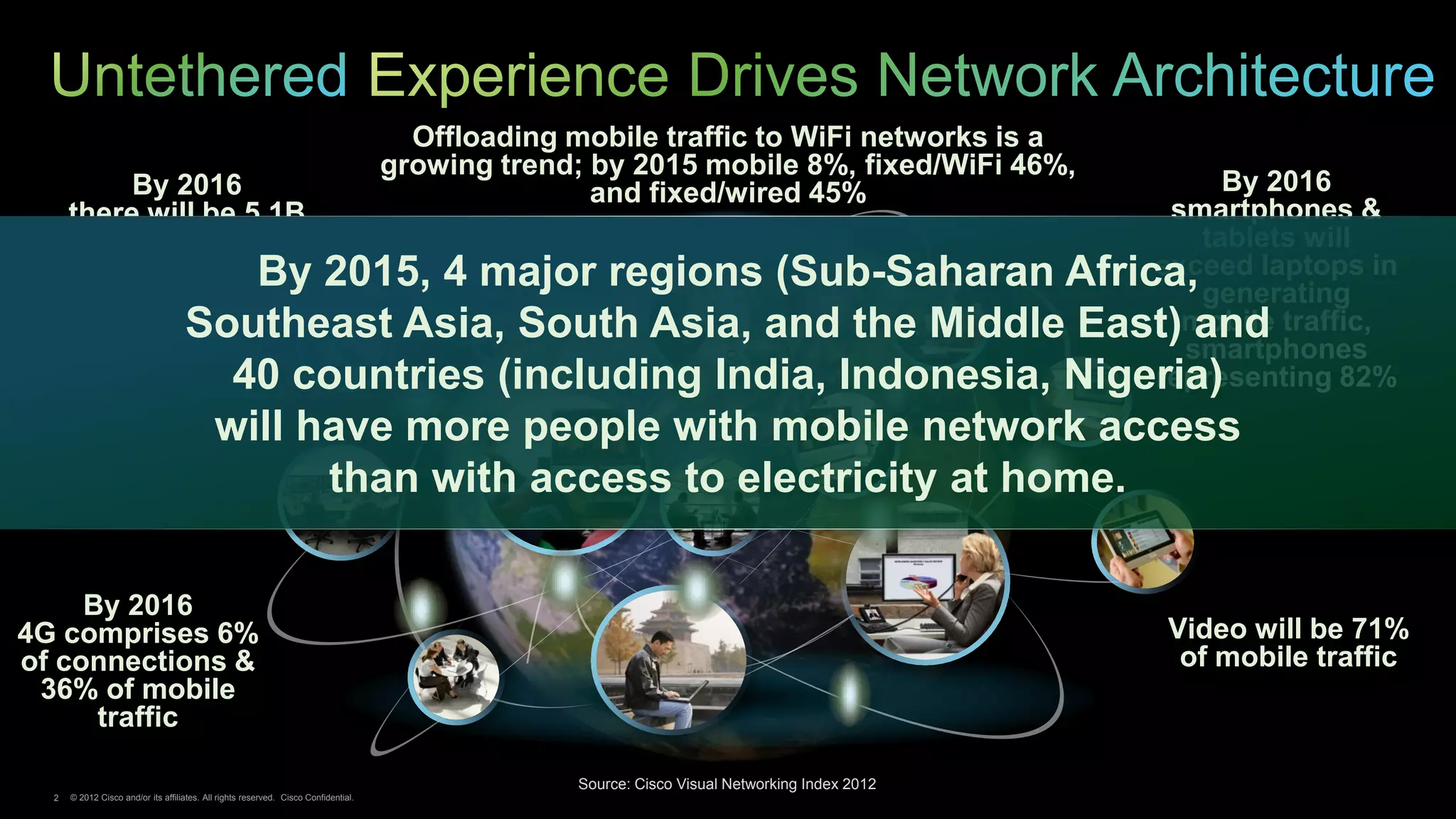
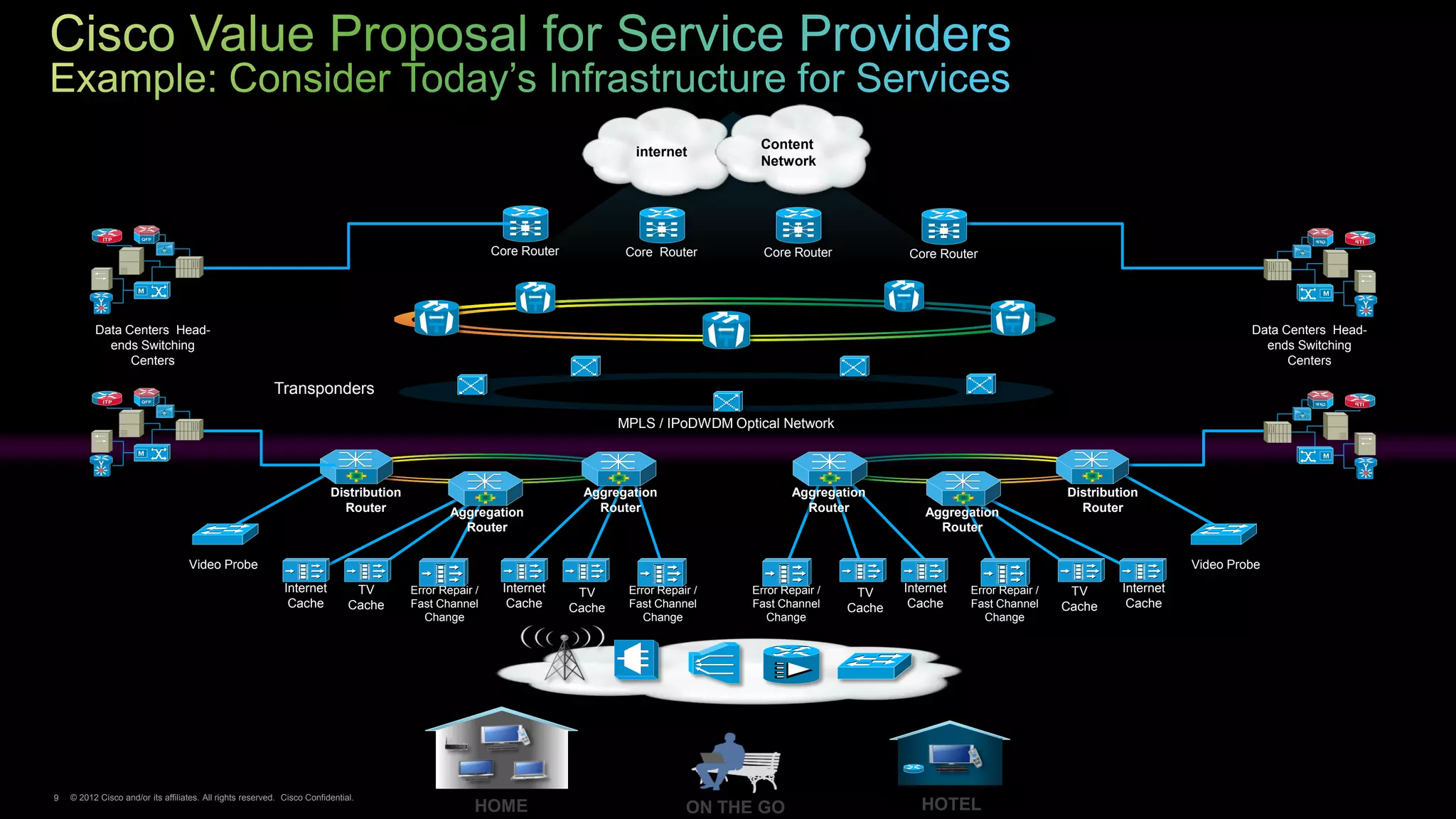
- Mobile data traffic is growing exponentially and will exceed fixed network traffic by 2015. By 2016, video will comprise 71% of mobile traffic.
