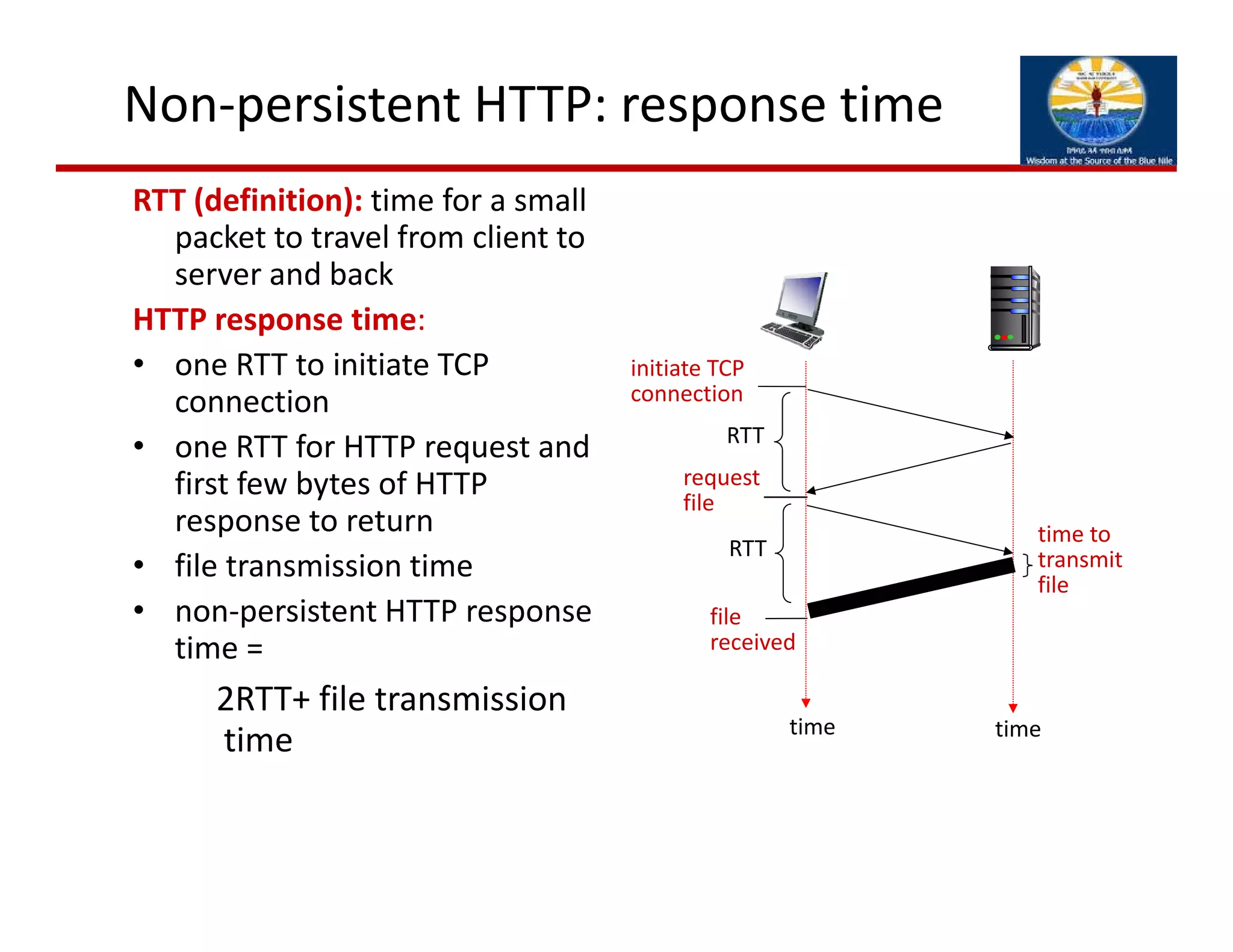
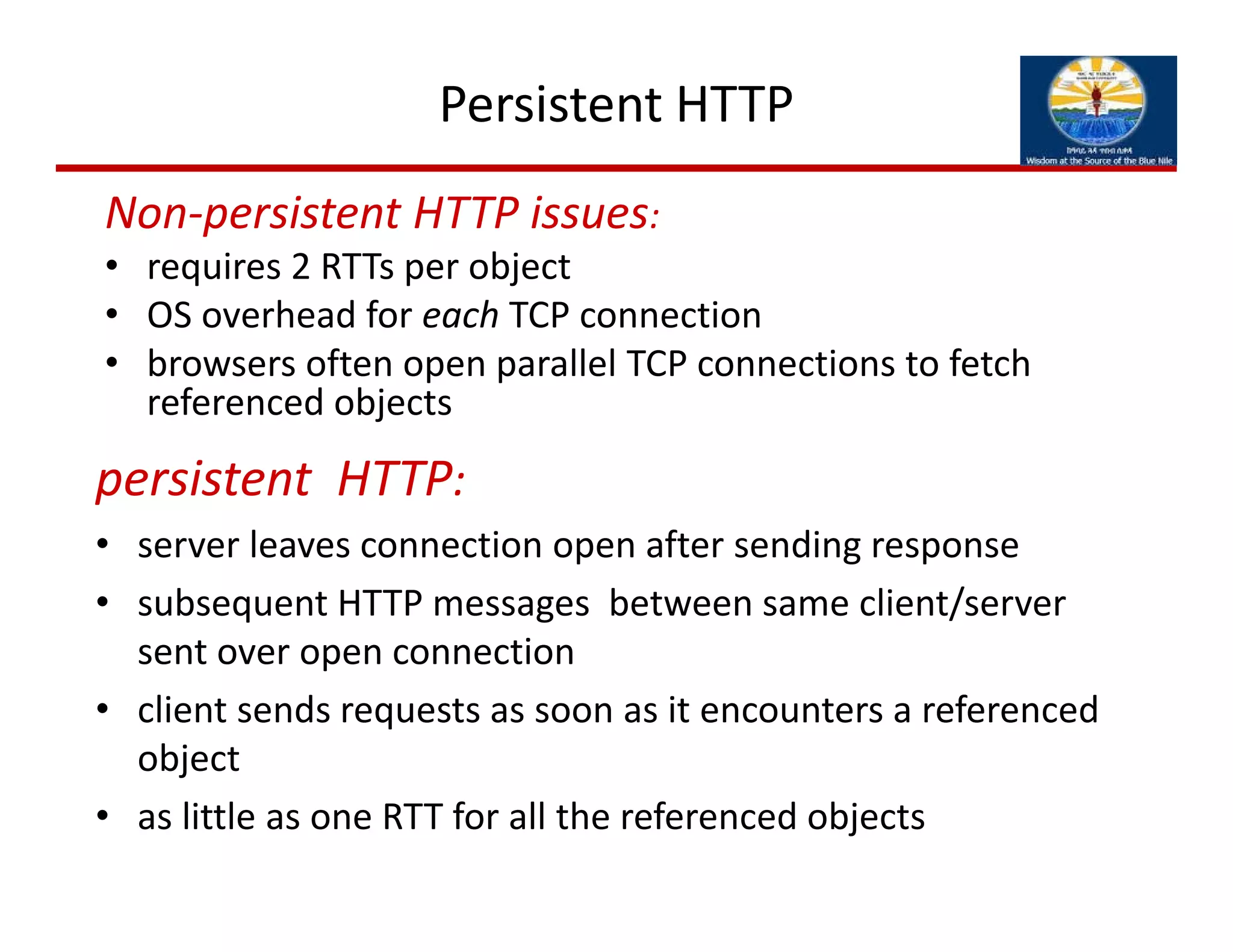
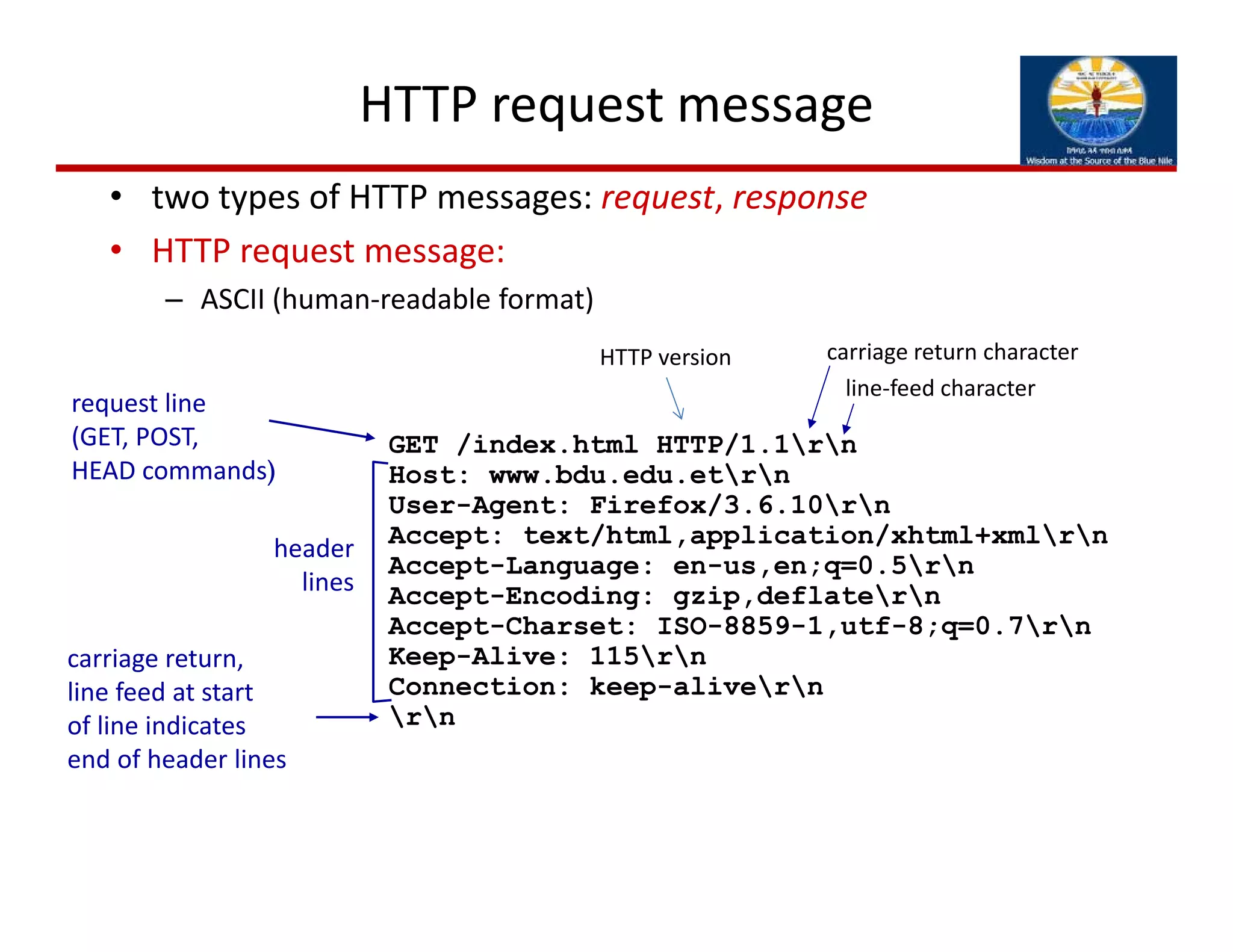
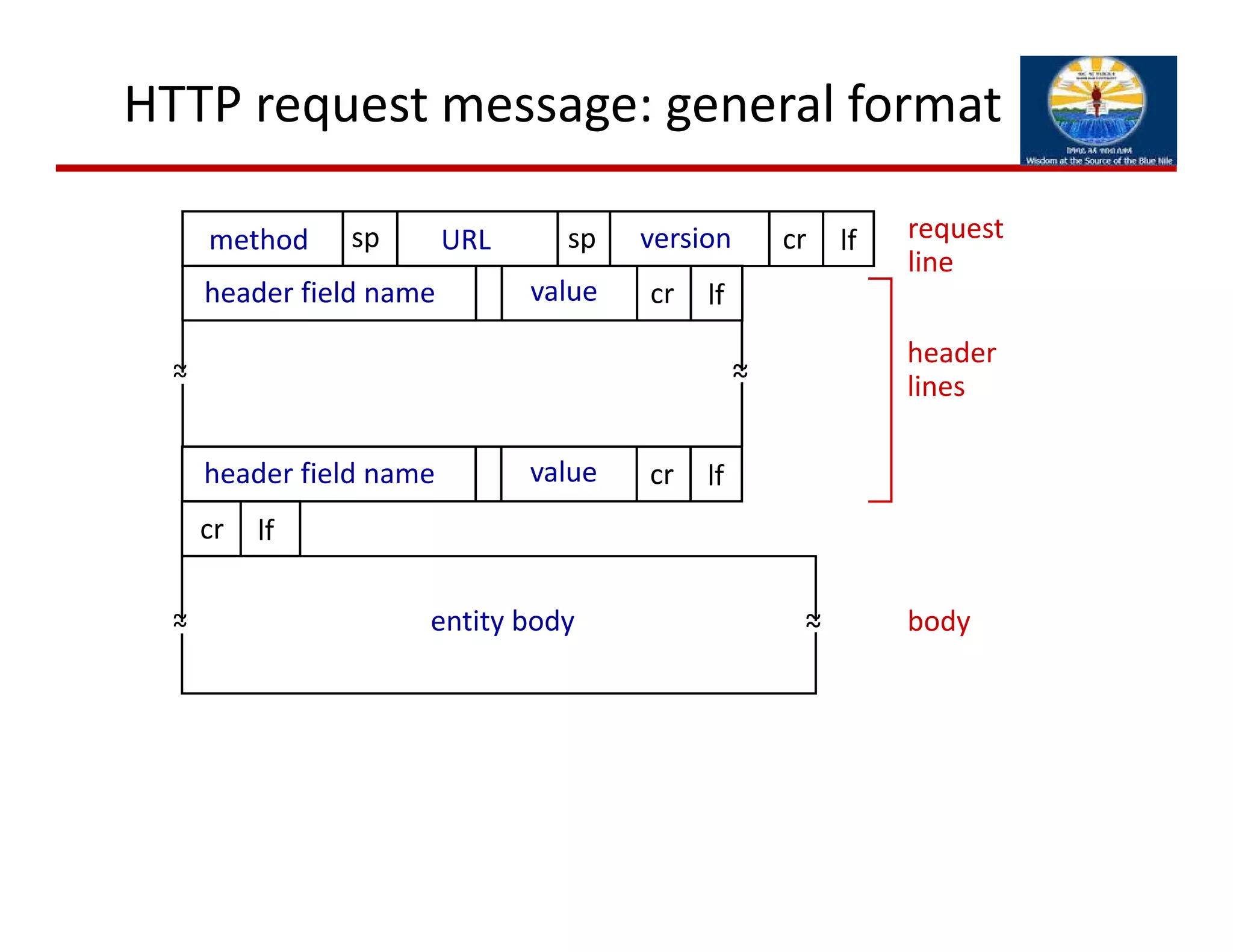
This document discusses the application layer in computer networks. It begins by outlining key learning outcomes related to network application protocols, popular protocols like HTTP, FTP, SMTP, and DNS, and socket programming. It then covers principles of network applications like the client-server and peer-to-peer paradigms. Specific sections discuss the HTTP protocol that powers the