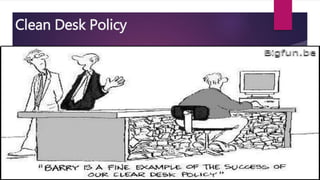
The document outlines a clean desk policy which requires employees to clear their desks of all papers and sensitive information at the end of the day. It discusses how clean desk policies are increasingly motivated by information security regulations to protect sensitive data from unauthorized access. Desks should be cleared of papers with sensitive information like account numbers to reduce the risk of a data breach. Implementing and enforcing a clear clean desk policy with disciplinary actions for non-compliance helps create a secure work environment and positive company image.