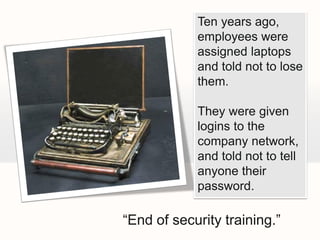
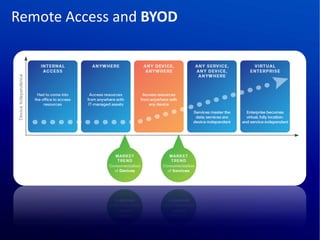
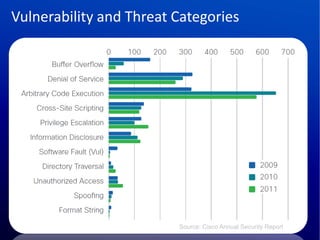
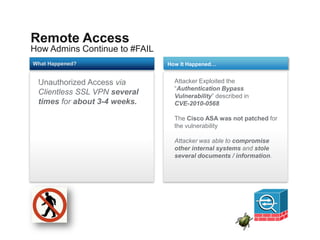
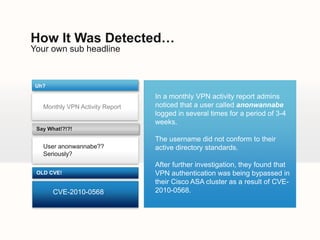
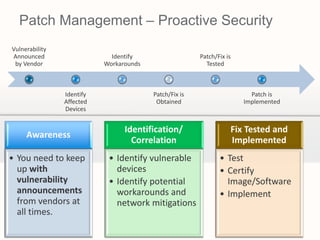
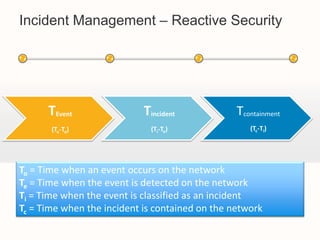
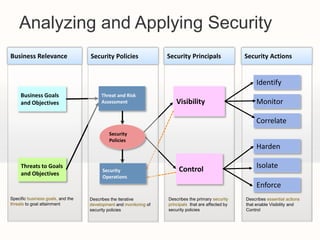
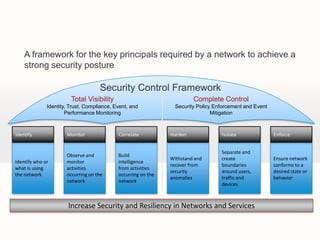
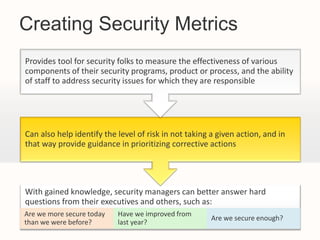
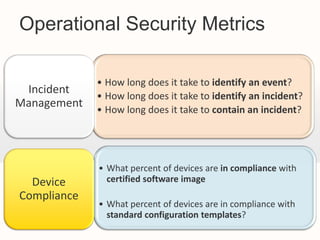
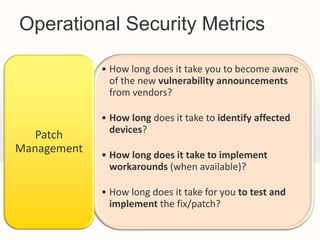
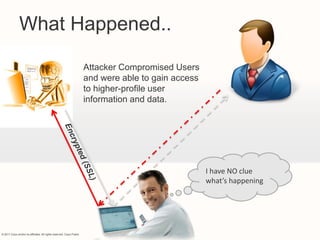
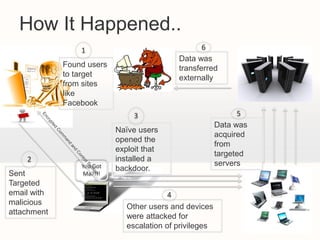
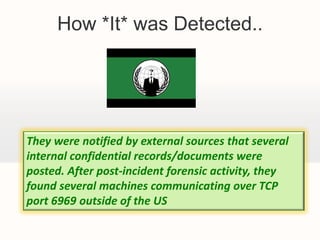
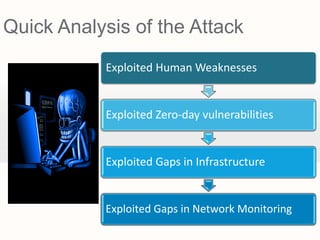
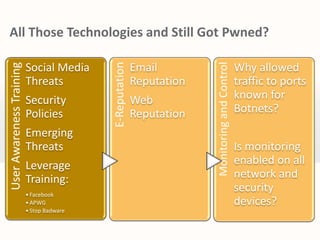
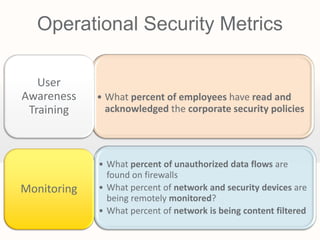
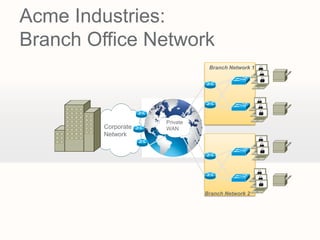
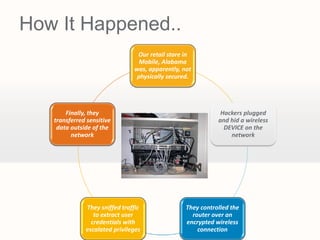
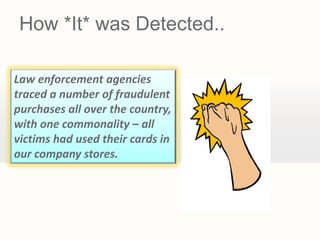
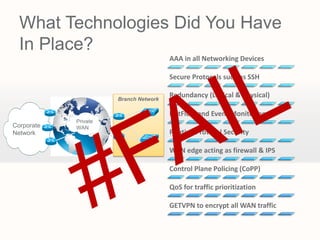