web, including HTTP requests and responses, and how HTTP connections can be persistent. The document also briefly mentions securing TCP connections with SSL.






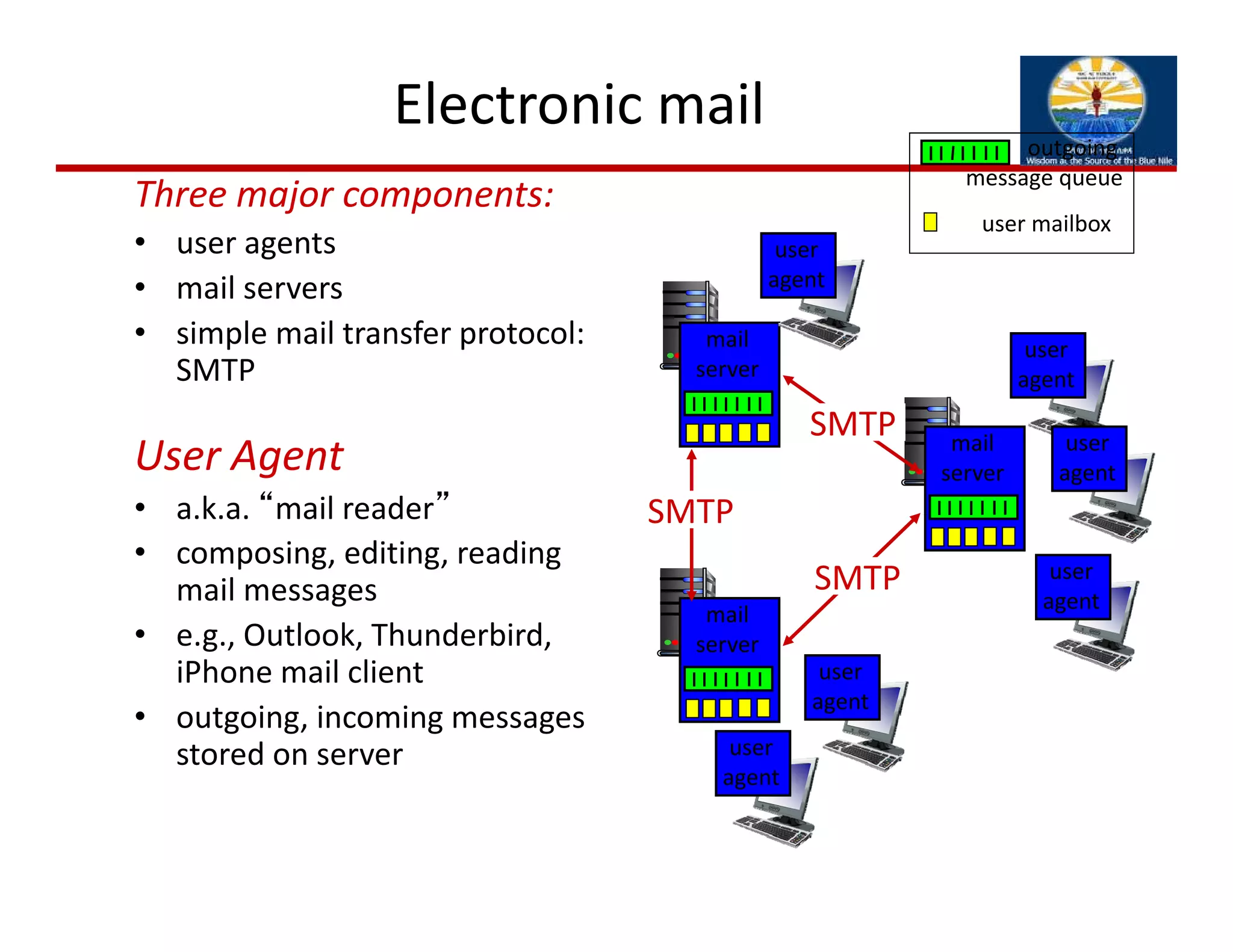
![Electronic Mail: SMTP [RFC 2821, RFC 5321]
• uses TCP to reliably transfer email message from
client to server, port 25
• direct transfer: sending server to receiving server
• three phases of transfer
– handshaking (greeting)
– transfer of messages
– closure
• command/response interaction (like HTTP, FTP)
– commands: ASCII text