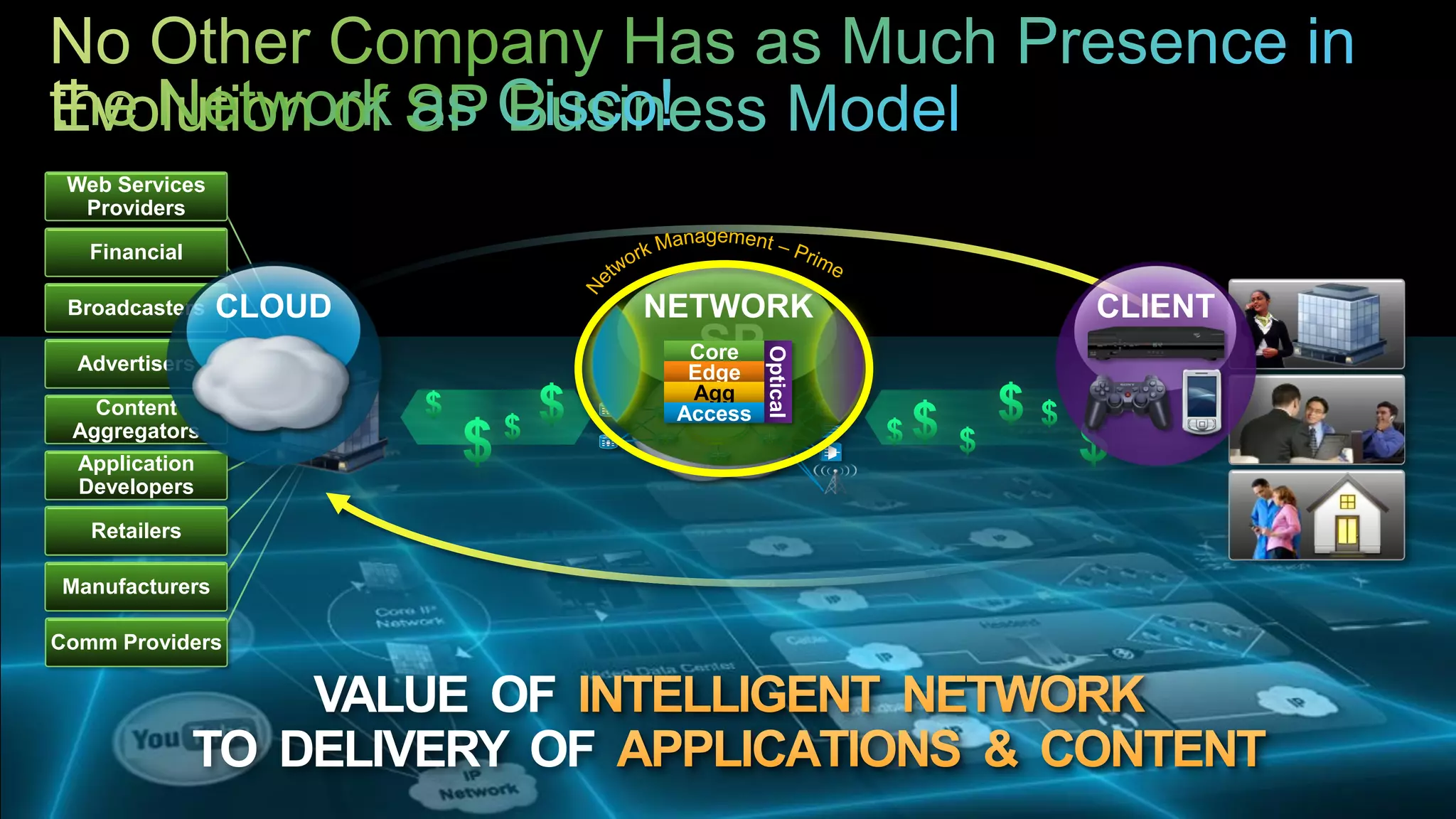
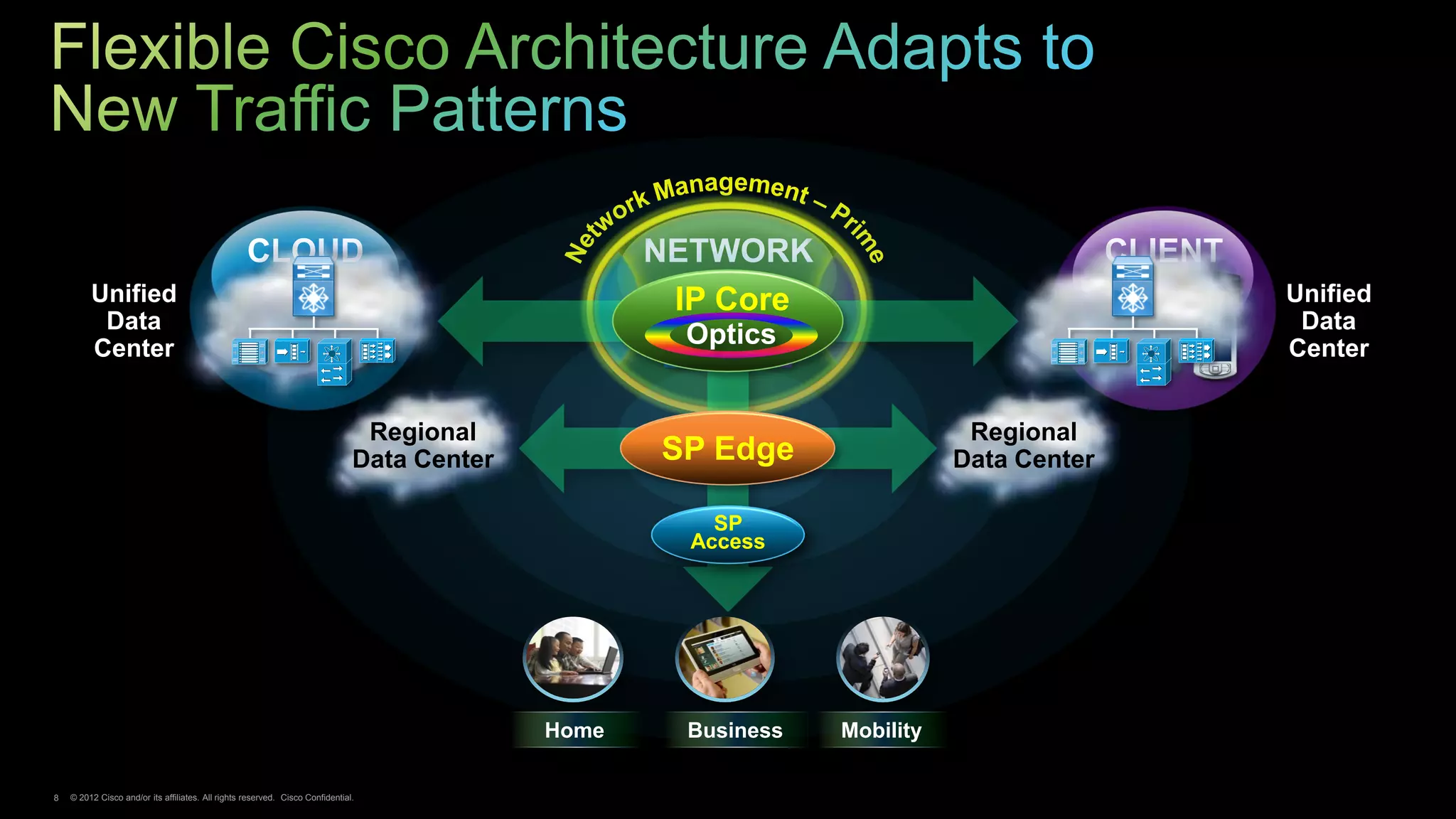
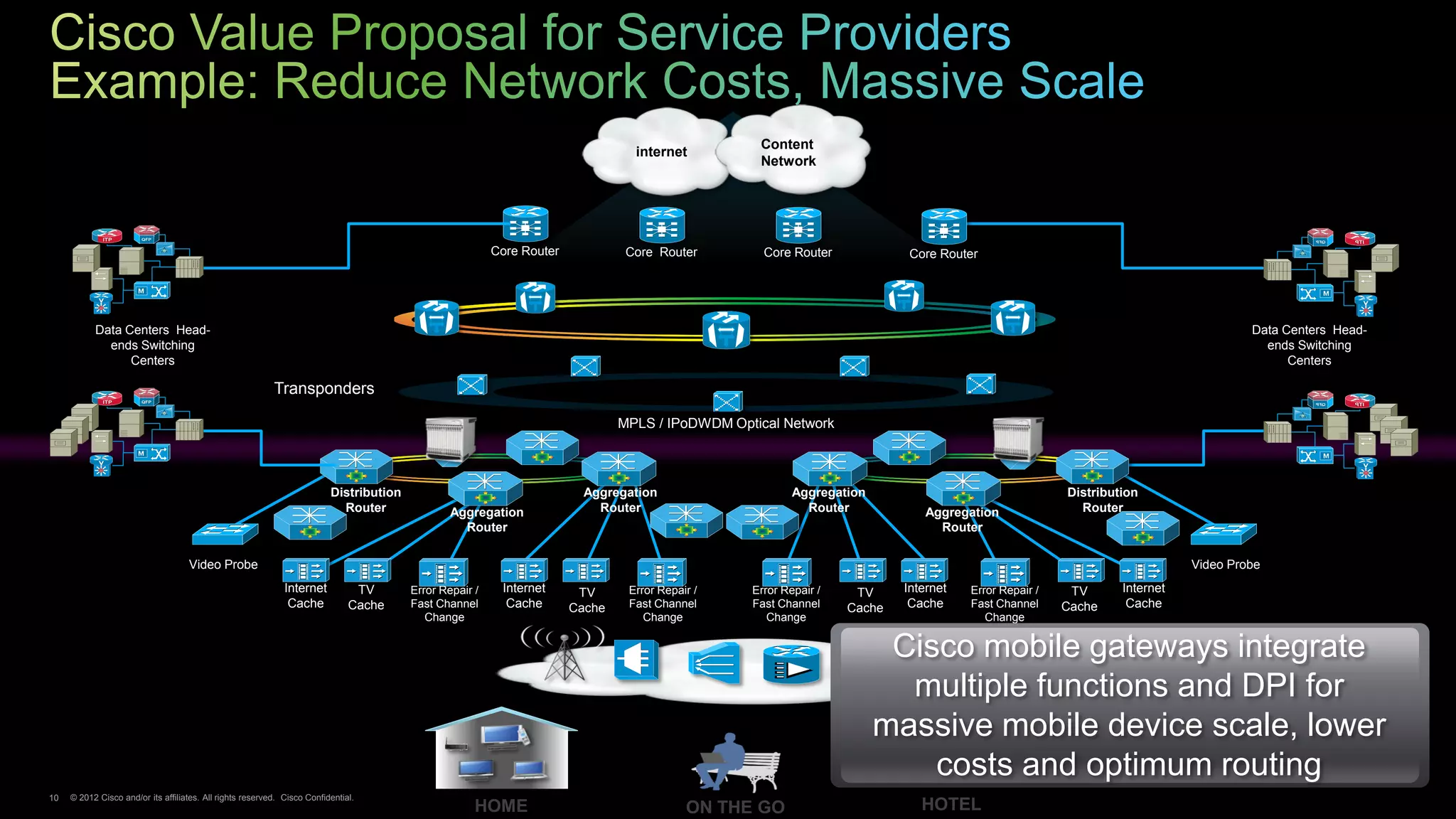
