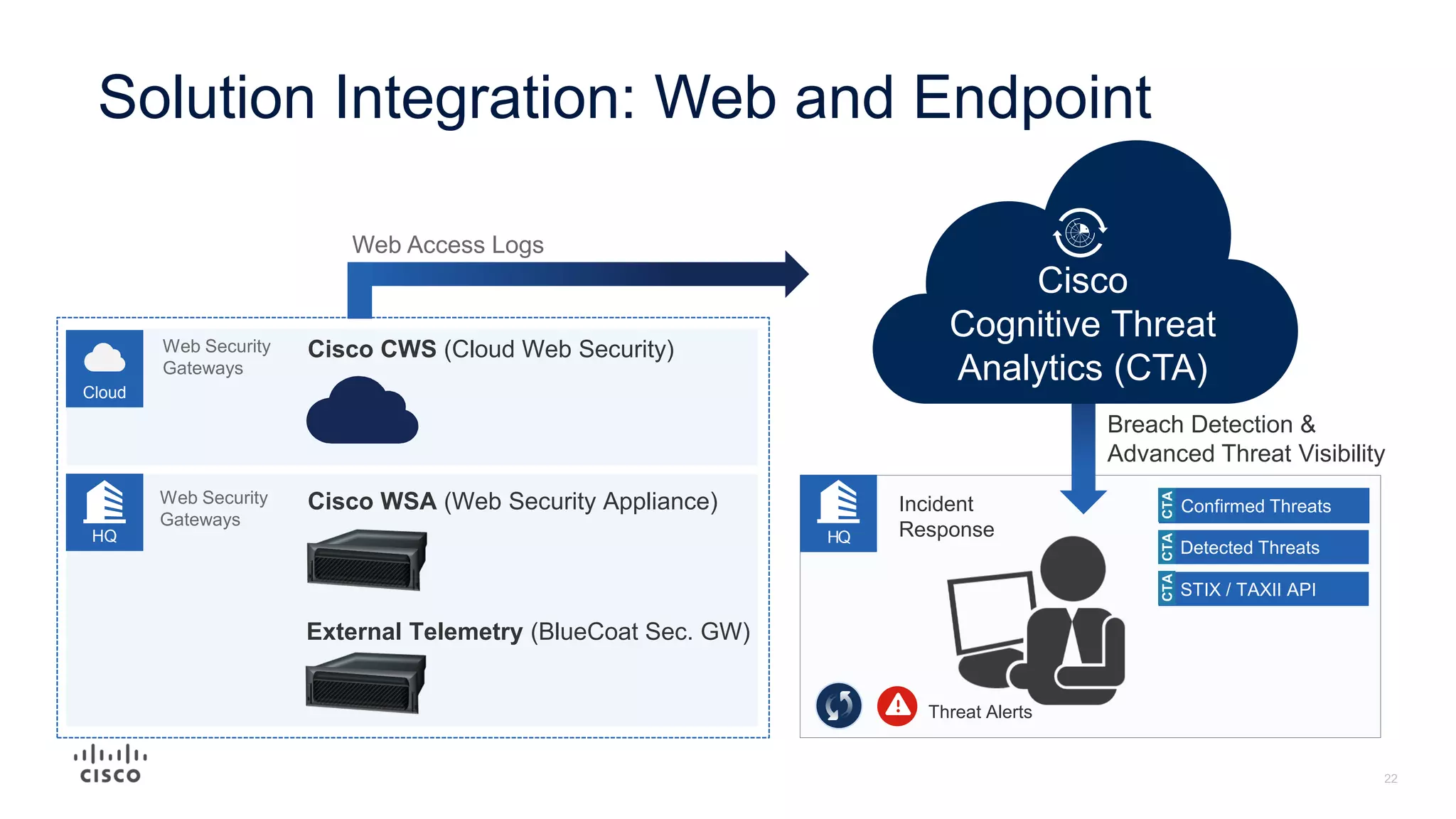
The document discusses the need for an integrated security architecture approach rather than relying on individual security products. It outlines how integration across the Cisco security portfolio provides functional integration through shared threat intelligence, event information, automated policy changes, and contextual awareness. Examples are given of how integration allows for rapid threat containment, sharing of events and policy, leveraging threat intelligence across the environment, and profiling of users and devices on the network. The document advocates for an approach that is simple, open, and automated through integration.