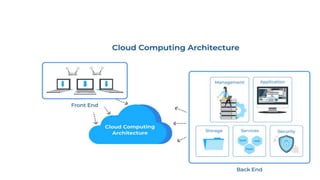
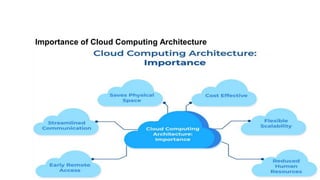
The document provides an overview of cloud computing architecture, highlighting its components including front-end and back-end services, along with management, application, storage, services, and security aspects. It discusses the importance of cloud computing, emphasizing benefits such as space savings, streamlined communication, remote access, reduced human resources, and cost-effectiveness. Finally, it offers tips for businesses transitioning to cloud computing, stressing the need for careful planning, employee training, and regular security checks.