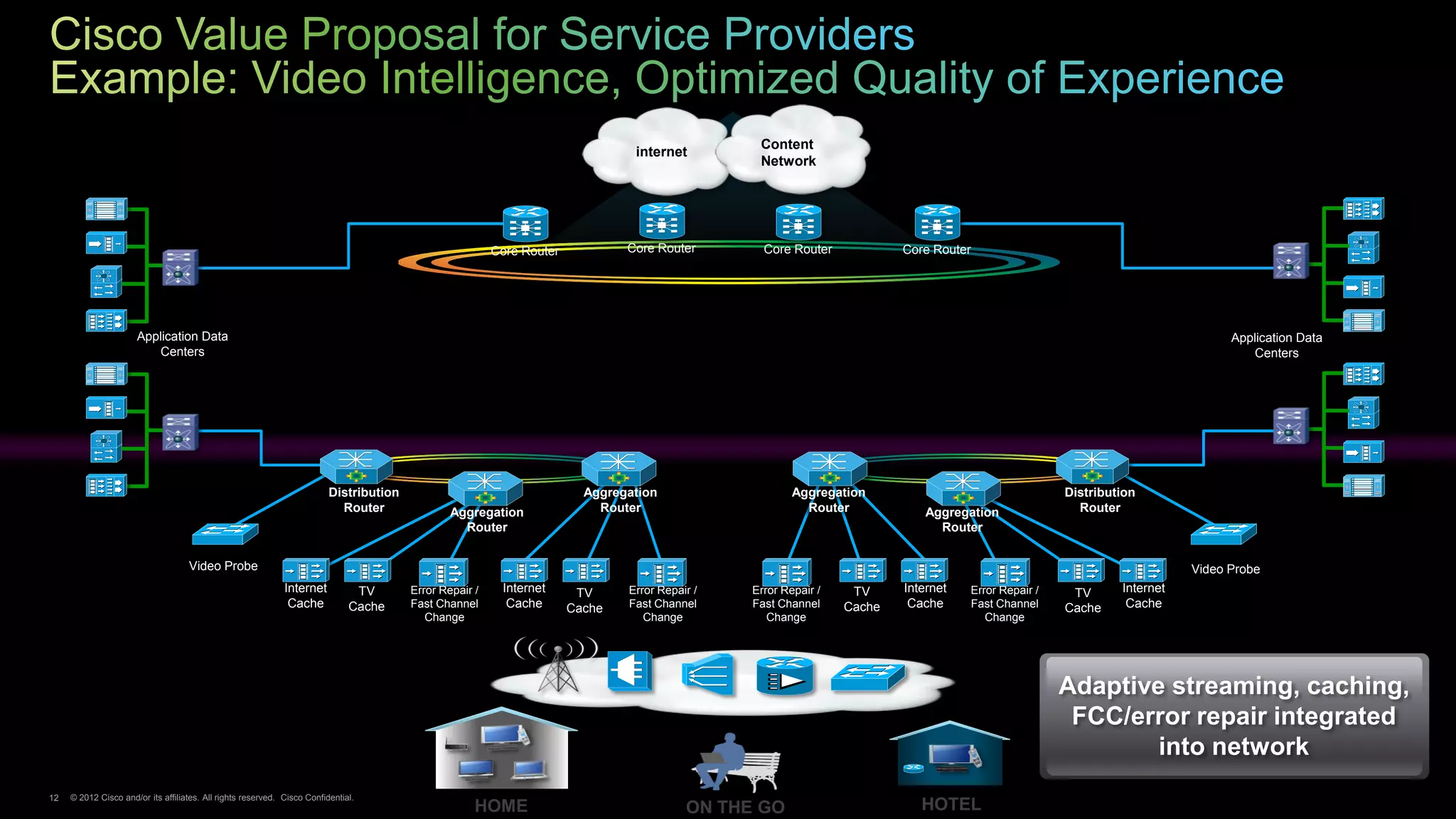
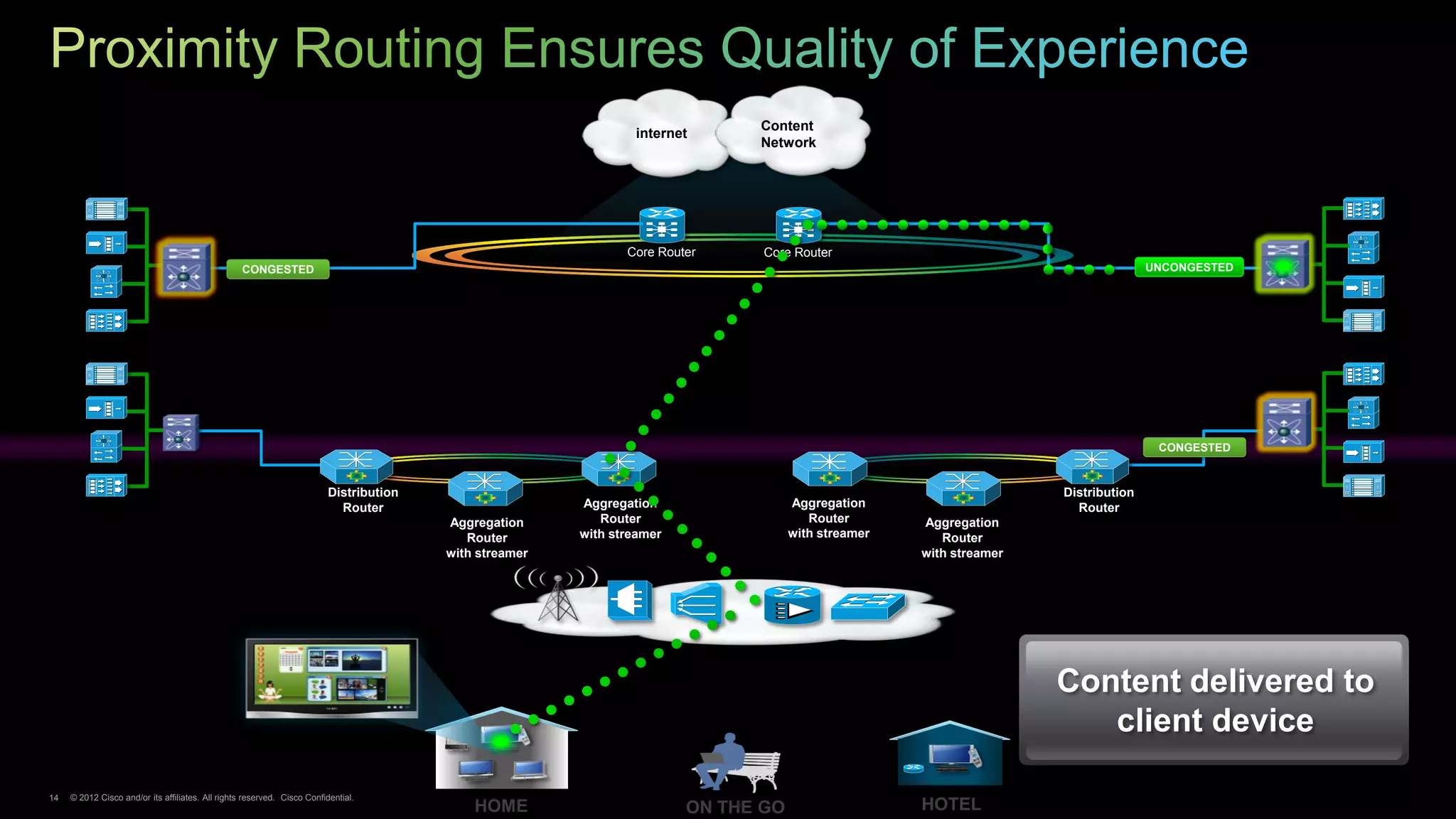