– response: status code and phrase
• messages must be in 7‐bit ASCI](https://image.slidesharecdn.com/2-180206150217/75/2-application-layer-53-2048.jpg)
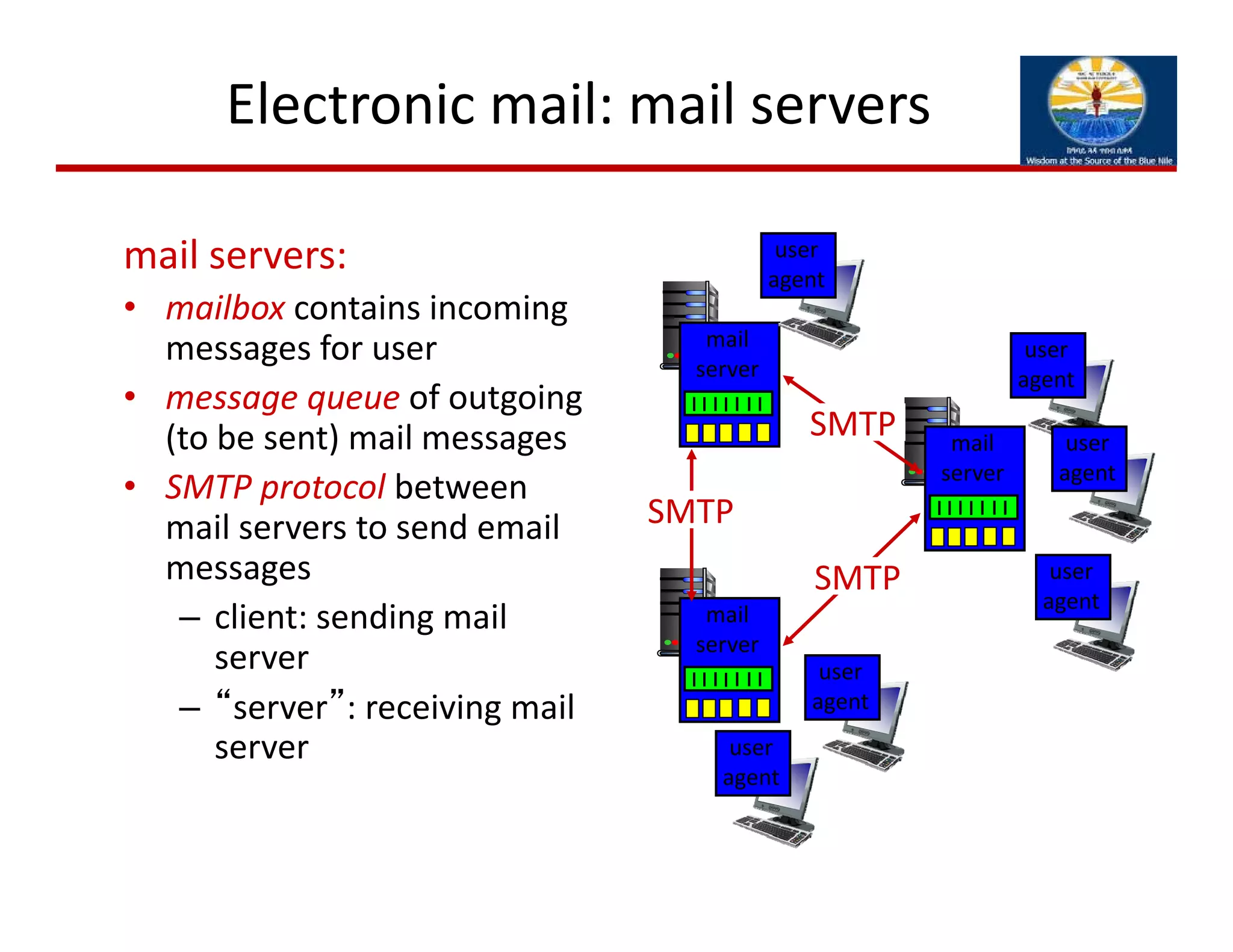
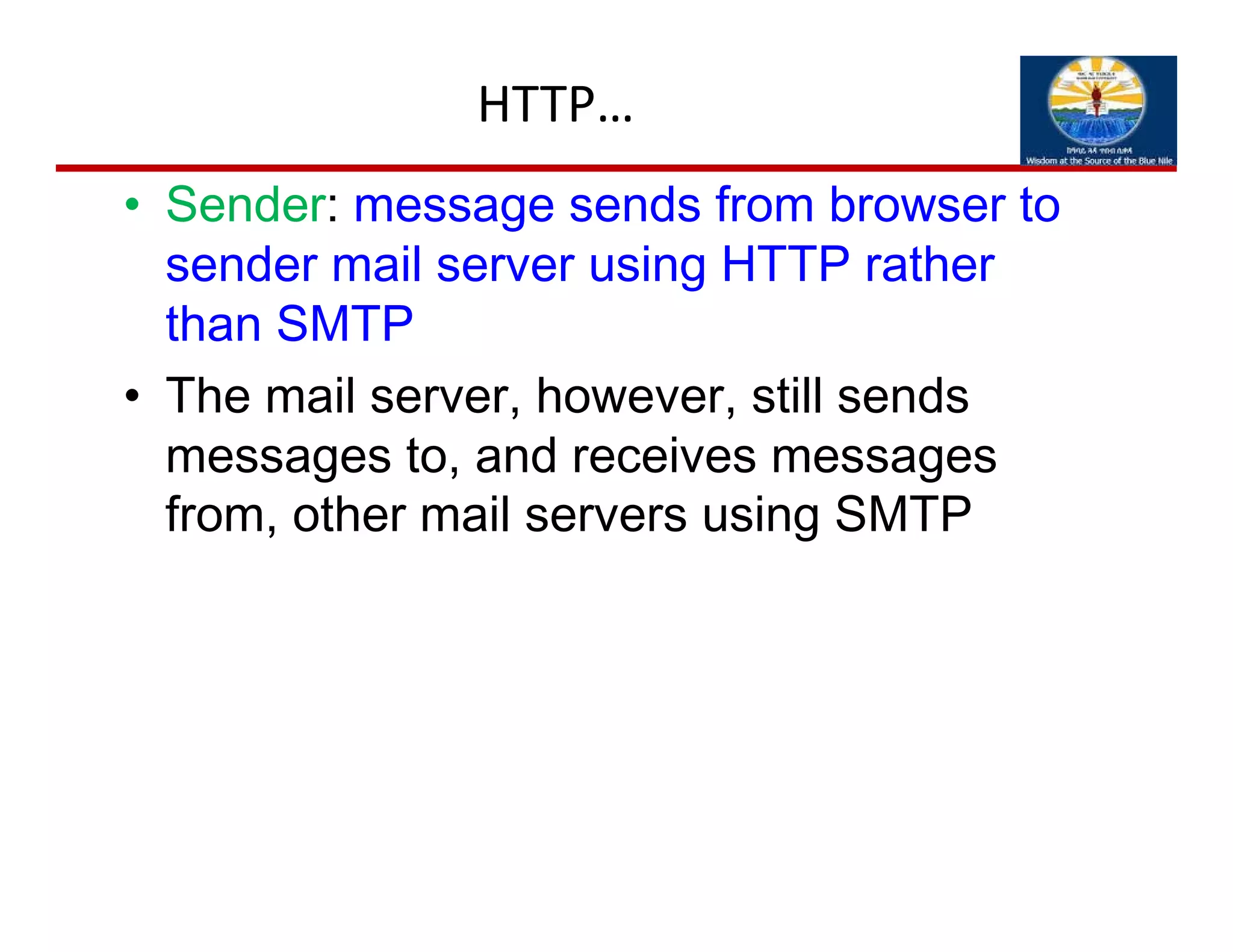
![Mail access protocols
• SMTP: delivery/storage to receiver’s server
• mail access protocol: retrieval from server
– POP: Post Office Protocol [RFC 1939]: authorization, download
– IMAP: Internet Mail Access Protocol [RFC 1730]: more
features, including manipulation of stored msgs on server
– HTTP: gmail, Hotmail, Yahoo! Mail, etc.
