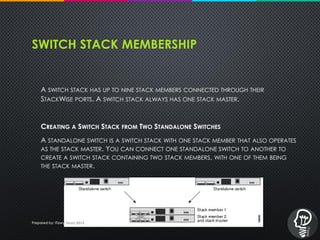
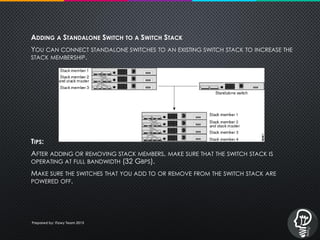
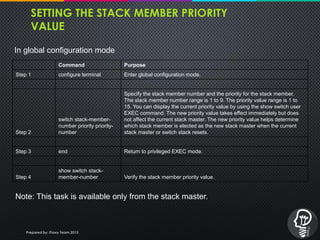
The document provides an overview of Cisco StackWise technology and its components, particularly focusing on switch stacks made up of Catalyst 3750 switches. Key aspects include the role of the stack master, the management of stack members through a unified system, and the process of assigning stack member numbers and priority values. Additionally, it addresses stack management connectivity and configuration guidelines to facilitate effective network operations.
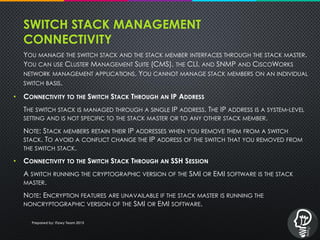
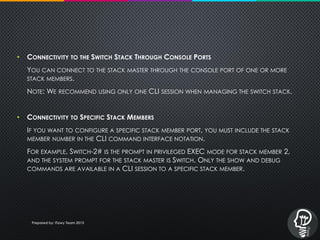
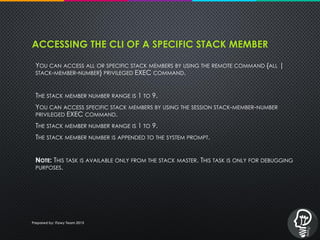
![FOR EXAMPLE:
WNISW01#SESSION ?
<1-9> SWITCH NUMBER
WNISW01#SESSION 3
WNISW01-3#SH VER
WNISW01-3 UPTIME IS 9 WEEKS, 3 DAYS, 20 HOURS, 7 MINUTES
SYSTEM RETURNED TO ROM BY POWER-ON
SYSTEM RESTARTED AT 12:53:52 NZDT SUN DEC 14 2008
SYSTEM IMAGE FILE IS "FLASH:/C3750-IPBASEK9-MZ.122-44.SE.BIN"
WNISW01-3#CONF T
^
% INVALID INPUT DETECTED AT '^' MARKER.
WNISW01-3# EXIT / Q [ COMMAND TO COME OUT FROM THE MEMBER MODE TO STACK MASTER ]
• WNISW01#
NOTE: ONLY THE SHOW AND DEBUG COMMANDS ARE AVAILABLE IN A CLI SESSION TO A SPECIFIC STACK MEMBER.
Prepared by: iTawy Team 2015](https://image.slidesharecdn.com/ciscostackwisetechnology-151109151413-lva1-app6891/85/Cisco-stack-wise-technology-17-320.jpg)