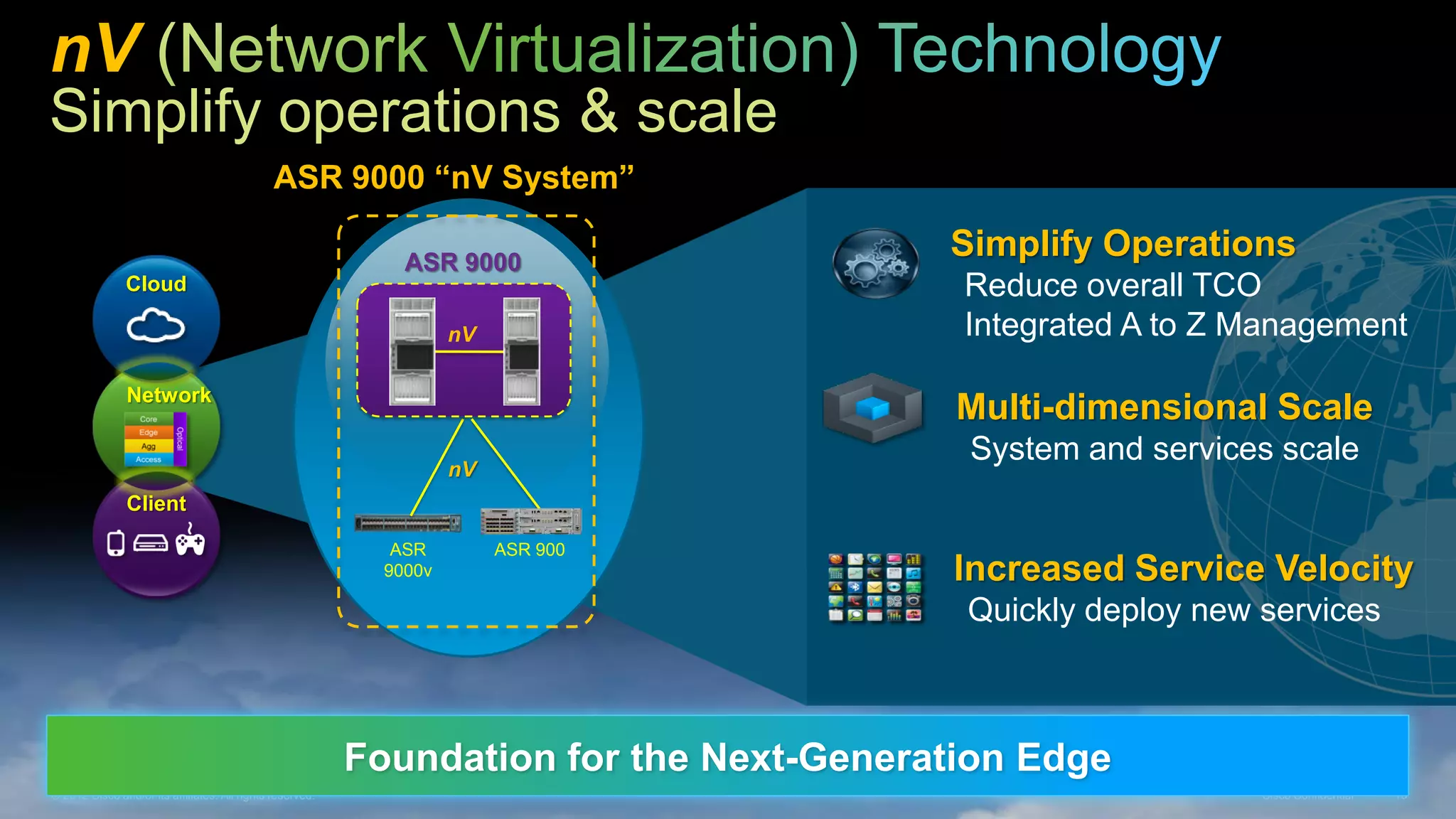
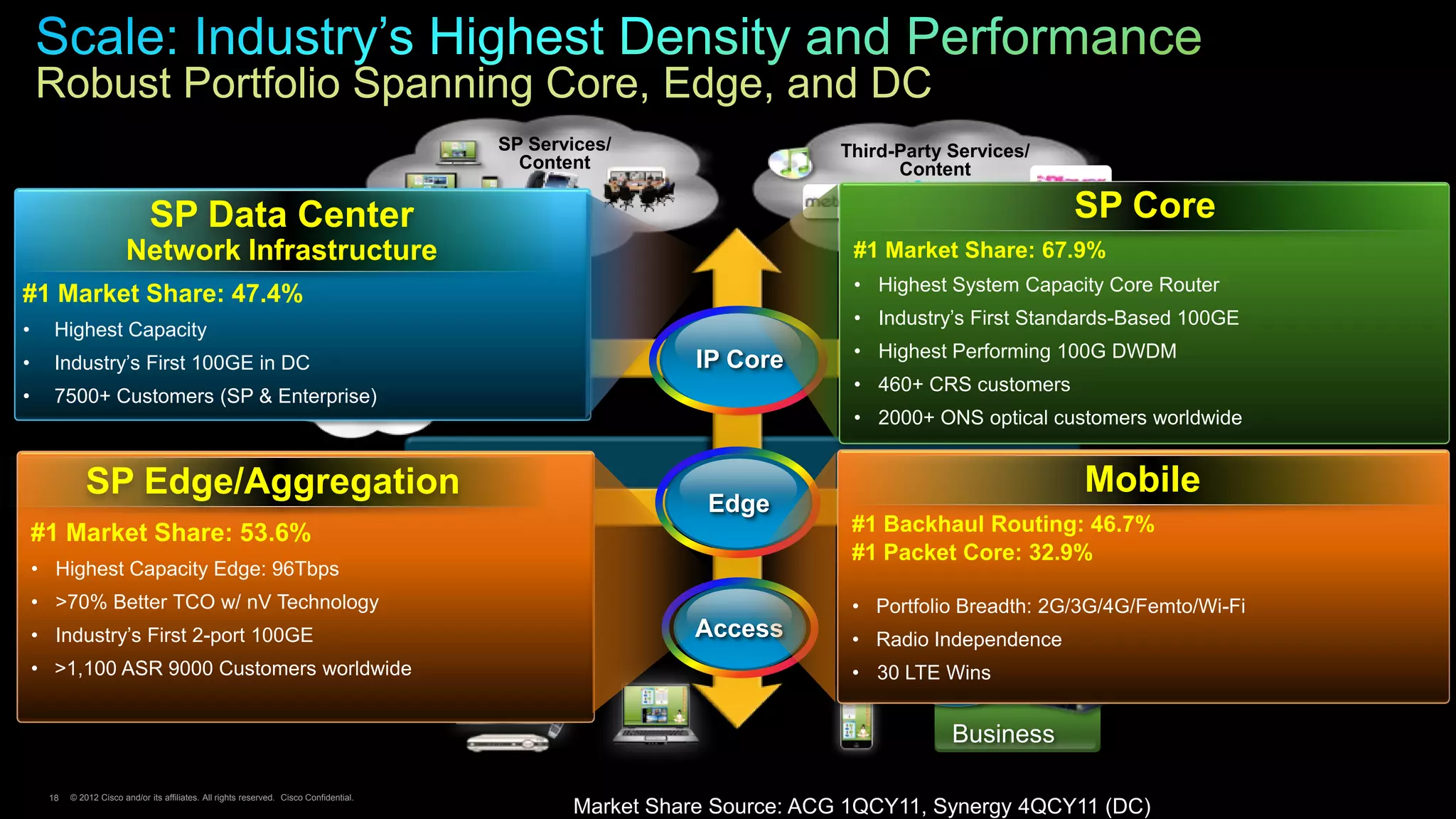
- The network must scale to support this traffic explosion while enabling new business models and services through intelligence in the network.