sender’s mail
server
SMTP SMTP
mail access
protocol
receiver’s mail
server
(e.g., POP3,
IMAP)
user
agent
user
agent](https://image.slidesharecdn.com/2-180206150217/75/2-application-layer-60-2048.jpg)
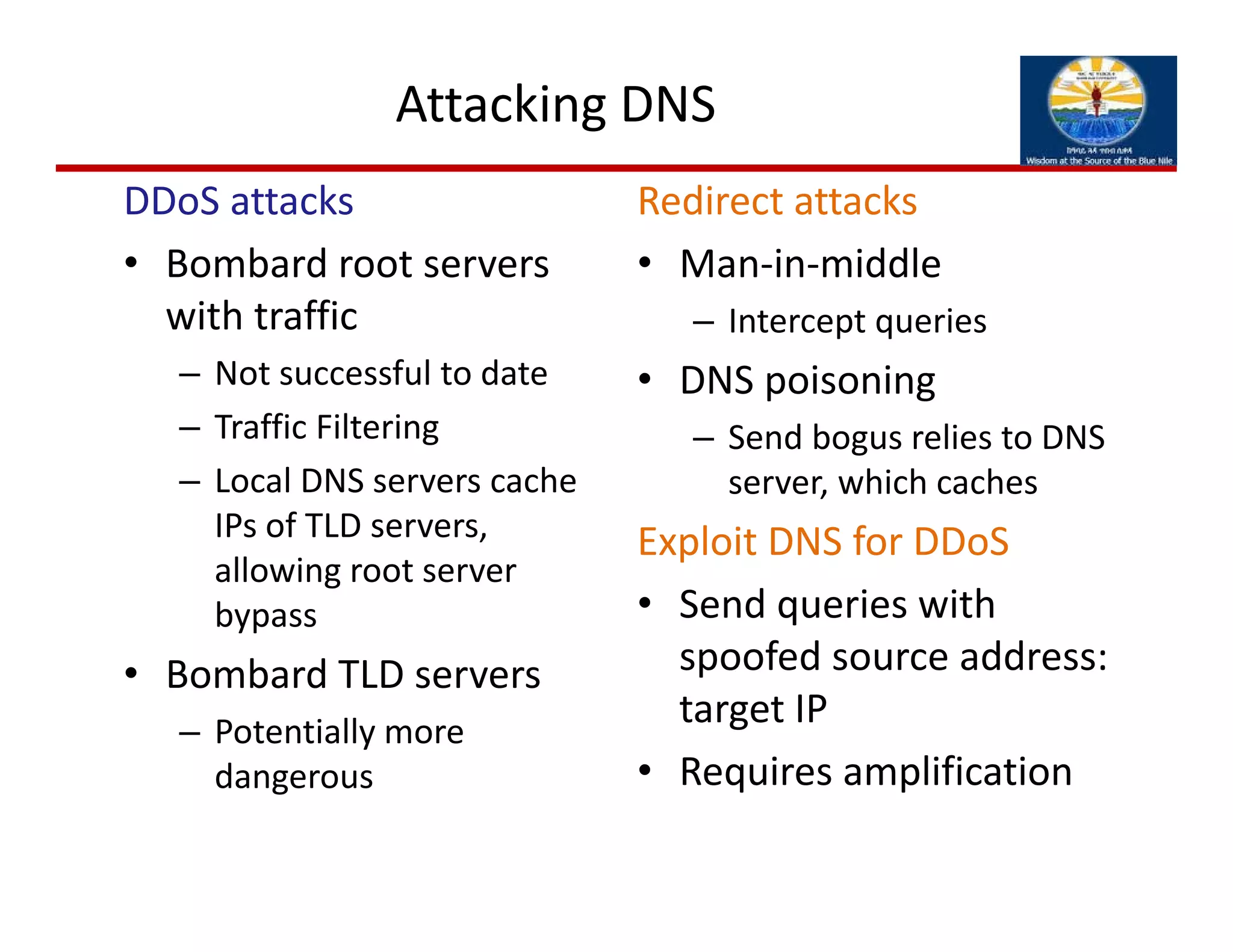


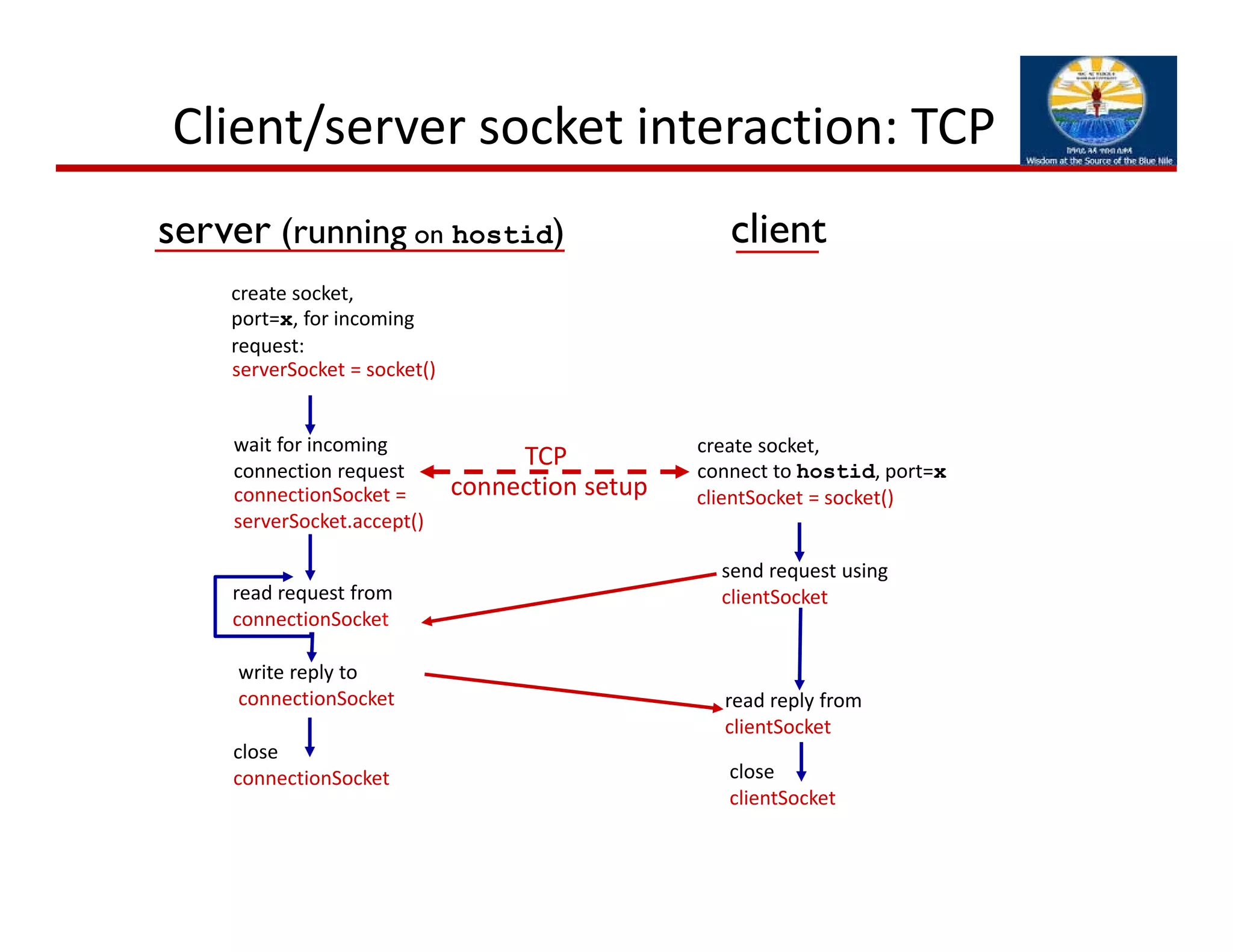
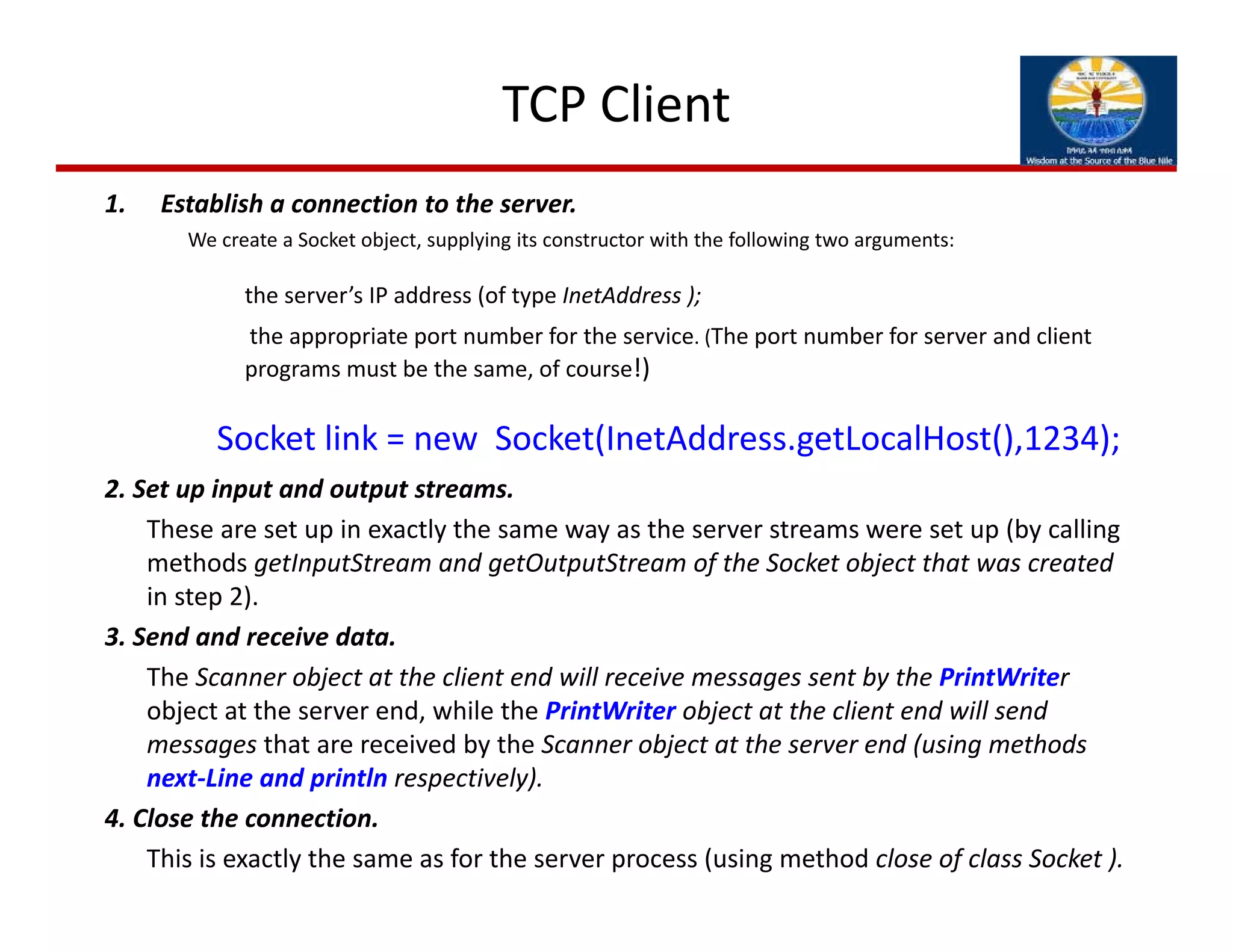
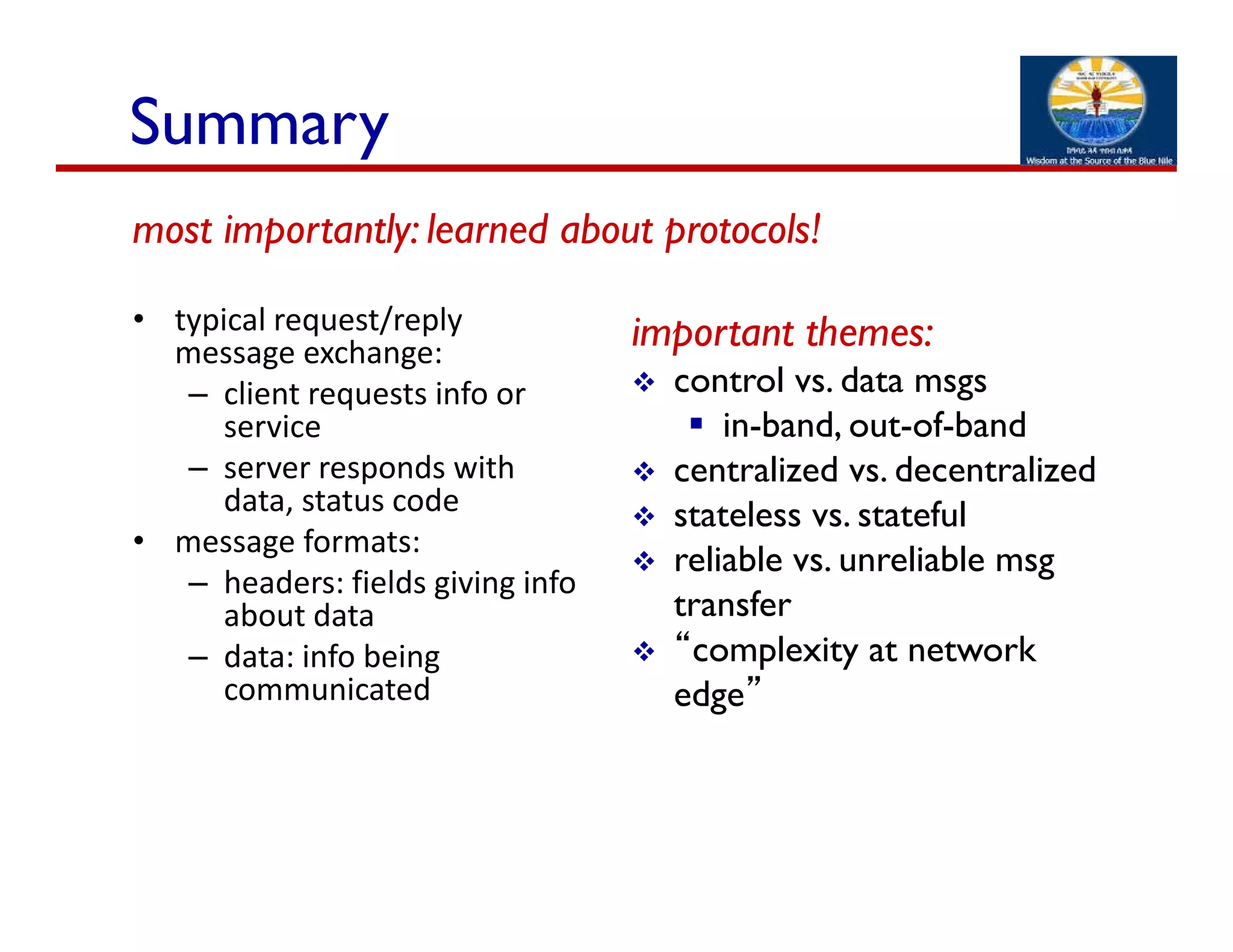
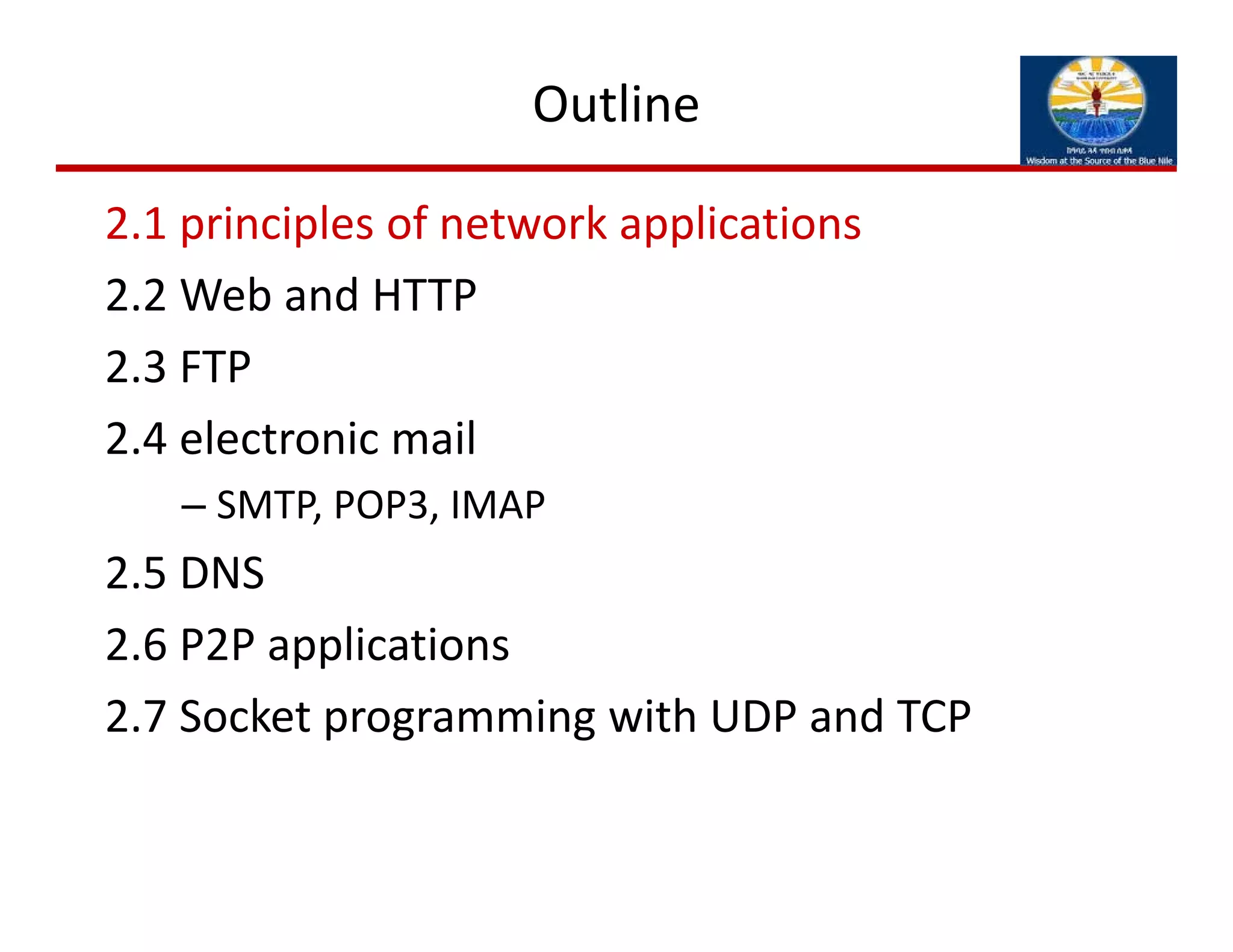
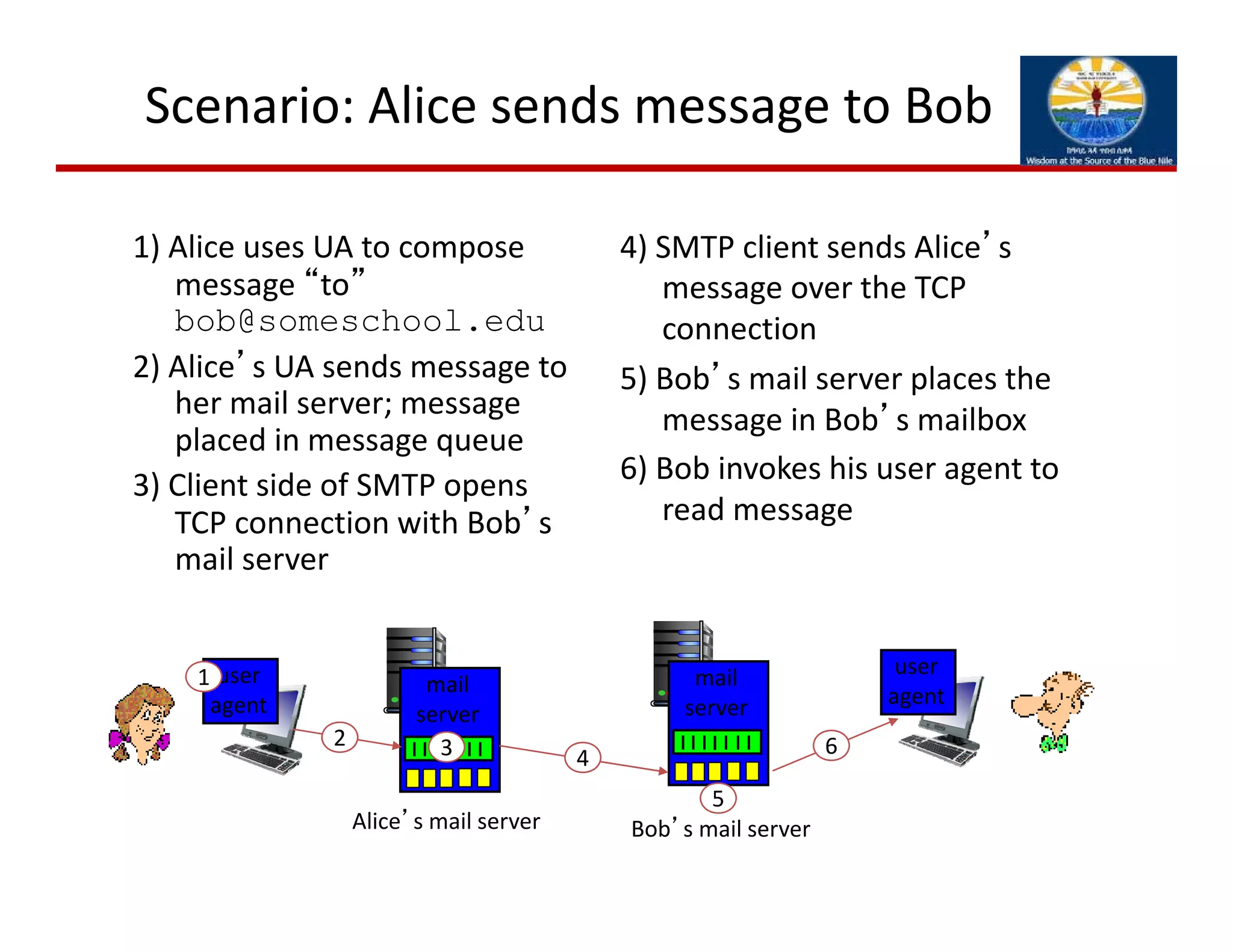
![TCPServer.java
• import java.net.*;
import java.io.*;
import java.util.*;
public class TCPServer {
private static ServerSocket serverSocket;
private static final int PORT = 4567;
