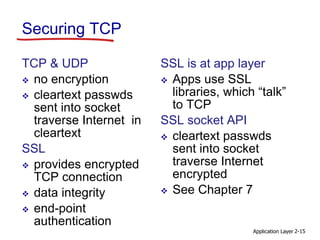
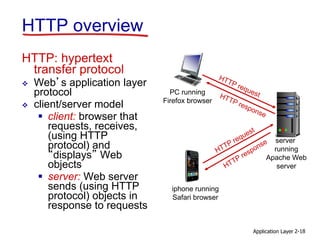
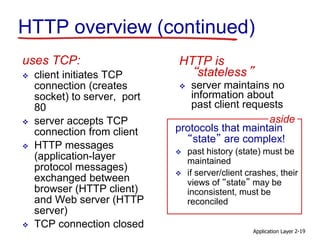
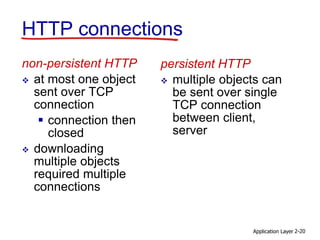
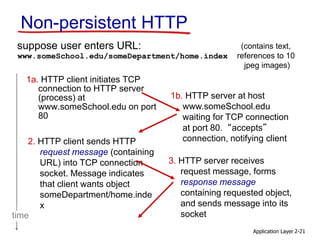
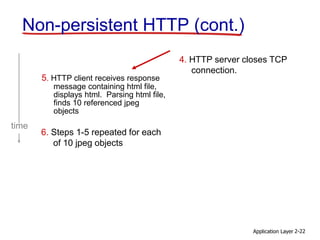
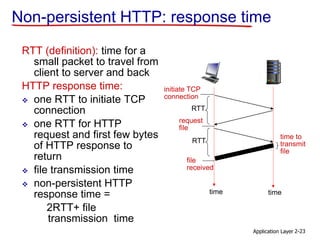
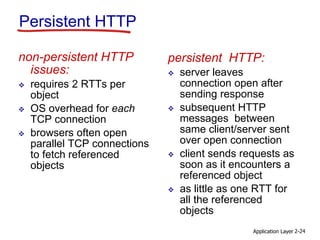
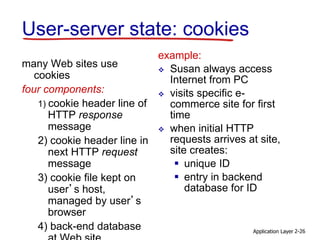
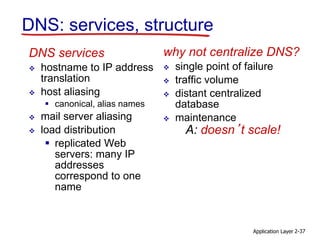
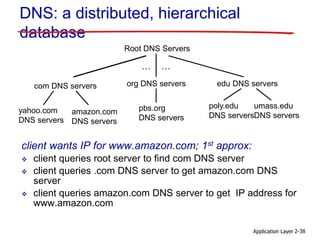
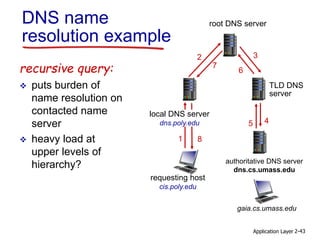
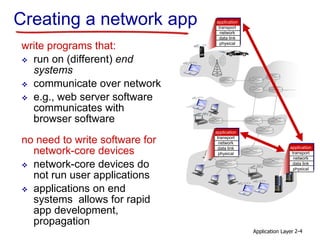
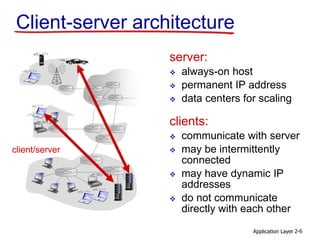
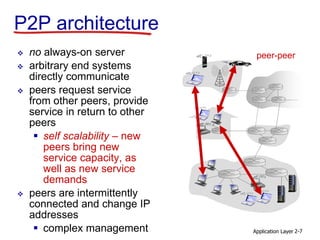
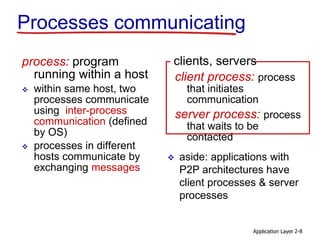
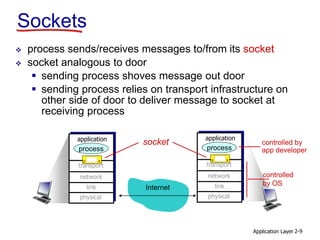
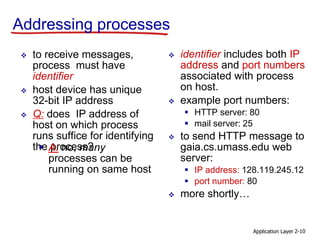
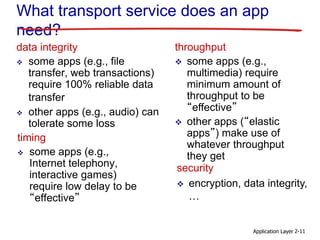
The document discusses the application layer and network applications. It covers key concepts like application architectures (client-server and peer-to-peer), application requirements, and protocols like HTTP, FTP, and email. It specifically describes HTTP and how it uses TCP for reliable data transfer between clients and servers. It compares non-persistent and persistent HTTP connections, noting that persistent connections allow referenced objects to be fetched with just one round-trip time instead of multiple connections. The goal is to conceptually and practically cover important application layer protocols and how network applications are built.

![Application Layer 2-14
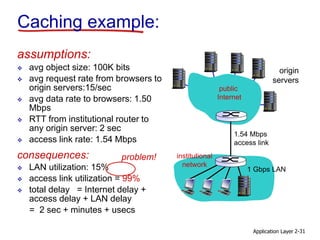
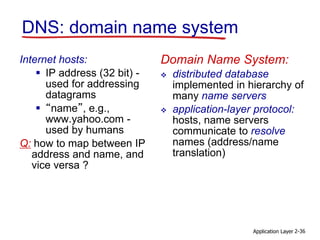
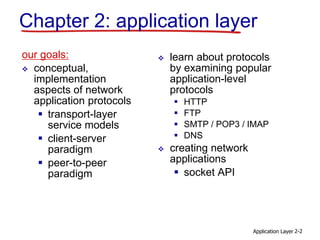
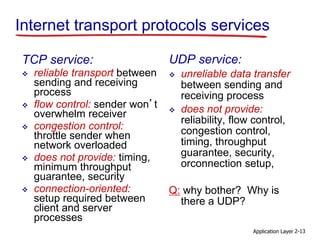
Internet apps: application, transport protocols
application
e-mail
remote terminal access
Web
file transfer
streaming multimedia
Internet telephony
application
layer protocol
SMTP [RFC 2821]
Telnet [RFC 854]
HTTP [RFC 2616]
FTP [RFC 959]
HTTP (e.g., YouTube),
RTP [RFC 1889]
SIP, RTP, proprietary
(e.g., Skype)
underlying
transport protocol
TCP
TCP
TCP
TCP
TCP or UDP
TCP or UDP](https://image.slidesharecdn.com/2-appl2-200414170951/85/Ch2-application-layer-Network-14-320.jpg)