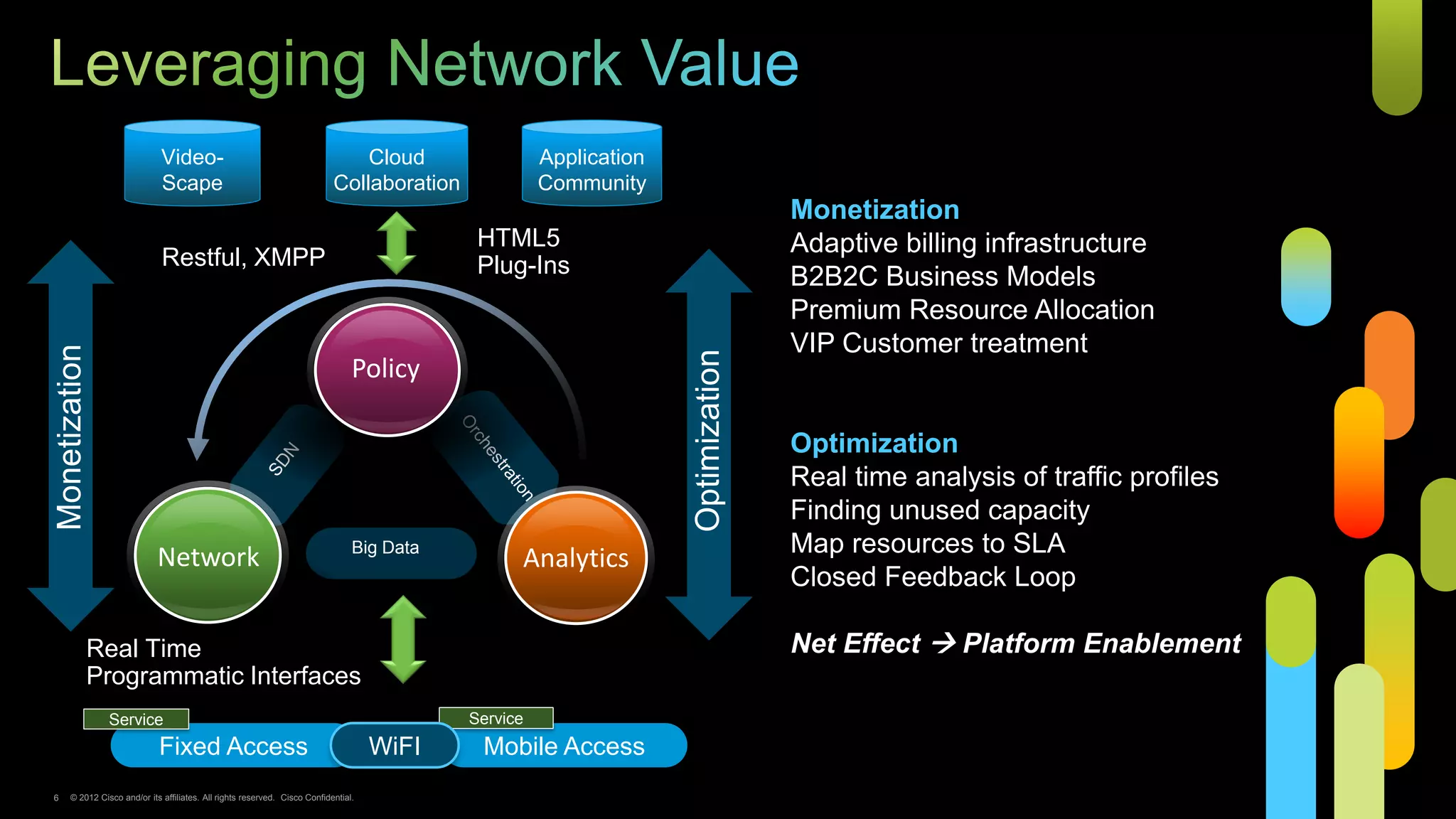
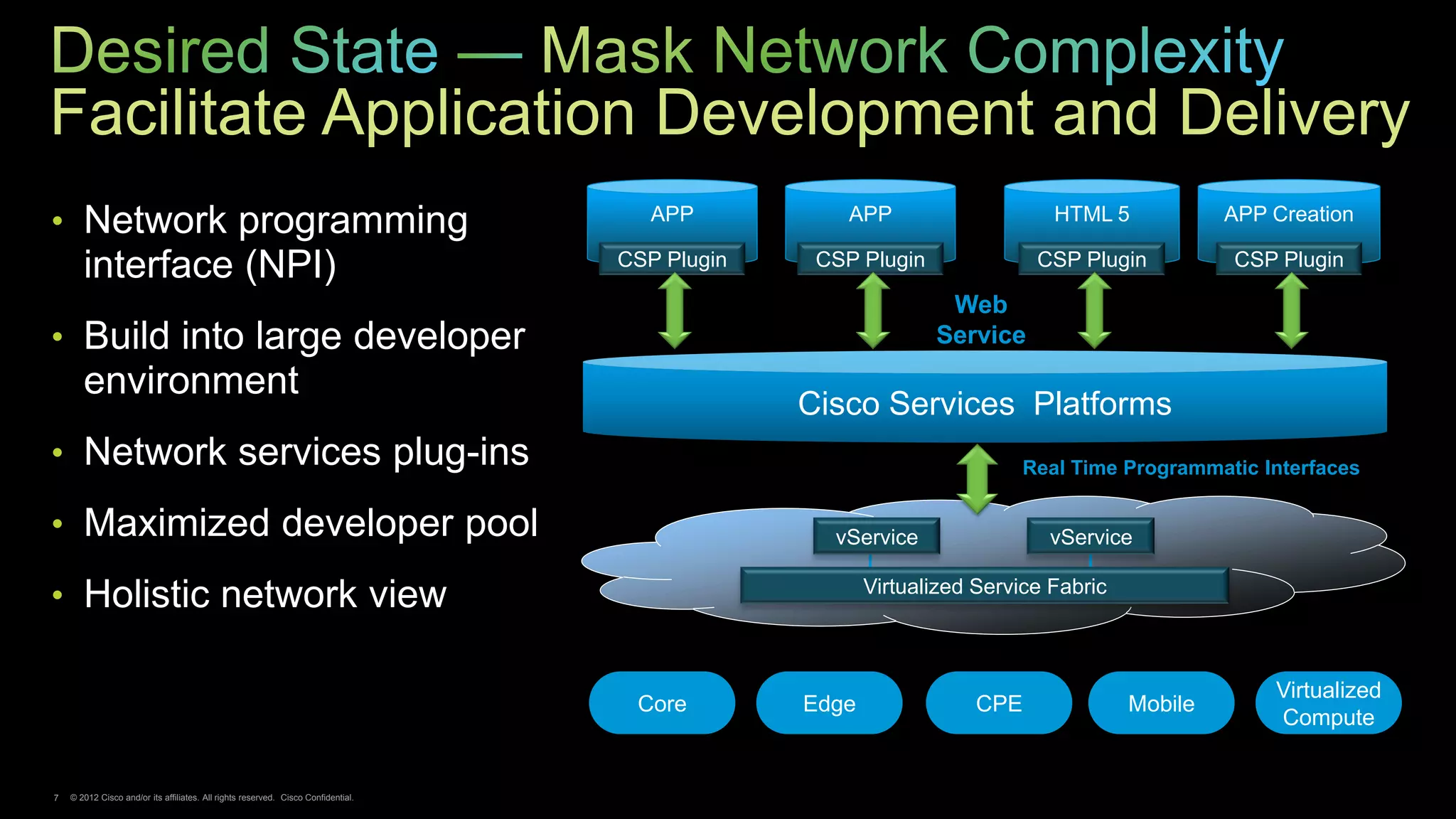
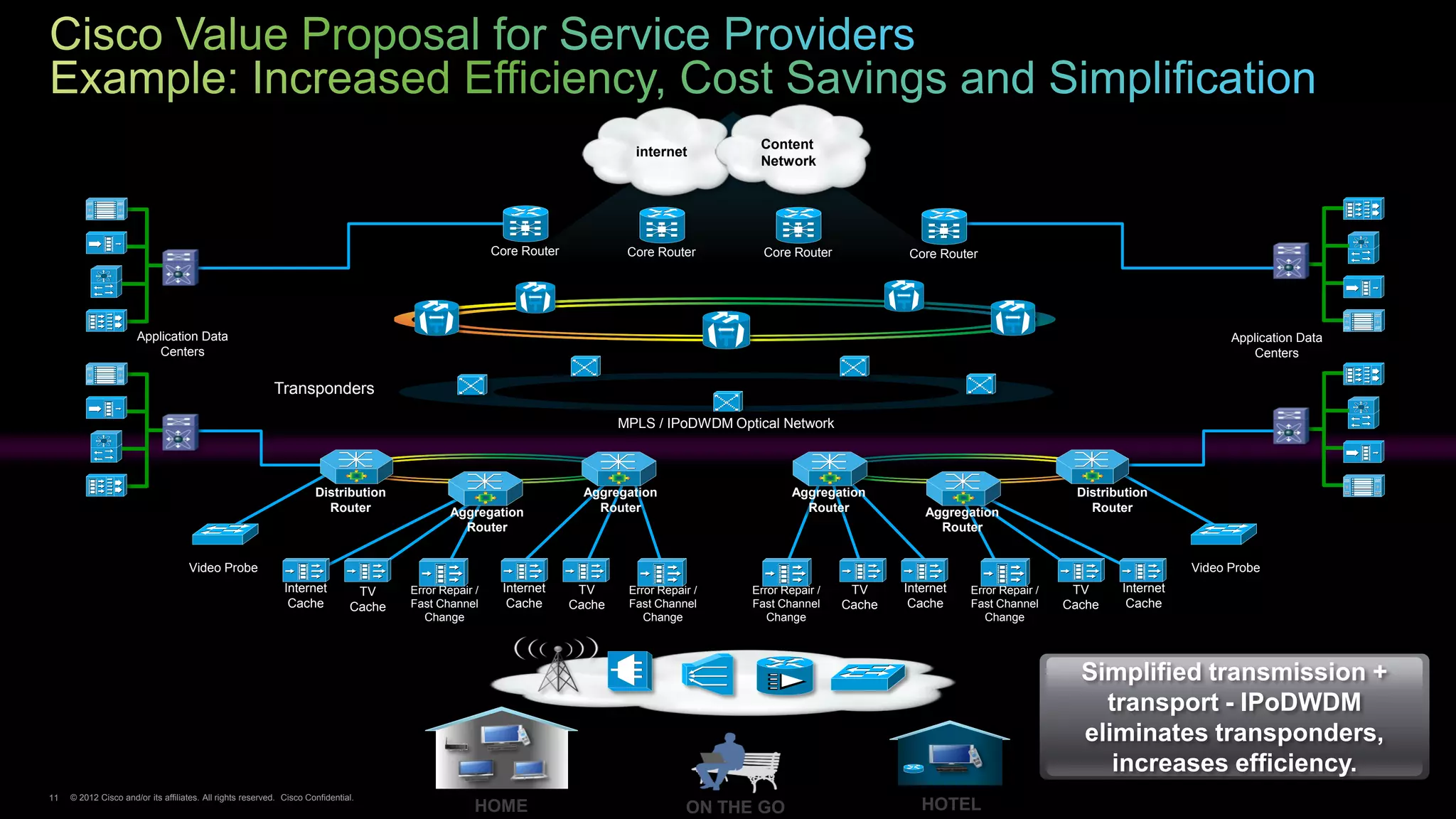