public static void main(String[] args)
{
System.out.println("Opening port…n");
try
{
serverSocket = new ServerSocket(PORT);//Step 1.
}
catch(IOException ioEx)
{
System.out.println( "Unable to attach to port!");
System.exit(1);
}
do
{
handleClient();
}while (true);
}
private static void handleClient()
{
Socket link = null; //Step 2.
try
{
link = serverSocket.accept(); //Step 2.
Scanner input =
new Scanner(link.getInputStream());//Step 3.
PrintWriter output =
new PrintWriter(
link.getOutputStream(),true); //Step 3.
int numMessages = 0;
String message = input.nextLine(); //Step 4.
while (!message.equals("***CLOSE***"))
{
System.out.println("Message received.");
numMessages++;
output.println("Message " + numMessages
+ ": " + message); //Step 4.
message = input.nextLine();
}
output.println(numMessages
+ " messages received.");//Step 4.
}
catch(IOException ioEx)
{](https://image.slidesharecdn.com/2-180206150217/75/2-application-layer-120-2048.jpg)
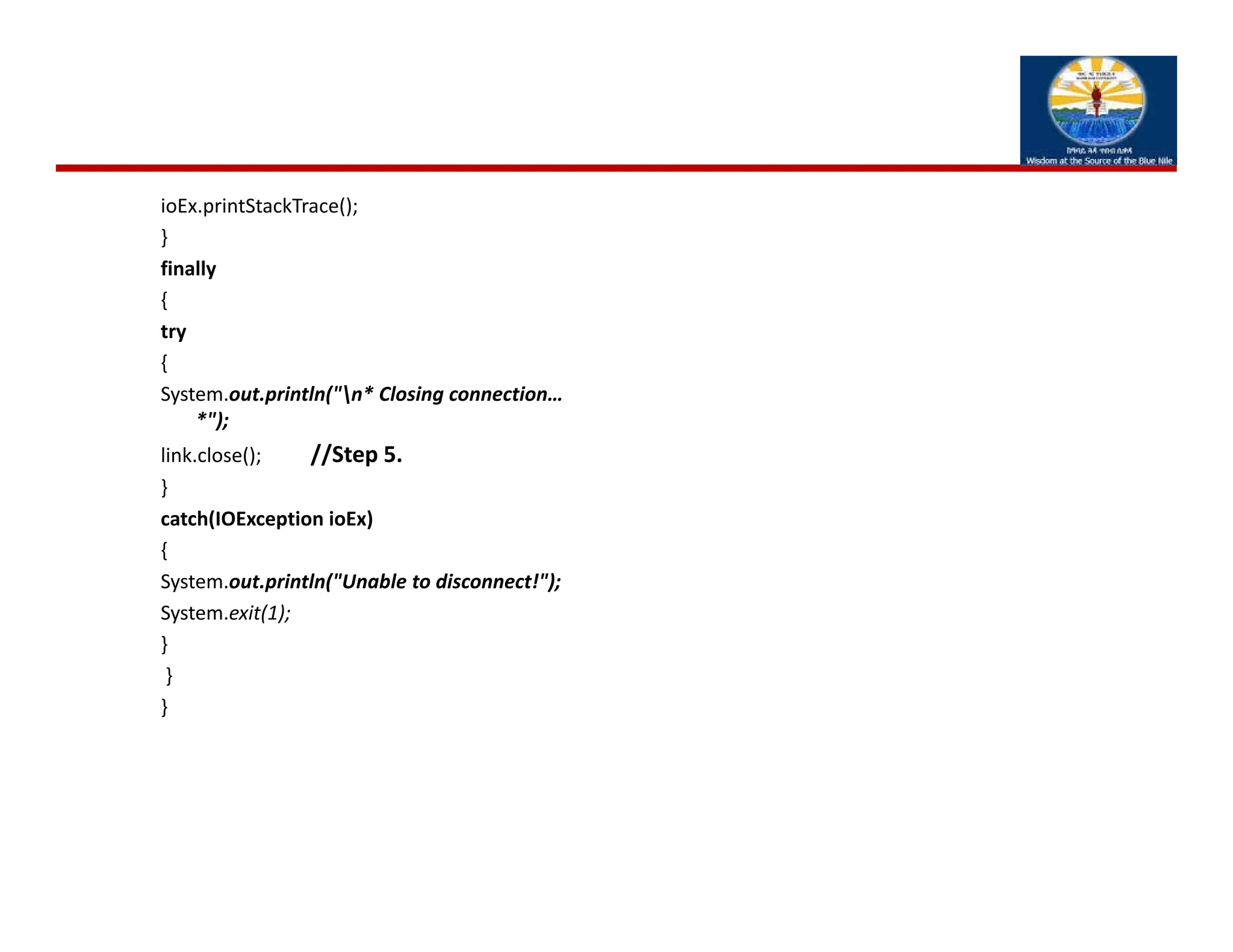
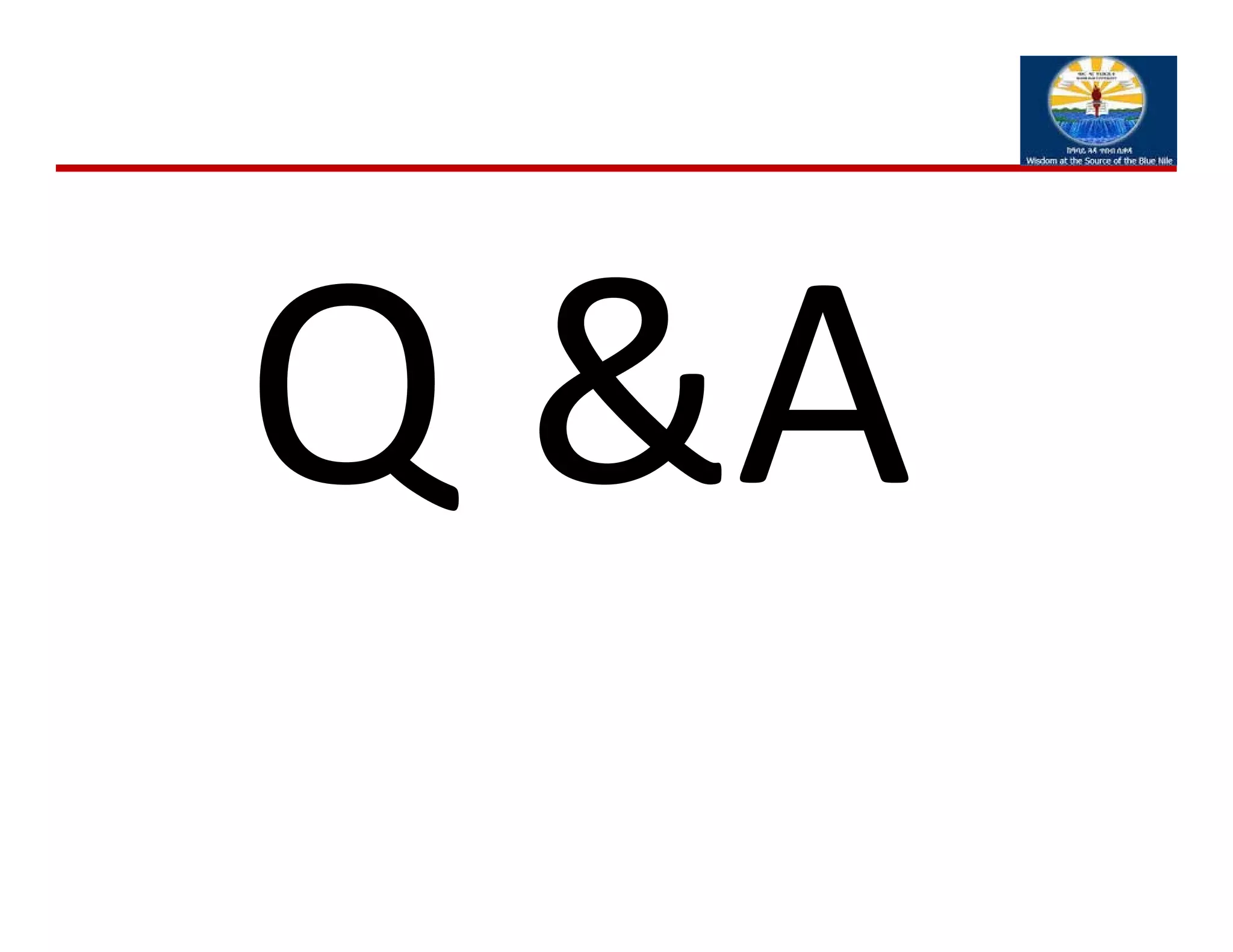
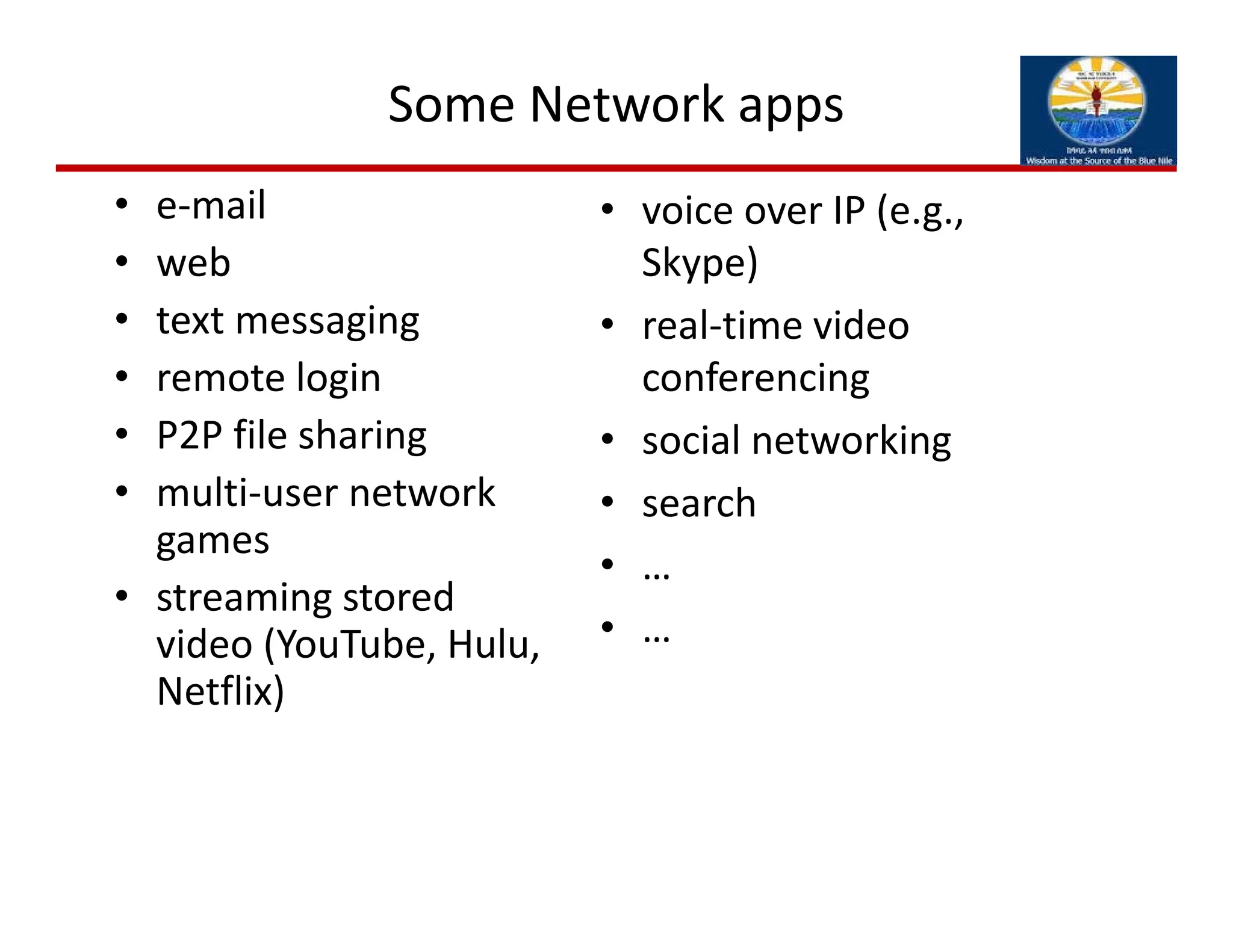
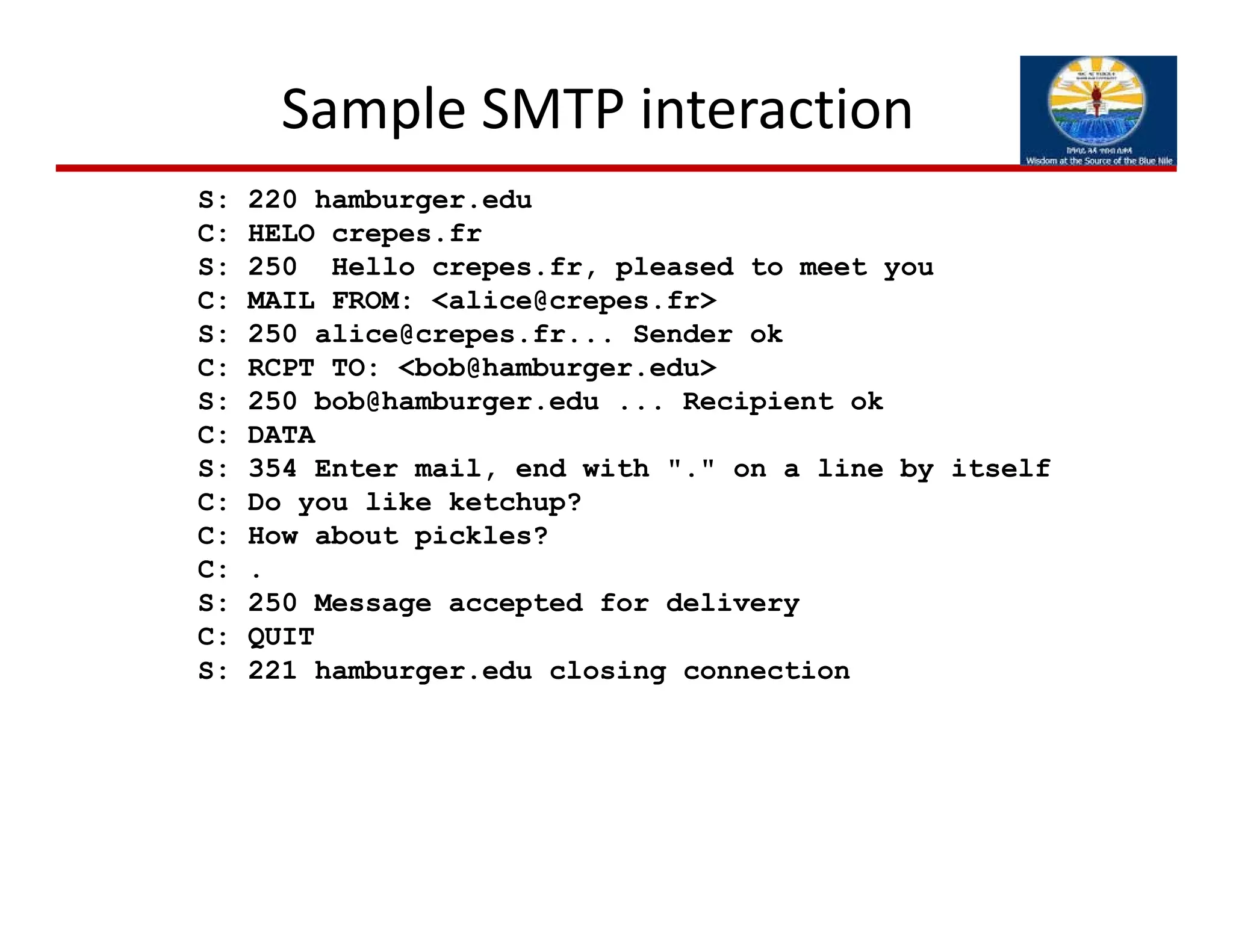
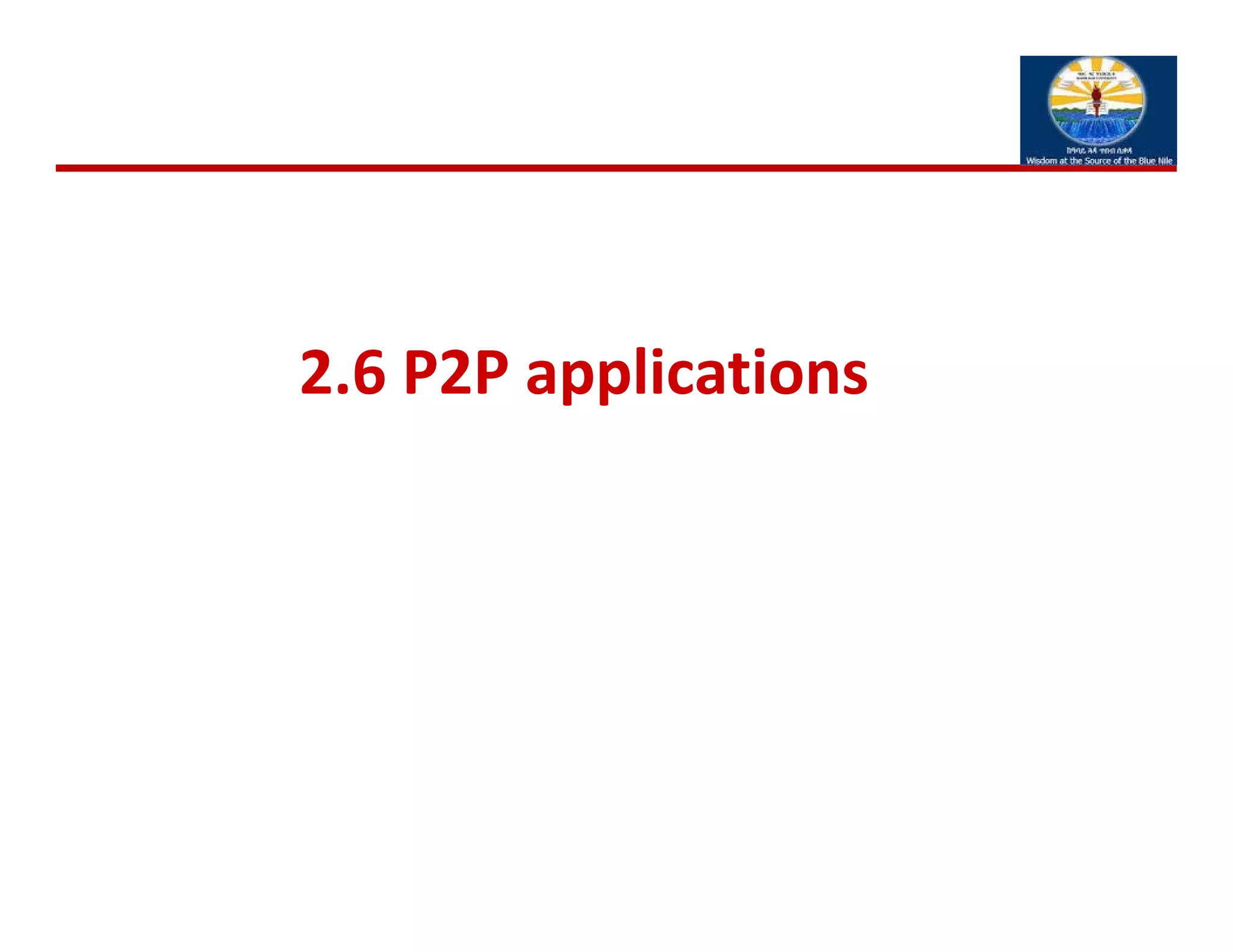
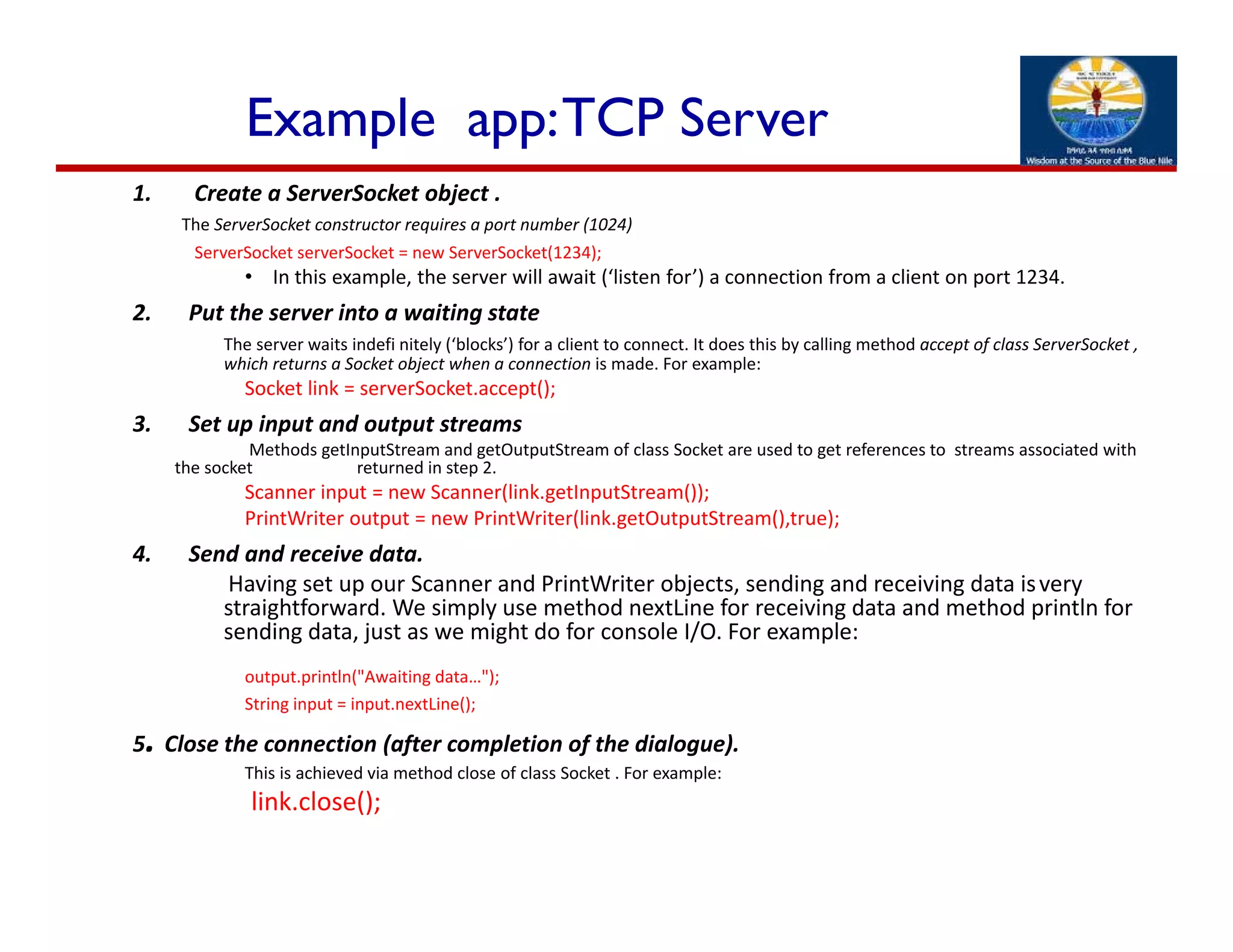
![TCPClient.java
import java.net.*;
