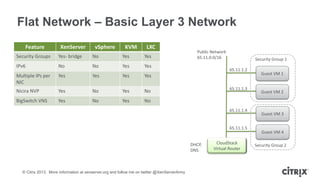
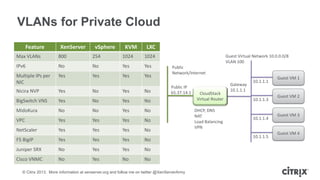
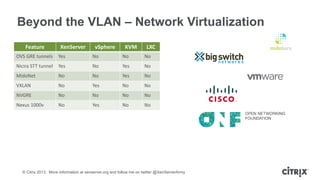
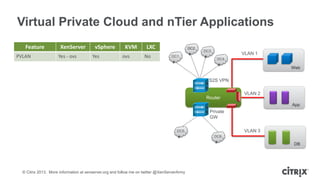
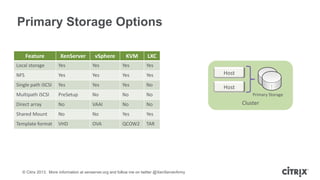
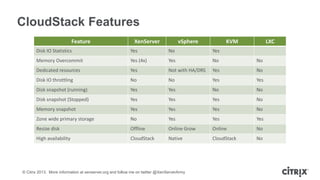
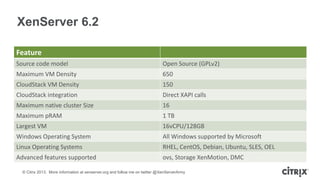
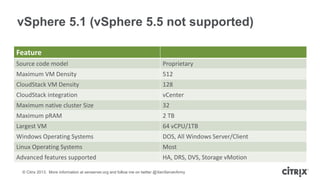
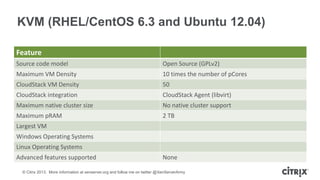
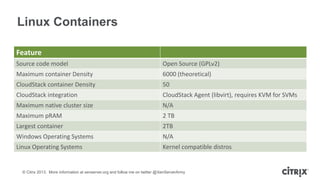
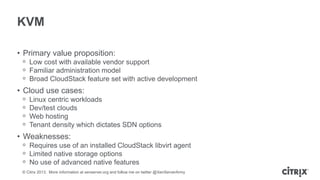
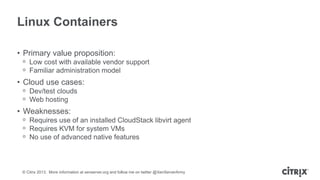
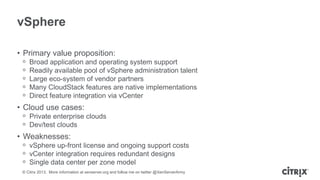
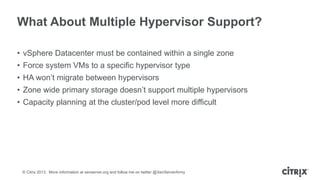
The document discusses hypervisor selection for cloud environments, emphasizing the importance of clearly defining service offerings, compliance, and availability expectations. It compares various hypervisors—XenServer, KVM, vSphere, and Linux containers—highlighting their strengths, weaknesses, and specific use cases while addressing storage, networking, and virtualization capabilities. The presentation aims to guide organizations in choosing the right hypervisor based on operational needs and resource management requirements.