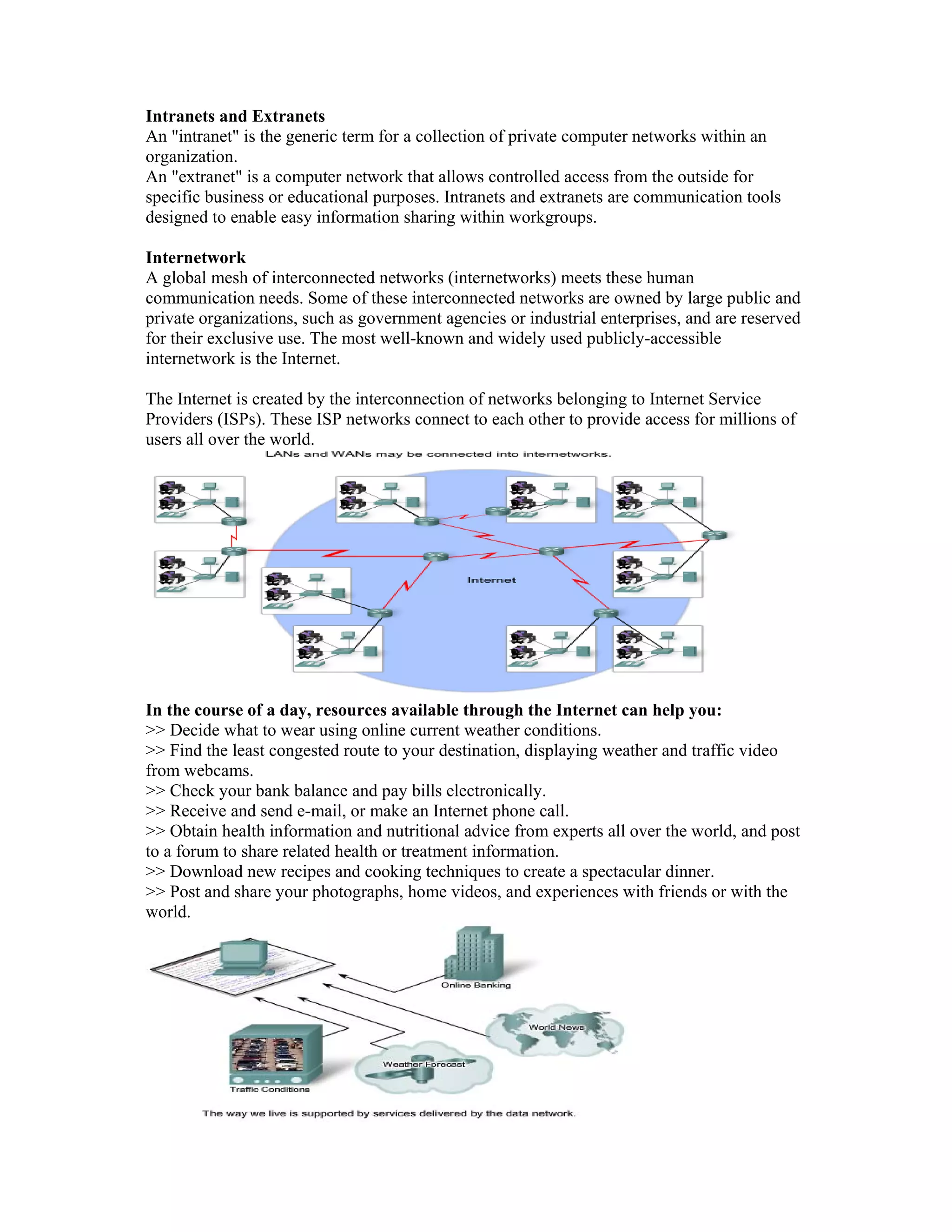
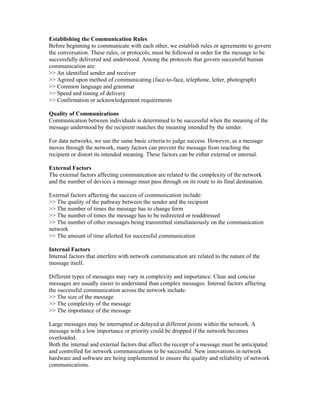
An intranet is a private computer network within an organization, while an extranet allows controlled external access for business purposes. The internet is a global mesh of interconnected public and private networks that people use every day for tasks like checking weather, finding routes, paying bills, communicating, researching health topics, cooking, and sharing photos. Before communicating, people establish rules like identifying the sender and receiver, communication method, language, and timing to ensure understanding. For data networks, factors like network quality, number of message handovers, message complexity, size, and priority can prevent successful communication if not controlled. Technology is enabling voice, video, and data to travel over a single converged network rather than separate networks, but new applications require consistent