import java.io.*;
import java.util.*;
public class TCPClient {
private static InetAddress host;
private static final int PORT = 4567;
public static void main(String[] args)
{
try
{
host = InetAddress.getLocalHost();
}
catch(UnknownHostException uhEx)
{
System.out.println("Host ID not found!");
System.exit(1);
}
accessServer();
}
private static void accessServer()
{
Socket link = null; //Step 1.
try
{
link = new Socket(host,PORT); //Step 1.
Scanner input = new Scanner(link.getInputStream()); //Step 2.
PrintWriter output = new PrintWriter(
link.getOutputStream(),true); //Step 2.
{
b//Set up stream for keyboard entry…
Scanner userEntry = new Scanner(System.in);
String message, response;
do
{
System.out.print("Enter message: ");
message = userEntry.nextLine();
output.println(message); //Step 3.
response = input.nextLine(); //Step 3.
System.out.println("nSERVER> "+response);
}while (!message.equals("***CLOSE***"));
}
catch(IOException ioEx)
{
ioEx.printStackTrace();
}
finally
{
try
{
System.out.println( "n* Closing connection… *");
link.close(); //Step 4.
}
catch(IOException ioEx)
{
System.out.println( "Unable to disconnect!");
System.exit(1);
}
}
}
}](https://image.slidesharecdn.com/2-180206150217/75/2-application-layer-122-2048.jpg)