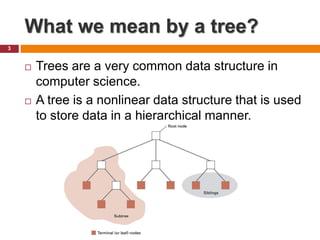
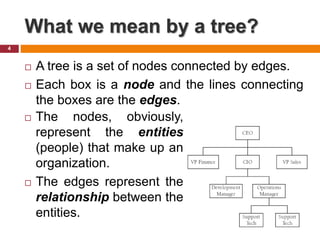
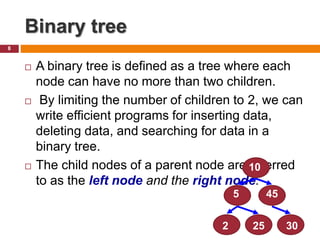
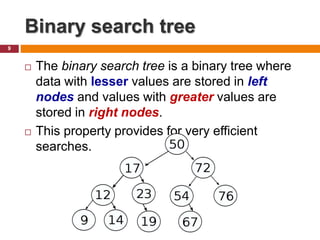
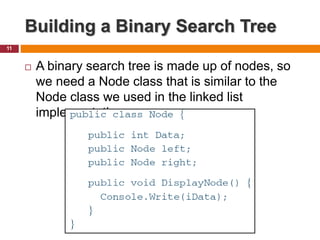
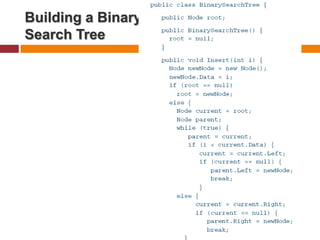
The document discusses trees and binary trees as data structures. It defines what a tree is, including parts like the root, parent, child, leaf nodes. It then defines binary trees as trees where each node has no more than two children. Binary search trees are introduced as binary trees where all left descendants of a node are less than or equal to the node and all right descendants are greater. The document concludes by discussing how to build a binary search tree class with Node objects.