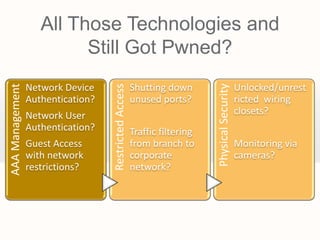
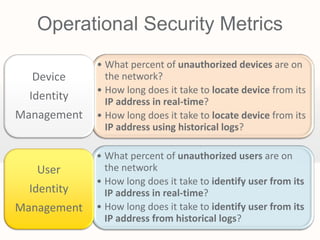
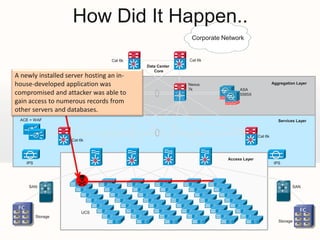
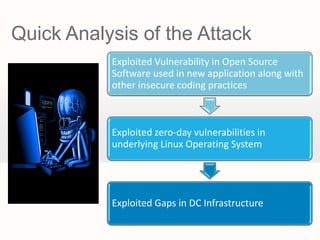
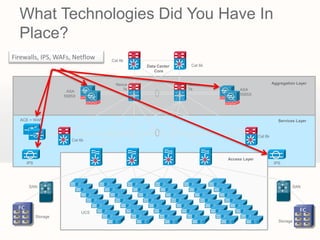
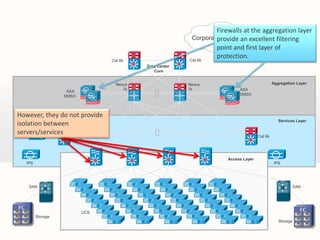
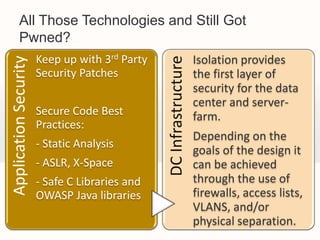
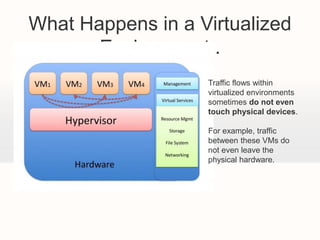
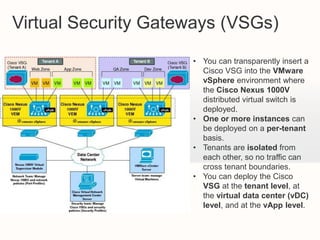
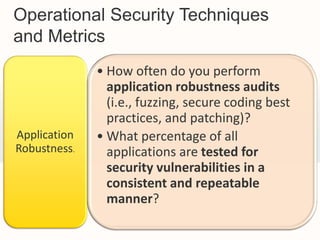
The document discusses the evolution of network security concerns from 2012, highlighting the frequency of cyberattacks, the inadequacies in current security measures, and case studies of security breaches. It emphasizes the need for proactive patch management, incident management, and the establishment of effective security policies to mitigate risks. Additionally, it explores the influence of social media, device vulnerabilities, and the importance of security metrics in evaluating organizational security posture.