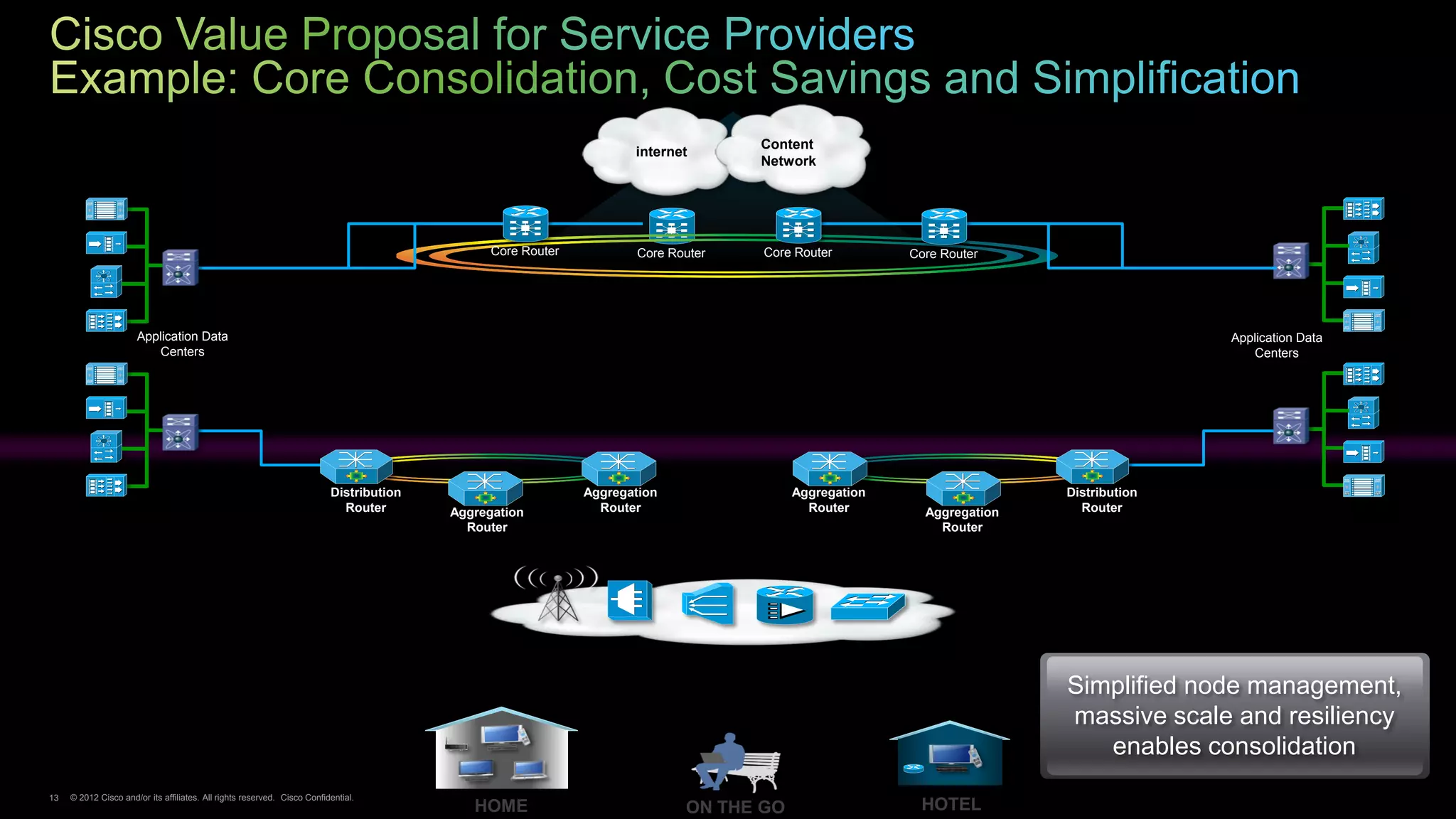
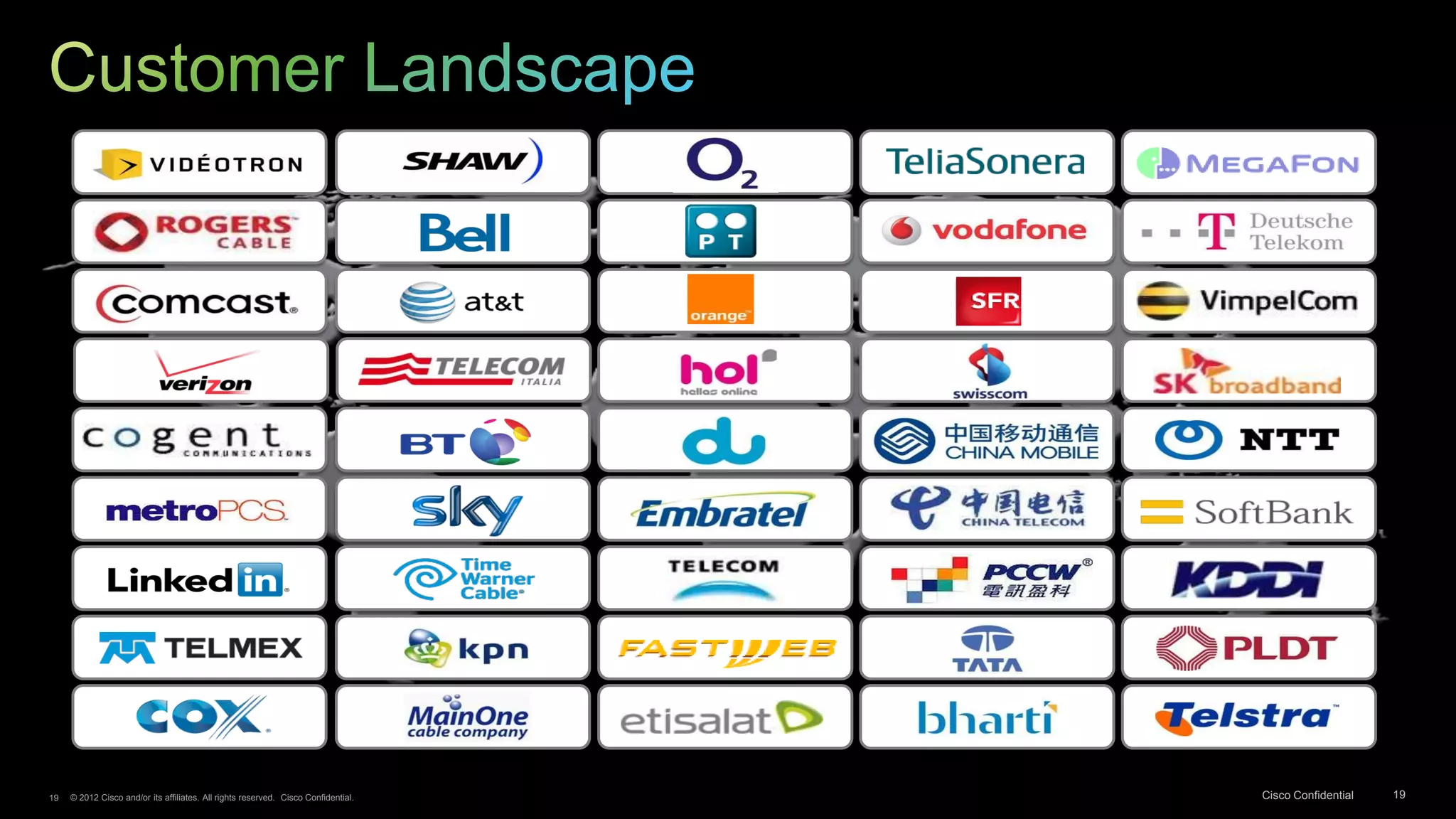
- Cisco's strategy is to simplify the network architecture, enable applications and services delivery through cloud platforms, and optimize the network through analytics and policy to facilitate new monetization approaches.