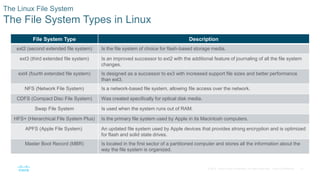
Linux is an open source operating system first created in 1991. It is maintained by a community of programmers and comes in various distributions like CentOS and Fedora. Some distributions are free while others like Red Hat Enterprise Server require payment but include support services. Linux is widely used as the operating system of choice in security operations centers due to its security, customizability, and powerful command line interface.