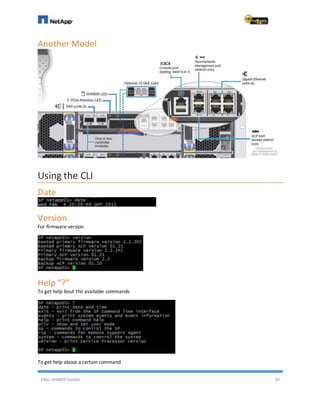
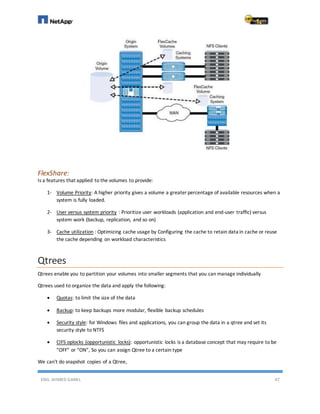
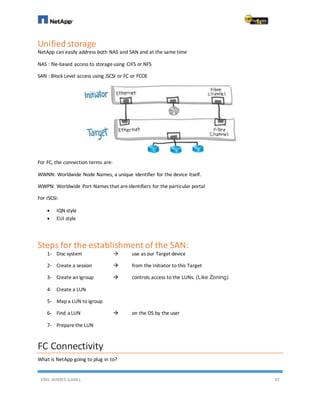
This document provides an overview of data storage concepts and NetApp technologies. It begins with an introduction to different storage solutions like disks, disk arrays, and intelligent storage systems. It then covers storage types including DAS, NAS, and SAN. The document discusses virtualization, data networks, and protocols like SCSI, iSCSI, SAS, and Fibre Channel. It provides details on flash storage, solid state technologies, and flash endurance. The remainder covers NetApp products, technologies, and configuration topics.