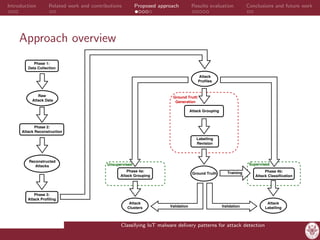
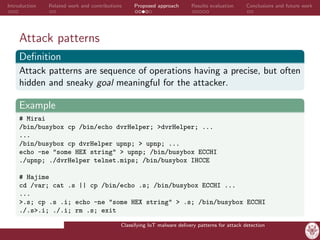
The document presents a master's thesis focused on classifying IoT malware delivery patterns to enhance attack detection. It highlights the vulnerabilities of IoT devices, the proliferation of malware, and proposes a platform that leverages real attack data for recognizing and classifying various attack types. The findings emphasize the effectiveness of the proposed approach in profiling and grouping attacks, along with recommendations for future work in improving detection and data organization.



![Introduction Related work and contributions Proposed approach Results evaluation Conclusions and future work
Related work
Works in the IoT security field divides into:
• Studies providing basic security guidelines for preventing,
mitigating and recovery from attacks.
[Angrishi et al., 2017]
• Proposing honeypot systems designed for the IoT environment,
with the goal of assessing the current threats.
[SIPHON, Guarnizo et al., 2017]
• Designing detection strategies, employing either simple device
white-listing mechanism or unreliable signature-based approaches.
[Meidan et al., 2017]
• Proposing proof-of-concept mechanism for detecting infected
devices and automatize the recovery strategy.
[AntibIoTic, De Donno et al., 2017]
Classifying IoT malware delivery patterns for attack detection](https://image.slidesharecdn.com/masterthesispresentation-180204162825/85/Classifying-IoT-malware-delivery-patterns-for-attack-detection-5-320.jpg)